Joe
1K posts


After Months of Development, FINALLY ready to share: Harden System Security🎉
✅ Complete System Hardening
✅ Security Posture Analysis
✅ All-in-One Toolkit
✅ Built-in Intune support for Scalability
✅ Beautiful Modern UI
✅ CLI support
github.com/HotCakeX/Harde…
#Cyber #Windows
English
Joe retweetledi

New video: deep dive into Defender for Endpoint/Antivirus settings.
- what every one really does
- what “good” looks like
- gotchas
- nuances
And why some of the important ones are “hidden”.
Watch: youtu.be/R8btJ_SjwVk

YouTube

English

I'm honored and super excited to be accepted as @Microsoft MVP for the 2nd year, this time in 2 new categories!!
Shoutout to @MVPAward and @BelaLior for accepting me in their community. ❤️🙏🏻
Been working on something big, will share more dits soon 😇💯
mvp.microsoft.com/en-US/mvp/prof…

English
@reprise_99 That’s and toys requiring 22 batteries and have no volume control.
English

🔥 BYPASS WINDOWS DEFENDER
XOR-obfuscate a Sliver C2 payload on Kali, forge a stealth C++ loader, and drop a reverse shell on Win10 in seconds.
OUT NOW:
youtu.be/lC9zh3_S-zg

YouTube
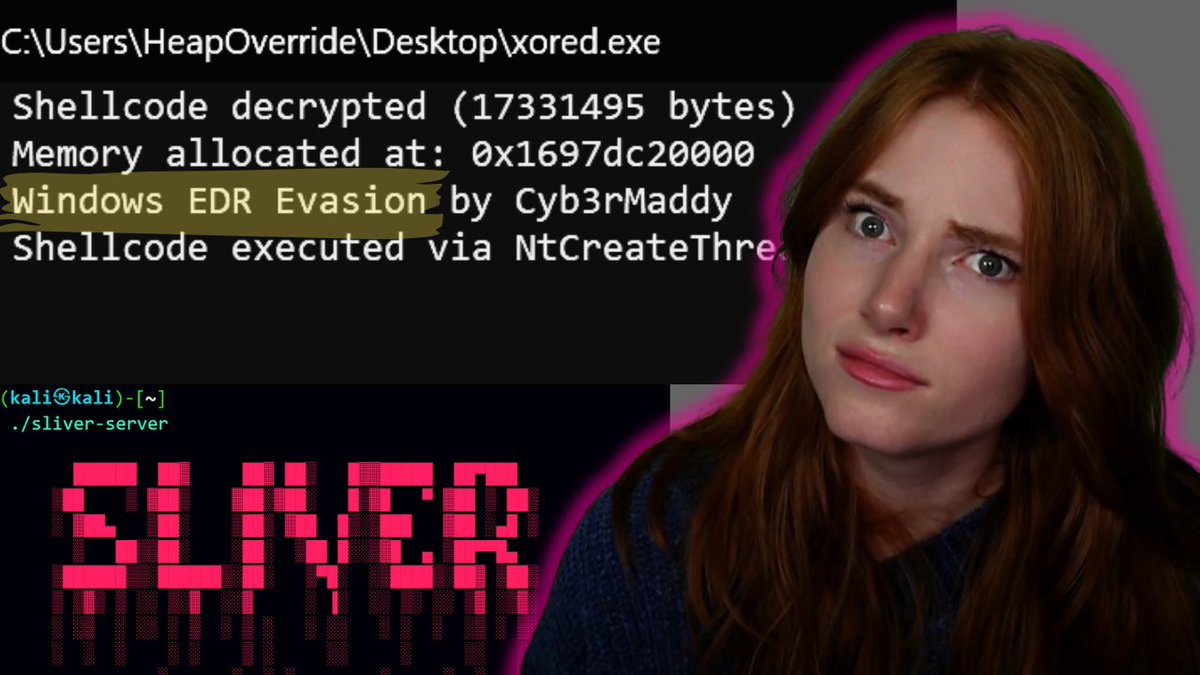
English

I successfully tested a LSASS dumping technique on a Windows 10 lab machine, which we encountered on a recent Incident Response engagement (no EDR, default Defender installed).
The "MiniDumpWriteDump" technique, as described here [1], was successful in writing the LSASS process to disk.
However, as soon as I tried to copy the dump to my Kali machine, Defender jumped into action, prohibited access to the LSASS dump, and removed the file to the quarantine. And here is the catch.
I browsed to the following folder:
C:\ProgramData\Microsoft\Windows Defender\Quarantine
In the ResourceData folder, you will find different sub-folders (or not, if Defender never quarantined something on that host), each folder containing a quarantine file.
The files are encrypted with a static key that leaked years ago, and this 10-year-old code snippet is still sufficient to decrypt the files back to their original state. [2]
Long story short: I copied the encrypted file to my Kali machine, decrypted it using the Python code from [2], and extracted the credentials and hashes with pypykatz. [3]
Classic example of "No, it's not enough when your AV blocked or removed a threat". As you can see, an attacker can easily get the LSASS dump, even if Defender removed it from the disk ¯\_(ツ)_/¯
[1 ]ired.team/offensive-secu…
[2] raw.githubusercontent.com/malmoeb/DFIR/r…
[3] github.com/skelsec/pypyka…

