Sabitlenmiş Tweet
CryptoInsane
3.8K posts

CryptoInsane
@CryptoInsane
Threat Intelligence | Analyst/Researcher | #Malware | #Reverse | #OSINT | #Programmer | #Cryptographer | Physicist & Mathematician | 🕵️♂️🦾🇵🇪
Lima - Perú Katılım Eylül 2015
162 Takip Edilen13K Takipçiler

🚨 Threat Intelligence Alert | China's CVERC warns about new "Silver Fox" (银狐) trojan variant 👾
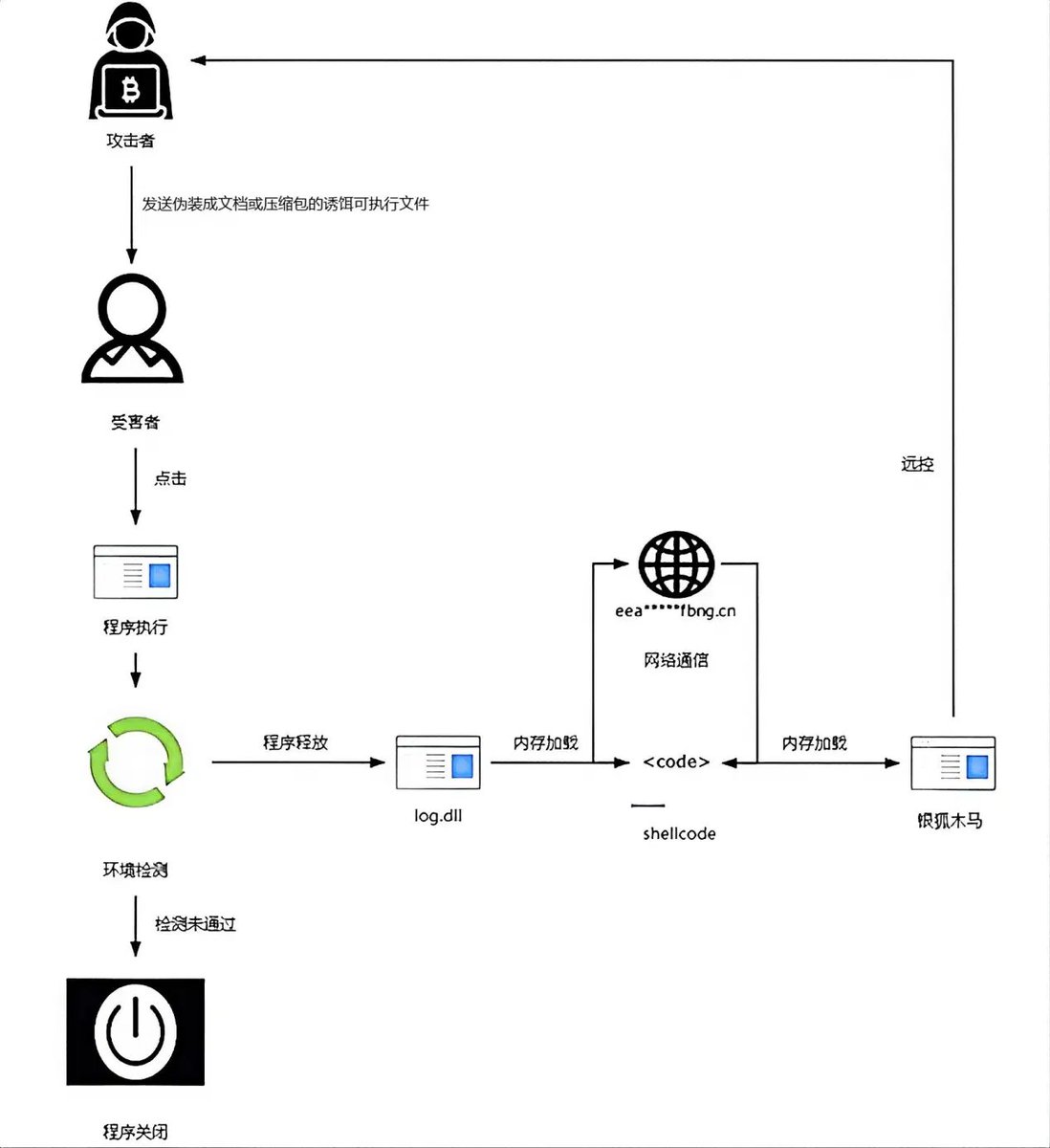
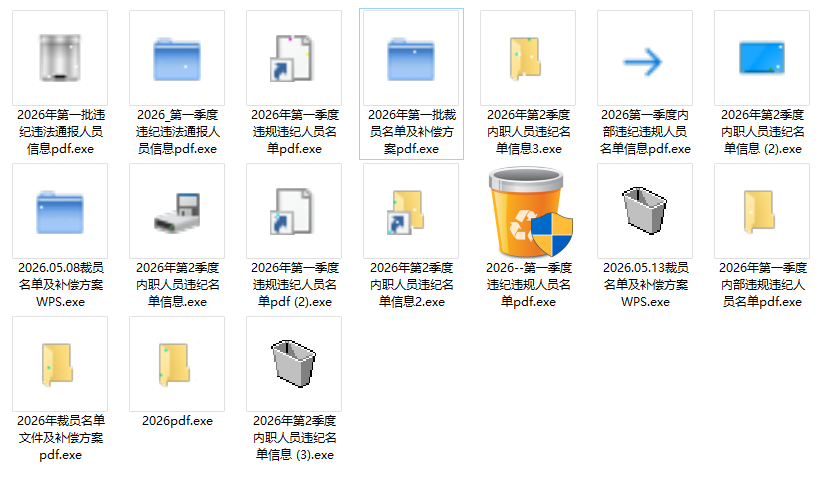
On May 21, 2026, China's National Computer Virus Emergency Response Center (CVERC) released an advisory regarding a new wave of the "Silver Fox" trojan family (also tracked as Yóu Shé / 游蛇, Valley Thief, UTG-Q-1000, and SwimSnake), specifically targeting Windows users in China.
🎣 Attack vector — HR-themed social engineering Threat actors leverage highly persuasive corporate-context filenames, including:
📤"Internal investigation results"
📤"Quarterly disciplinary violation list"
📤"Personnel notification information"
📤"Layoff list and compensation plan"
The payloads are disguised as shortcuts, folders, recycle bin icons, or PDF documents, distributed primarily through WeChat, QQ, DingTalk, Feishu, and email.
⚙️ Observed TTPs
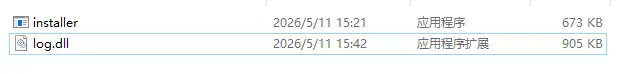
🔹 Persistence & DLL sideloading: payloads dropped in C:\Program Files\Internet Explorer\, abusing a legitimate binary (installer.exe) to sideload the malicious log.dll.
🔹 C2 communications: HTTP traffic over port 8880, with endpoints such as /getinstall64.
🔹 Primary target profile: HR personnel in medium-to-large organizations.
English

🚨 Potential massive data breach – Lockheed Martin🛡️
A reported 375 TB of data allegedly linked to Lockheed Martin has surfaced on a “Threat Market”, now in a sale phase.
📊 Leaked data breakdown:
• 🎥 Confidential videos — 68 TB
• 🖼️ Confidential images — 24 TB
• 🛠️ Unfinished projects — 31 TB
• 📁 Completed projects — 42 TB
• 💻 Executable files — 18 TB
• 📐 Blueprint files — 27 TB
• 🎥 Office CCTV backups — 55 TB
• 💻 Source code — 9 TB
• 👥 Personnel information — 6 TB
• 📄 Defense contracts — 5 TB
• 📧 Email backups — 8 TB
• 🛰️ F-35 Block 4 — 21 TB
• 🛡️ Defense systems — 14 TB
• 🔬 R&D — 16 TB
• 🧪 Technical & Debugging — 7 TB
• ⚙️ Engineering Systems — 11 TB
• 📊 Operations data — 7 TB
• 🔐 Security & access — 6 TB
🔒 All data appears encrypted and access-locked, suggesting attackers may be selling access or decryption keys.
🔎 Key insights:
• 📦 The structured organization suggests prolonged access or a staged exfiltration.
• ⚠️ The nature of the data implies a potential geopolitical impact if legitimate.
• 🧠 References to advanced projects may aim to increase perceived value.
• ❗ There is a possibility of exaggeration or fraud, which is common in underground markets.

