

𝐂𝐚𝐦𝐦𝐲 𝐁𝐚𝐫𝐧𝐞𝐬
1.4K posts


@Blocbross
Singer-Songwriter 🏴 | Bookings - [email protected]



You open a lootbox… it lands on a Mythic. What’s your reaction?🍡




The $CERB token has a clear burn mechanism tied to agent usage, more wallets protected means more tokens burned, @CerbAgent created a model where adoption directly benefits holders

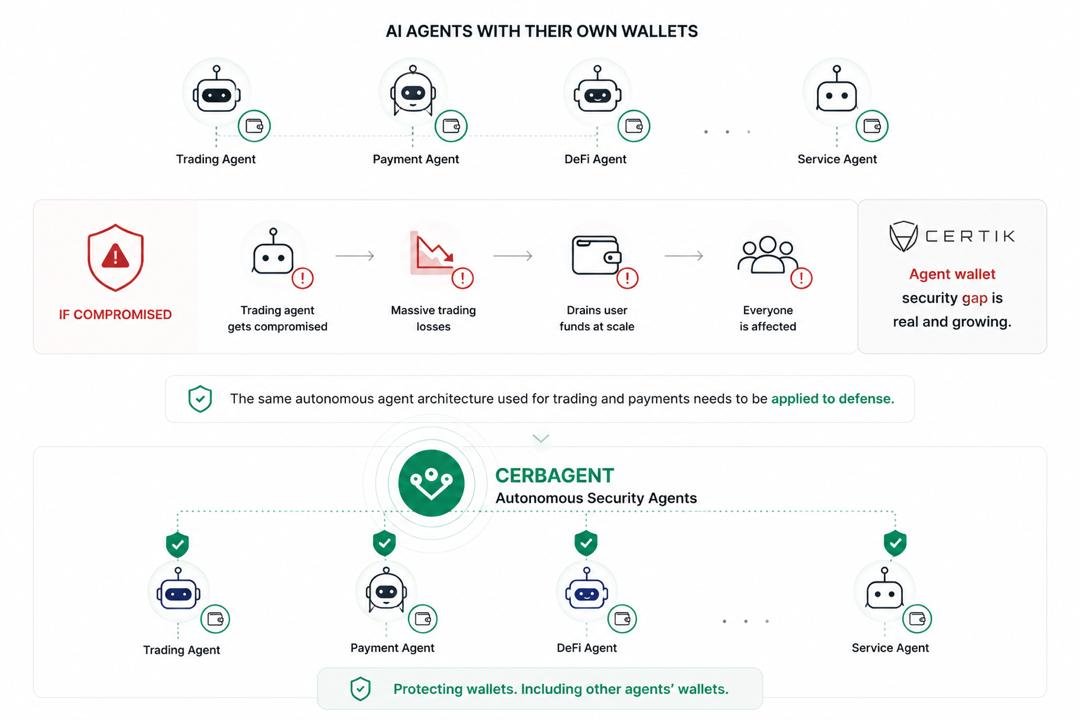


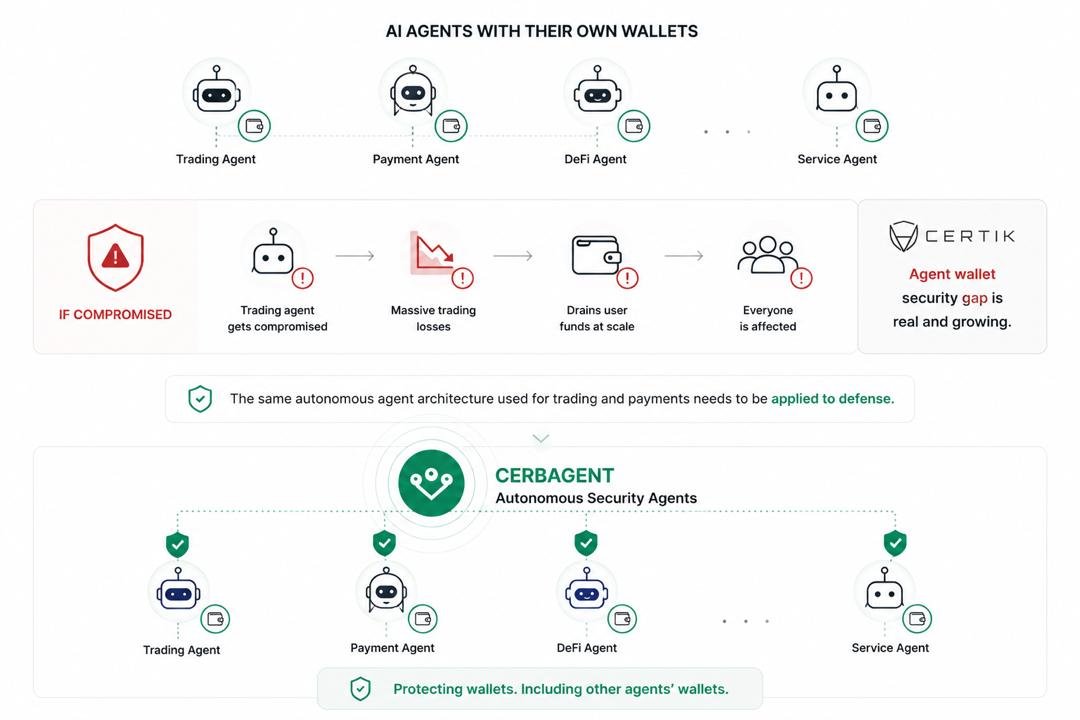
Wallets were supposed to give users full control. Instead, they’ve quietly become the weakest link in crypto. Most losses today don’t come from “breaking the blockchain.” They come from exploiting the human layer around wallets—phishing links, malicious approvals, signature traps, and invisible contract interactions. Attackers don’t need to hack code when they can trick users into signing away access. Once a wallet signs the wrong transaction, it’s already too late. There’s no reversal, no support line, no undo button. This is the core wallet security problem: blind trust in actions users don’t fully understand. Every day, users approve contracts they can’t read, interact with dApps they haven’t verified, and sign messages that look harmless but grant full asset control. Traditional security tools don’t solve this because they are reactive. They alert after risk appears, not before a decision is made. And in crypto, one wrong signature equals total loss. That’s where @CerbAgent shifts the model completely. Instead of leaving users alone at the point of decision, CerbAgent introduces an AI security layer that actively interprets, analyzes, and challenges every wallet interaction in real time. It doesn’t just scan transactions—it understands behavior. It flags abnormal patterns, detects malicious intent in contracts, and prevents users from approving dangerous permissions before they execute. This aligns with a broader evolution in security architecture: moving from passive detection to continuous, real-time verification and enforcement, where every action is analyzed before it’s trusted . The real breakthrough is that CerbAgent doesn’t rely on static rules. Attackers evolve too fast for that. Instead, it operates like an intelligent agent, learning patterns, adapting to new threats, and monitoring wallet activity as a dynamic system rather than isolated transactions. This closes the gap where most exploits happen: the milliseconds between user approval and execution. Then comes $CERB. The token isn’t just a financial layer—it’s what turns security into a coordinated system. It can power incentives, validation layers, and participation in a network where threat detection and response scale with usage. Because wallet security isn’t a single tool problem, it’s an ecosystem problem. And that’s the real insight: Crypto wallets were built for ownership, not safety. CerbAgent is building for ownership with intelligence. Until wallets can think, users will keep getting exploited. AI agents like CerbAgent are how that changes.


