ทวีตที่ปักหมุด
w1j0y
1.5K posts


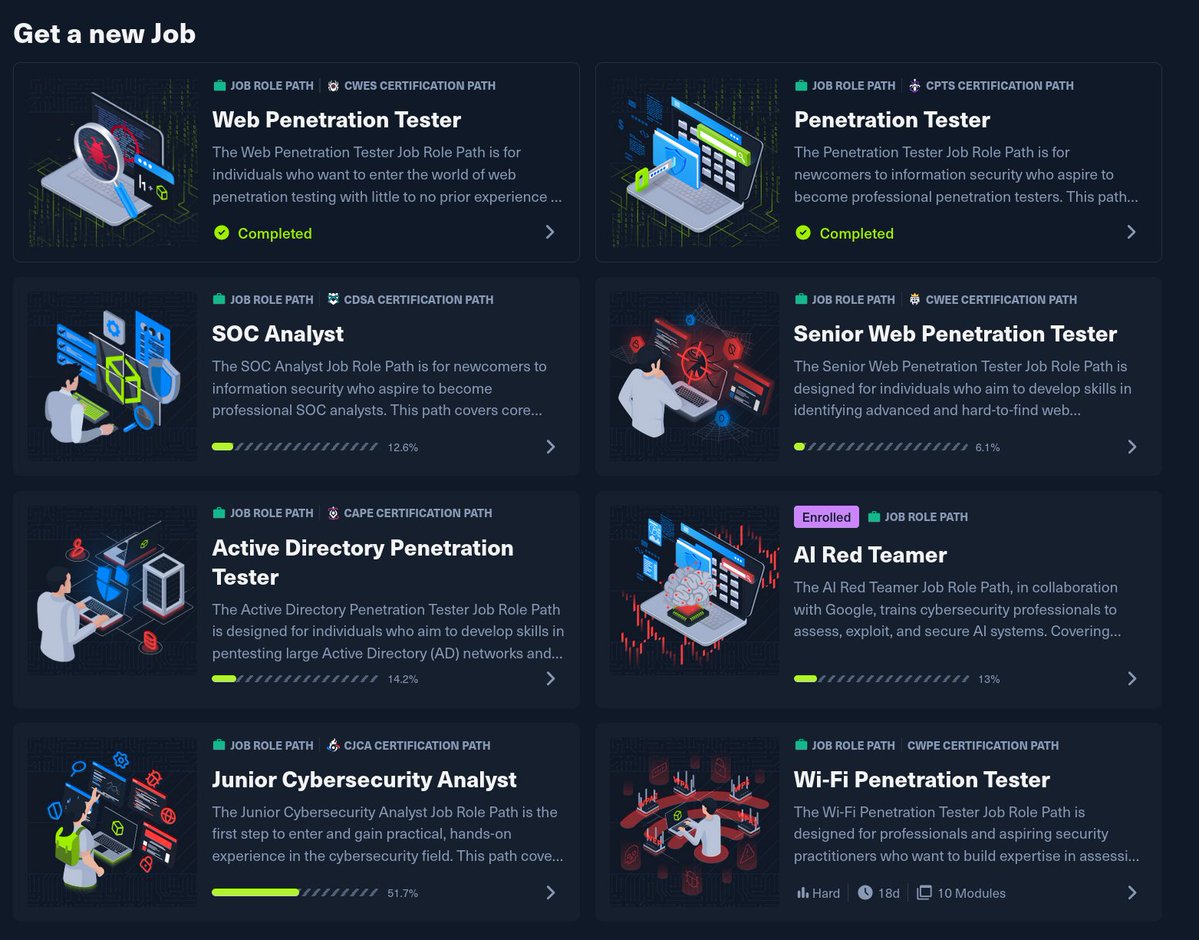
w1j0y
@runyourcron
Security Researcher | CPTS | CWES Penetration Tester - External & Internal Networks, Web Apps Founder @ rycron - AI Automation for SMBs [email protected]
เข้าร่วม Ocak 2013
690 กำลังติดตาม102 ผู้ติดตาม

