cogio
404 posts


cogio
@CyberDevOG
building @BreachLens (BEC forensics for M365) cybersecurity nerd who ships learning in public, breaking in private python stdlib only, zero dependencies
the internet Sumali Haziran 2024
43 Sinusundan37 Mga Tagasunod

@ZackKorman yeah this is the failure mode i keep designing around. i'm wiring agents into M365 audit logs for BEC triage and half the work is keeping the attacker's own email body from steering the agent. tight tool scope + structured output + classifier on inputs — still feels thin.
English

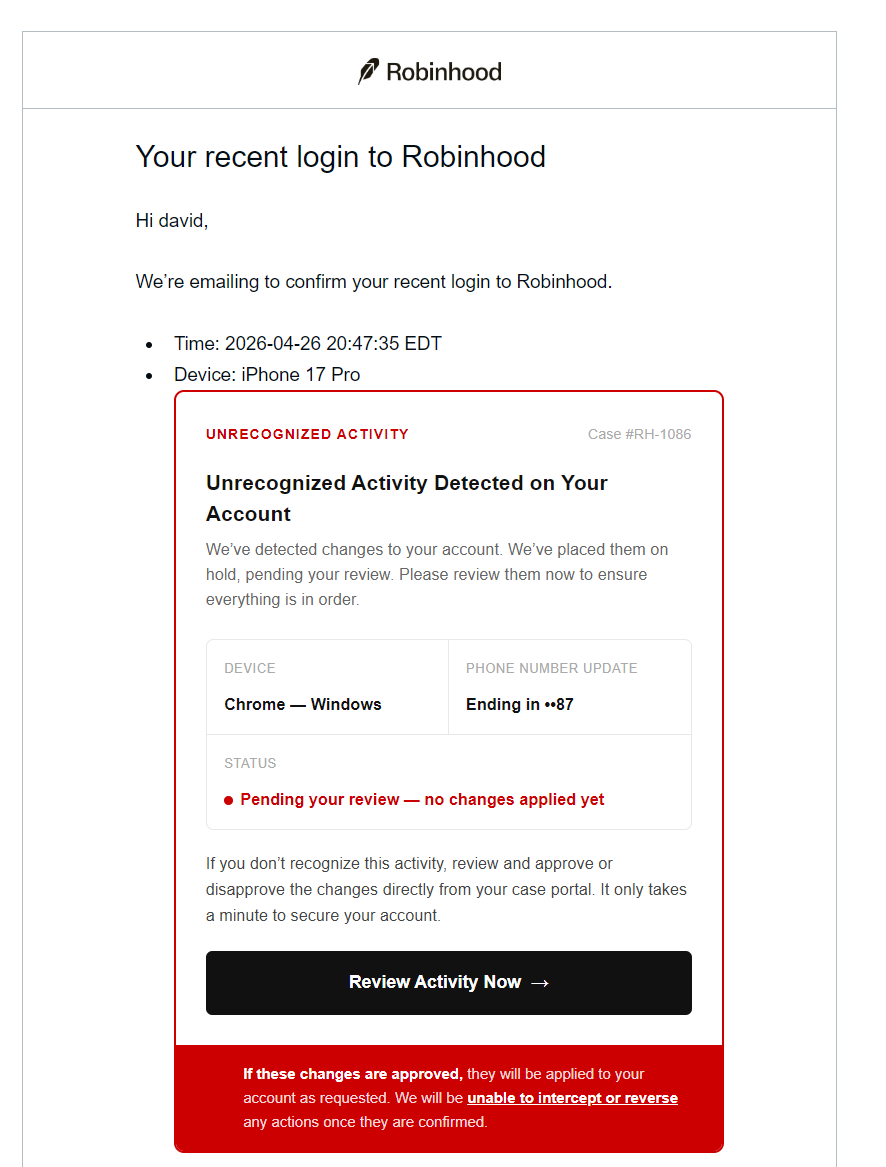
Now imagine the damage a threat actor can do by prompt injecting your AI agent.
JER@lifeof_jer
English

