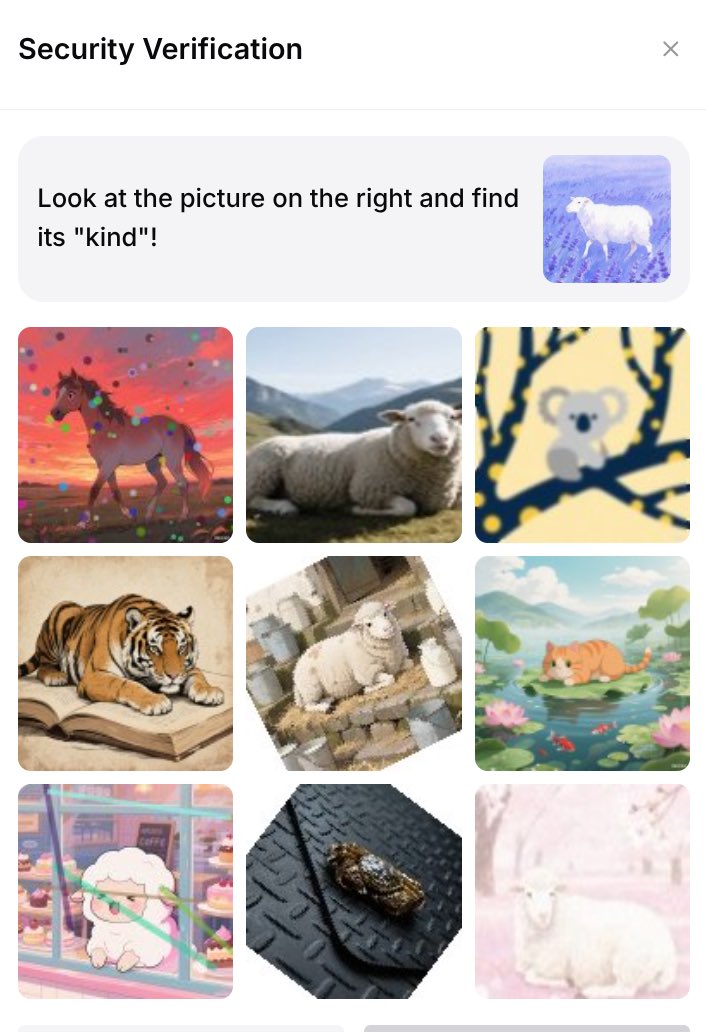
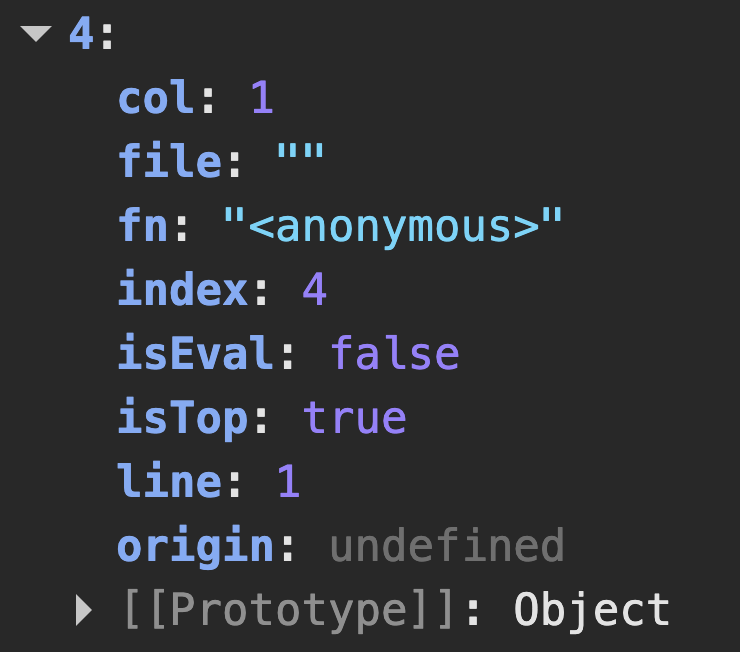
We are publishing the research of Copy&Paste issues in browsers by @SecurityMB. Over $30k in bounties for bugs in Chromium, Firefox, Safari, Google Docs, Gmail, TinyMCE, CKEditor, and others. Includes also 0-day in Froala. research.securitum.com/the-curious-ca…