RealVovochka
1.3K posts

RealVovochka
@TobyFrei4
Decentralization Maxi | On-chain sleuth | Investigator




Balancer Labs to shut down after $128 million exploit; protocol eyes 'lean' restructuring theblock.co/post/394797/ba…

A small thank you to everyone using Claude: We’re doubling usage outside our peak hours for the next two weeks.







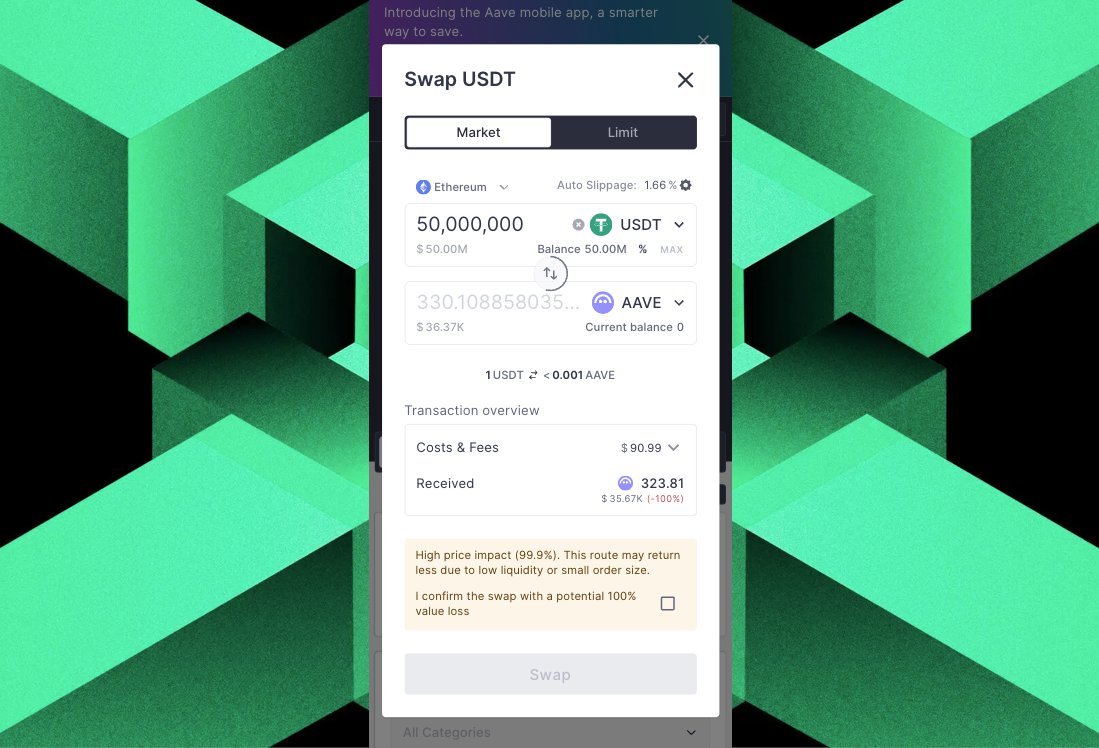
The person who swapped 50.43M aEthUSDT for only 327 aEthAAVE ($36K) may actually be Garrett Jin(#BitcoinOG1011short)! 👀 Evidence:👇 Through on-chain tracing, we found 13 wallets that may belong to him. These wallets: - All wallets received USDC or USDT from Binance on Feb 16 and Feb 20. - All wallets became active again today and moved funds to 2 new wallets. One of these wallets shares the same Binance deposit address as Garrett Jin. Garrett Jin sold 261,024 $ETH($543M) and 11,318 $BTC($761M) on Feb 15 and Feb 20, which is close to the dates when these wallets withdrew stablecoins from Binance. Wallets: 0x98B9D979C33dD7284C854909BCC09b51FBF97Ac8 0x8794C43CEaB422EF4F9397A818B0D5Fa73f9EEac 0x7017dD6E3C604626ADCB95E4e5562356E55442E0 0xAB6efD7ca41E7245573a54afa3Ec16D660Ad0548 0xd7536E10330Af851032102baDA7174910E8f3e5B 0xE197ac9a200A7EA52C0fb2Ab15f8A1f702077bf4 0x651b5943111E0B89216f36be8BC70B75cE0f415b 0xcaE19A19128C4Aabbabc2334613C6b7AE75b1111 0xA71E174Ef86d93573CfD0f18e04808Ebb4f718C4 0xaFec395F6CBeb64e674bd0a0d8c873fd2f97513e 0x315b44f9397b426F8453bB9b22DbcfBEFd3eFFd0 0xBE295544d2C07FcB67CEF20699DfF3Ebc45829e4 0x1AC312360AACf782993CB6E283aC433623f7e8b6 0x1cBa79CF8DD10D0D6cD6f098B34DFc3499377829 0x2E42E686c6444781E110775F2623E895e900AcbF 0x7d09eBF7A43FD3b0427541BA9D762466C9CBfC8A

JUST IN: Trader accidentally swaps $50 million $USDT for $36,000 $AAVE on Ethereum.



This one escalated very fast 🥶. Wallet 0xA5e4F8141Cb2759CeA58F28cF2d0AB21b98580cA came in heavy about 19 hours ago, receiving 1.7M USDC and going straight into a massive short --- 15,457 $ETH , roughly a $31M position. Big size and Clear conviction. But #ETH didn’t cooperate. As price pushed higher, the pressure started building. The position got hit with partial liquidations as the move continued against him. Margin kept shrinking… and shrinking. Now............. That original $1.7M USDC stack has been cut down to just $171K USDC. Roughly $1.53M gone in under 20 hours. High leverage cuts both ways. When you’re right, it feels unstoppable. When you’re wrong… it moves just as fast.














I'm going to one day show this, but their are two Serial rug artists in Crypto. They create a ton of contracts. Their contracts leave their signature marks, the word "beef" or "fed", found typically at the very beginning, in the very middle, or at the very end of their contract.


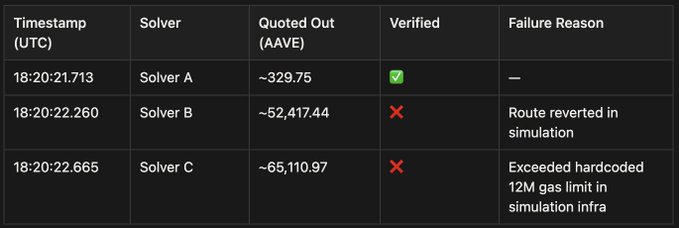
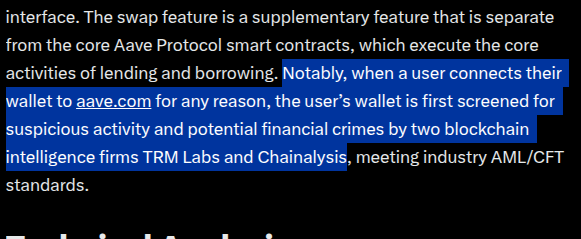
Hey guys, I was sleeping. Really sorry about that. If I’d been awake, I would of course have stopped these funds from going through. 1. Wagyu will never freeze funds. That’s just against everything I stand for. My goal is instead to stop these kinds of funds from ever entering, similar to NEAR Intents or Railgun. Compliance tools are in place to block transactions like these. These just happened to pass because there was no risk score on them for a while from multiple venues. The risk scores eventually kicked in, which is why the transactions stopped and only a small amount went through. Clearly the current protocols aren’t sufficient. I’ll be working to make sure this never happens again.