Sabitlenmiş Tweet

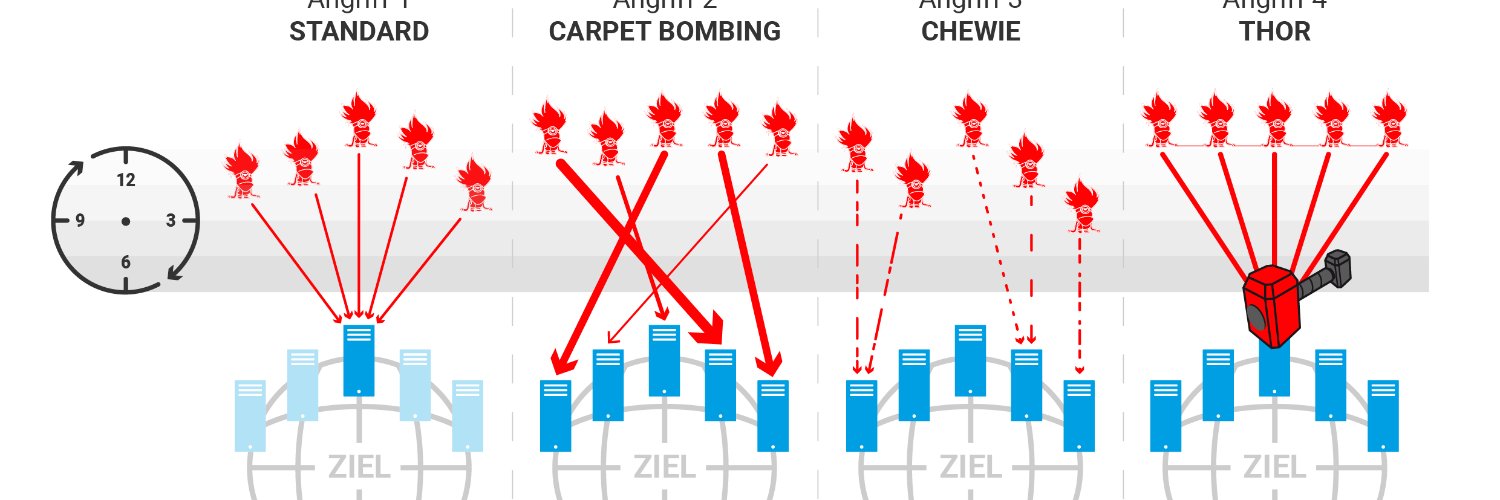
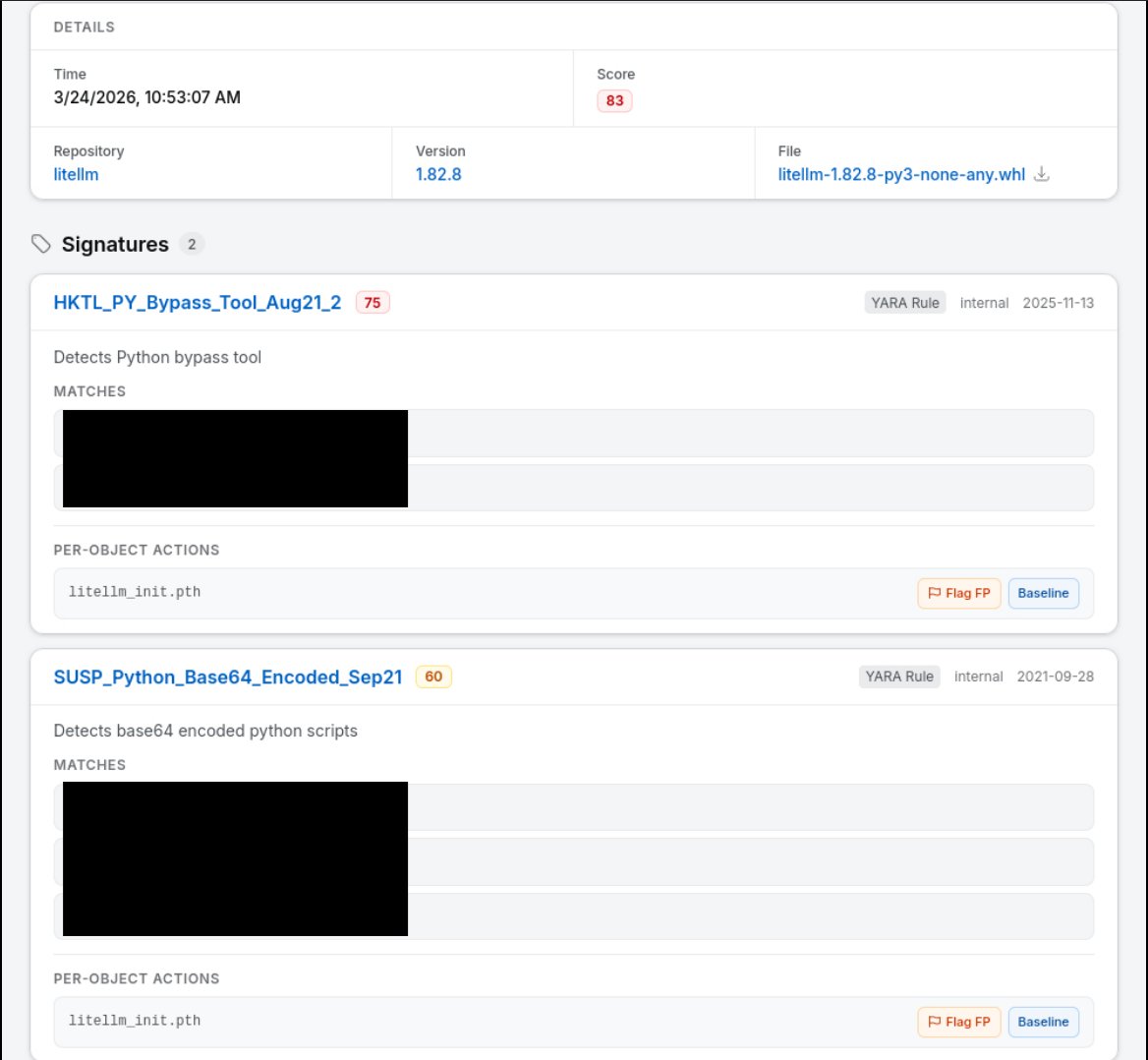
We analyzed 400 DDoS-Stresstests from 2022 and gathered very interesting insights into the current state of protection/mitigation-solutions, what works (well), what doesnt, and especially: WHY.
zero.bs/optimization-o…
#ddos #dfir #cybervandals

English