DefSecSentinel retweeted

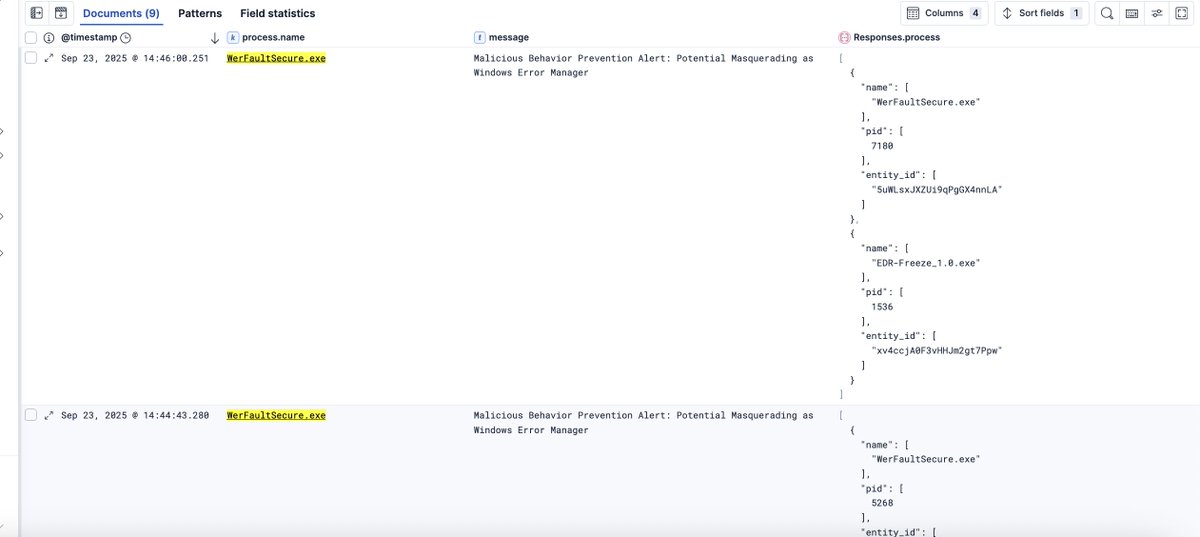
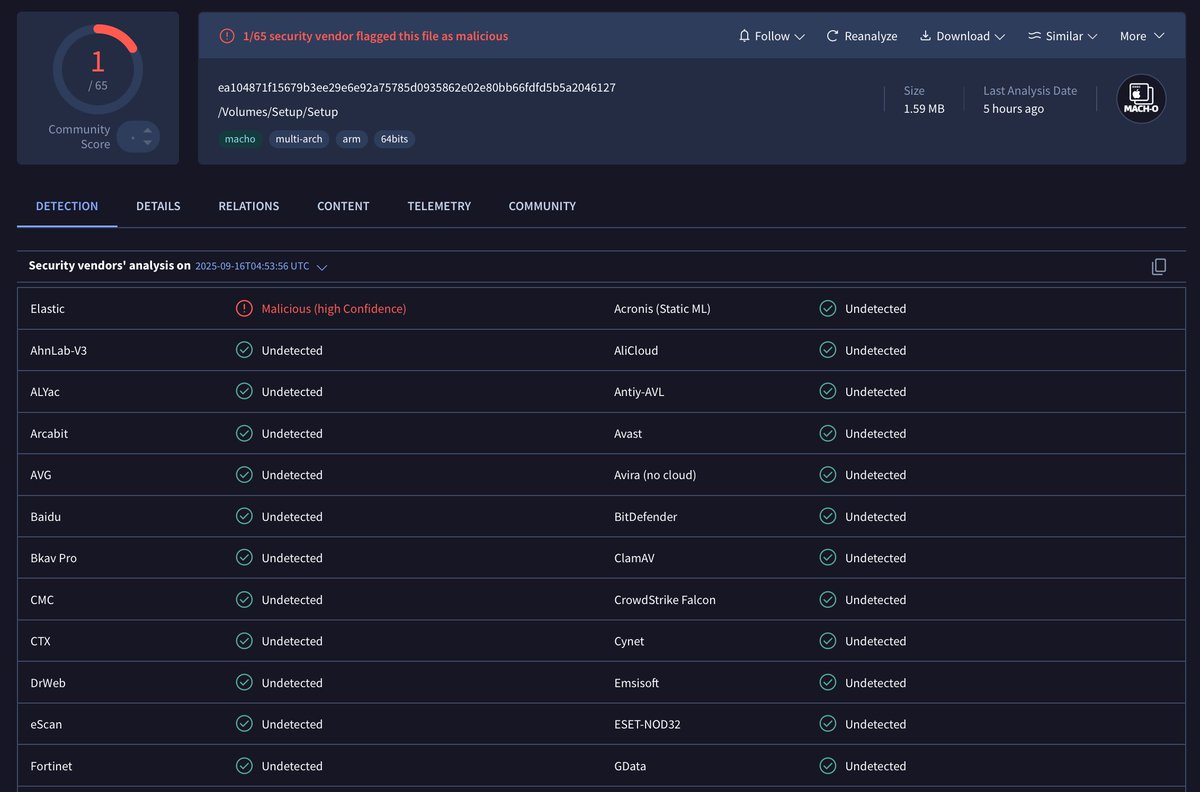
Jamf Protect + Elastic Security = macOS XDR done right.
Ingest Jamf Protect telemetry, normalize it to ECS, and investigate with AI — all without leaving Elastic.
What's included:
- Prebuilt Jamf Protect detection rules
- AI Assistant for alert explainability & response plans
- Timeline & Analyzer for full attack reconstruction
See how it works
go.es.io/4bjFOnF

English