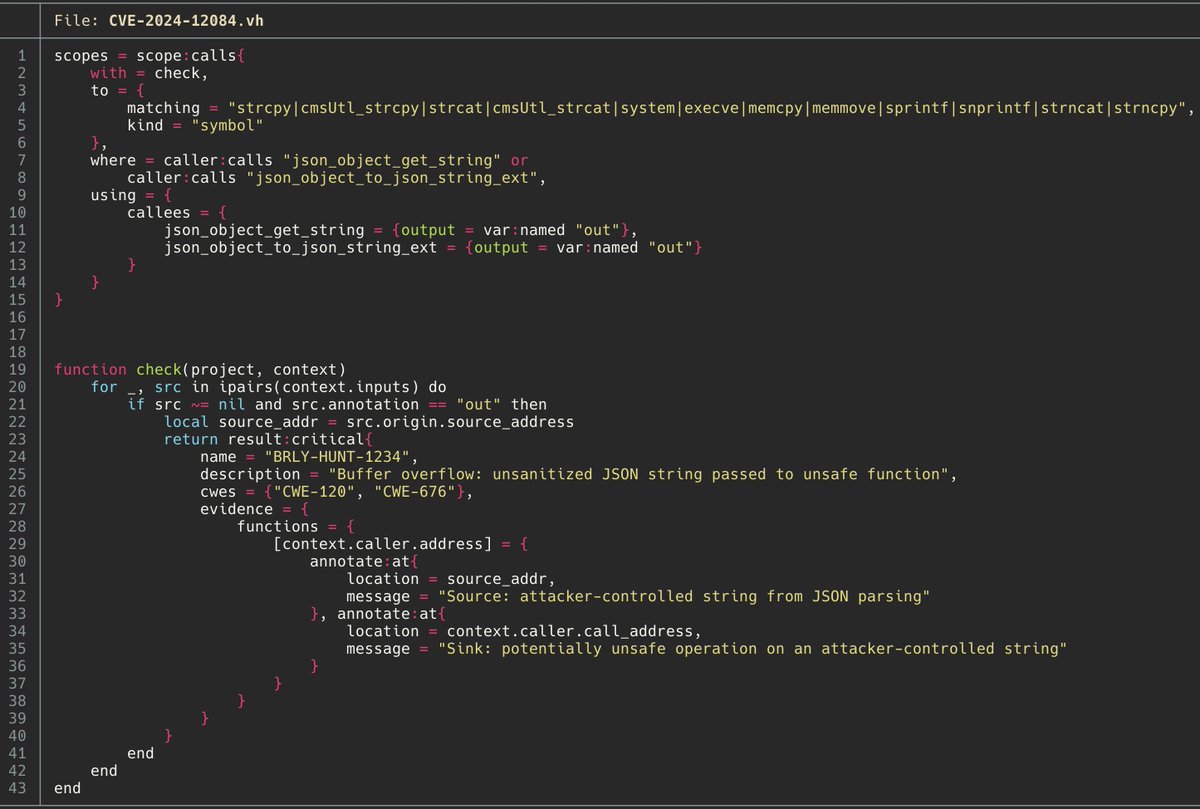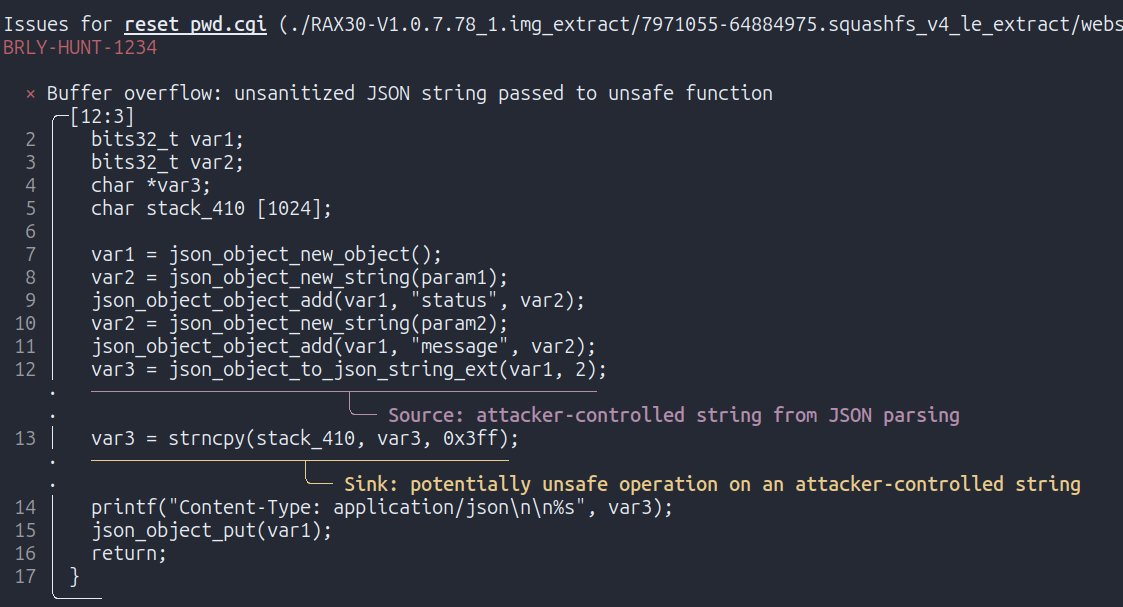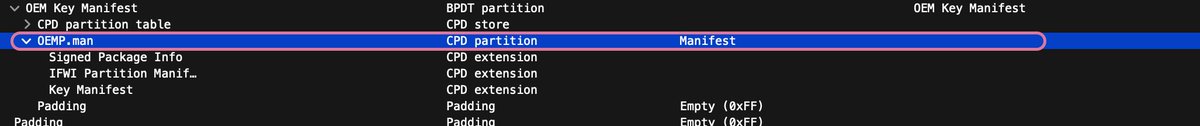
⛓️Digging deeper into the aftermath of the @msiUSA data breach and its impact on the industry. 🔥Leaked Intel BootGuard keys from MSI are affecting many different device vendors, including @Intel , @Lenovo, @Supermicro_SMCI, and many others industry-wide. 🔬#FwHunt is on!