Adam Kohler
1.7K posts

Adam Kohler
@AdamJKohler
Father | Husband | macOS Detection Engineer and Malware Researcher




Last week we piloted our "macOS Vulnerability Researcher" training with @gergely_kalman privately at @officiallyiru . We delivered the training for our entire Threat Intel team, and some of our Solution Engineers. It was super cool, all the students were amazing and we had plenty of interactions. We, as trainers also learned a lot. We are looking forward now to our first public offering, which will be in Seoul, South Korea, at Zer0Con. This will be the only training this year in Asia, and there are still a few places left, if you are interested you can sign up here: zer0con.org
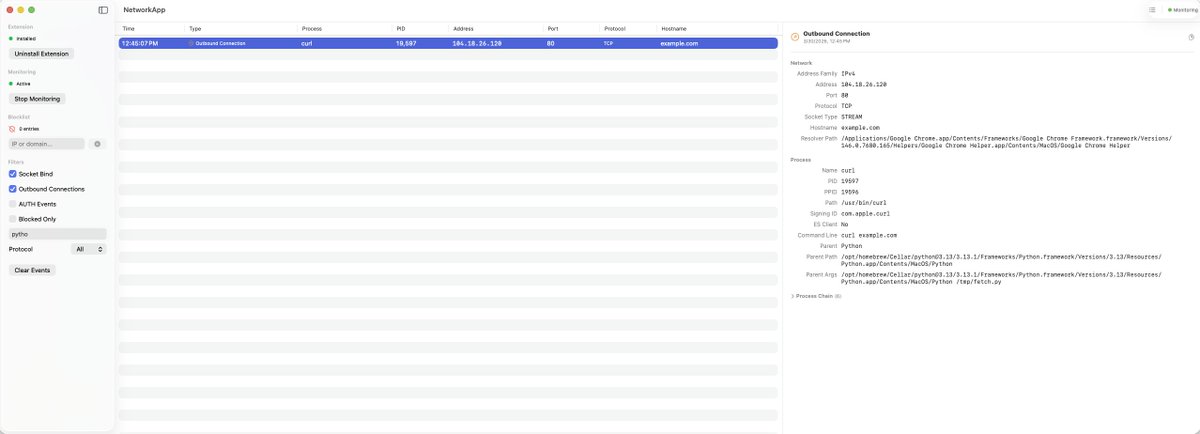
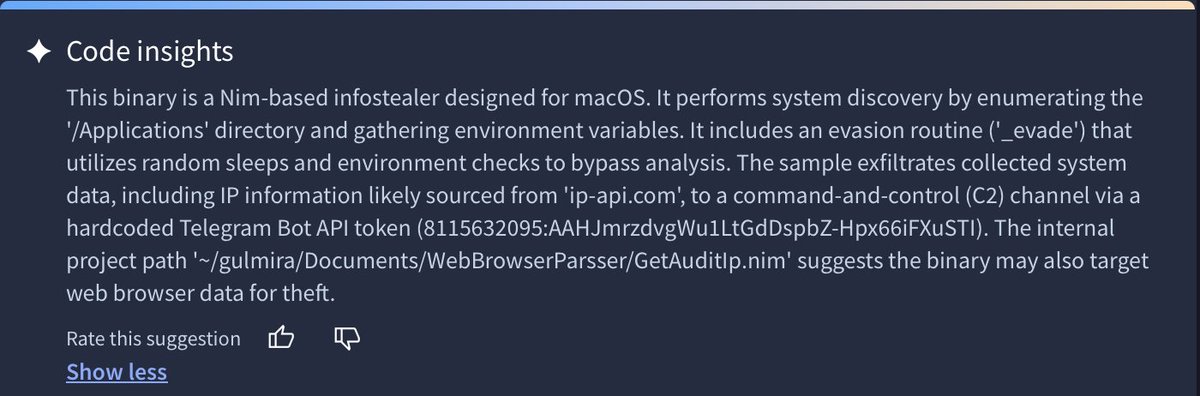
Motivated by @moonlock_lab’s recent findings on ClickFix attacks surfacing via Google Search results and even LLMs 🤯, I’ve added basic protection against most of these attacks to BlockBlock 🍎🛡️ Read: “ClickFix: Stopped at ⌘+V” objective-see.org/blog/blog_0x85…









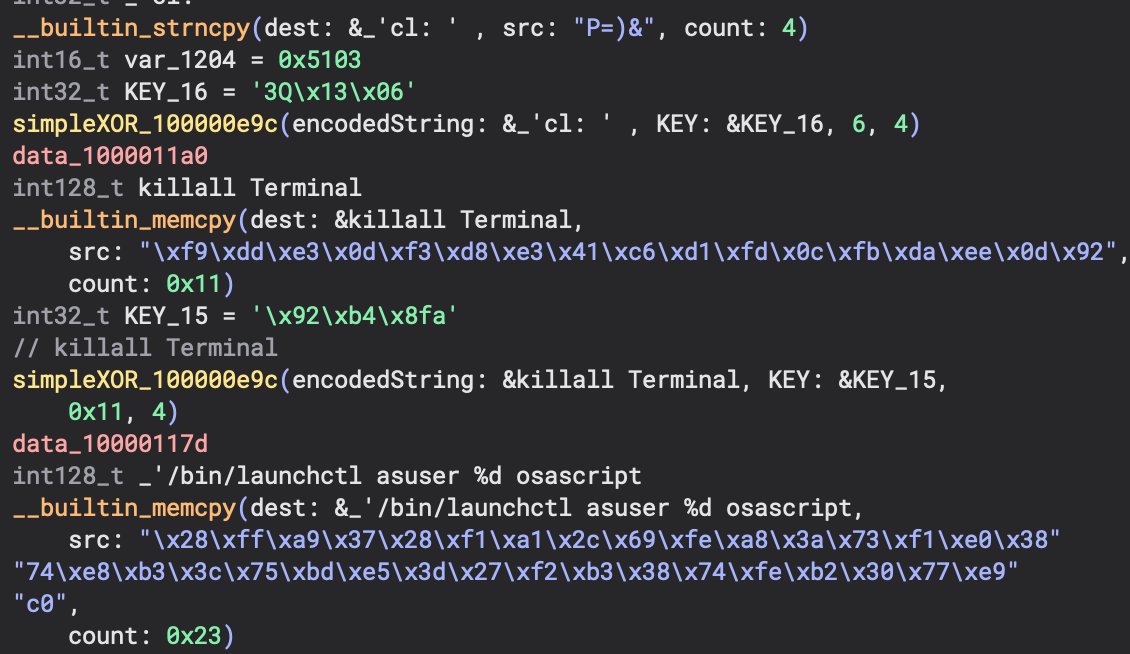
New RE Blog Post: RustyPages-Pt1 the-sequence.com/rustypages-mal… We RE a Rust dropper, that sets persistence and runs the downloaded next stage, queries @patrickwardle's tools, and quiets notifications. We included relevant IOCs as we continue our analysis of the loader for Part 2. :)