Socialk@s retweetledi
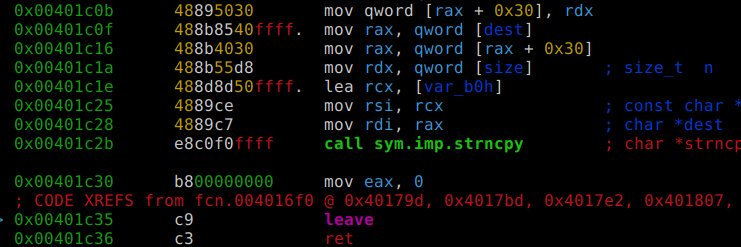
The world's fastest Android/DEX decompiler (garlic by @neocanable ) meets radare2 ( @radareorg ) 🔥
github.com/radareorg/r2ga…
English
Socialk@s
6.1K posts

@Disbauxes
r2 devotee; retro-gaming lover; ocasional CTF player; constant reader; hacking the hours away since 2015... https://t.co/de4ZVjdi0k