English

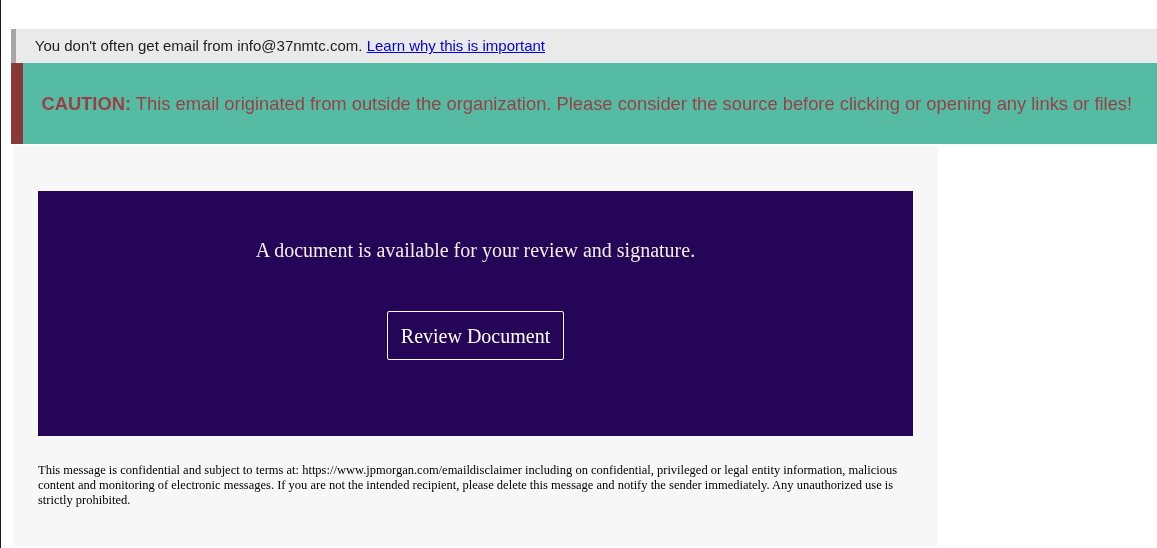
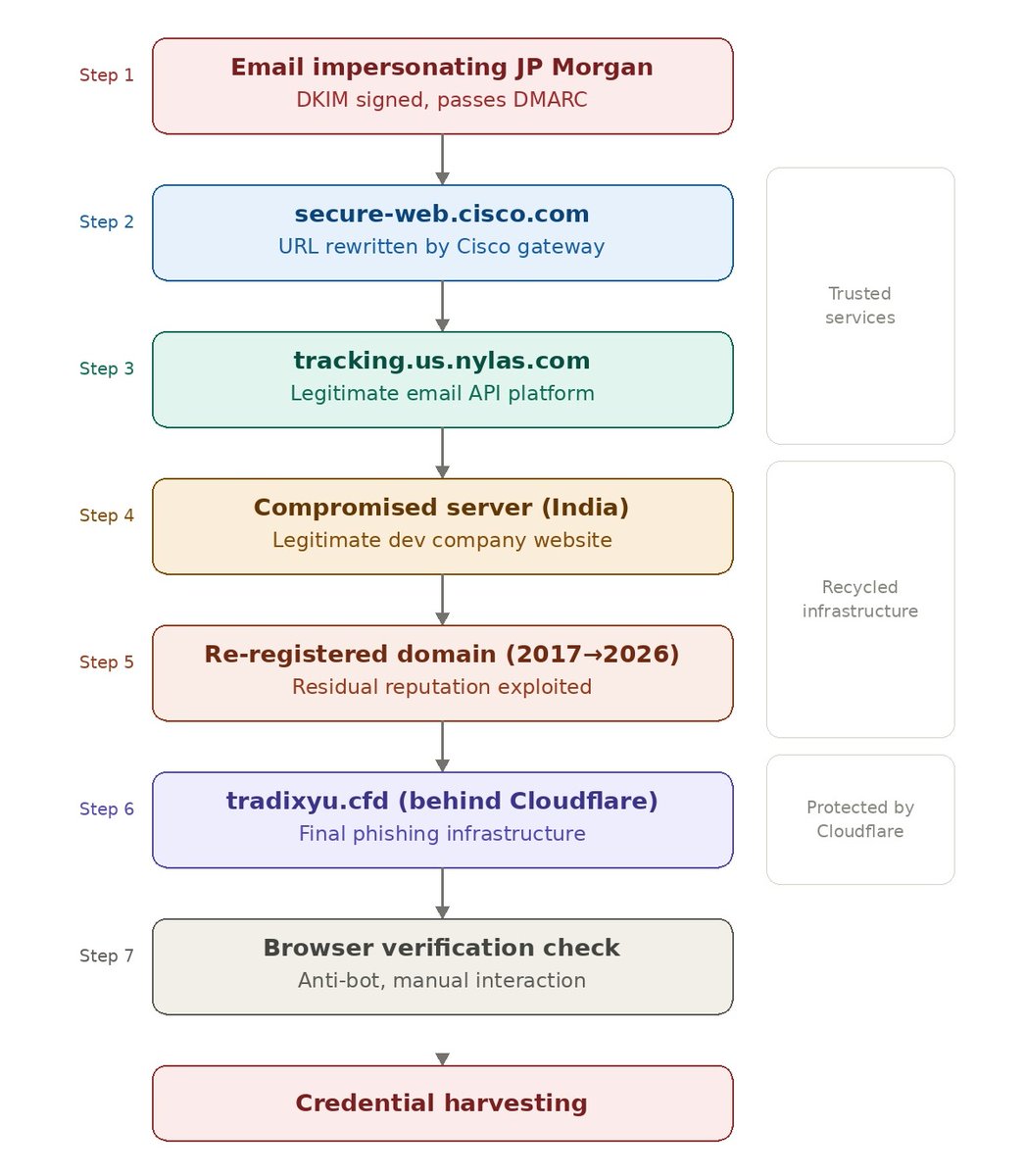
🚨 New phishing campaign exploits Cisco domains to bypass security filters
The threat intelligence team at Outpost24 just documented a sophisticated attack that shows how attackers are taking phishing to the next level.
How does it work?
📧 It starts with an email impersonating JP Morgan, inserted into what looks like an existing thread. The email passes DMARC thanks to legitimate DKIM signatures via Amazon SES.
🔗 The "Review Document" link points to secure-web.cisco.com — a trusted domain no one would block.
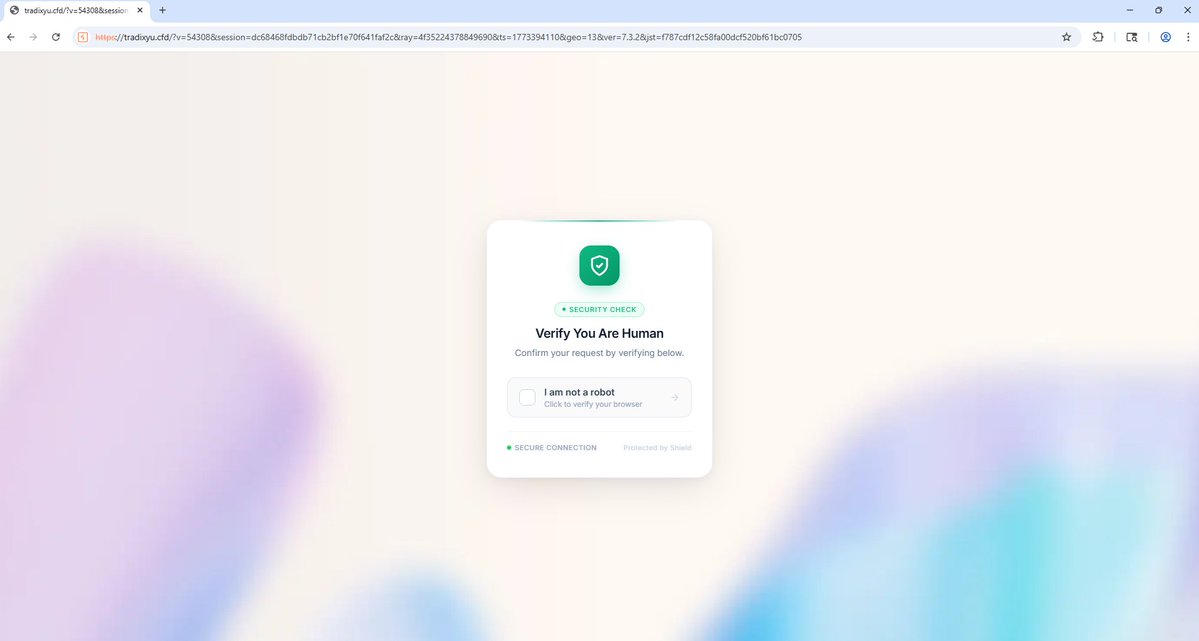
🔄 From there, the victim bounces through Nylas (a legitimate email API platform), then through a compromised server in India, next through a domain originally registered in 2017 with residual reputation, and finally lands on the real phishing page protected by Cloudflare.
🛡️ 6 hops through trusted infrastructure. Each link in the chain has good reputation on its own. Traditional filters don't evaluate the full chain.
💡 Key takeaways:
• A known domain in the URL doesn't guarantee safety
• Valid DKIM signatures don't mean the sender is legitimate
• Phishing-resistant MFA (FIDO2/WebAuthn) is no longer optional
• Ongoing security awareness training remains the first line of defense
The good news: the attack was detected and unsuccessful. ✅
The bad news: these techniques will keep evolving. 🔎
📖 Full analysis by Specops Software: specopssoft.com/blog/phishing-…
English

