DrStache
341 posts

DrStache
@DrStache_
CTF player with @AperiKube 🧊 Co-author of @AZORult_Tracker 🦅
France Katılım Temmuz 2016
628 Takip Edilen1.2K Takipçiler
DrStache retweetledi

@kmkz_security @Blaklis_ @joaxcar Here are two recent examples where reflected XSS were exploited by APT groups.
twitter.com/billyleonard/s…
proofpoint.com/us/blog/threat…
billy leonard@billyleonard
TAGs favorite 🤖 @wxs has been finding new FROZENLAKE (APT2⃣8⃣) daily, including XSS on 🇺🇦 gov websites they are using for cred phishing. For the past few months, FL has been shipping phished creds to compromised Ubiquiti devices .. 6/🧵
English

This one was weird "we had a regression and many others reported it, so we will lower the bounty to 10%". I mean, either you have a vulnerability or you dont. Blaming regression was a new one..
publiclyDisclosed@disclosedh1
Reddit disclosed a bug submitted by mrzheev: hackerone.com/reports/1962951 - Bounty: $500 #hackerone #bugbounty
English
DrStache retweetledi

Aperi'Kube termine deuxième au #BreizhCTF2023 🥈
Merci à @gcc_ensibs et aux copains (cc @Zeecka_, @b0oml) pour les challs, et un gros GG aux admins pour l'infra !
@teamBrewette RDV l'année prochaine 🤗

Français

@dor0n1 @James_inthe_box @jstrosch @JAMESWT_MHT @executemalware @fumik0_ @ViriBack @Mister_Ch0c It's not maintained, but I try to keep LP-DB up to date lp-db.github.io/lp-db/
English

@James_inthe_box @jstrosch @JAMESWT_MHT @executemalware @fumik0_ @ViriBack @Mister_Ch0c u still Update this one?
English

