Defi Nerd
286 posts

Defi Nerd
@Defi_Nerd_sec
Web3/DeFi Security Researcher & Enthusiast. Hosted by DARKNAVY @DarkNavyOrg.













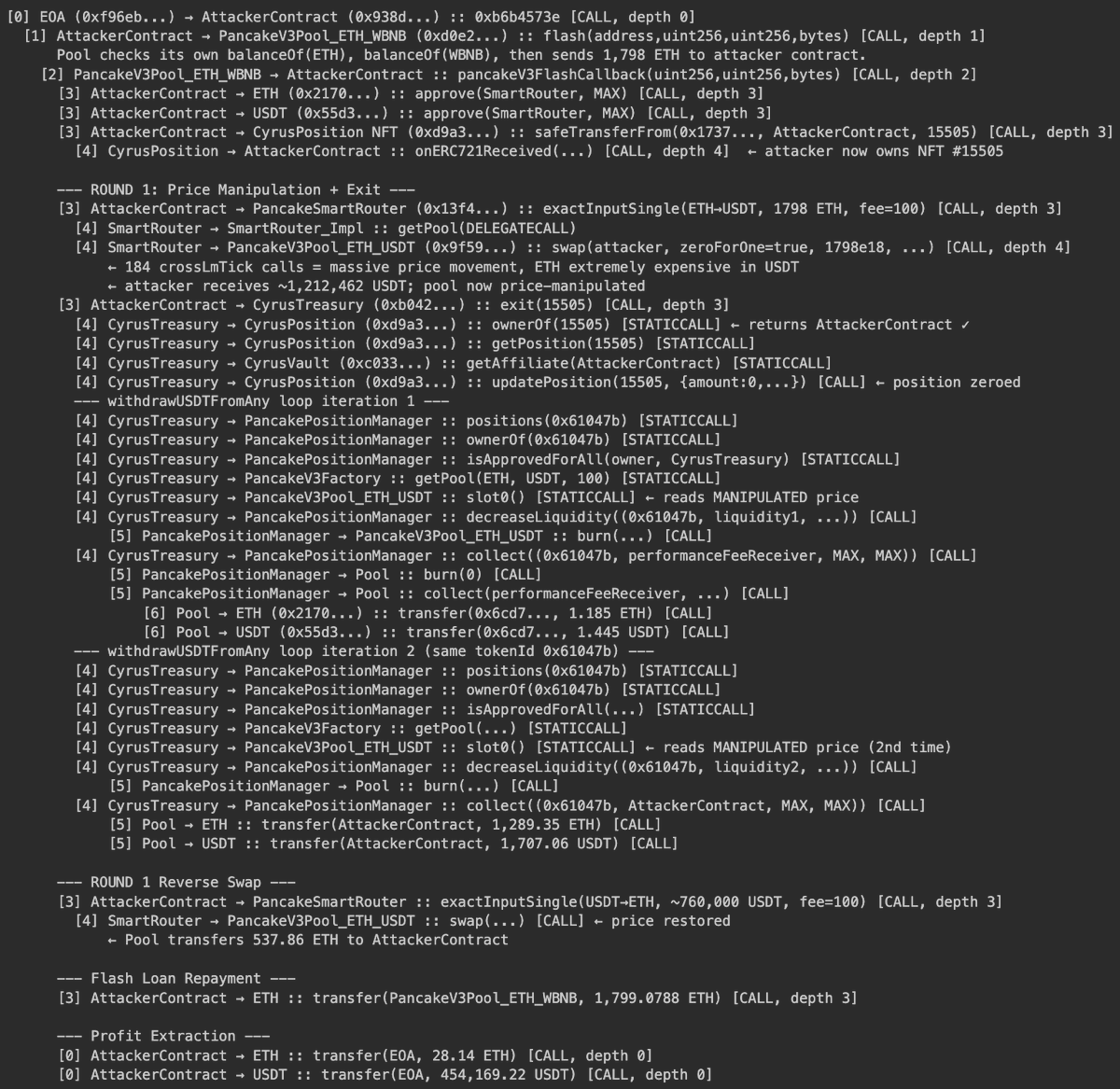
Another day, another $500k hack Remember that for every AI auditor company you see on the timeline there are 50 AI blackhats working 24/7 I only expect this to get worse bscscan.com/tx/0x2b7efdac5…


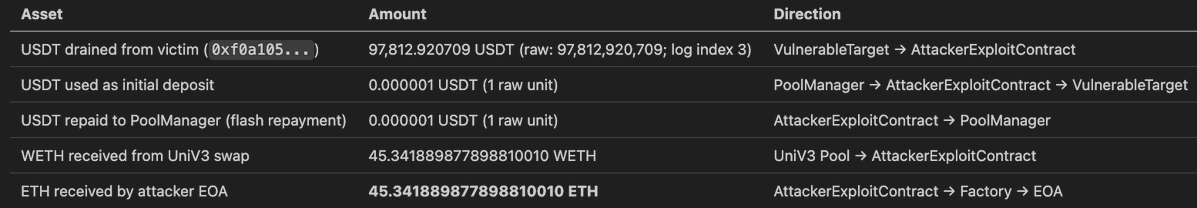
🚨An unverified escrow-like contract at on Ethereum Mainnet was fully drained in block 24,707,679 (timestamp 2026-03-22 UTC) through an **integer overflow** in its deposit function `0x317de4f6`. The deposit function accumulates entry amounts into a running total using unchecked arithmetic before passing that total to `transferFrom`. By supplying two entries whose amounts sum to `1 mod 2^256`, the attacker caused only 1 raw USDT unit to be pulled from them via `transferFrom`, while the per-entry amounts stored in the claim mapping remained uninflated — giving the attacker a stored claimable balance of 97,812,920,709 raw USDT (the full pool) at a cost of 1 raw unit. The attacker then called `claim()`, which faithfully transferred the stored amount, draining ~97,812.92 USDT. The stolen USDT was swapped to approximately 45.34 ETH via the Uniswap V3 USDT/WETH pool, and sent to the attacker EOA through two self-destructing disposable contracts.




🚨TenArmor Security Alert🚨 Our system has detected two suspicious attacks involving two unverified contracts 0xf0a1/0x39ed on #ETH by an attacker, resulting in an approximately loss of $108K. Attack transactions: etherscan.io/tx/0x73bd1384e… etherscan.io/tx/0x1382e898a… With TenArmor’s TenMonitor, you get early detection and automated response to on-chain attacks. Need protection? Reach out anytime! #TenArmorAlert #TenArmor