Artificial intelligence is no longer slowly entering our professions —
it is beginning to redefine them in real time ⚙️
First it impacted visual creativity 🎨, then writing ✍️, then programming 💻… and now it is starting to directly influence cybersecurity 🔐 and technical decision-making.
Every new technological release does not only introduce a tool — it changes the very way work is understood.
That is why we see immediate reactions in the stock market 📉 not because companies suddenly lose value overnight, but because the market anticipates a shift in the production model.
When the way knowledge is produced changes, the way value is produced changes as well.
However, these movements do not mean the end of professions — they mean transformation 🔄
Technology has always followed the same pattern: tasks disappear, but more complex roles emerge.
Artificial intelligence automates execution 🤖
but increases the need for human judgment 🧠
Therefore, the right approach is not fear, but adaptation 🚀
Stay calm, keep studying, understand the new tools, and learn how to work with them instead of resisting them 📚

English

🚨 RAMP Forum Takedown & RaaS Migration 🚨
Following the FBI takedown of the RAMP cybercrime forum 🕵️♂️, a progressive reconfiguration of RaaS activity across alternative underground forums has been observed.
📌 Notably:
🐉 DragonForce Ransomware Cartel appears to have started operating on this forum after the RAMP takedown, actively promoting its RaaS program and recruiting affiliates.
🎩 The Gentlemen’s RaaS, while maintaining a presence on this forum since 2025, is expected to increase its operational activity and visibility following the RAMP shutdown and subsequent redistribution of threat actors.
This reinforces a well-established pattern:
⚠️ Takedowns do not dismantle the ecosystem—they accelerate activity consolidation within alternative hubs.
Some actors migrate, while others scale operations within existing infrastructures.
📊 Key CTI monitoring indicators:
✔️ Post-takedown activity surge
✔️ Consolidation of alternative forums
✔️ Adjustments in RaaS business and affiliate models
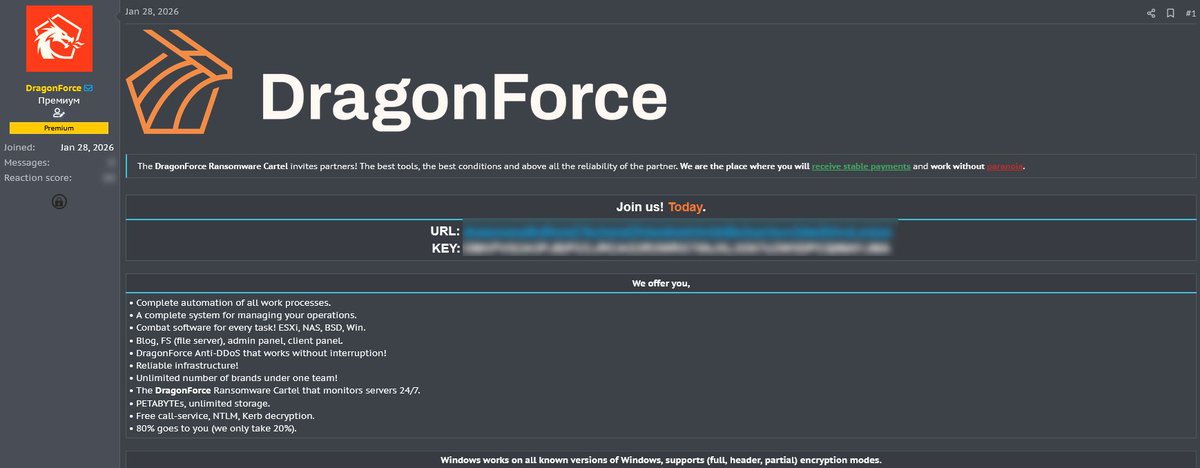

English

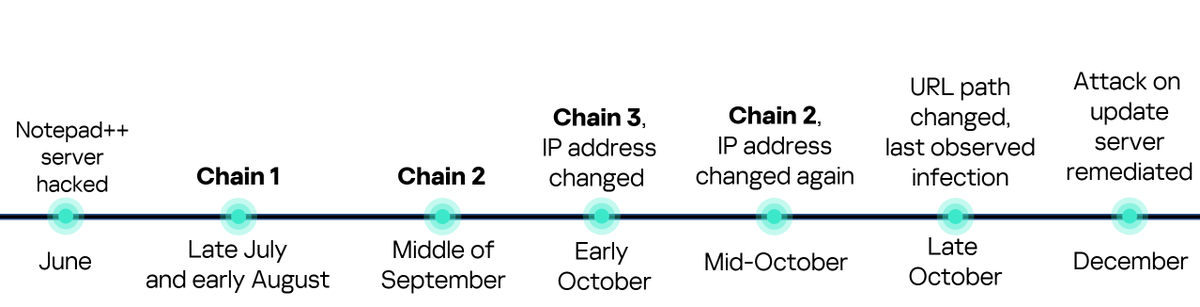
🚨 Notepad++ Supply Chain Attack — Advanced Technical Summary
Recent investigations revealed a highly sophisticated supply chain compromise impacting Notepad++ update infrastructure, enabling attackers to selectively deliver trojanized installers to targeted victims.
According to Kaspersky GReAT’s deep technical analysis, this was not a single-stage incident, but a long-running, multi-phase campaign active between June and December 2025.
Key technical insights from Kaspersky:
🧬 Multiple infection chains
- At least three distinct execution chains were identified
- Each chain used different:
⚠️ C2 servers
⚠️ Domains
⚠️ File hashes
⚠️ Payloads
- Tooling and infrastructure were rotated roughly monthly to evade detection
🎯 Highly targeted operation
- Victims included:
🔴 Government organizations (Philippines)
🔴 Financial institutions (El Salvador)
🔴 IT service providers (Vietnam)
🔴 Individuals across multiple regions
- The campaign was selective, not mass-distributed
🛠️ Advanced malware tradecraft
Delivery of the Chrysalis backdoor/loader
- Use of NSIS-based malicious installers
- Abuse of legitimate updater process (GUP.exe)
- DLL sideloading to load malicious payloads
- Use of Cobalt Strike Beacons
- Metasploit-based payload delivery
- Frequent infrastructure rotation to bypass IOC-based detection
🗂️ Key TTPs observed
- Registry Run Key persistence
- Collection and exfiltration of:
🛠️ Process lists
🛠️ System information
🛠️ Network connections
- Use of temporary file hosting (e.g., temp[.]sh)
- Multiple previously undisclosed IoCs published by Kaspersky
⚠️ Critical defensive takeaway
- A clean scan against public IoCs does not guarantee historical non-compromise
- Earlier infection chains used completely different indicators
- This highlights the limits of static IOC-based detection for APT-level supply chain attacks
This incident reinforces that modern supply chain attacks are:
🔴 Targeted
🔴 Long-lived
🔴 Multi-stage
🔴 Designed to evade traditional detection
securelist.com/notepad-supply…
English

