ทวีตที่ปักหมุด
Maverc Technologies
82 posts


Maverc Technologies
@Maverctech
Cyber Security consultants here to pilot you through the complex security maze .
Miami, Florida เข้าร่วม Nisan 2021
106 กำลังติดตาม14 ผู้ติดตาม

@LBHTShow Context is important when you make these types of hot takes !
2015 we led league the league in injuries 18 players went on ir: including
Terrell Suggs out for the season
Joe Flacco out for the season
Steve smith
Starting Tackles
Dennis pitta
The first two running backs.
English

This right here would have gotten just about any coach fired. Lamar extended his stay longer than it should have been. #ravensflock

English
Maverc Technologies รีทวีตแล้ว

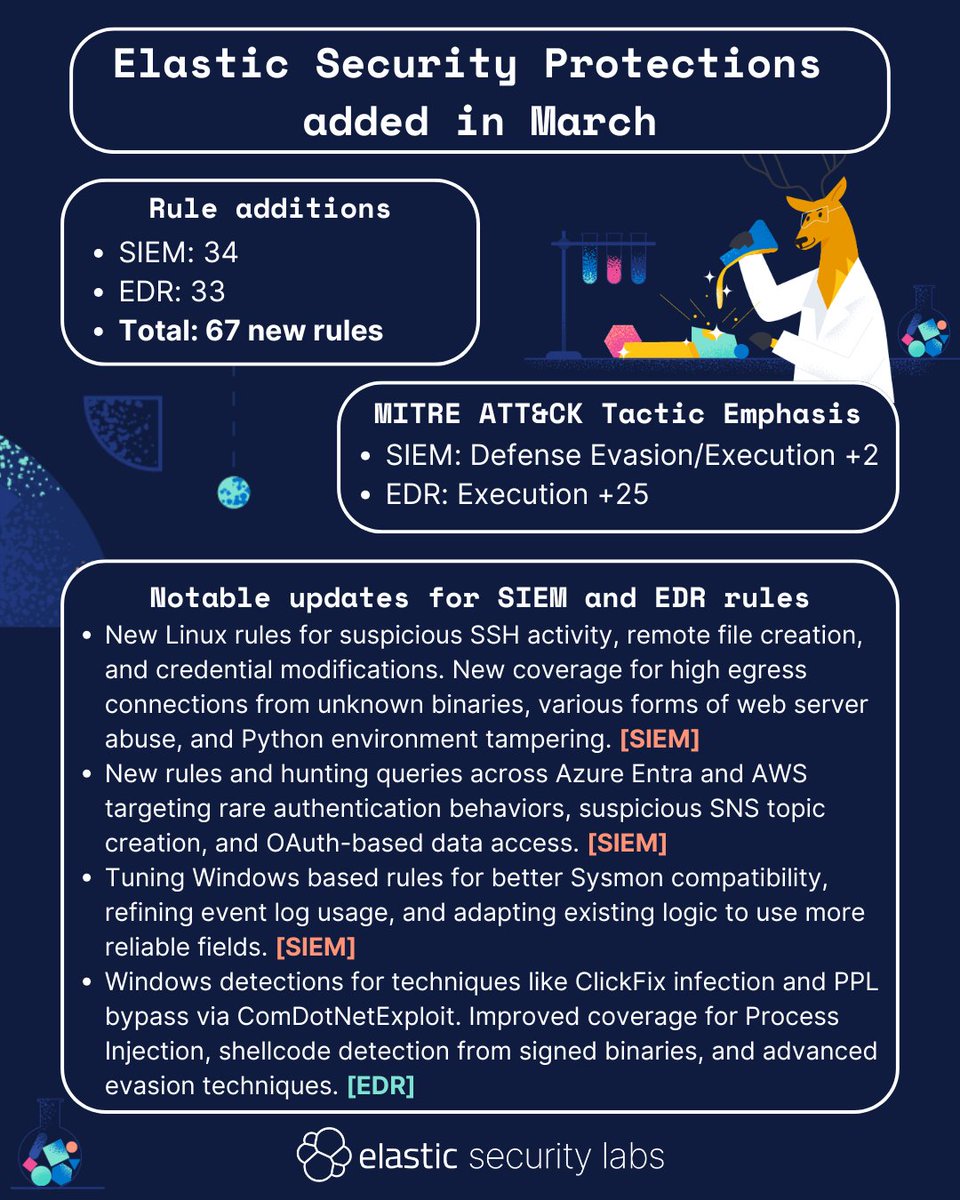
In March, #ElasticSecurityLabs published 67 new rules! Take a look at the overview, or check out our entire library of protections here: go.es.io/42qPQhc
#detectionengineering #SIEM #EDR
English