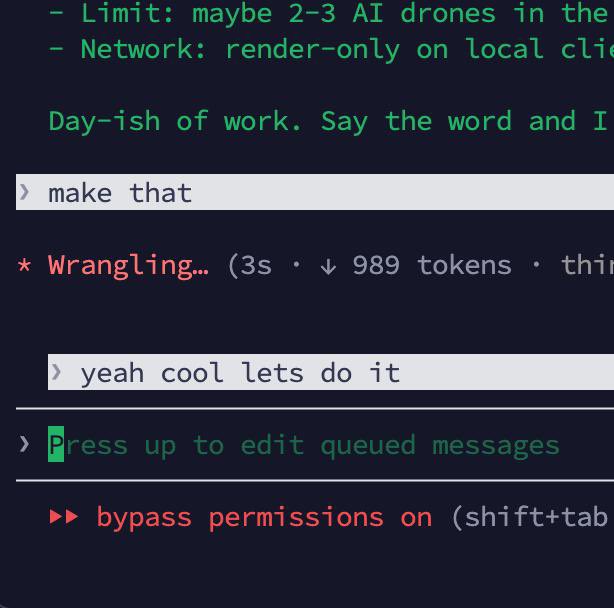
@staskulesh the leverage isn't claude writing code — it's me getting better at writing the prompt. half my repo is now /commands and skill files instead of source.
English

@JoelKatz the gnarly part of this one: SPF/DKIM/DMARC all pass clean because the email IS coming from RH's infra. authentication checks tell you nothing here — detection has to move to content/behavior (weird device names, html in fields, suspicious account-creation patterns)
English

@munza14 @NikkeiAsia tradecraft is brutally consistent — forwarding rule, forged invoice, dual-approval skipped under deadline pressure. the part that never makes headlines is the triage after. pulling months of UAL across dozens of mailboxes is why i built breachlens.io
English

For @NikkeiAsia, I write how a $2.5m cyber heist doesn’t happen in a vacuum. It happens when warnings go unheeded, controls lag and governance fails.
The Sri Lanka Treasury breach is a wake-up call on the cost of ignoring expert advice.
asia.nikkei.com/spotlight/cybe…
#LKA #SriLanka
English

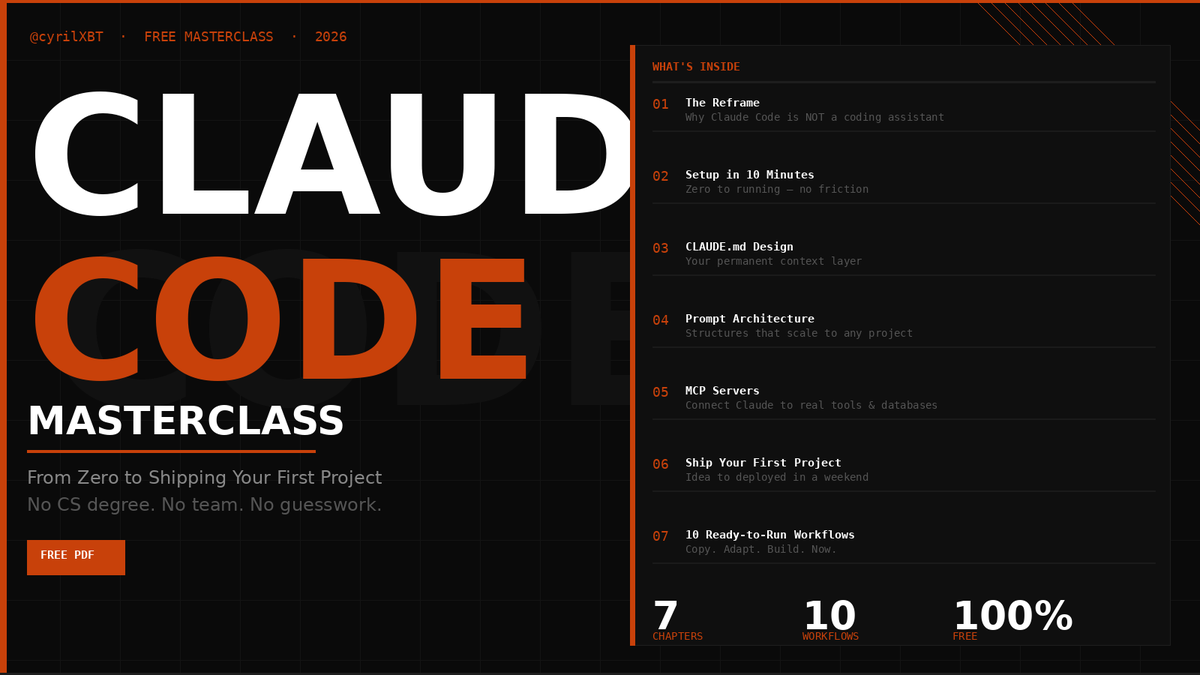
I spent 6 months learning Claude Code the hard way.
Every mistake.
Every workflow that did not work.
Every prompt I had to rewrite 10 times before it clicked.
I turned all of it into a free masterclass:
THE CLAUDE CODE MASTERCLASS.
Zero to shipping your first project alone.
No CS degree. No team. No guesswork.
Inside you get:
- The reframe that changes how you use Claude Code forever
- The CLAUDE .md template that makes every session 10x more powerful
- The 4-layer prompt architecture that scales to any project
- MCP server setup nobody is teaching yet
- The 6-phase sequence to go from idea to deployed in a weekend
- 10 ready-to-run workflows you can copy right now
The people who read this tonight will be building things next week that most developers still cannot do with a team.
I should be charging $199 for this.
It is free.
Comment CLAUDE and I will send it to you directly.
RT if you know someone who needs to see this.
English