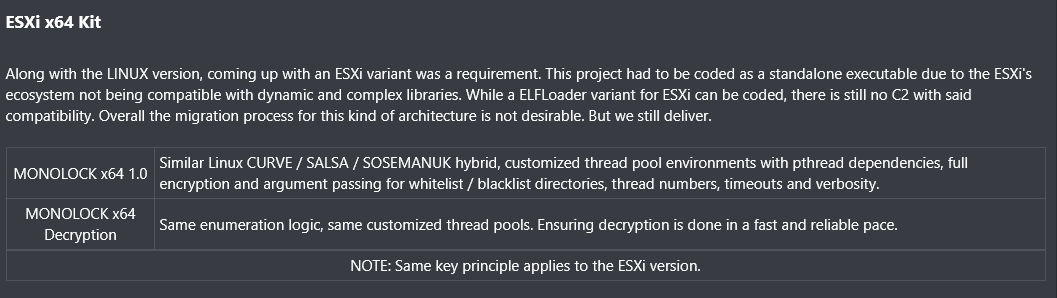
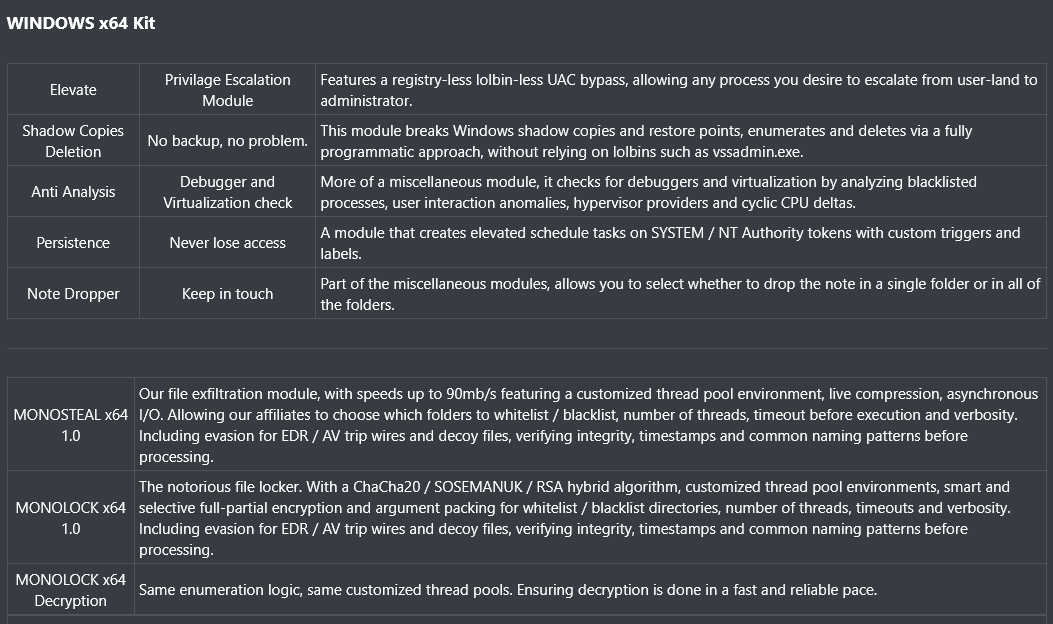
🔴 A New Ransomware Threat Emerges in Underground Hacker Forums: MonoLock 🚨
MonoLock is a newly emerged ransomware threat actor observed in high-profile underground hacker forums. The group presents a redesigned, multi-platform ransomware framework with a strong emphasis on operational security (OPSEC) and architectural efficiency, aiming to modernize traditional ransomware tradecraft. 🧠⚙️
MonoLock is built around a Beacon Object File (BoF)–centric architecture, enabling fully in-memory execution, modular payload deployment, and a reduced forensic footprint while maintaining centralized control. 🧬🧠
🪟 Windows Capabilities
On Windows systems, MonoLock provides a mature ransomware toolkit that includes:
- Privilege escalation without registry or LOLBin abuse 🔓
- Programmatic deletion of shadow copies and restore points 🧹
- Anti-analysis and virtualization detection 🛡️
- SYSTEM-level persistence mechanisms ♻️
- High-speed data exfiltration 🚀
- Selective full or partial file encryption using hybrid cryptography 🔐
These features indicate a solid understanding of Windows internals and enterprise defenses 🏢🧩.
🐧 Linux Capabilities
MonoLock extends its operations to Linux by offering:
- Custom ELF loaders for in-memory execution 🧠
- Native encryption and decryption tooling 🔐
- Optimized thread management ⚙️
- Granular targeting via whitelist and blacklist logic 🎯
This reflects a deliberate focus on Linux servers and infrastructure environments ☁️🖥️.
🧊 ESXi Capabilities
For virtualized environments, MonoLock delivers a dedicated ESXi variant as a standalone executable:
- Full encryption and fast decryption routines 🔒⚡
- Cryptographic consistency with Linux implementations 🧩
This highlights an intent to target enterprise virtualization layers 🏗️.
🔒 Zero-Panel Strategy
MonoLock adopts a Zero-Panel Strategy, avoiding public leak sites, Tor panels, and extortion portals. This approach prioritizes silence, reduced exposure, and private negotiation, significantly lowering OPSEC risks 🤫🛡️.
📌 Assessment
MonoLock represents an evolution toward low-noise, high-OPSEC ransomware operations, characterized by:
- Memory-resident, modular tooling 🧠
- Explicit multi-platform targeting 🌍
- Reduced public visibility 👁️🗨️
🧠 Ongoing monitoring will be essential to evaluate MonoLock’s maturity, adoption, and long-term impact 📊.

English

🎉 As 2025 wraps up, we want to give a shout-out to the researchers and analysts who helped push the cybersecurity community forward with their work. These voices are definitely worth following to keep up with new threats and fresh research in 2026.
Here’s our list, in no particular order:
@UK_Daniel_Card
@MauroEldritch
@JAMESWT_MHT
@James_inthe_box
@morimolymoly2
@skocherhan
@ericparker
@akaclandestine
@__kokumoto
@g0njxa
@CryptoInsane
@executemalware
@5mukx
@fr0gger_
@kondah_ha
@G3tSyst3m
@jstrosch
@petikvx
@ale_sp_brazil
@SquiblydooBlog
@k3yp0d
@hipdead010
@0x534c
Know someone else who deserves a shoutout? 💬
Tag them below and help build a stronger cyber community 🌐
GIF
English

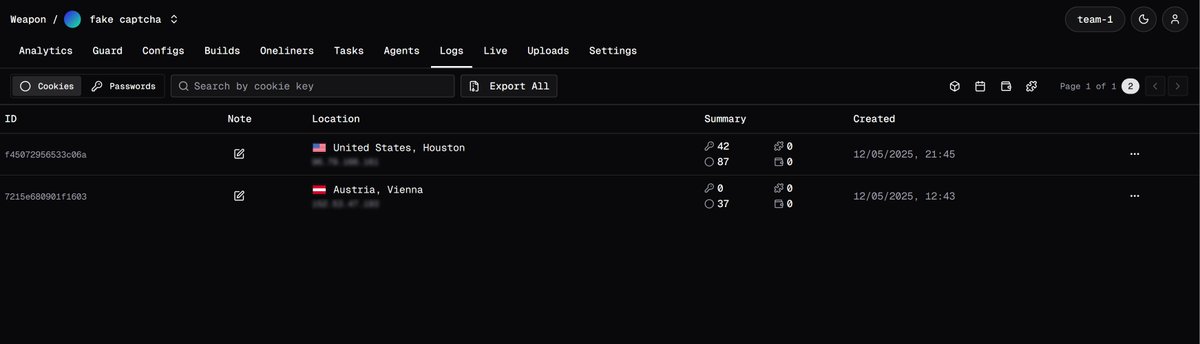
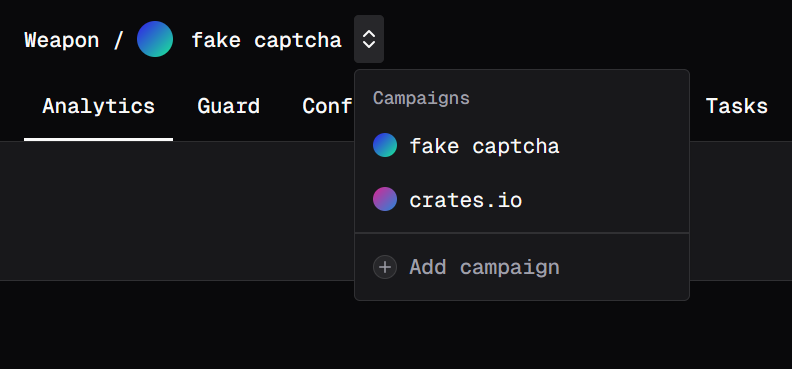
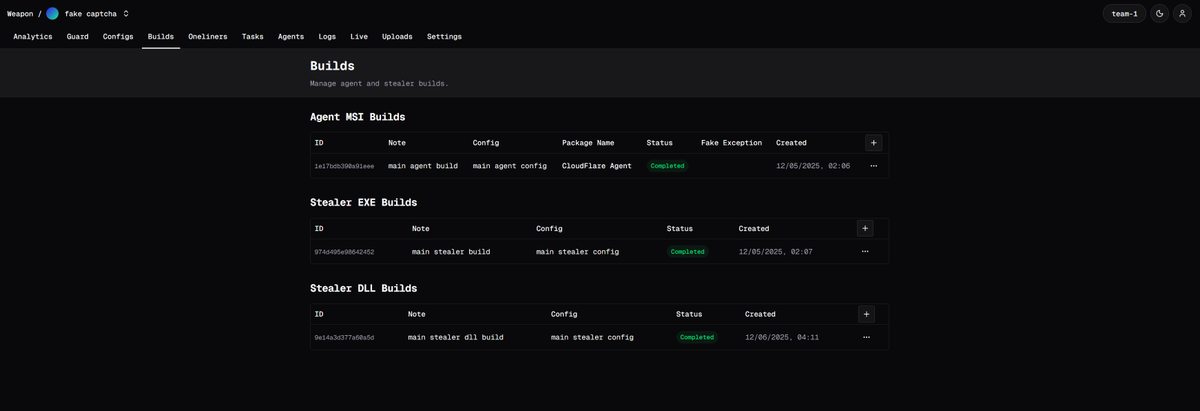
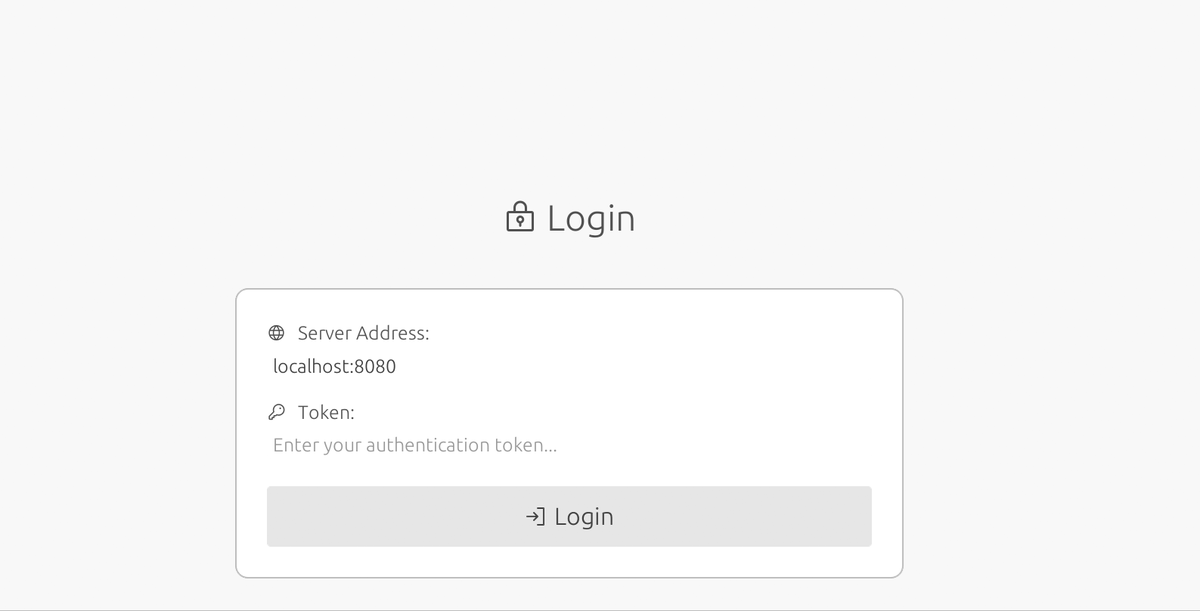
🧨🛠️ Weapon — undetected bot with extensive functionality 🛠️🧨
A new Weapon project is up for sale on underground forums, presented as a platform that evolved from an initial stealer into a full-featured multifunctional bot, developed in Node.js + Rust + PowerShell. It stands out for its modular architecture, efficient communication via a single WS/WSS connection, and a hot updates system that enables instant deployment of changes and improvements. Distribution is mainly via MSI, with an alternative cmd oneliner installation, and it is managed through a modern Next.js web panel, with full proxy support and simplified deployment using Docker Compose. The key advantage of MSI is that it remains clean for an unrealistically long time; according to the creator, it has already been distributed across 30,000 installations using a single MSI.
🧩 Bot Features
🔄 Hot updates for code and features
🧬 Additional morphing and AV recognition
⚙️ Core logic moved to a native addon
🧠 Keylogger with Unicode support
📋 High-precision seed clipper (clipboard)
📁 File manager with extended capabilities
🔗 Single WebSocket communication channel
🧪 Includes runPE and shellcode loaders
🛠 Installation via MSI and cmd oneliner
🕵️ Stealer Features (Rust)
🦀 Developed in Rust
📦 Compiles to EXE (DLL option planned)
🧵 No use of std::thread or TLS-dependent std components
🧱 Can operate as shellcode
🌐 WS/WSS server communication
🌍 Browser data collection:
Chromium (Chrome, Edge, Brave, Opera, Opera GX): passwords, cookies, payments, autofill
Gecko (Firefox): cookies
🧩 Collection of 65 browser extensions
💼 Collection of 10 desktop wallets
💬 Discord tokens (desktop app and browsers)
✈️ Telegram data
📂 File grabber: .ssh, Documents, Downloads, Desktop
🧭 Control Panel Features (Next.js)
🗂 Campaigns with separated workspaces
📊 Analytics and metrics
🛡 Guard manager (proxies), Config manager, Build manager
☁️ Uploads (file hosting)
👥 User manager (admins only)
🔍 Log viewer, exports, and filters
🤖 Agent viewer, file manager, SOCKS, keylogger
🐳 Simple deployment with Docker Compose

English

🚨 Cybersecurity Alert: Radiant Ransomware Group Shuts Down and Offers Free Decryption for Hospitals & Schools 🔓
The Radiant ransomware group has issued a surprising statement announcing their full shutdown of operations and withdrawal from the dark web. This decision appears to be a direct response to the intense public condemnation generated by their attacks.
Most notably, they are attempting to "compensate" by focusing exclusively on the Health and Education sectors:
• Specific Offer: Radiant is providing a complete free decryptor for any Hospital 🏥 or School 🏫 that was victimized by them.
• Motivation: The group states that attacks on hospitals and children are "unpleasant targets" and apologizes for the damage caused.
💡 Key Implications
1.- Reputational Impact: The Radiant case underscores how public opinion and media condemnation can influence cybercrime groups.
2.- Lingering Risk: Despite the shutdown, data stolen from non-paying victims has reportedly been sold to third parties. The risk of a data leak still persists.
📞 Call to Action for Victims (Hospitals/Schools)
If your Hospital or Educational Center was affected by a recent ransomware attack, it is crucial to make contact as soon as possible to try and obtain the free decryptor.
Free Decryption Contact (ONLY Hospitals/Schools): 97DF90F5B408E053465D6A3F85596DB3B2342CA47D1D944D45A0A6E654A5A33CF9D634B13981

