
Vijay Sarvepalli
423 posts


Vijay Sarvepalli
@vijaycert
Keep life chaotic.






#ESETresearch discovered and reported to @certcc a vulnerability that allows bypassing UEFI Secure Boot on most UEFI-based systems. This vulnerability, #CVE-2024-7344, was found in a UEFI app signed by Microsoft’s 3rd-party UEFI certificate. @smolar_m welivesecurity.com/en/eset-resear… 1/4











🚨New! "PKFail: Untrusted Platform Keys Undermine Secure Boot on UEFI Ecosystem." #PKfail is a supply-chain issue affecting x86/ARM devices around the globe. Blog: binarly.io/blog/pkfail-un… Full report: …222483.fs1.hubspotusercontent-na1.net/hubfs/22222483… A free scanning tool: pk.fail




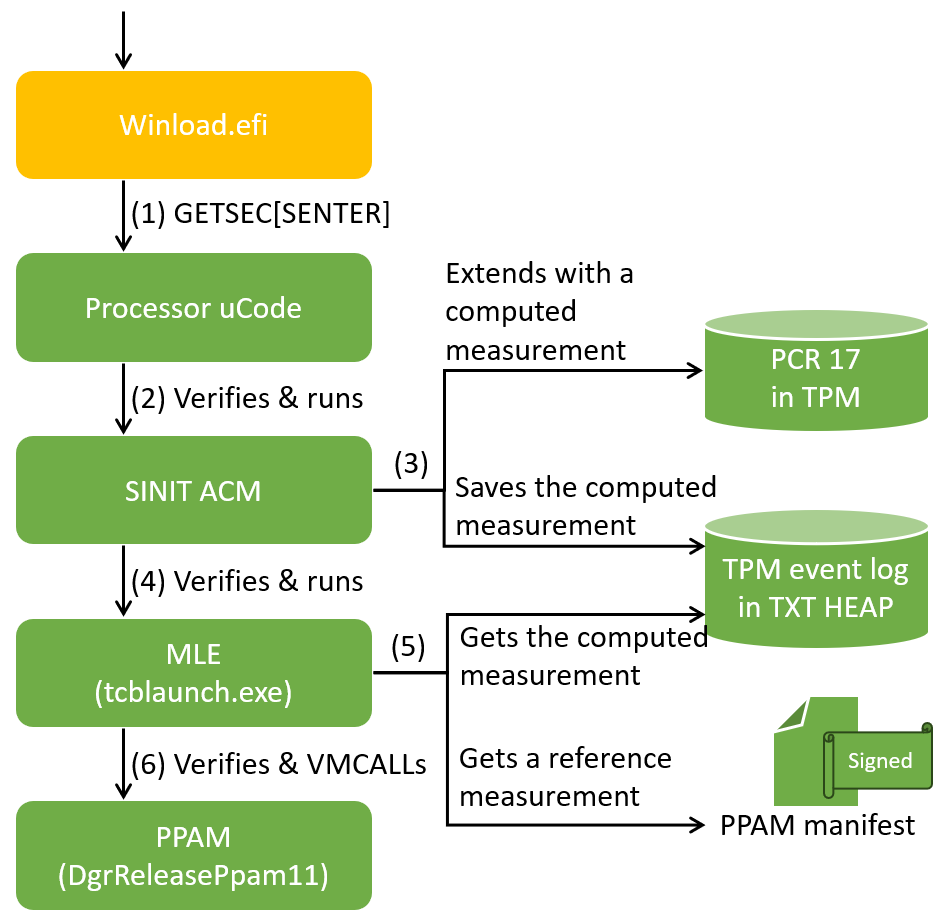

Intel Hardware Shield deep dive: part 1 is user-mode System Management Mode (ISRD). tandasat.github.io/blog/2024/02/2… ISRD is beautifully architected, and I have enjoyed studying it a lot. Excellent work by Intel.






This iMessage exploit is crazy. TrueType vulnerability that has existed since the 90s, 2 kernel exploits, a browser exploit, and an undocumented hardware feature that was not used in shipped software: securelist.com/operation-tria…




Calling all #cybersecurity pros! Join #BHEU Briefings "LogoFAIL: Security Implications of Image Parsing During System Boot" with CEO of BINARLY @matrosov sharing the latest research revealing significant security vulnerabilities. Register now >> bit.ly/3sLm2hD