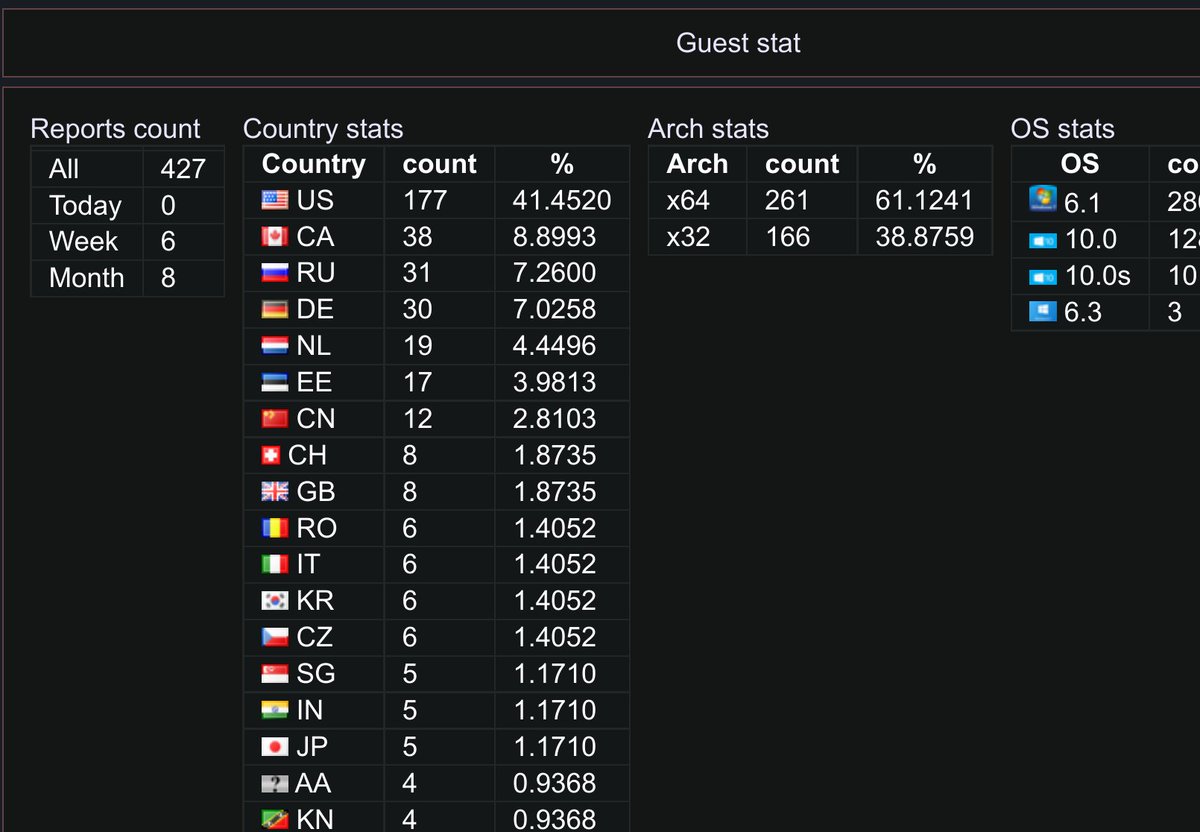
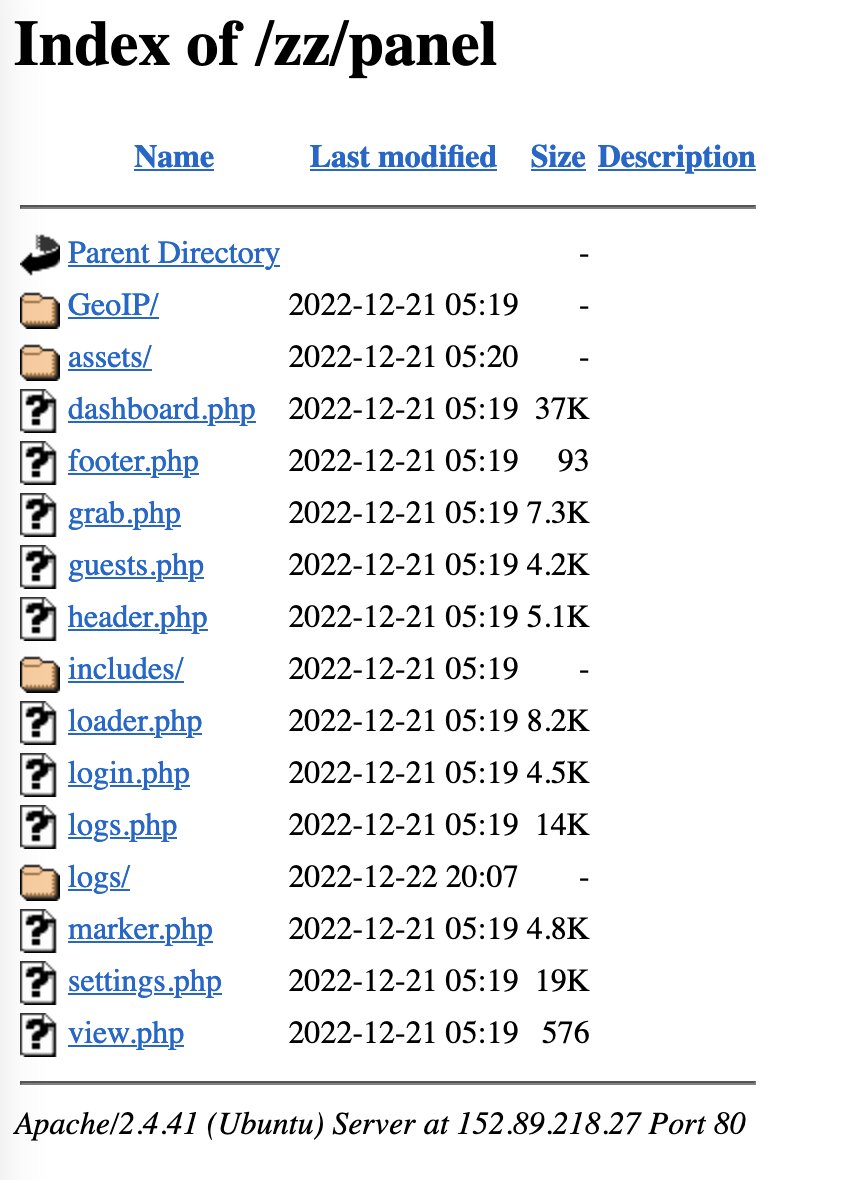
#opendir stealer #panel - poss #vidar or #arkei?
hxxp://152.89.218[.]27/zz/
@James_inthe_box @JAMESWT_MHT @executemalware

HT
DrStache retweetledi

Après une longue absence, Aperi'Kube remporte la 1ère place au #FakeCTF 🎉! Merci aux organisateurs @teamfakenews et bravo aux autres équipes ! Cc @teamBrewette et FC Ronald 👌.

