

Oleg
217 posts

@Cyber_0leg
#Cybercrime #CTI #OSINT #Cybersecurity https://t.co/b3uWuDBEVs




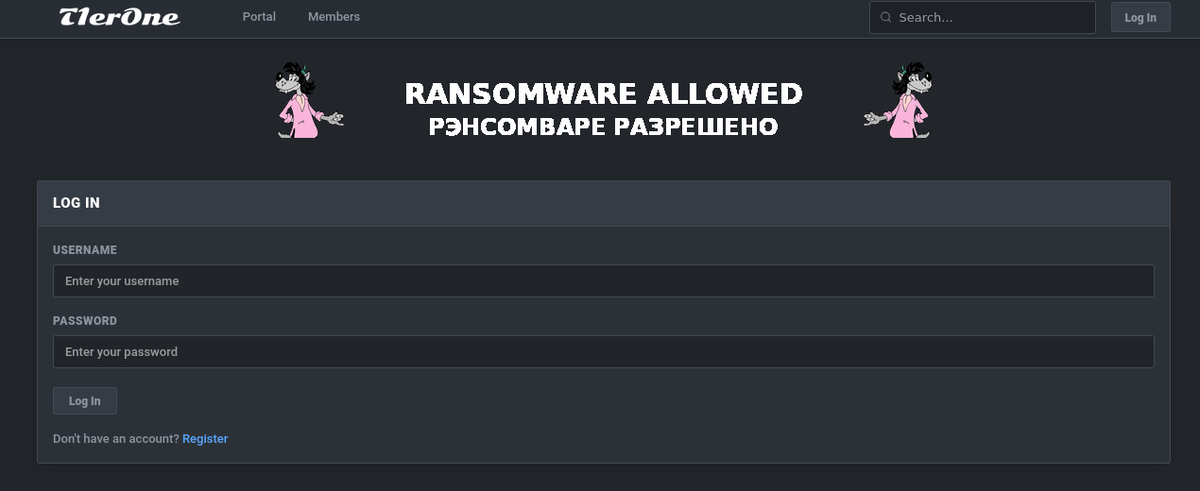
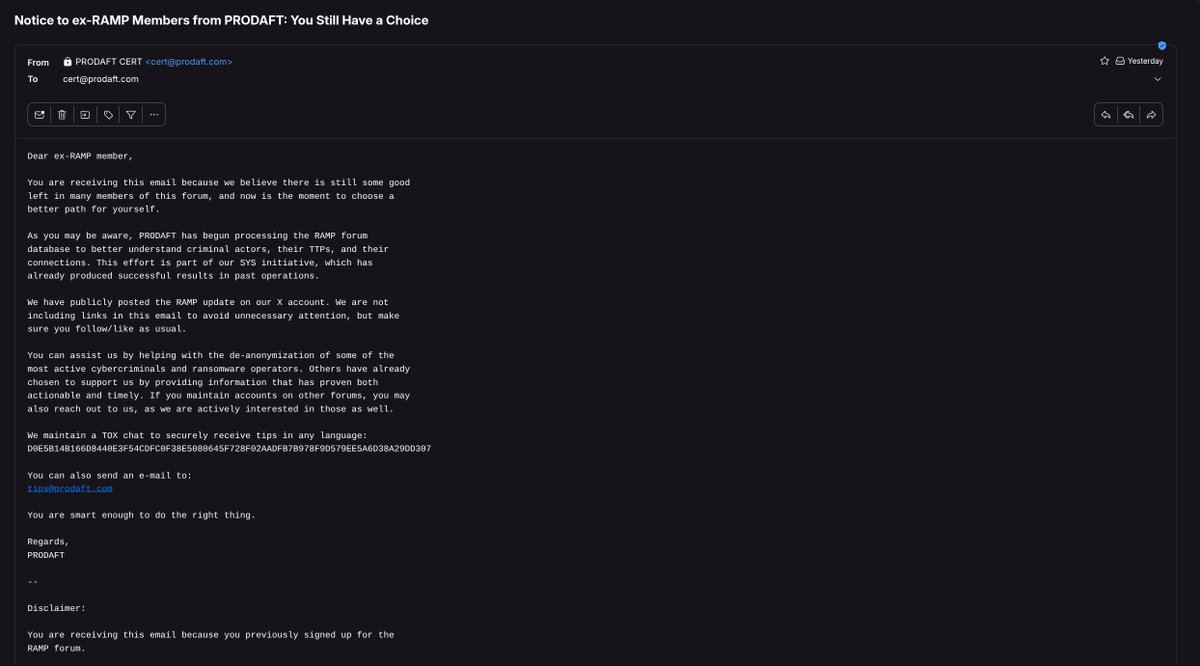
vibecoder threat actors, threat actors who end up hacking themselves, and many more undiscovered stealers along with their logs… I’ve started writing my blog post..























Chat, we are cooked Discord is being extorted by the people who compromised their Zendesk instance They've got 1.5TB of age verification related photos. 2,185,151 photos tl;dr 2.1m Discord users drivers license and/or passport might be leaked. Unknown number of e-mails







Looks so good @club31337 @AlvieriD @joetidy @RussianPanda9xx