devvbankx
12.1K posts


devvbankx
@devs_lyfe
I post what I want. @grok Father | Student @WGU ‘28 Cybersecurity and Information Assurance.





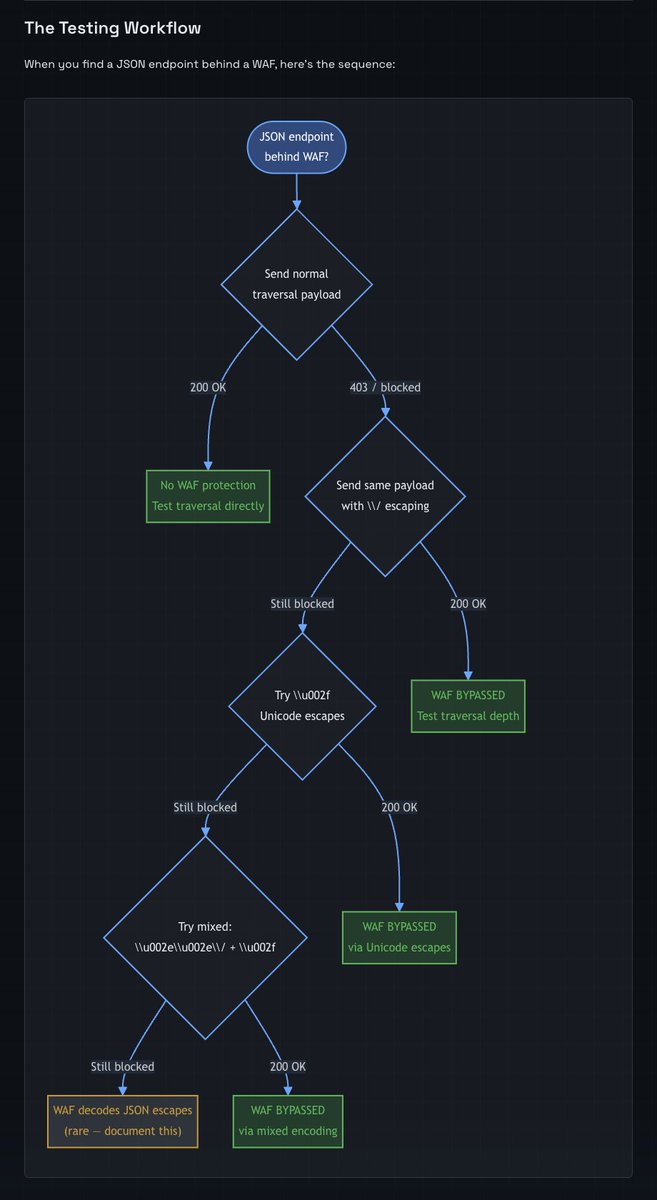

It's Thursday... time for... WAF bypass of the week! Every major WAF — Cloudflare, AWS WAF, Akamai, Imperva — inspects the raw HTTP request body for attack signatures. Every JSON parser normalises escape sequences before handing data to the application. These two facts create a gap that’s been sitting in the JSON spec since 2006. The gap is one character: \/ labs.trace37.com/blog/json-esca…


@elonmusk So far Grok is the most based AI tool


@PortSwigger is dead wrong for this one. Making a claim that allowing people to BYOK for AI does not do shit for your own AI policies, if anything it would make it easier for you to abide by them since you offload the responsibility to the user and not yourself. It may be time to start thinking of using something other than Burp if they are going to force you to use their shitty AI instead of something that works well.