Français

@Abjuri5t @AZORult_Tracker @HybridAnalysis @fr3dhk @abuse_ch @ViriBack @malbeacon Yeah, Delis LLC is full of AZORult C2 azorult-tracker.net/s/asn/AS211252
English

Cluster of #malware C2s hosted on 45.133.1.0/24 - DELIS LLC 🔥
45.133.1[.]13
45.133.1[.]20
45.133.1[.]45
45.133.1[.]107
45.133.1[.]191
Includes #C2 servers for #AZORult #Redline #Mirai and #Lokibot
cc @AZORult_Tracker @HybridAnalysis @fr3dhk @abuse_ch @ViriBack @malbeacon
English

@pr0xylife @ankit_anubhav @x3ph1 @Max_Mal_ @1ZRR4H @Ledtech3 Panels' statistics azorult-tracker.net/s/asn/AS60567
Català

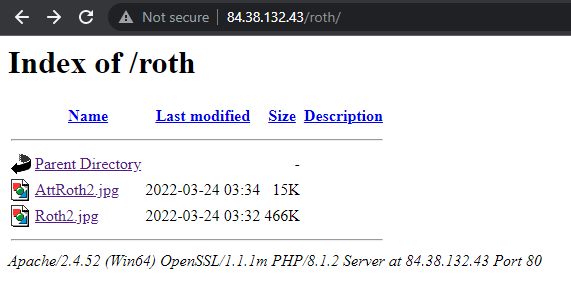
@ankit_anubhav @x3ph1 @Max_Mal_ @1ZRR4H @Ledtech3 Have some more :) They really are being creative...
bazaar.abuse.ch/sample/12a5eb4…
http://84.38.132.]43/roth/AttRoth2.jpg
http://84.38.132.]43/roth/Roth2.jpg
c2'
http://185.29.8.]100/Panel/index.php
English
#Azorult RabbitHole
Malspam
⬇️ ISO attachment
⬇️ VBS unzip
⬇️ PowerShell launch
⬇️ Binary to ASCII conversion
⬇️ Download fake png from opendir
⬇️ Compile payload on fly using aspdot_net
⬇️ Theft
⬇️ POST to C2
⬇️ Persistence by moving file to startup
bazaar.abuse.ch/sample/e93cc14…




English

@Marco_Ramilli @_odisseus @Arkbird_SOLG @JAMESWT_MHT @JCyberSec_ You can follow the evolution of the number of victims since November on @AZORult_Tracker
azorult-tracker.net/panel/6198ca8f…
English
DrStache retweetledi

I love how they casually mention having a shell on Conti server 🤩
pancak3@pancak3lullz
“One of the most valuable pieces of threat intelligence we discovered is the the real IP address of Conti’s TOR hidden service and contirecovery[.]ws, and 217.12.204.135, on Tuesday, 28 September 2021 21:30:03 UTC.”
English
DrStache retweetledi
DrStache retweetledi

For those who are curious about how Azorult Tracker works, @DrStache_ and @b0oml had the opportunity to present the project at the #hitchhack2021 organized by @hack2g2. The replay is available (it's in French 🇫🇷).
youtube.com/watch?v=h8SJ5R…
YouTube
English
DrStache retweetledi

Reprise des festivités de la #hitchhack2021 en live à 14h avec @DrStache_ et @b0oml pour "@AZORult_Tracker : behind the scene" 🦅
GIF
Français

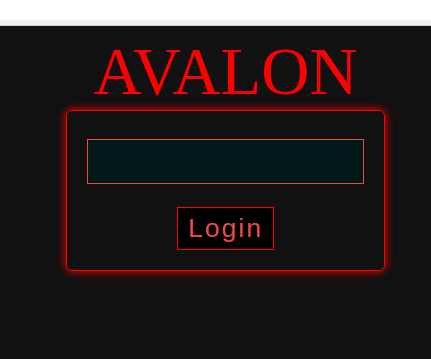
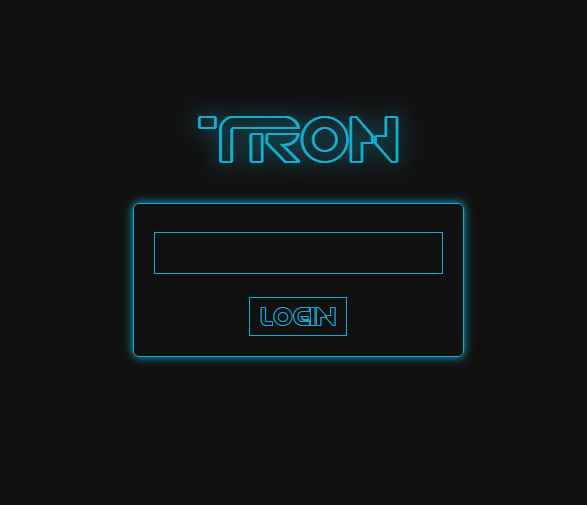
@ViriBack The login page and css files are similar to the TRON stealer panel.
github.com/lucianmaxx/TRO…
English

