
Ruby
19.3K posts


Ruby
@thisorthat17
Secure Software Development/Information Security #BITCOIN | #BTC | #2A | #1A Typoes are bait.


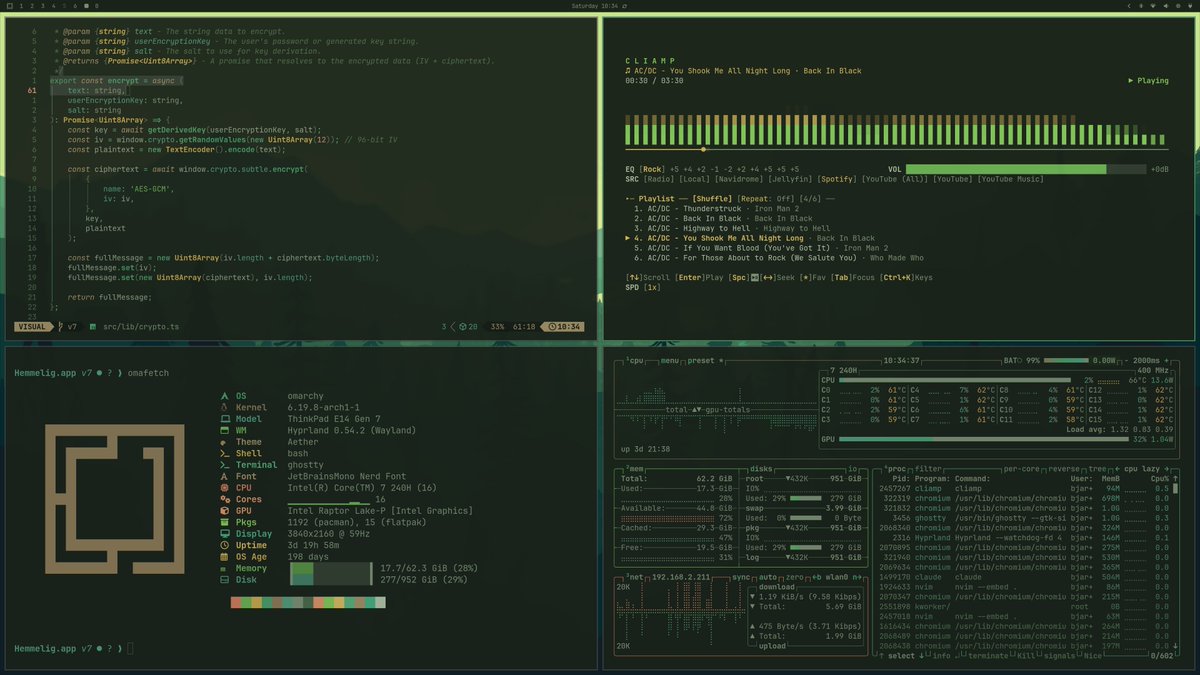
I won't add AI to Aether, instead, I added the IPC protocol to it, and a remote using the CLI to live update the running application using Claude. Here is a video demo using the Tokyo Night color ramp to turn it into a Forest color scheme. Added an additional picture to the thread of this post.





If quantum “kills” Bitcoin, it also kills: • The global banking system • SWIFT transfers • Stock exchanges • Military communications • Nuclear command systems • Every HTTPS website on earth If Bitcoin is dead from quantum, your portfolio is the least of your problems.


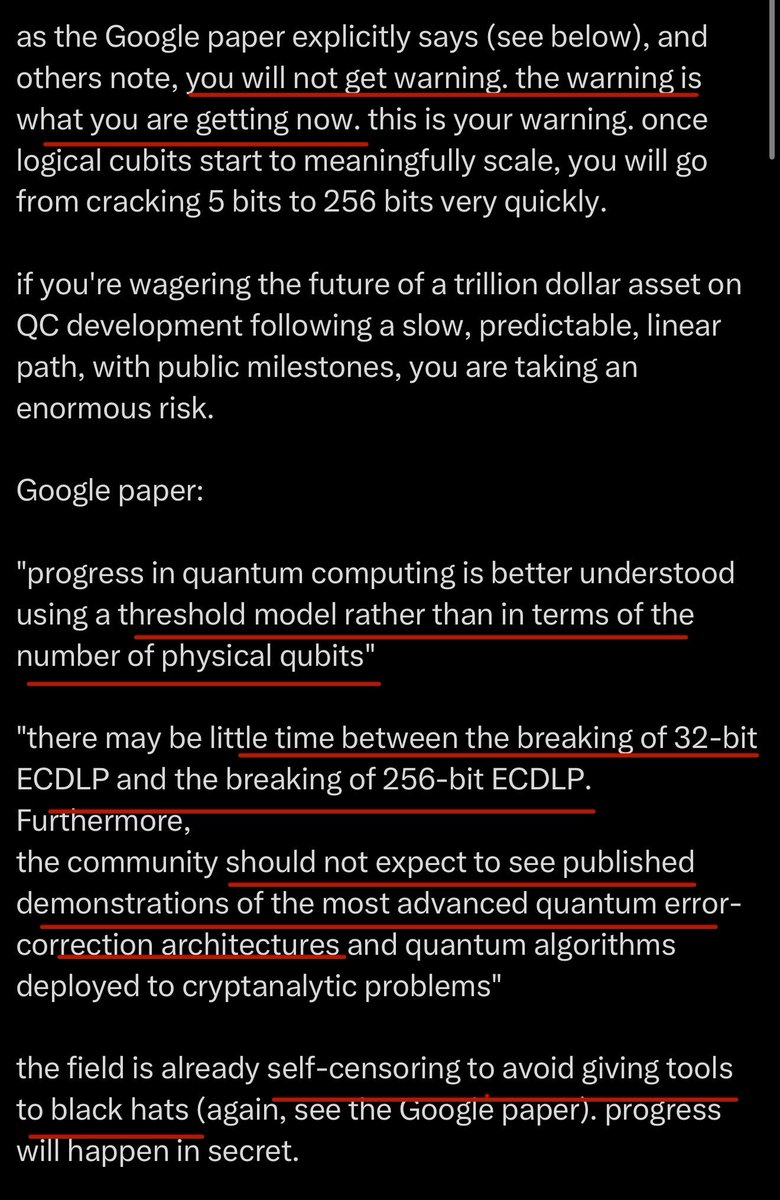
this might seem like a reasonable take, but it's actually unreasonable and wildly risky. as the Google paper explicitly says (see below), and others note, you will not get warning. the warning is what you are getting now. this is your warning. once logical cubits start to meaningfully scale, you will go from cracking 5 bits to 256 bits very quickly. if you're wagering the future of a trillion dollar asset on QC development following a slow, predictable, linear path, with public milestones, you are taking an enormous risk. Google paper: "progress in quantum computing is better understood using a threshold model rather than in terms of the number of physical qubits" "there may be little time between the breaking of 32-bit ECDLP and the breaking of 256-bit ECDLP. Furthermore, the community should not expect to see published demonstrations of the most advanced quantum error-correction architectures and quantum algorithms deployed to cryptanalytic problems" the field is already self-censoring to avoid giving tools to black hats (again, see the Google paper). progress will happen in secret. additionally, as we all know, it will take a minimum of several years to fully transition. a signature scheme must be chosen, tested, deployed, soft forked, and adopted (this has to happen for every single address, which alone will take months). thus, you have to start acting several years before Q-day. unfortunately, the premise that the development of a CRQC will happen slowly, publicly, and predictably that almost all Bitcoin devs seem to be relying on, is false. Bitcoin devs will have to do something uncomfortable: act under conditions of uncertainty and make difficult and costly tradeoffs _before_ the threat seems clearly apparent. we will not have the luxury to waiting until a N bit key is broken. at that point, we will have weeks or months, not the years required. this means that the testing and deployment of a PQ signature scheme on Bitcoin has to occur in 2026.




