Br*an
16.3K posts

Br*an
@SecurityCollins
☁️ security, general technology fan • opinions = mine




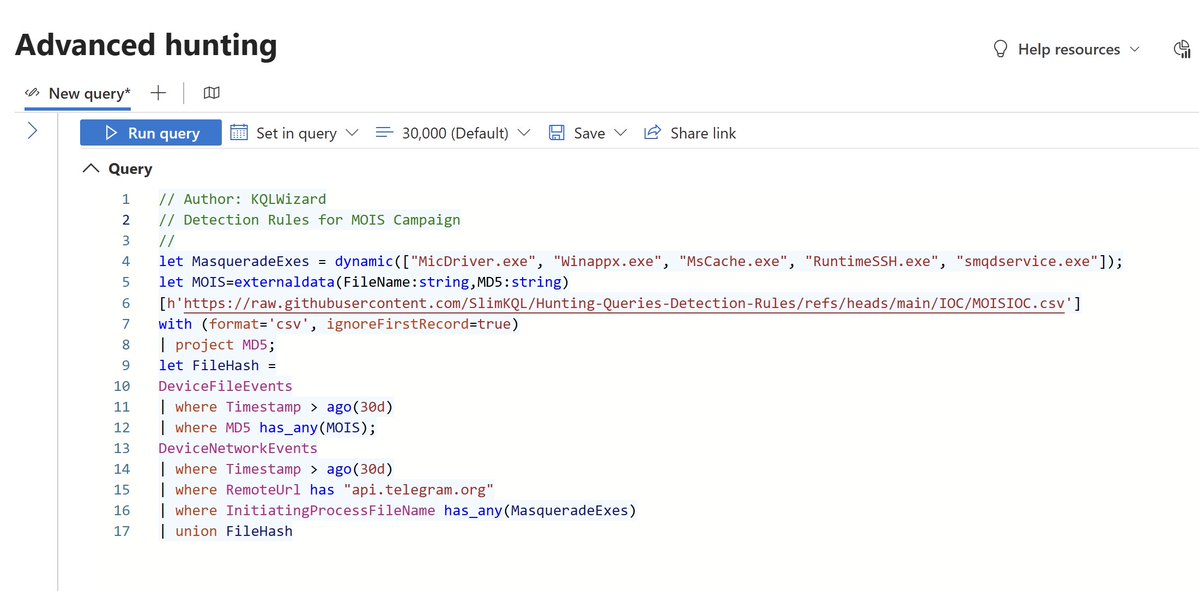
THREAD: (1/13) A foreign-linked influence network has been running coordinated operations against the Trump administration for 22 months. I know it's real because they ran one against me. I was targeted in something I knew was far from organic. This level of media is isolating, unwanted, and unwarranted. There was nobody to help, nobody to jump in and say, this is a false OP and help me. Well, I don’t believe in problems without solutions, so I’ve spent the last few months learning to build programs to utilize publicly available information to prove that this is way bigger than me. This is about creating chaos in the Republican Party. It's about the organized effort to lose Republicans the midterms and subvert President Trump's agenda, and I have the data for you to see 🧵




I need a GitHub too! Is it like that or nah?



Here is Jay Leno driving the new redesigned @Tesla Semi. He is the first person outside of Tesla to drive it. @danWpriestley: "This truck from an energy standpoint is 50% cheaper to run here in California. Across the US, we're 20% cheaper on a per mile basis, and that's inclusive of everything, not just energy, whether that's reduced maintenance, fuel." via @LenosGarage





🚨 “I Pushed him TWICE... Then He Kicked the Crap Out of Me" – Neighbor Breaks Silence on Viral Beatdown Ronnie Taylor, the guy "Reacher" star Alan Ritchson beat up explains how the fight started in the first place. “I did push him because he was coming towards me on his bike. He did it again a second time. I pushed him a second time, then he got off his bike and kicked the crap out of me.”