Luca Steeb
982 posts
Luca Steeb
@steebchen
co-founder https://t.co/mPOZUaqgpx talk to me about AI & Infrastructure https://t.co/rO9vRvLQjc









Giving a restaurant a three star review is illegal in Germany.

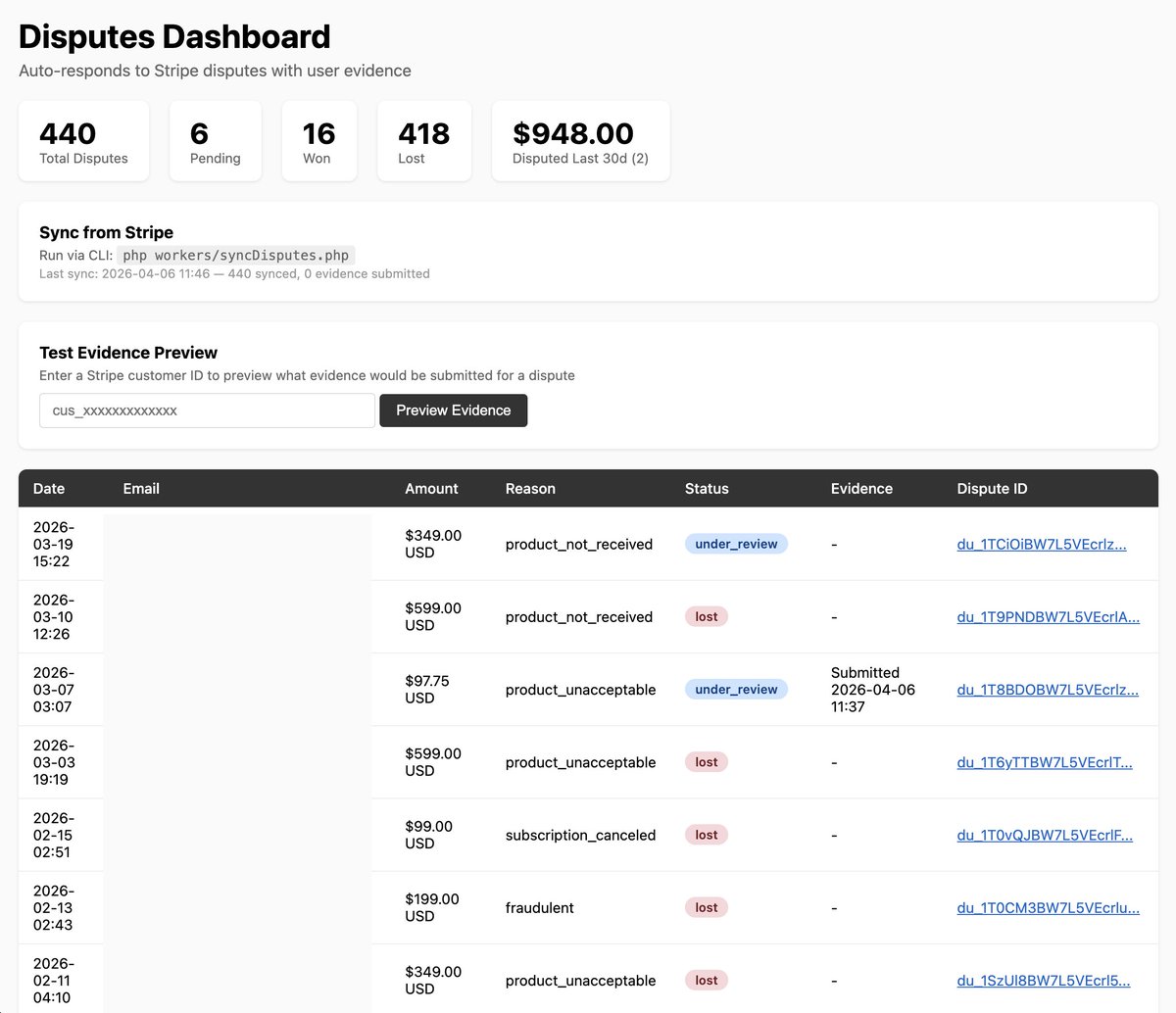

Okay I'll try to vibe code an automatic Stripe dispute responder that: 1) receives disputes via webhook 2) collects evidence of user sign up and activity 3) puts it in a beautiful PDF 4) submits it back to Stripe for the banks to review Once it works I'll ask it to summarize it and share the prompt/skill here Codebase is too unique per project so prompt/skill makes more sense!



I want to keep everyone updated on the details of the security investigation. The team performed an in-depth analysis to search for root causes and to better understand the behavior of the threat actor. We cast a very wide net, pulling and processing nearly a petabyte of logs of the entire Vercel Network and API, extending well beyond the initial Context[.]ai compromise. We now understand that the threat actor has been active beyond that startup's compromise. Threat intel points to the distribution of malware to computers in search of valuable tokens like keys to Vercel accounts and other providers. Once the attacker gets ahold of those keys, our logs show a repeated pattern: rapid and comprehensive API usage, with a focus on enumeration of non-sensitive environment variables. As a result: ◾We've deepened and widened our collaboration with partners across the industry, like Microsoft, AWS and Wiz, to further protect the broader internet. ◾ We've notified other suspected victims of this threat actor, independent of this event, encouraging them to rotate credentials and adopt best practices. We've also shipped a bunch more product enhancements. I'm extremely thankful to our team and industry partners for working around the clock. For more details on the ongoing investigation, refer to our security bulletin: vercel.com/kb/bulletin/ve…