English

Hey @elonmusk can you use the power of this new US government to investigate this Lakers Mavs trade for us all? Thanks 🙏
English

@DebugPrivilege you still got pals in MSFT? got an interesting submission MDE is missing...nice bundled cobalt strike, nitrogenloader with MSTeamsSetup.exe
English
@NathanMcNulty @YongRheeMSFT It’s the proactive perf part I’m not super familiar with as the last 4 years or so of IR work it was always ad-hoc, mixed tooling situations we needed to troubleshoot so we knew the machine and generally how to repo perf issues.
English

@trk_rdy @YongRheeMSFT Should always start with a clean slate...
But there's no proactive performance reporting, so orgs bring exclusions over because "we don't wanna risk it..."
Poor Yong Rhee has already worked with one of these, but hopefully I can save him a call next month on something else :p
English

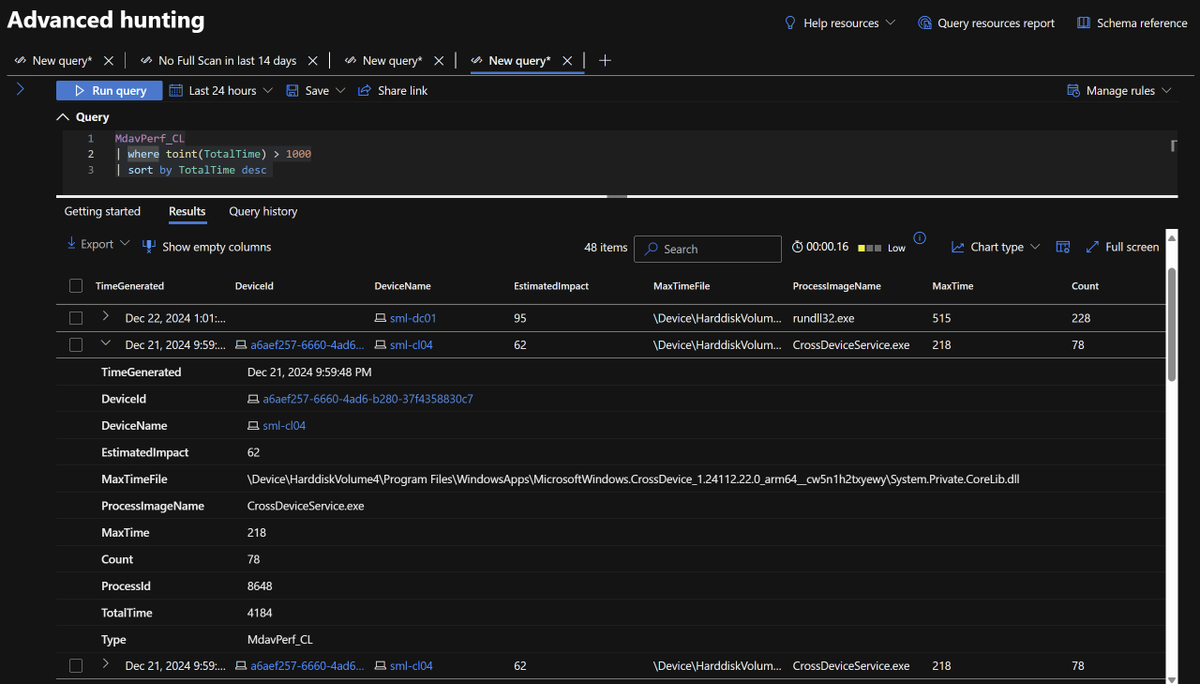
OK, now we're cooking :)
Will have to publish a blog on setup, but this is pretty awesome
Done with the part to collect EstimatedImpact events from MPLog and send back to a Log Analytics Workspace in a way we can query
Next is the performance analyzer output 😎
Nathan McNulty@NathanMcNulty
In case anyone is interested, here's a script to gather Defender logs and create a performance recording, then compress it and upload it to Azure blob storage This works via Live Response, Intune scripts, etc. Just need Create permissions on a SAS token. github.com/nathanmcnulty/…
English
@NathanMcNulty Oh boy haha, that’s usually the time to start with as clean of a slate as possible. @YongRheeMSFT and recommendations here?
Seems like there would many variables to this. Let me ponder on this.
English

@trk_rdy Proactive performance monitoring :)
Very long story short, I keep getting orgs that migrate a freaking mess of exclusions despite best efforts...
So I want to create a simple solution where we can identify/correlate potential issues and help create contextual process exclusions
English
@NathanMcNulty Very interesting question, is this something you’d collect ad-hoc or based on an event?
English

Yo @trk_rdy, got any recs on combinations of EstimatedImpact and time for cutoffs on what to collect from MPLog?
I'm thinking default of 70+ with over 1K total time for reasonable volume and things to chase down
Thoughts? :)
English
@reprise_99 Haha, garage fridge is for beer and venison. Certainly not a rich thing in the Midwest. For me it was a dining room, kids whose parents brought the food into a whole other room to eat was wild.
English