NEW: 🚨 GOOGLE RESEARCH FINDS QUANTUM COMPUTERS COULD BREAK BITCOIN, ETHEREUM, AND MOST MAJOR BLOCKCHAINS SOONER THAN EXPECTED


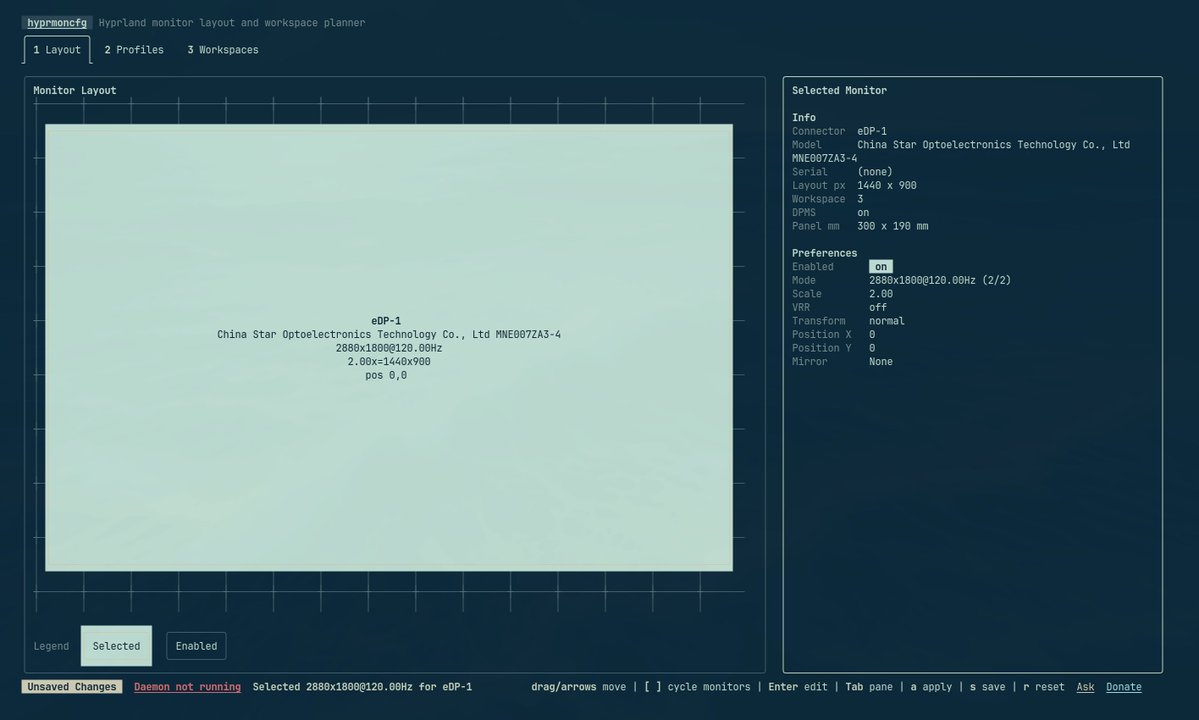
Hyprland monitor config is painful. You edit monitor= lines by hand, do coordinate math, reload, off by 40 pixels, edit again. Unplug at a conference and you're back to editing config files backstage. I built hyprmoncfg: a TUI where you drag monitors on a canvas and save named profiles. A daemon auto-applies the right one on hotplug. Two Go binaries. No Python, no GTK, no D-Bus. yay -S hyprmoncfg hyprmoncfg.dev paolino.me/hyprmoncfg-mon… #Hyprland #Linux #OpenSource @ryanrhughes @dhh @charmcli @hyprwm




Many are wondering "what Google saw" that caused them to revise their post-quantum cryptography transition deadline to 2029 last week. It was this: research.google/blog/safeguard…