Introducing Maverc’s Penetration Testing as a Service solution (PTaaS)
Fast, Automated, and Verified by Experts—Pentest-as-a-Service You Can Trust. instagram.com/reel/DFOUUDZvi…
English

🚨 #BREAKING: CHAOS has broken out at the White House Press Briefing as Karine Jean-Pierre REFUSES to say why a world-renowned Parkinson’s expert has REPEATEDLY visited the White House in recent months
KJP is a shameless LIAR
English

Cyber Threat Advisory: A financially motivated cybercriminal organization recently used a zero-day vulnerability in the widely used file compression tool WinRAR to launch cyberattacks against traders and brokers, aiming to steal their digital currency.
conta.cc/3Paj9h9
English
Maverc Technologies รีทวีตแล้ว

🚨More than 40 vulnerabilities were routinely exploited by malicious cyber actors targeting orgs across the globe. An annual fan favorite --> Protect your org by diving into the 2022 Top Routinely Exploited Vulnerabilities: go.dhs.gov/o4a

English
Maverc Technologies รีทวีตแล้ว
Maverc Technologies รีทวีตแล้ว

The ransomware gang claimed the cyber attack on Siemens Energy and four other organizations including Schneider Electric and the University of California Los Angeles.
#cybersecurity lnkd.in/ehJwzvjk
English
Maverc Technologies รีทวีตแล้ว

The agenda is forming, speakers are getting vetted, sponsors are working their process and ICS Miami Training Day is about to announce a number of hands on training options.
Registration:
ICS-Miami.com
@DigitalTrends @INDOPACOM @BlueTeamCon @INL @FIU @Amtrak @NATO_MARCOM @Southcom #Cyber @Grid32InfoSec #OT @razorsecure @ICSSecurityGeek @FLChamberFDN @FLManufacturers @Claroty @TXOneNetworks #ICS #SCADA
Hollywood, FL 🇺🇸 English
Maverc Technologies รีทวีตแล้ว

DreamPort hosted the Joint Cyber Warfighting Architecture (JCWA) technical exchange meeting this week, which examined the need to illuminate capability shortfalls. The keynote speaker was Khoi Nguyen, Command Acquisition Executive and J9 for U.S. Cyber Command.
#cybersecurity

English
Maverc Technologies รีทวีตแล้ว
A critical vulnerability was discovered in the secure file transfer service MOVEit Transfer. The ReliaQuest Threat Research team is monitoring the situation closely. Read more here for what you should know and immediate mitigation steps: bit.ly/3ITx2hE
English
Maverc Technologies รีทวีตแล้ว

GreyNoise has observed scanning activity for the login page of MOVEit Transfer as early as March 3rd, 2023. While we have not observed activity directly related to exploitation, all of the 5 IPs we have observed attempting to discover the location of MOVEit installations were marked as “Malicious” by GreyNoise for prior activities.
greynoise.io/blog/progress-…
English
Maverc Technologies รีทวีตแล้ว

Today Kaspersky announced they were a victim of an iOS zero-click 0day exploit. The exploit delivered spyware targetting Kaspersky middle and upper management.
They named the attack 'Operation Triangulation'
More info: usa.kaspersky.com/blog/triangula…
English
Maverc Technologies รีทวีตแล้ว

Cross-Sector Cybersecurity Performance Goals (CPGs) can help all organizations, regardless of size or industry, prioritize the steps they need to take to mitigate risk of potential threats from sophisticated cyber threat actors. Learn more: cisa.gov/cpg

English
Maverc Technologies รีทวีตแล้ว

The critical infrastructure #cybersecurity one day C-Suite Conference.
Subject matter expert presentations
Use case and solutions from asset owners
Announcing Dr. Michael Mylrea as subject matter expert presenter and moderator.
Website launch is eminent.

