Ron Twist retweetledi

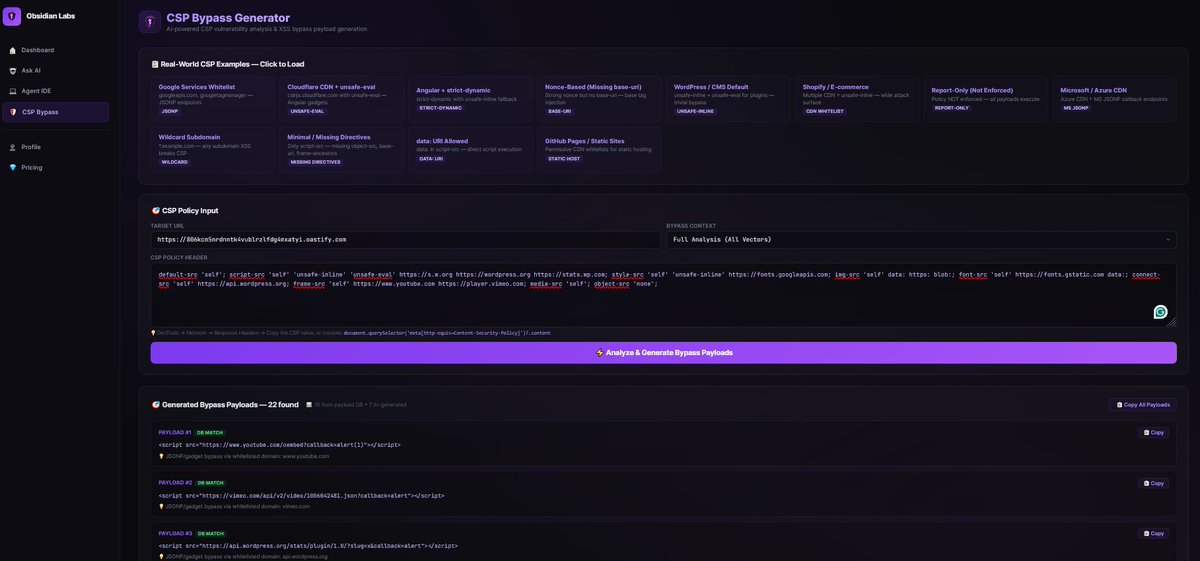
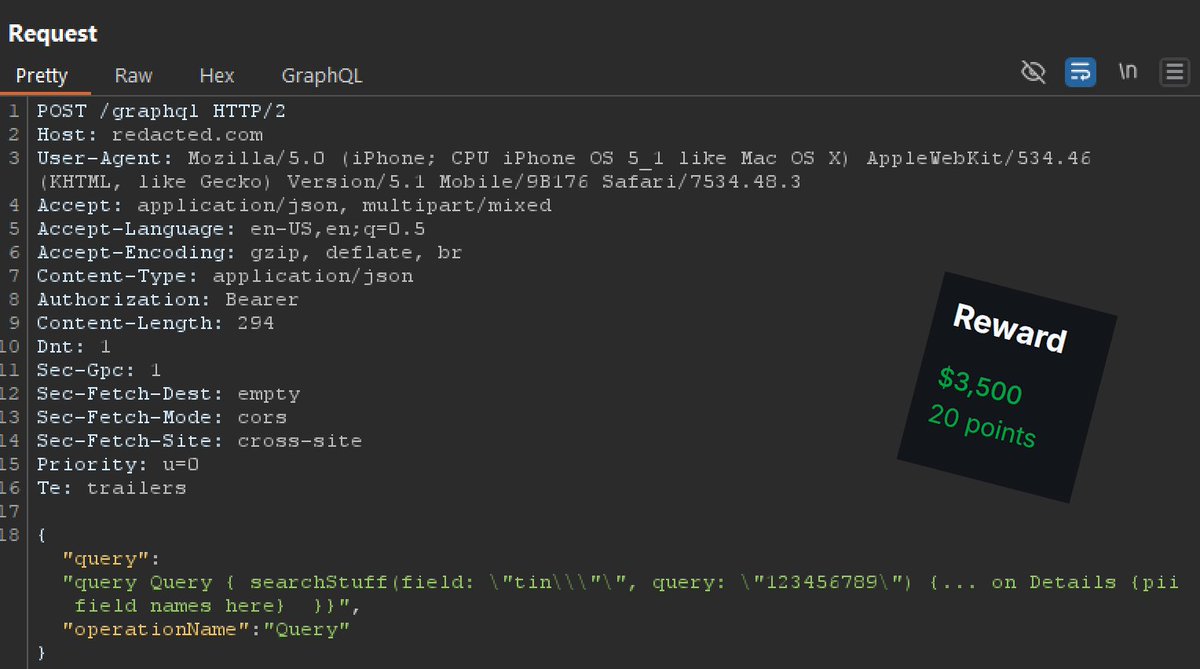
WAF bypass 101 #bugbountytips:
If the request is a POST/PUT/PATCH, many times the WAF will stop reading the payload after a certain number of characters, which varies from WAF to WAF and by configuration settings. This means you can insert harmless alphanumeric garbage to exceed its read limitation, and then your naughty payloads/injection comes after and will NOT be blocked. YAY
So in your payloads, if you add a new parameter as the FIRST parameter in the payload body, such as:
{"trash":"value", ... the rest of the payload}
or
trash=gibberish& ...theRestOfThePayload
I use the website below to generate the garbage:
onlinefiletools.com/generate-rando…
Start with 256KB in file size, copy and paste the text into your parameter, and then add something that would normally cause a WAF block into one of the other parameters. I tried to show an example here but it blocked me from posting the example (LOL).
Keep increasing gibberish size up to 2MB. If it doesn't work by then it usually wont on that target. Have fun!
English