Spence
6.4K posts


Spence
@SecEventsPen
Cyber Geek, Pentester, Social Engineer & all round awesome guy! Should have been in the Avengers, but all the spots were taken! Views/opinions are my own 🙊

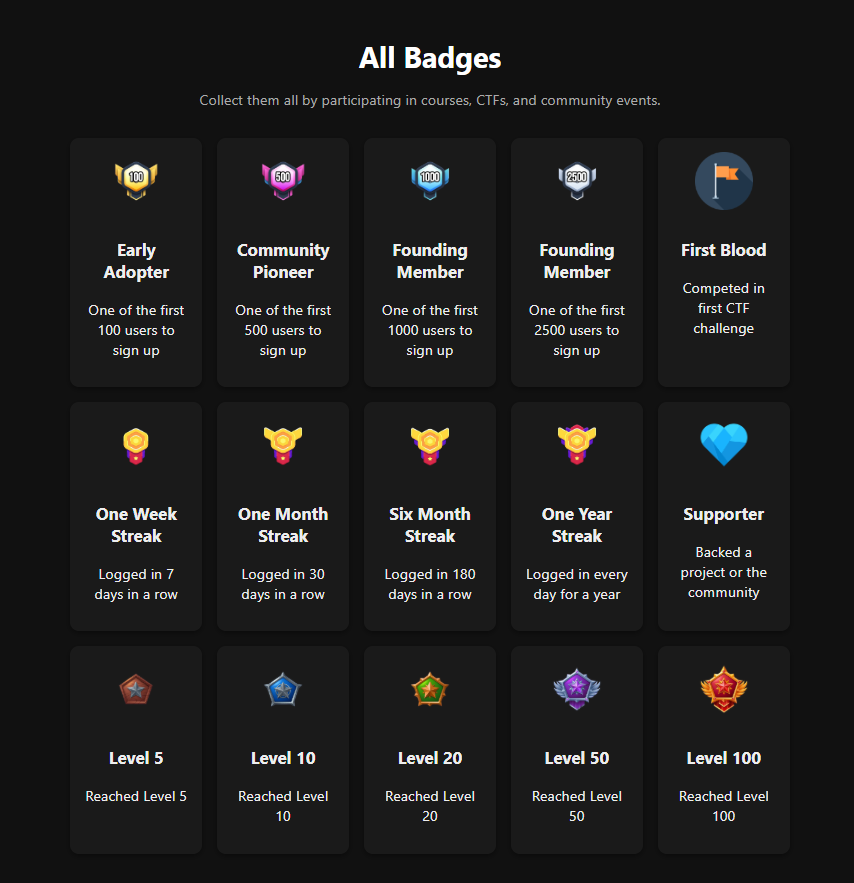
Today is the day and I'm sorry it's been so long, and also provisionally delayed by nearly a week. lms.zsec.red launches today with my Malwareless Adversarial Emulation (MAE) course. If you signed up for the waitlist, you should have received an email.


Today is the day and I'm sorry it's been so long, and also provisionally delayed by nearly a week. lms.zsec.red launches today with my Malwareless Adversarial Emulation (MAE) course. If you signed up for the waitlist, you should have received an email.



NEW: Cocospy, Spyic and Spyzie, the stalkerware apps that were breached earlier this year and caught spying on millions of people's phones, now appear to have shut down. The apps not working, their websites gone, and Amazon-hosted cloud storage deleted. techcrunch.com/2025/05/19/coc…

TIL My name is actually Jane Doe according to @Balaji_GBH where @The_Cyber_News have ripped my blog post word for word blog.zsec.uk/commit-stompin…




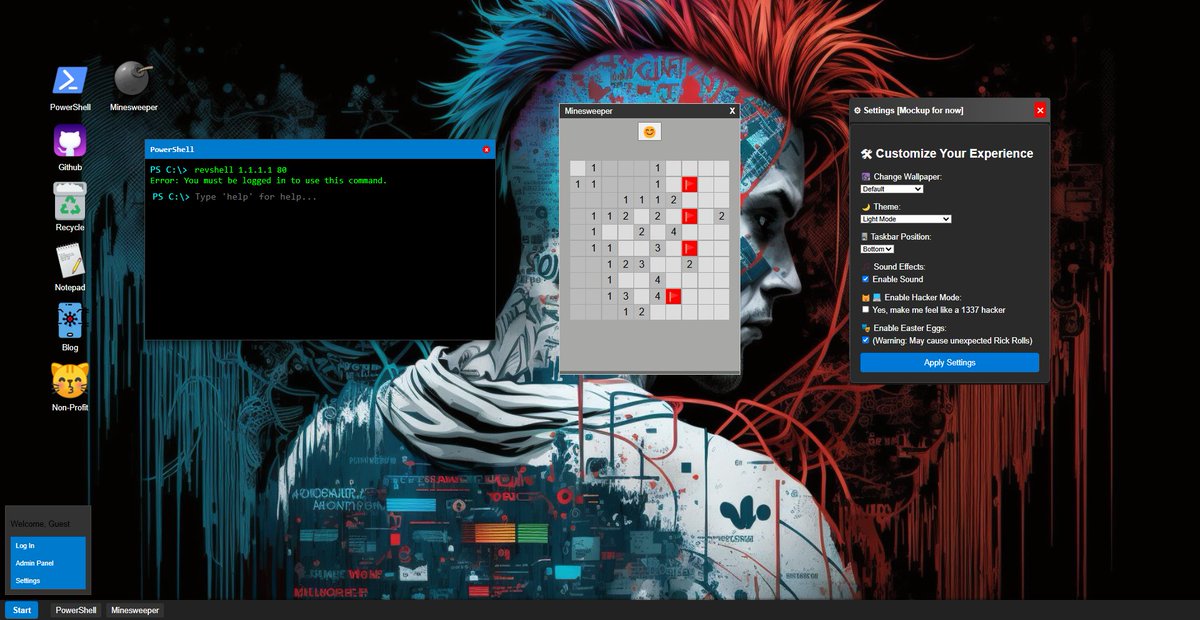







Jakoby you can't turn everything into a Powershell 1 liner under 259 characters... what if you want to enumerate subdomains? You have to use a tool like Amass... BET. we'll make google do it for us Code in ALT text 😉 (change website as desired)