Karkas
29 posts


@HaifeiLi a lot ppl might not know that you can disable certain API Calls with registry Keys/GPOs:
#blacklist-configuration" target="_blank" rel="nofollow noopener">adobe.com/devnet-docs/ac…
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Adobe\Adobe Acrobat\DC\FeatureLockDown\cJavaScriptPerms tBlackList=RSS.addFeed|Util.readFileIntoStream
...and you are safe :)
English

Fun fact about the Adobe Reader 0day: actually, it's the "AdobeCollabSync.exe" ("C:\Program Files\Adobe\Acrobat DC\Acrobat\AdobeCollabSync.exe") process who communicates to the attacker-controller server, not the "Acrobat.exe".
Therefore, if you're hunting the threat with your e.g EDR telemetry, you may want to look at that "AdobeCollabSync.exe" process too.
#threatintel
English

@dcuthbert met him countless times even in the smallest Cons where he held top notch talks and always stopped for questions... true legend. Will never be forgotten
English

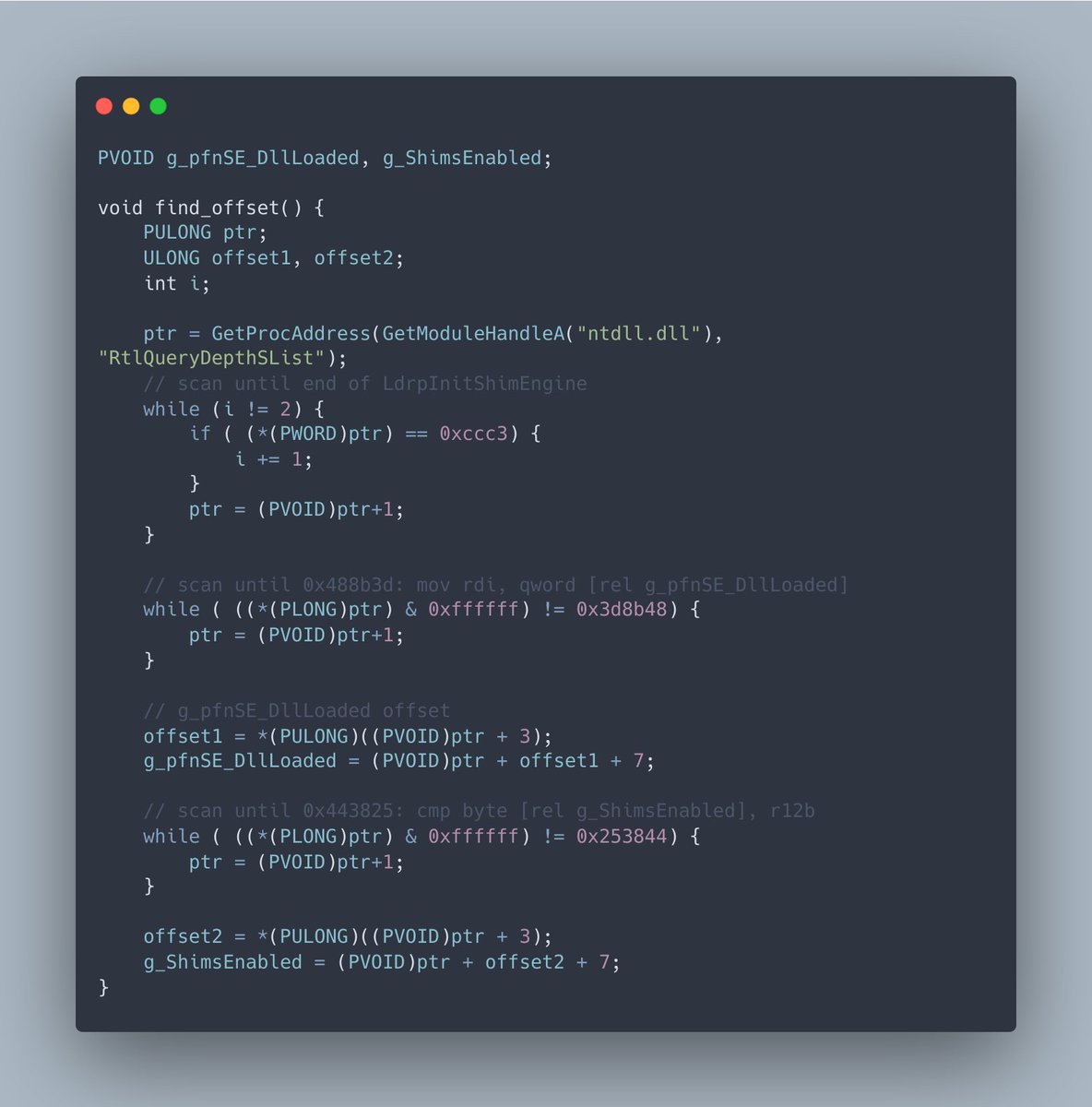
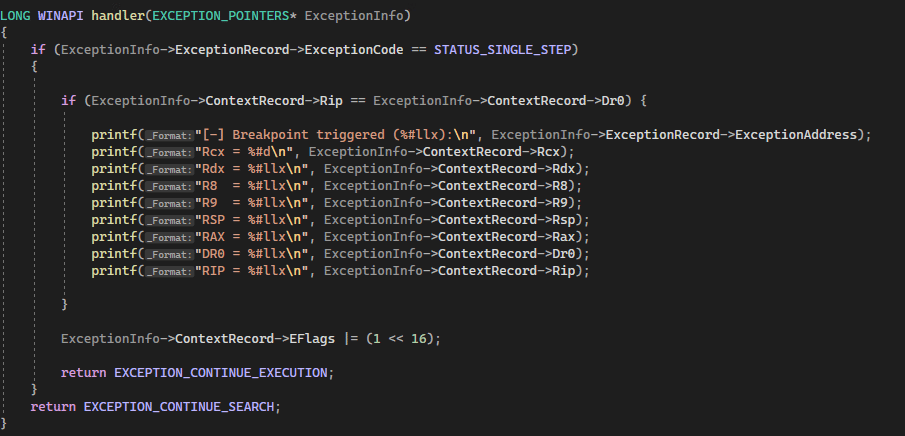
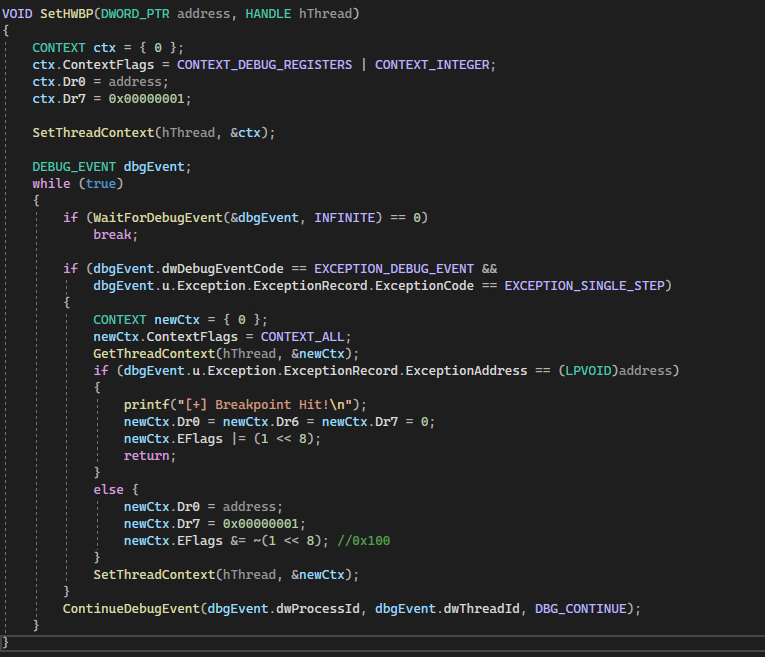
Malware development intermediate: EDR Evasion - A New Technique Using Hardware Breakpoints
cymulate.com/blog/blindside…
English

