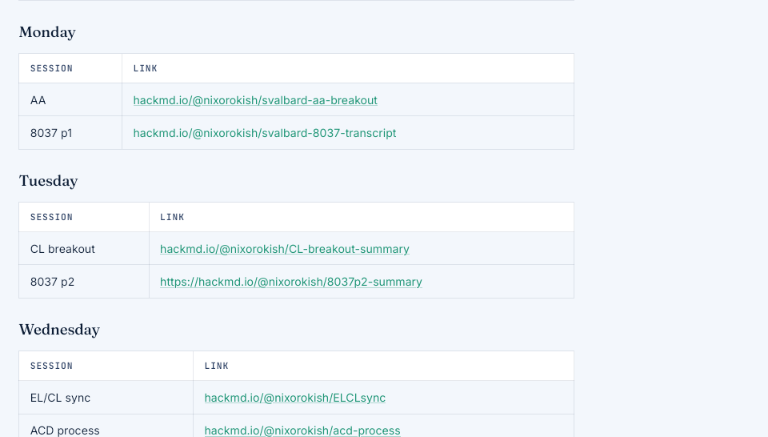
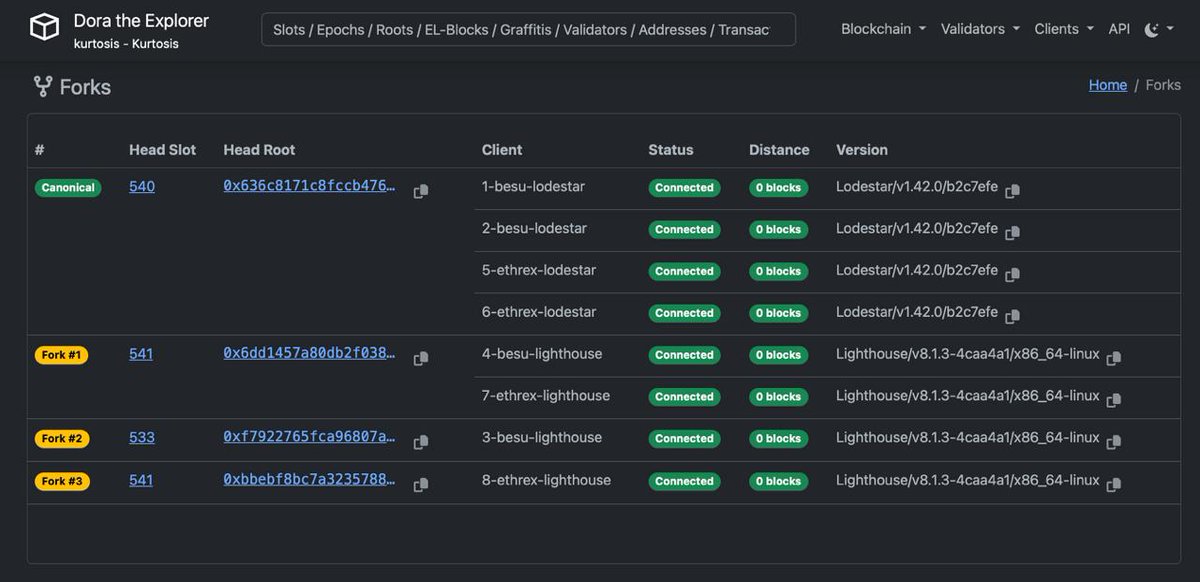
Last week, Ethereum core contributors gathered in Svalbard for the Soldøgn interop: a week long event focused on hardening Glamsterdam implementations to scale Ethereum securely ☀️ Read the full recap, including their candidate post-fork gas limit, below: