Sabitlenmiş Tweet
skynet
2.6K posts

skynet
@sky31337
• ghost in the shell • reformed blackhat • SEC hacker •
127.0.0.1 Katılım Haziran 2020
980 Takip Edilen4.2K Takipçiler
skynet retweetledi

Russia 🇷🇺 sentenced the carding gang leader “Flint” and 25 associates for large-scale payment fraud, mainly targeting stolen financial data, highlighting rare domestic prosecution of cybercriminals tied to global fraud networks.
therecord.media/russia-flint-c…
More information: t.me/cIub1337/490
English
skynet retweetledi

Footage of the detention of the administrator of LeakBase forum in Taganrog, Rostov Region, Russia 🇷🇺. Via MVD representatives
Report: "According to available information, the platform hosted hundreds of millions of user accounts, bank details, logins and passwords, as well as corporate documents obtained as a result of hacking. Over 147 thousand users registered on the forum could buy and sell this data, as well as use it to commit fraudulent actions against citizens.
During the search at the detainee's residence, technical equipment and other items of evidentiary significance were seized.
A criminal case has been initiated by the investigator of the Main Investigative Department of the Ministry of Internal Affairs of Russia in Moscow on the grounds of crimes provided for in parts three and six of Article 272.1 of the Criminal Code of the Russian Federation. A preventive measure in the form of detention has been chosen against the defendant."
English
skynet retweetledi

Russian Citizen Sentenced to Prison for #Hacking into U.S. Companies and Enabling Major #Cybercrime Groups to Extort Tens of Millions of Dollars
“Volkov, 26, of St. Petersburg, Russia, was an “initial access broker,” that is, a person who specializes in gaining unauthorized access to computer networks and systems of corporations and organizations and selling that access to other cyber threat actors such as ransomware groups. #Volkov found vulnerabilities in computer networks and systems, identified ways to access those networks and systems without authorization, and sold that illicit access to conspirators who were also cybercriminals.”
justice.gov/opa/pr/russian…
English

Dissecting the #RAMP (Russian Anonymous Marketplace) #Ransomware Forum
ddanchev.blogspot.com/2026/02/dissec…
English

@Cointelegraph It’s very unattractive to steal photos from Dmitry @ddd1ms and not even provide a link to the original source. Reputable publications don’t behave like that.
fyi @vxunderground
English

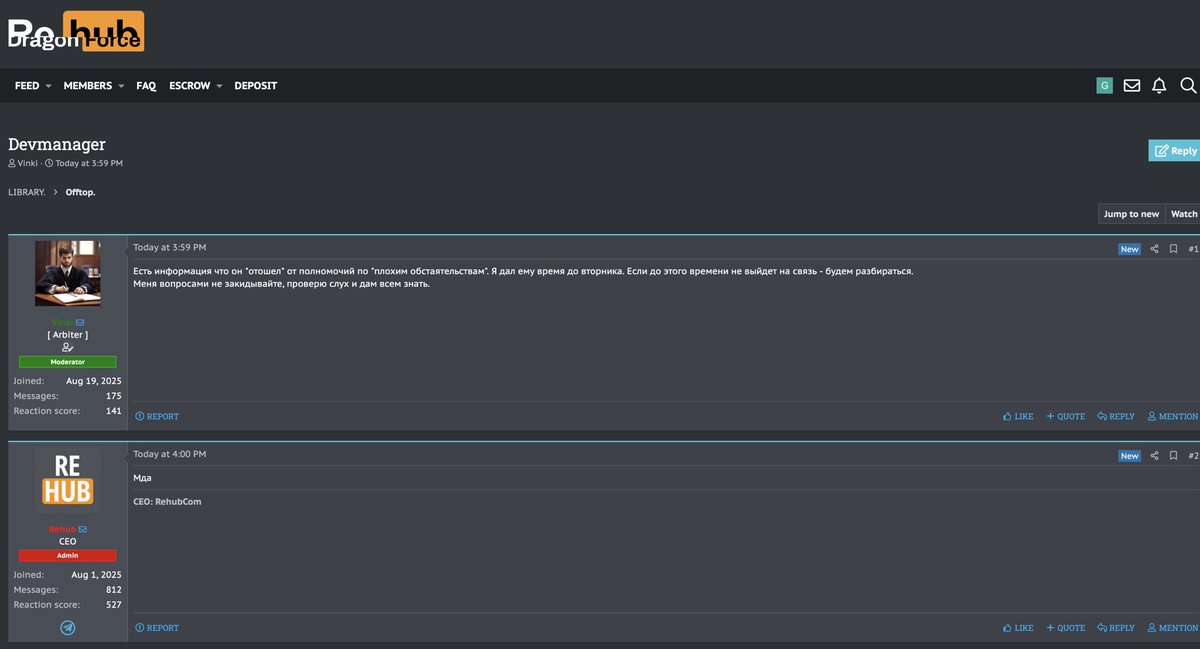
Devman has “stepped away” due to “unfortunate circumstances.”
On the ReHub forum, this was discussed carefully — the thread was originally titled “Devmanager”, then it was renamed to “Dv” in order to avoid drawing broader attention.
Post dated 06.02.2026:
“There is information that he has ‘stepped away’ from his role due to ‘unfortunate circumstances.’ I gave him time until Tuesday. If he doesn’t get in touch by then, we’ll sort it out.
Don’t bombard me with questions — I’ll verify the rumor and let everyone know.”
After that, the topic was quietly closed, with a message along the lines of:
“Everything is OK. He has verified. An update will be published. Closed.”
http://rehubg7wpn5vuwttbzqrzm5epq6ta5mqm6cbfpn7wtukaskzte3ehcyd[.]onion/threads/1673/
I cannot cite closed sources — I’m only showing what managed to leak out.
English