English

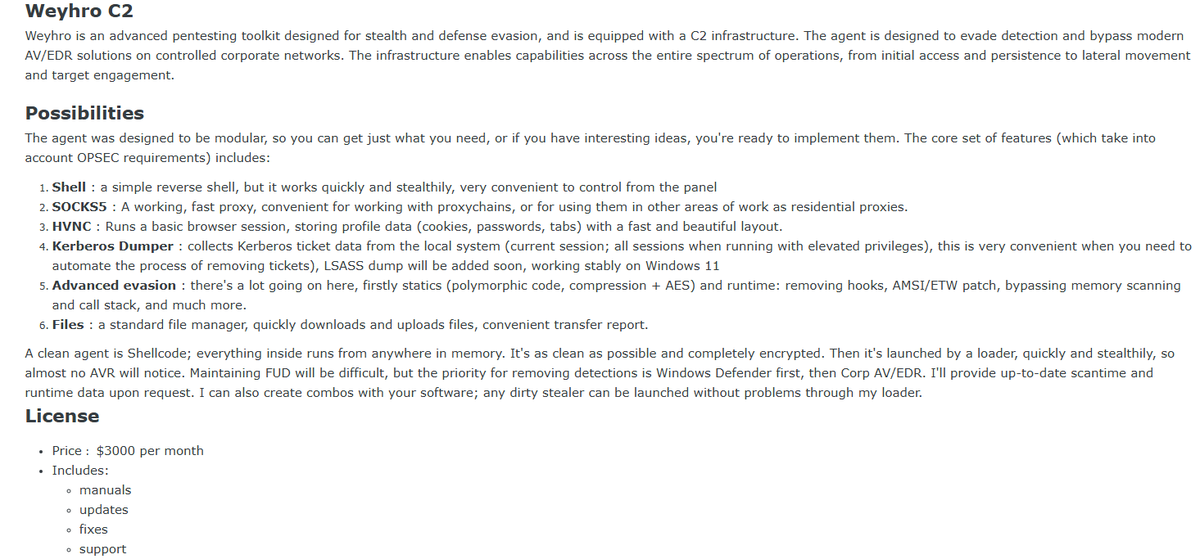
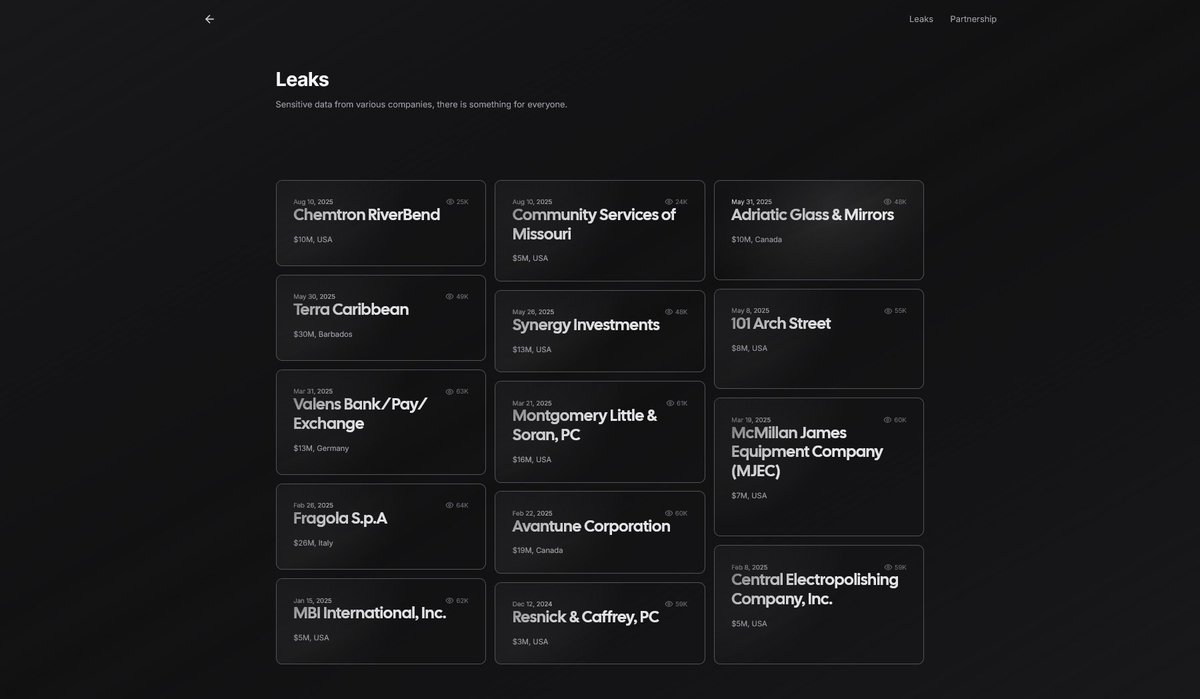
🔄 Transition of Weyhro Group: From Ransomware Operators to Offensive Cyber-Mercenary Services
🕵️♂️ Intelligence gathered from cybercrime underground forums indicates a strategic pivot by the threat actor known as "Weyhro." Formerly identified exclusively as a ransomware operator targeting corporate entities, the group has transitioned into a "Cyber-Mercenary" and infrastructure provider role.
📅 The actor's timeline shows active ransomware operations from December 12, 2024, to August 10, 2025. Following a period of silence, the actor resurfaced on December 3, 2025, not to recruit affiliates for a RaaS scheme, but to sell a proprietary C2 framework and offer direct offensive services to other criminals.
🎯 Strategic Objectives
• 💼 Professionalization of Cybercrime: Move away from typical affiliate models to offer specialized, tiered "consulting" services (Pentesting, Intelligence, Extortion) with fixed pricing or profit-sharing models.
• 💰 Tool Monetization: Capitalize on internal development by licensing the "Weyhro C2" framework, likely battle-tested during their previous ransomware campaigns.
• 👻 Operational Evasion: Maintain a focus on stealth and anti-forensics to ensure the longevity of their tools and services in controlled corporate environments.
🛠️ Attack Tools & Methods
Weyhro C2 Framework:A modular Command and Control agent designed for stealth and persistence, offered at 💵 a significant monthly subscription. It strictly prohibits execution on CIS (Commonwealth of Independent States) machines 🚫🇷🇺.
Communication & Access:
🐚 Shell: High-speed interactive reverse shell for real-time command execution ⚡.
🌐 SOCKS5: Stable resident proxy compatible with ProxyChains for lateral movement within internal networks 🔗.
💻 HVNC (Hidden VNC): Launches a covert browser session utilizing the victim's profile data (🍪 cookies, 🔑 passwords) for undetectable remote access 🕵️♀️.
Credential Theft:
🎟️ Kerberos Dumper: Automates the extraction of Kerberos tickets (current or all sessions via admin) and LSASS dumps 🔓.
Advanced Evasion:
🛡️ Defense Evasion: Features polymorphic code 🧬, compression 📦, AES/ChaCha20 encryption 🔐, API Unhooking, and AMSI/ETW bypass to evade EDR detection 🚫👁️.
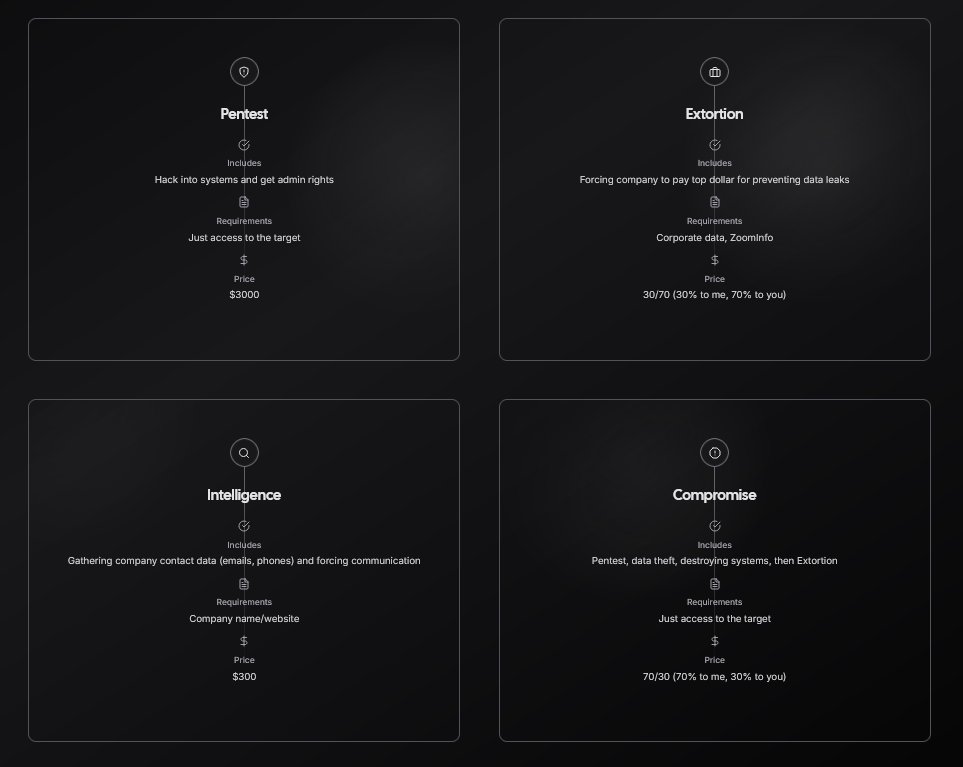
📋 Operational Services & Business Model
The group now operates a structured service menu, allowing third parties to outsource specific stages of an attack chain. The pricing reflects the level of effort and risk assumed by Weyhro:
⚔️ Pentest (Significant fixed sum):
Scope: Hacking into systems and obtaining administrative rights 🔓.
Requirements: Just access to the target 🎯.
🧠 Intelligence (Standard fixed sum):
Scope: OSINT gathering of company contact data (📧 emails, 📱 phones) and forcing communication channels 📣.
Requirements: Company name or website 🌐.
📢 Extortion (30/70 Profit Split):
Scope: Coercing companies to pay to prevent data leaks 💧.
Requirements: Corporate data and ZoomInfo access 📂.
Split: Weyhro retains 30%, client keeps 70% 📉.
💥 Compromise (70/30 Profit Split):
Scope: Full-spectrum attack execution: Pentest, data theft, system destruction 💣, followed by extortion.
Requirements: Just access to the target 🎯.
Split: Weyhro retains 70%, client keeps 30% (reflecting the heavy operational load on Weyhro) 📈.
🌍 Impact & Hypothesis
• 🏗️ Internal Capability to Commercial Product: The release of Weyhro C2 and the specific "Compromise" service strongly suggests that the group is monetizing the exact TTPs (Tactics, Techniques, and Procedures) used during their 2024-2025 ransomware campaign. The "Compromise" service essentially allows unskilled actors to pay Weyhro to conduct a full ransomware-style attack on their behalf 🤖.
• 🗺️ Attribution & Origin: The strict "No-CIS" restriction on the C2 tool reaffirms the likelihood of the operators being based in Russia or Eastern Europe. The naming convention remains ambiguous; it is unclear if "Weyhro" was initially a project name that became the group's alias, or vice versa, but the brand is now being leveraged to sell high-end cybercriminal services 🏴☠️.


