Clay Cowgill
298 posts










i never want to read any other way again.


So the other side of this was me. By 1997, I had written or rewritten most all the "protocol decodes" in the "Sniffer™ Network Analyzer", the premier closed-source product for this sort of thing. The reason it was expensive is that it could capture at WIRE SPEED. We wrote special hardware drivers that could keep up with the network, capturing all the packets. Competing solutions, especially Ethereal/Wireshark, could not. You could analyze slow networks with Ethereal, but not fast ones. Capture and analysis are two different things. The Sniffer™ did them both than anybody else. Linux didn't get close to wire-speed capturing until around 2010, and still isn't quite fully there. But now you can do some reasonably fast filtering in Wireshark to get just the packets you want, without losing them. This isn't a problem, though, because now most capture is done on the ends instead of the middle. Tapping into wires or hanging off mirror ports is much more rare. Writing protocol decodes is grunt work, and exactly the sort of thing that's amenable to open-source. For a vendor, we have to figure out which protocols customers want that will increase overall product sales. It means fewer and fewer obscure protocols being decoded. With open-source, even the least popular most obscure protocols get decoded. Some engineer simply roles up their sleaves and writes just enough code to decode what they need, and when it's not enough for the next engineer, they write more. In the long run, it means everyone eventually has to use it, because we always come across something obscure. That the Sniffer™ would eventually get replaced by an open-source product was inevitable. Anyway, I left in 1998 to create a company to do deep packet inspect at wire speed, but that's another story.


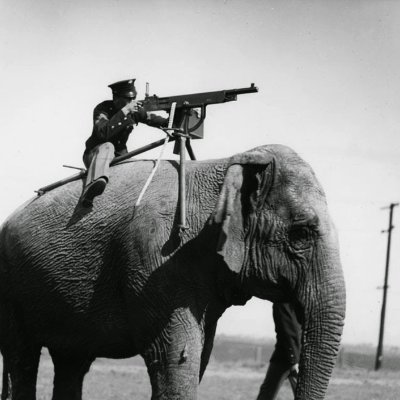
Over the past two months, production of STING interceptors has increased by more than twofold.