“Safe signature” is one of the most dangerous illusions in crypto. You can sign something that looks completely normal, and still lose everything. Case: Curve Finance pool exploit (Vyper reentrancy bug, 2023) - Bug in Vyper compiler enabled reentrancy - Attackers drained multiple pools (~$70M+) - Users interacting with affected pools weren’t doing anything unusual The vulnerability lived below the user layer. This is where the thesis of @CerbAgent gets interesting: It’s not about spotting scams. It’s about detecting broken environments. A $CERB agent, in theory, could: → recognize abnormal contract behavior patterns (reentrancy loops) → simulate repeated calls within a single execution context → detect that funds can be recursively extracted → warn users interacting with affected pools in real time But here’s the catch: Detecting reentrancy before it’s widely known is extremely hard without: - deep bytecode analysis - behavioral anomaly detection - fast pattern recognition across contracts So again, CerbAgent sits on a knife edge: If it can generalize exploit patterns → powerful If it relies on known signatures → reactive Security is only valuable before the exploit is obvious.




Happy New week guys let's keep showing up for each other 𝐂𝐄𝐑𝐁𝐀𝐆𝐄𝐍𝐓 𝐂𝐇𝐑𝐎𝐍𝐈𝐂𝐋𝐄𝐒 🚥 𝐄𝐏𝐈𝐒𝐎𝐃𝐄 𝟐𝟔: 𝐅𝐀𝐊𝐄 𝐒𝐔𝐏𝐏𝐎𝐑𝐓 𝐒𝐄𝐑𝐕𝐄𝐑𝐒 𝐀𝐑𝐄 𝐇𝐀𝐂𝐊𝐄𝐑 𝐇𝐔𝐁𝐒 You joined for help. You left without your wallet. A Thread 🧵🧵 1️⃣ Real Hack Breakdown: Fake Community Server 🚦 user has wallet issue 🚦 searches Telegram/Discord help group 🚦 joins fake “official” server 🚦 scam admin DMs instantly 🚦 asks to verify / sync wallet 🚦 user signs request or shares seed 🚦 funds drained fast The help desk was the attack. 2️⃣ Why This Attack Works 🚦 urgency when funds are stuck 🚦 fake branding + copied logos 🚦 large member counts (bots) 🚦 instant responses feel professional 🚦 trust in community spaces Panic creates vulnerability. 3️⃣ Why Existing Tools Fail 🚦 platforms don’t verify every server 🚦 fake admins impersonate staff 🚦 wallets can’t detect social scams 🚦 DMs bypass normal warnings 🚦 users trust appearance over proof The scam happens before tools matter. 4️⃣ Where @CerbAgent Comes In 🚦 incentivized support scam breakdowns 🚦 AI-scored security education 🚦 real exploit case studies 🚦 rewards for clarity Awareness becomes protection. 5️⃣ How $CERB Agents Protect Users 🚦 expose fake support tactics 🚦 teach verification habits 🚦 highlight DM red flags 🚦 share real victim stories Clarity blocks panic traps. 6️⃣ How to Stay Safe 🚦 never trust unsolicited DMs 🚦 use links from official websites only 🚦 no real support asks for seed phrase 🚦 verify admins publicly Help should never cost your wallet. 7️⃣ Why This Content Wins 🚦 real scam stories = high impact 🚦 clear warnings = higher score 🚦 practical tips = real value 🚦 consistency = leaderboard growth Security insight earns more. 8️⃣ What This Prevents 🚦 fake support drains 🚦 seed phrase theft 🚦 rushed mistakes 🚦 repeated social scams Without awareness, help becomes harm. ✅ TL;DR 🚦 Fake support servers steal wallets 🚦 Panic drives bad decisions 🚦 Tools can’t stop social traps 🚦 Awareness is defense 🚦 $CERB rewards real insight @CerbAgent turns fake help into real warnings.

Dango turns collaboration into a system you can actually trust,every step defined, every transition verifiable. It removes ambiguity from teamwork, replacing guesswork with clarity and structure.