A forum thread advertising Qilin RaaS activity alongside Cry0 has been spotted.
The post openly recruits affiliates and outlines ransomware capabilities including selective encryption modes and shadow copy removal.
jprrin6bqe3flvtpyxkt4zsmzc3u6vvn7ahgtcbul224w3xn4h3gawid[.]onion
t1eron3[.]vip

English

@sky31337 Great find! I wondered where the ramp refugees would go, now it’s clear.
English

And so another chapter begins.
skynet@sky31337
A forum thread advertising Qilin RaaS activity alongside Cry0 has been spotted. The post openly recruits affiliates and outlines ransomware capabilities including selective encryption modes and shadow copy removal. jprrin6bqe3flvtpyxkt4zsmzc3u6vvn7ahgtcbul224w3xn4h3gawid[.]onion t1eron3[.]vip
English

@FalconFeedsio @DarkWebInformer @AlvieriD @aejleslie @vxunderground @vxdb @campuscodi @BleepinComputer @Reuters @LawrenceAbrams @g0njxa @RussianPanda9xx @fastfire @H4ckManac @SOSIntel @banthisguy9349 @Threatlabz @PRODAFT @ValeryMarchive @AShukuhi @ddd1ms @3xp0rtblog @Jon__DiMaggio @SttyK @jamieantisocial @UK_Daniel_Card @EvilRabbitSec @Cyber_0leg @GangExposed @bellingcat @Ransom_DB @azalsecurity @joetidy @WhichbufferArda @malwrhunterteam @cyberfeeddigest @H4ckmanac @ransomnews
QAM
skynet retweetledi

skynet retweetledi

RAMP Forum User Intelligence Available for Our Platform (U.S.T.A. & Catalyst) Members
🫶Our SYS initiative remains highly active, as a well-known forum member voluntarily contacted us. We are grateful for their contribution. Even when admins attempt to dox each other for 10 BTC, it's good to see some members doing it voluntarily for us.
🔍As a result, our team has acquired intelligence associated with 7,709 RAMP forum users, including the following high-value investigative datasets:
📧Private messages exchanged between threat actors, enabling reconstruction of operational planning and coordination;
👾Attachments sent and received between threat actors, supporting malware, tooling, and infrastructure attribution;
🔐Authentication and login activity, facilitating access-pattern analysis and operational security assessment;
🌌Forum search history, providing insight into intent, targeting, and operational focus;
🧐Profile information, including but not limited to registered email addresses, supporting identity correlation and cross-platform attribution;
🗣️Chat room and group communication metadata, indicating collaboration structures and coordinated activity across specific operations and campaigns.
We will be correlating these datasets to support and advance multiple previously unsolved investigations.
#cyberintelligence #ramp #LockBitSupp <3


English

Where RaaS going after RAMP takedown!!

Raaz@solostalking
Where users going after Breachforums/XSS honeypot version
English
skynet retweetledi