@NoahEpstein_ sqlite + fts5 over your own message history beats most rag setups for personal context. been doing the same with IR notes — grep wins 9/10 times for "where did i write that thing about oauth consent grants"
English

everyone's still arguing about vector DBs like agent memory is some unsolved problem.
steipete just shipped 3 tiny CLIs that dump your full X, discord and whatsapp history into local sqlite with fts5 search.
- birdclaw: your X (tweets, dms, mentions, archive)
- discrawl: any discord server you can read
- wacrawl: whatsapp desktop chats
no embeddings. no RAG. no subscription. just sqlite + fts5 (the same thing your phone uses to search imessage).
each one is a single binary. brew install. done.
i'm putting birdclaw on the mac mini today. my writer-agent has been drafting takes i already posted because it has zero memory of what i've actually said. now it can grep my full archive in 50ms before every draft.
the move isn't the tools, it's the shape. one tiny crawler per data source, all dumping to local sqlite. notioncrawl, telegramcrawl, gmailcrawl on the same recipe.
Peter is just dropping dimes every other day.
Peter Steinberger 🦞@steipete
the crawl army so agents can read it all.
English

@SCMagazine @Mimecast tracks with what shows up post-compromise in M365. once they're in, the tradecraft is boring and identical: inbox rules, oauth app grants, MailItemsAccessed bursts. "targeting people" is the right framing for prevention but the IR signal lives in the audit log.
English

Insider threats, credential misuse, and user-driven errors now account for the majority of incidents, with attackers increasingly targeting people rather than systems, according to @Mimecast's 2026 State of Human Risk report. #cybersecurity #CISO #infosec bit.ly/4sZn4iX
English

@HuntressLabs the AWS+CF infra angle is what guts most IP/ASN-based detections. once token replay lands you're chasing it in UAL — OfficeHome appId + new device + fast MailItemsAccessed. been writing my BEC triage flow around exactly this signal at breachlens.io
English

@realsohamparekh yeah these are getting really polished. same template hitting m365 tenants right now too — once someone consents to the "appeal" oauth app, mfa is already bypassed and there's nothing in the inbox to investigate
English
Another OAuth phishing scam. OAuth phishing scams have been really on the rise!
himanshu@himanshustwts
Your X acc can be compromised in uncountable number of ways and here's the new one. I received this email 3hrs ago. See the email. And the funniest thing is my email which is mentioned here is wrong by a single digit. LMAO. be aware bros and don't really login in any case when asked.
English

@c7five the fake-invoice version shows up in BEC cases too — victim wires the bad invoice, days later a "recovery firm" emails offering to claw it back for a fee. same crew. sometimes the original mailbox forwarding rule is still live and they're reading the recovery thread.
English