English
Maverc Technologies รีทวีตแล้ว

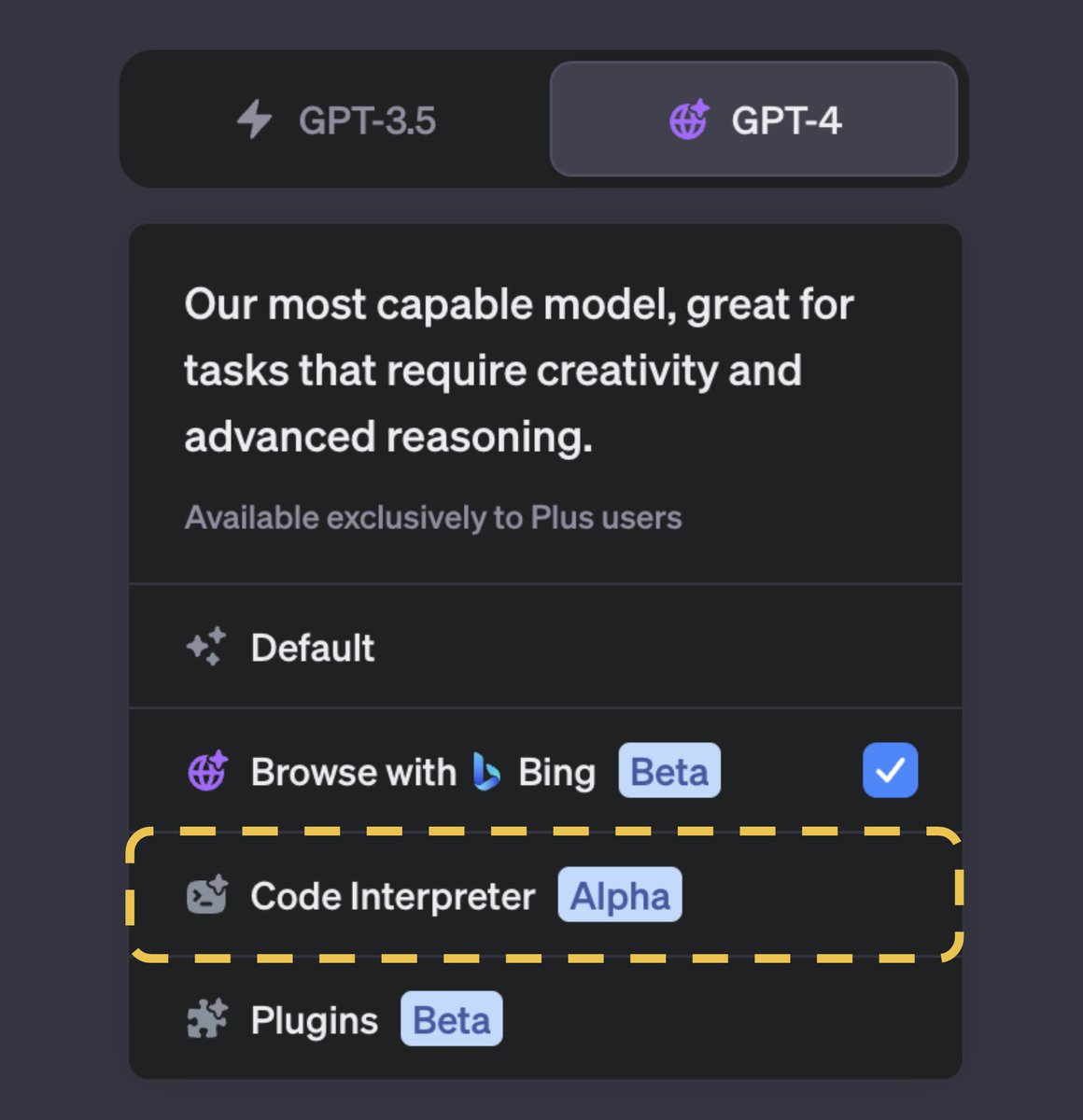
Microsoft announces a new GPT-4 powered AI assistant known as Security Copilot to help with incident response and threat hunting
bleepingcomputer.com/news/microsoft…
English
Maverc Technologies รีทวีตแล้ว
Maverc Technologies รีทวีตแล้ว

Critical #0day in #Outlook fixed.
CVE-2023-23397 exploited by #FancyBear to breach government, military, energy, and transportation orgs.
Reported by CERT-UA so probably used in Russia's war against Ukraine.
The flaw can be used to steal NTLM Hashes of victims.
To cite:
Threat actors can exploit it by sending messages with extended MAPI properties containing UNC paths to an SMB share (TCP 445) under their control.
"The attacker could exploit this vulnerability by sending a specially crafted email which triggers automatically when it is retrieved and processed by the Outlook client. This could lead to exploitation BEFORE the email is viewed in the Preview Pane," Microsoft says in a security advisory published today.
"The connection to the remote SMB server sends the user's NTLM negotiation message, which the attacker can then relay for authentication against other systems that support NTLM authentication," Redmond explains added in a separate blog post.
CVE-2023-23397 impacts all supported versions of Microsoft Outlook for Windows but doesn't affect Outlook for Android, iOS, or macOS versions.
Additionally, since online services like Outlook on the web and Microsoft 365 do not support NTLM authentication, they are not vulnerable to attacks exploiting this NTLM relay vulnerability.
Patches are out so #Patch now!
#infosec #vulnerabilty #news
English
Maverc Technologies รีทวีตแล้ว

Microsoft has released CVE-2023-23397 to address the critical elevation of privilege (EoP) vulnerability affecting Microsoft Outlook for Windows. We strongly recommend all customers update Microsoft Outlook for Windows to remain secure. Learn more ⬇️
msft.it/6018504d4
English