English

@RussianPanda9xx It appears that the Weyhro group, which was initially focused on ransomware, has expanded its "business scope." They now provide a "service" kit, and I estimate that this shift has motivated them to develop a tool both for their own use and for rental to third parties 🛠️💻🕵️♂️
English

Announcing the rebrand of TRACLabs → LummaLabs.
This is where I'll be publishing my personal research. And as promised, at 200 followers, new blog is live.
Took more than 24 hours but I have a job, ok, leave me alone 😭
Weyhro C2: because ransomware wasn't paying the bills anymore
lumma-labs.com/weyhro-c2-beca…
English

@RussianPanda9xx In March of this year, a ransomware called Weyhro emerged. I wonder if it is the same team 🧐

English

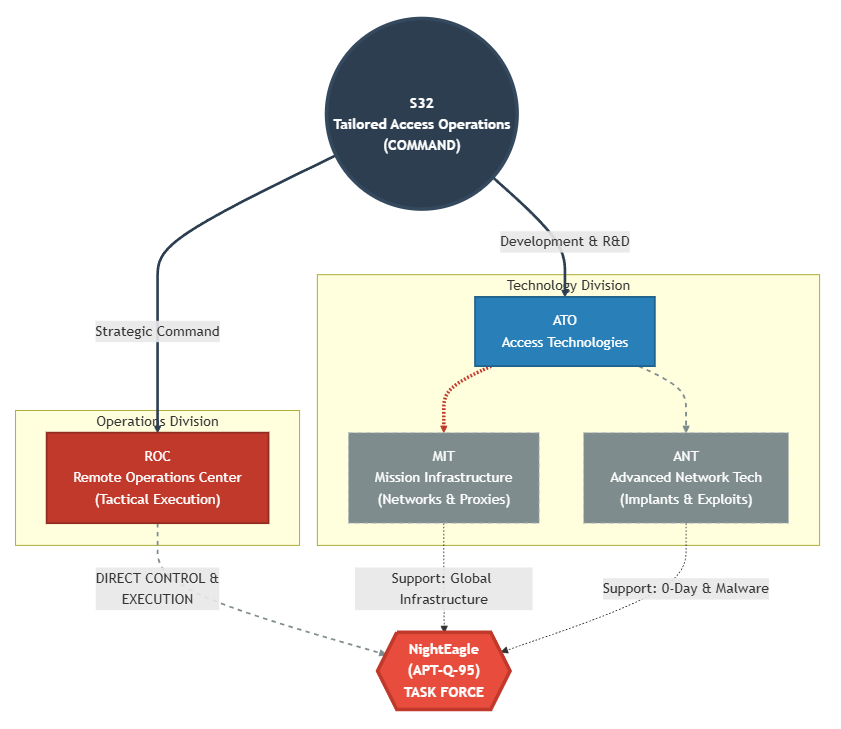
Integrating "NightEagle" into the US Cyber Operations Group (S32 Division) 🕵️♂️🇺🇸
After months of inactivity due to my scientific research, I had this post pending. For years I have been collecting public and leaked information about APT groups, and for this research, I will rely on the data I have gathered regarding the US Cyber Operations Group, focusing specifically on the S32 Division. 🕵️♂️💻
A few months ago, the NightEagle (APT-Q-95) group was exposed. I have analyzed their patterns to locate them within my S32 diagram and observe the correlations:
📍 1. Operational Discipline (ROC) : In my scheme, the Remote Operations Center (ROC) coordinates real-time attacks. NightEagle fits here by operating strictly from 21:00 to 06:00 Beijing time (US West Coast business hours) and without overtime, typical behavior of a regulated military unit.
🌐 2. Massive Infrastructure (MIT) : The Mission Infrastructure Technologies (MIT) unit manages proxy networks and persistence. This matches NightEagle's ability to use "ultra-fast switching infrastructure" and assign unique domains per target, relying on centralized logistics.
🛠️ 3. Access Technology (ATO) : The Access Technologies & Operations (ATO) division develops covert implants. NightEagle employs precisely these elite capabilities: unknown Exchange exploit chains and undetectable in-memory malware.
🚩 Conclusion:I have integrated NightEagle as an execution force (Task Force) under the command of the ROC, but technologically supported by ATO and MIT. It is not an isolated actor, but part of a larger gear in the S32.


English

Hi friends! 👋😇
I’ve been MIA for 7 months because I was fully focused on an academic project I’m really excited about… I just finished my first scientific paper! 📄🚀
It’s been an intense journey of math, strange patterns, and a lot of code while diving deeper into cryptography.
I’m now checking if my university’s scientific journal is the right place to publish it, so the title and details stay secret for now 🤫.
I’m officially back! Thanks for sticking around. ✨
English

@elonmuskTN The best number is 23 because it is formed by the first two consecutive prime numbers, and the union of them also results in another prime.
English