I used to think wallet security was just about being careful. “Don’t click bad links. Don’t sign shady transactions.” Then I ran the @CerbAgent demo. And that assumption fell apart instantly. “Security tools just alert you. You still have to act” That’s the normal flow. You get a notification. You panic. You try to react before it’s too late. But that’s already failure, just delayed. In this case, there was no reaction needed. The agent detected compromised approvals, revoked them, and secured the wallet… before I even processed what was happening. 4.2 seconds. “Okay, but alerts are still useful” Not when speed is the problem. By the time most alerts reach you, the damage is already done. That’s the gap people underestimate. Detection isn’t enough. Notification isn’t enough. Execution is what matters. And that’s the shift here. From: “Something is wrong, go fix it” To: “It’s already handled” Three approvals cleared. Funds intact. Full audit trail. No scramble. No damage control. Just a system that acts. At some point, you realize The real risk isn’t exploits. It’s relying on systems that wait for you to respond.


As decentralized ecosystems continue to expand, managing security across multiple layers is becoming increasingly complex. The growing number of interactions, protocols, and user actions makes it harder to maintain consistent protection over time. In this context, @CerbAgent is exploring approaches focused on coordinated security systems and continuous monitoring, where protection is not limited to isolated tools but operates as an integrated layer across different environments. Developments in this area could influence how security is structured at scale. Rather than relying on fragmented solutions that activate at specific moments, this model shifts toward persistent systems that observe, evaluate, and respond in real time. The emphasis moves from reactive checks to ongoing coordination across interactions. By introducing roles such as transaction evaluation, behavioral monitoring, and recovery mechanisms, the system moves beyond single-point tools toward a more unified framework. Each component contributes to a broader understanding of activity across networks. As decentralized systems grow more complex, approaches like this could reshape how users interact with security, reducing dependence on constant manual oversight while maintaining awareness across multiple layers.







We’ve all seen the meme of the guy sweating over two buttons, in crypto, it’s choosing between missing out on a massive airdrop and getting your entire net worth drained. During peak FOMO, our critical thinking turns off and that's exactly what modern scammers prey on. Let’s break down one of the most common live exploit vectors right now: the fake claim portal. Hackers spin up a pixel-perfect clone of a trending protocol's UI. When you rush to connect and hit Claim Token, you aren't actually calling a distribution function. Instead, the drainer mechanics slip in a setApprovalForAll request hidden in the data. Because you're rushing to beat a gas war or secure your allocation, you blind-sign it. In one click, they have full access to move your NFTs and ERC-20s. We always tell each other to rely on the standard stack. Pocket Universe is great for simulating the transaction and Revoke Cash is essential hygiene. But let’s be entirely honest, in the heat of an airdrop claim, people routinely click right past simulator warnings, and Revoke is just the cleanup crew you call after your wallet is already empty. It's a fundamentally flawed, human-dependent security model. As someone deeply interested in the evolution of DeAI infrastructure, this is why I'm looking at $CERB from a completely different angle. What @CerbAgent is building isn't just another layer of friction, it's the exact evolution the space needs. They aren't building a louder warning label; they are deploying autonomous AI agents at the execution layer. If you trigger a hidden approval on a known drainer contract, the $CERB agent doesn't just ask if you're sure, it actively intercepts and neutralizes the threat based on real-time on-chain intelligence before the transaction is ever broadcasted. Sentinel is the 24/7 monitoring agent from CerbAgent that watches chain activity around your wallet, it never sleeps and it never misses, $CERB token powers the compute behind it It’s the difference between wearing a seatbelt and driving a car that automatically hits the brakes before a crash. The future of Web3 isn't forcing users to manually decode hex data; it's deploying AI agents to defend our wallets in the background. Stop trusting your FOMO and get actual, active protection. $CERB




The @CerbAgent Recovery agent doesn't promise miracles but it gives you the best shot at tracing and recovering stolen assets, $CERB funds the forensic AI that makes this possible