LP-DB now contains over 300 login pages 🎉
lp-db.github.io/lp-db/
Thanks to @ANeilan for the contributions!
English

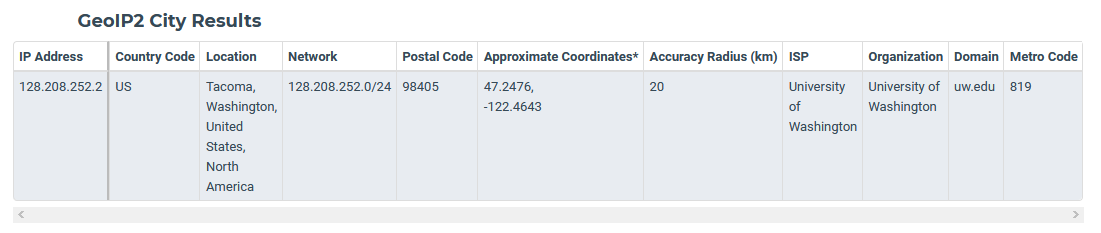
@OSINTDojo We can then validate the location via google maps: 47.24471937419535, -122.43736565558046

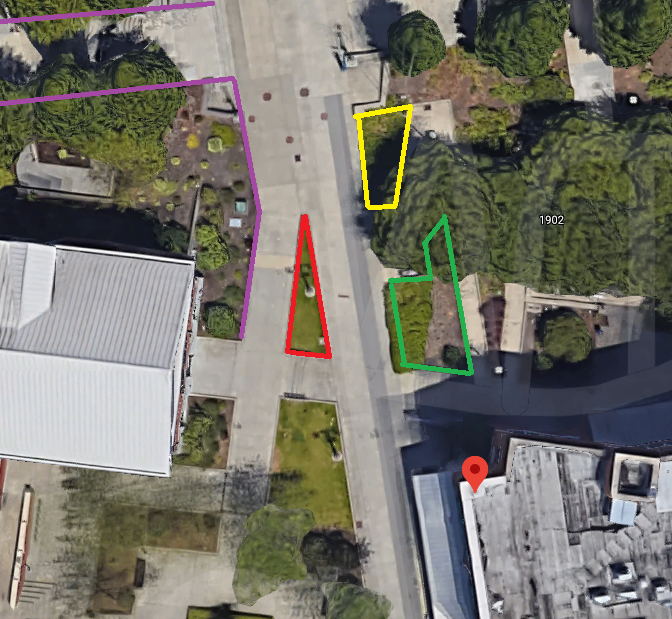
English

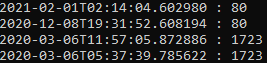
@OSINTDojo According to the date on the photo, it was taken at 5:17:37 on February 5, 2021.
We search for the camera IP on maxmind's GeoIP2 database in order to locate it: Tacoma, Washington, United States.
shodan.io/host/128.208.2…
maxmind.com/en/geoip-demo

English

For today’s #MondayMotivation #OSINT challenge, see if you can answer the following questions about the attached photo.
Which University runs the ISP for this webcam?
At what time did the webcam take this photo?
What is the lat/long of the attached photo?

English

@OSINTDojo We can finaly use the Shodan API in order to find the port that was exposed on the IP address 14.250.13[.]233.
#historic-data" target="_blank" rel="nofollow noopener">help.shodan.io/developer-fund…

English

@OSINTDojo Searching for "Dong Hoi, Tinh Quang Binh" on Google image we find this website quangbinhtravel.vn/du-lich-thanh-… It contains a picture of a hotel that looks like the one on the webcam view, the Vinpearl Hotel.

English

For today’s #MondayMotivation #OSINT challenge, see if you can answer the following questions about the attached photo.
What city is this webcam located in?
What is the name of the hotel in the background?
What port was previously open on this device that is now closed?

English