@eversinc33 @cyb3rops Looks like the boys (colleagues) and I are soldiers now
English

@yarden_shafir Once you reach the level "I´ve forgottn more stuff than the average Junior level Analyst knows" you enter the realm of the true masters
English

@techspence Let´s move everything to the cloud, they know how to do security
English

Ever since I was baby I've wanted speak or give a workshop at Defcon.. This year I get to finally make that dream happen.
It's on, @rpargman 😎

English

@yarden_shafir It´s a Kookaburra, in germany we call it "laughing Hans" :D
They are quite intelligent birds ;)
Kookaburra - Wikipedia
English

Today I improved and rereleased a Project: github.com/Karkas66/Early…
The original Code by 0xNinjaCyclone had hardcoded Injection Process Name and static plain Shellcode. I wanted to load dynamic Shellcode from files into a process of my choice. To get rid of plain msfvenom shellcode detections by several AVs I made a basic XOR Encryption of the embedded shellcode. I also made a Visual Studio 2022 Template, ready to compile and run. Did not yet find the problem why not msfvenom shellcode crashes the hosting payload process. So just use msfvenom SC for now. I successfully tested with meterpreter_reverse_tcp
English

@_RastaMouse it realy is. But learn my lesson: Don´t Update (OTC Wifi Dongle) without backing up the SD Card first
English

@C5pider @Octoberfest73 yeah sure it´s not... did not yet look into the code when writing the comment. Will steal the best ideas anyway!
btw, nice Framework @c5pider was hard to get into it, but yet fun to learn
English

@SOC5444 @Octoberfest73 This is not the same. While both of you wrote a stager, his is focused on creating a secure staging process by validating and verifying the retrieved stage against an MD5 checksum.
English

Happy to share another open source project- An x64 position-independent shellcode stager that validates the downloaded payload stage prior to execution. Integration with Cobalt Strike out of the box. Check out Secure_Stager here: github.com/Octoberfest7/S…
English

Thanks a lot @jstrosch for the great conversation and allowing me to demo some malware analysis techniques on your channel! If you missed it, you can find it here. 😎
youtube.com/watch?v=odRgHC…
YouTube
Josh Stroschein | The Cyber Yeti@jstrosch
🔥 Today's the day - Kyle Cucci (@d4rksystem) joins the stream to talk #EvasiveMalware! Join us at 1pm CDT 👇 😈 youtube.com/live/odRgHCfQC… We'll discuss the book and Kyle will provide some live demos of the content - it's going to be awesome!
English

@SOC5444 @OutflankNL There's nothing novel about it, except from overwriting a different pointer. 🤷
English

New Blog Alert! 🚨
Introducing Early Cascade Injection, a stealthy process injection technique that targets Windows process creation, avoids cross-process APCs, and evades top-tier EDRs.
Learn how it combines Early Bird APC Injection & EDR-Preloading: outflank.nl/blog/2024/10/1…

English

Thanks @Proofpoint for hosting me on the podcast! I love talking about malware🤓
Threat Insight@threatinsight
A new @Proofpoint DISCARDED podcast has dropped! 🔥 Kyle Cucci (@d4rksystem) joins Selena and Tim to shed light on the evasion techniques of today's threat actors and how modern malware ensures its survival. Listen on your favorite streaming platform! ow.ly/AHFP50SylOr
English