Just endorsed .agent—keeping it open and not owned by one company. If you build with AI agents: @agentcommunity_ agentcommunity.org
English
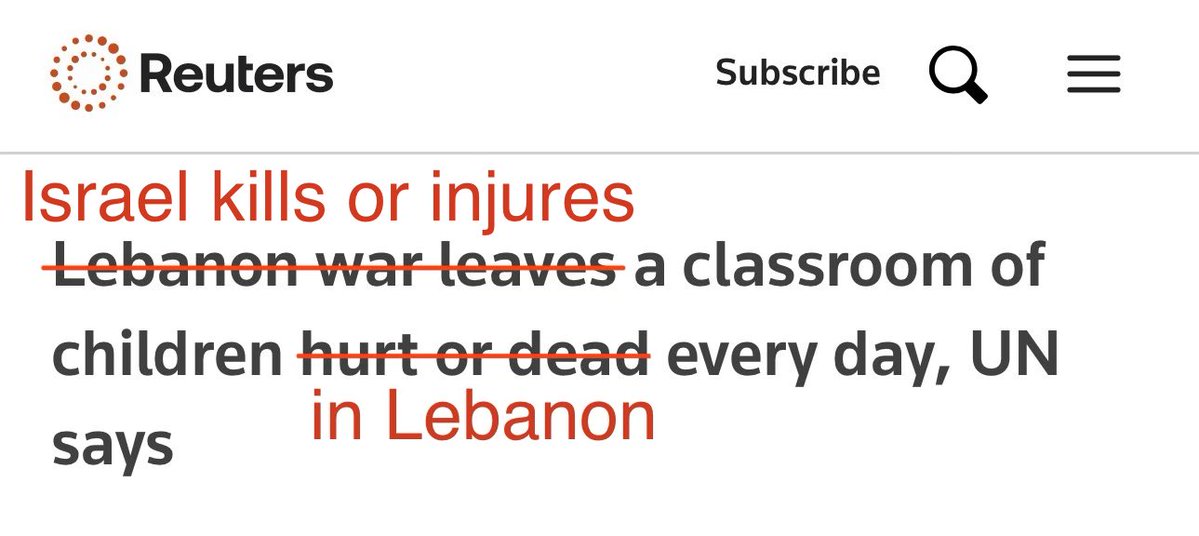
w1j0y รีทวีตแล้ว

Been spending the past few weeks deep in AI agent security research. Found multiple critical vulnerabilities across major AI platforms including RCE on production infrastructure and a novel cross-application attack chain that hasn't been documented before.
All findings responsibly disclosed. Reports pending.
Detailed writeup coming after patches are deployed.
English

Spent the day doing AI red teaming, testing how AI browsing agents handle untrusted web content.
Built a custom test lab, crafted multiple payload pages, and tested 6 major AI agents for indirect prompt injection
vulnerabilities.
Results: 4 security reports submitted to vendors through their official bug bounty/VDP programs. One finding achieved
full server-side data exfiltration, an attacker-controlled webpage caused an AI agent to transmit user PII to an external server, completely invisible to the user.
AI agents that browse the web are the new attack surface. The arms race between injection and defense is just getting started.
English

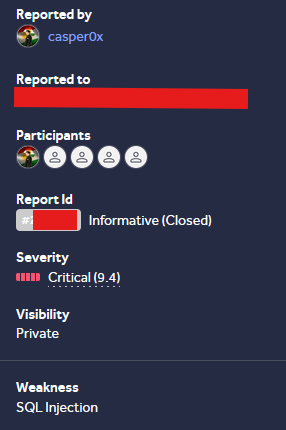
SQLi allowed database enumeration and dumping, Still a bit weird the report was closed as Informative
sqlmap -r r.txt --eval="import base64; payload_part='select 1 where 1=1'; GUID='x%27 or length(payload_part)=0'; del payload_part"
#bugbounty #sqli #hackerone #bugbountytips
English

I made close to $10,000 from bug bounties this month. I'm 19. Still in engineering school.
Here's what I didn't show you.
I found a Critical RCE — Remote Code Execution via path traversal on a company's server. The kind of bug that pays $5,000-$20,000.
Duplicate. Someone found it 12 days before me.
$0.
Same work. Same skill. Same report. Wrong timing.
That's one of dozens. For every bounty I post, there are 15+ reports that got:
→ Duplicated
→ Marked informative
→ Ignored for months
→ Closed as "not applicable"
→ Lowballed after months of follow-ups
But you know what I do when that happens?
I wake up. No emotion. No hate. I open Burp Suite. Next target. Next report.
Because if I don't, someone else will. Every day I take off is a day someone else dupes me on the next find. So I show up. Even when I don't feel like it. Even when it hurts.
Bug bounty is not "find bug, get paid." It's find 50 bugs, fight for 6, get duped on some of your best work, get ghosted on others, and still show up the next morning.
The $10K months are real. But behind every mountain is a hundred steps nobody sees.
If you're starting out and getting duped and rejected — that IS the path. You're not doing it wrong. You're doing it.
Keep going.


English

@pietrobaudin Anyone else felt normal is ChatGPT logo and Pro is Claude, or is my brain damaged
English
w1j0y รีทวีตแล้ว

For this cycle of destructive distractions from the Epstein files to be over, we need to credibly demonstrate that we will not let pedophiles get away with it.
If there's a demonstration this weekend, or any weekend, I will attend and I hope you will, too, until we get rid of every single child molesting monster in office.
English

Use Tosint when you need to gather intel on a Telegram bot tied to a phishing campaign or malware operation. It gives you insights into the bot's identity and capabilities quickly, saving time on manual checks.
github.com/drego85/tosint
English

When you need to test an application’s defenses, use this tool to create specific payloads without deep knowledge of shellcode. Save time during your pentesting workflow.
github.com/D3Ext/Hooka
English

Using this means you can easily integrate and customize tools in Golang for your engagement. It's useful when you want to adapt existing tools to meet specific needs in a testing scenario.
github.com/Enelg52/Offens…
English