Akul Gupta
44 posts


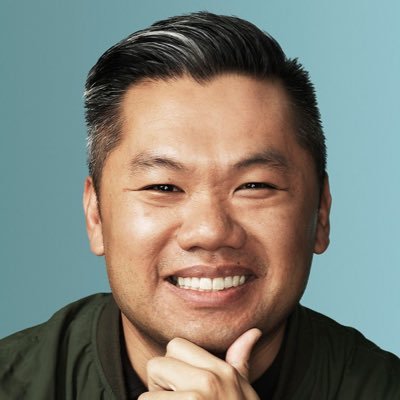
Akul Gupta
@AkulGupta30
Co-founder and CTO @mindfort (YC X25) - building autonomous security agents













We were made aware of concerns regarding the visibility of chat messages and code on Lovable projects with public visibility settings. To be clear: We did not suffer a data breach. Our documentation of what “public” implies was unclear, and that’s a failure on us. Specifically for public projects, chat messages used to be visible — this is now no longer possible. When it comes to code of public projects: That is intentional behavior. We have experimented with different UX for how the build history is surfaced on public projects, but the core behavior has been consistent and by design. Importantly, for enterprise customers, being able to set visibility to public for new projects has been disabled since May 25, 2025.