The Android root advocate
4.2K posts

The Android root advocate
@666archhwh
Android Enthusiast Modder who only cares about rooting and modding and so it's against companies and institutions who not allow it or oppose to it
apparently disclosing security vulnerabilities with benign PoC exploits that work as described is now against the rules this policy will kill the infosec community on this site

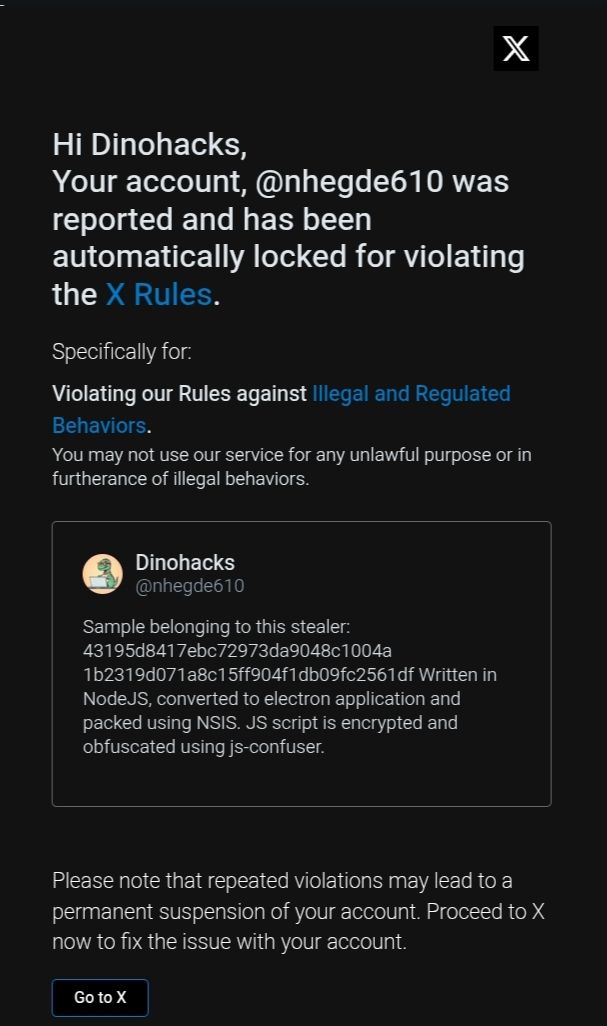



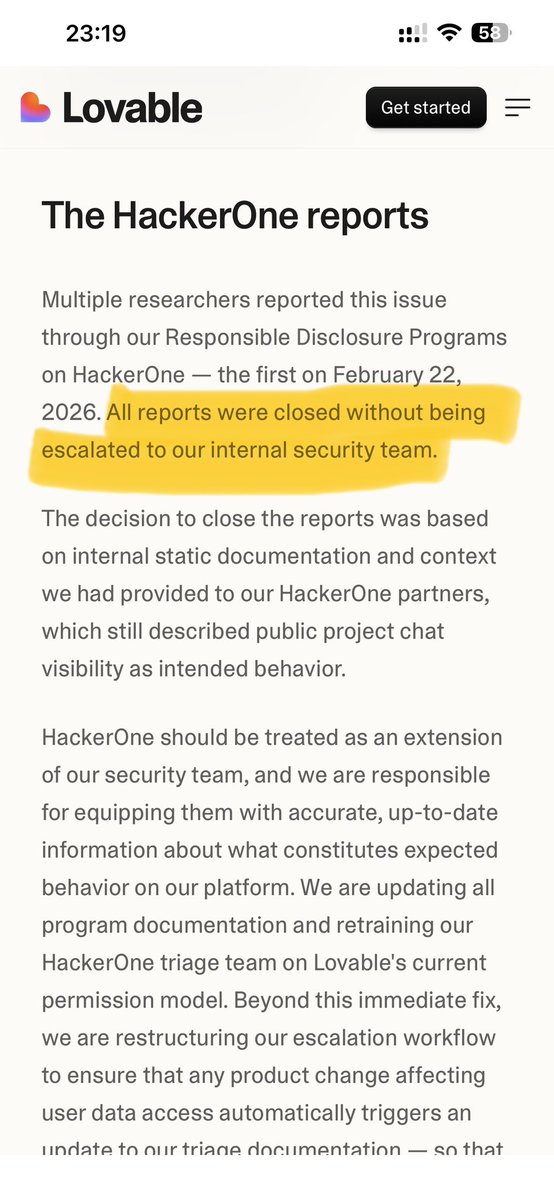






this man called me blackhat on his timeline to 71k people. in the dms he told me he's "not claiming i released some secret technique" so which is it? he had the platform to help get this fixed. contact the company, escalate the report, connect me with the right people. instead he chose to start a public fight over disclosure timelines and guess what? the company rotated the key. 25 days of private emails got nothing. one public tweet got it fixed. Joseph Thacker you know what you was doing when you made this post, you are a grown man instigating tl wars isn't there anything else you could be doing with your time right now?