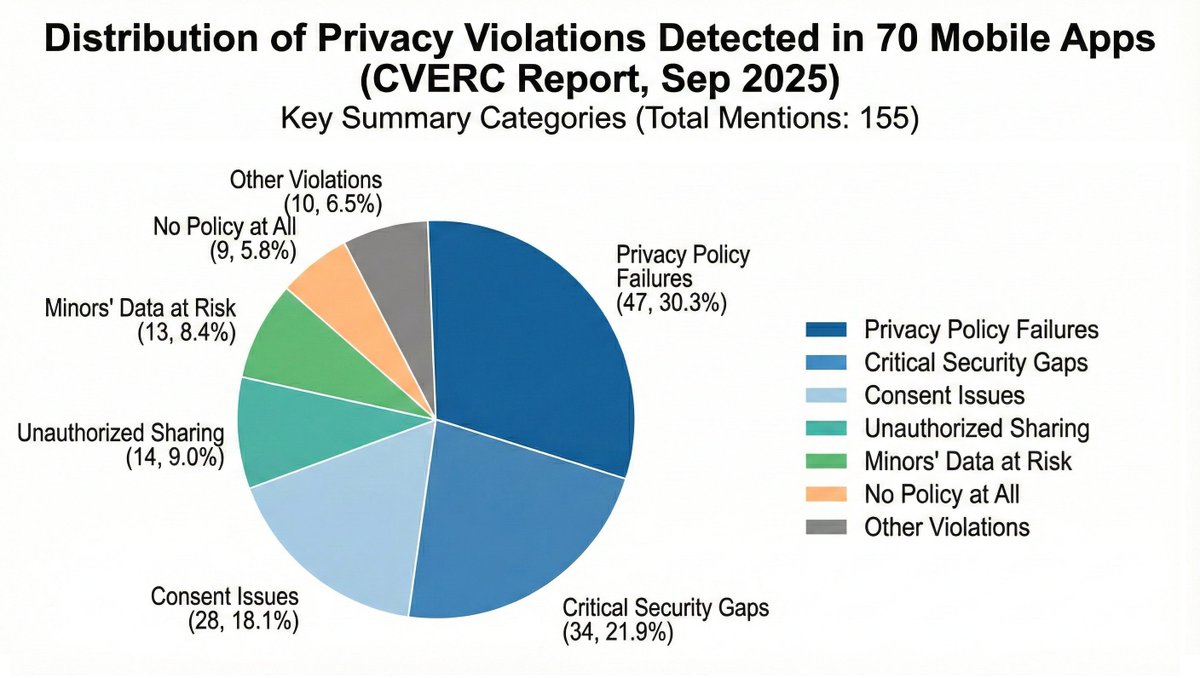
Headline: 🚨 Major Data Privacy Enforcement in China: 70 Mobile Apps Cited for Violations.
China's National Computer Virus Emergency Response Center (CVERC) has officially notified 70 mobile applications for illegal and improper collection and use of personal information.
This detection effort, conducted between September 1 and September 28, 2025, is part of a broader high-level "2025 Personal Information Protection Special Action" involving multiple state ministries (CAC, MIIT, MPS, SAMR) aimed at enforcing the Cybersecurity Law and the Personal Information Protection Law (PIPL).
🔍 Key Insights & Major Violations Detected:
The report identifies 12 distinct categories of compliance failures across the 70 apps. The most significant issues include:
🛡️ Critical Security Gaps: The largest category (34 apps) failed to implement necessary security measures like encryption or de-identification of data.
📜 Privacy Policy Failures: Many apps had inadequate policies that didn't clearly state the scope of collection, were difficult to access, or failed to prompt users approriately upon first launch.
🔄 Consent Issues: Significant hurdles for users trying to withdraw consent, or apps collecting data before obtaining consent.
🔗 Unauthorized Sharing: Sharing data with third parties (via SDKs/plugins) without separate consent or anonymization.
👶 Minors' Data at Risk: Several apps mishandled the data of minors under 14, lacking specific rules or guardian consent.
🚫 No Policy at All: 9 apps were found operating with absolutely no privacy policy.
📉 Enforcement Outcome: Besides listing the current 70 offenders, CVERC noted that 28 apps identified in a previous report failed to rectify issues upon re-testing and have been removed from app distribution platforms.
English

🛰️ Cyberattack Attributed to the NSA Against China’s National Time Service Center (NTSC) 🇨🇳
China’s cybersecurity authorities released a detailed technical report accusing the U.S. National Security Agency (NSA) of conducting a long-term cyber-espionage campaign against the National Time Service Center (NTSC).
The operation allegedly began in March 2022 with mobile-based espionage and extended until mid-2024, targeting China’s high-precision timing and navigation infrastructure.
🎯 Strategic Objectives
• Achieve persistent access and long-term surveillance within NTSC’s internal networks.
• Exfiltrate credentials and system configurations to maintain covert control.
• Prepare offensive capabilities against high-precision timing and navigation systems, critical for national infrastructure. 🛰️
🛠️ Attack Tools & Methods
Initial access: Exploitation of a foreign SMS service vulnerability to spy on 10+ NTSC employees and steal mobile data (contacts, messages, photos, location). 📱
→ Stolen credentials were later used for remote logins (80+ sessions) from anonymous nodes during 2023. 🌙
Three main malware families identified:
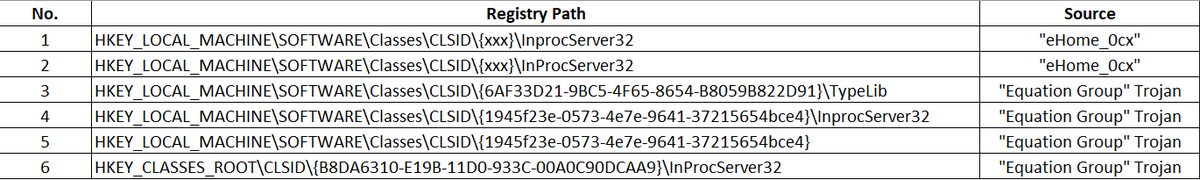
1.- eHome_0cx – persistence & initial control (auto-start via DLL hijacking).
2.- Back_Eleven – encrypted tunneling, traffic redirection, and C2 communication.
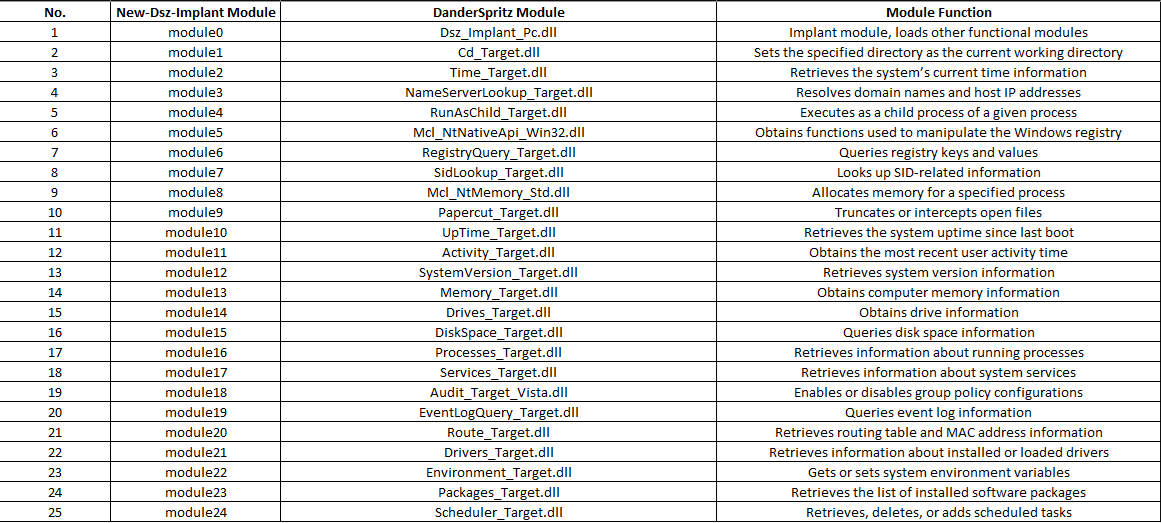
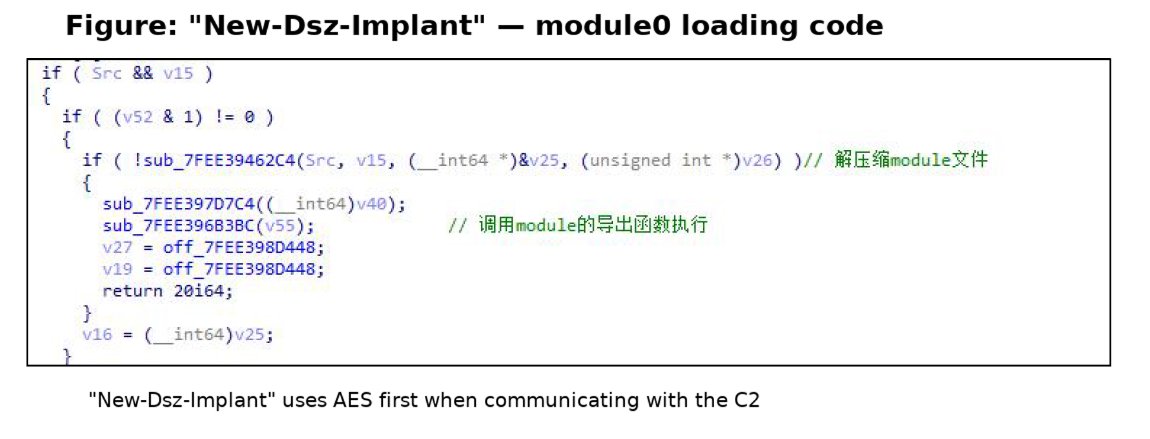
3.- New_Dsz_Implant – modular data-theft framework (25 plug-ins for system discovery and file access). ⚙️
Combined use achieved four-layer encryption (RSA + AES + TLS + local loopback), making network traffic nearly impossible to detect or decrypt. 🔐
Several attacks involved remote antivirus shutdowns, in-memory execution, and simulation of user behavior to evade EDR detection. 🧩🛡️
🌍 Command-and-Control Infrastructure
Over 40 C2 servers traced across the U.S., Europe, and Asia, showing a globally distributed relay network to conceal attribution. 🌐
⚠️ Impact & Risk
The attackers reached deep internal systems such as authentication servers and firewalls, posing a severe threat to national infrastructure that depends on synchronized timing — both civilian and military. ⏱️💥

English