A scam blowing up this year that nobody warns you about: the recovery scam. Here’s how it works.
You get scammed once. Crypto, romance, fake invoice. Doesn’t matter. You realize, you panic, maybe you tell the scammer “I’m calling the cops.”
They record that call. Then they wait 4 to 8 weeks.
Then a “police officer” calls. Or a “lawyer.” Or someone from a “consumer recovery agency.” They know specific details about your scam. Because they ARE the people who scammed you.
They offer to help recover your money. Just need an upfront fee. Gift cards work great, apparently. Or more crypto as a “recovery bond.”
Rule: Anyone who contacts YOU first about money you lost is the scammer. Government agencies and law enforcement do not work this way. Ever.
Share this. Send it to anyone who might be vulnerable to getting scammed TWICE.
English

@techspence yeah this. weirdly it's almost always the people who ship the least who are loudest about code quality. most prod code I've seen anywhere is duct tape, 2am decisions, and a test file nobody opens.
English

I sometimes defend open source stuff that’s “vibe coded” because like why does it matter?
The common argument is something along the lines of “they don’t know what the code does. They don’t know the code quality.”
How many people who have written any code have been 100% satisfied with the code they wrote?
Stop demonizing technology.
English

proper safeguards = audit logging on, alerts on new inbox/forwarding rules, dual-approval out-of-band before any wire. once it lands, the UAL + headers + login telemetry are the entire investigation. (kinda why i started breachlens.io — that triage by hand at 1am is brutal.)
English

Cybersecurity expert Asela Waidyalankara says the recent $2.5 million Treasury cyberattack, carried out using a Business Email Compromise (BEC) method, could have been minimized with proper safeguards.
He noted that while Sri Lankan banks follow strict standards like ISO 27001, similar controls appear lacking in institutions handling public funds, highlighting gaps in cybersecurity management and oversight.

English

@NewsWireLK spot on. most BEC i investigate has zero "hacking" — usually a forwarding rule the user never noticed, an invoice that looks legit, and a payments person under deadline pressure. catch isn't EDR, it's dual-approval + out-of-band callback before any wire change.
English

“Don’t insult hackers — this is not hacking. It falls into a different category. This is what we call a Business Email Compromise (BEC), a very simple impersonation technique,” Sarvajana Balaya leader Dilith Jayaweera said, adding that the Treasury fund compromise has caused serious damage to the country’s reputation.
English

@HackRead the patch is the easy part. the harder question: are tenants actually going back through their UAL to see if this got abused before the fix landed? service principal credential adds disappear into normal admin noise — that gap is exactly why i built breachlens.io
English

📢⚠️ Microsoft Entra Agent ID flaw allowed privilege escalation and tenant takeover via Service Principal abuse, now fully patched by Microsoft.
Read: hackread.com/microsoft-entr…
#CyberSecurity #Vulnerability #Microsoft #MicrosoftEntra #AI
English

Introducing: Browser Use Box (bux). Your 24/7 personal agent box, powered by Browser Harness. ♞
We got tired of agents that vanish when you close the laptop. So we put them on a server.
> 24/7 box that runs while you sleep
> Real Chrome with persistent logins
> Telegram baked in, text from anywhere
I gave mine my email and a Telegram chat. It books flights, replies to LinkedIn and does my to-do list before I'm awake.
Try it at cloud.browser-use.com/bux ↓
English

@arvidkahl hard agree. been writing my IR runbooks in .md for exactly this reason — me and whatever LLM i hand the case to parse it the same way. structured prose is the new API.
English

Markdown hits the exact middle-ground between human and machine. Clean enough to be parsed by the brain, structured enough to be meaningful to the machine.
XML, JSON, HTML failed for humans. Raw text failed for silicon.
.md will be a marker of a hybrid age.
tobi lutke@tobi
Everything is markdown now and it will likely be an important part of the rest of human history. @gruber must think this is extremely funny.
English

@dvassallo passkeys shipped on a vibe-coded racing game outpaces 80% of b2b saas auth i've seen in IR. the second you commit to webauthn the phishing-resistance debate just disappears. nice work.
English

Added passkey support to fullsend.game so if you claim your account you can login with touch/face ID from any device.
Add your passkey by clicking your account button from the top right.

Daniel Vassallo@dvassallo
6,000+ players. Map getting fuller. Big graphics update coming later today. 👉 fullsend.game/stats
English