Drift Victims Committee
96 posts


Drift Victims Committee
@DriftVictims
Drift Protocol Victims Committee. Collective action against management negligence. Enforcing recovery. https://t.co/cZYSDVPO0L



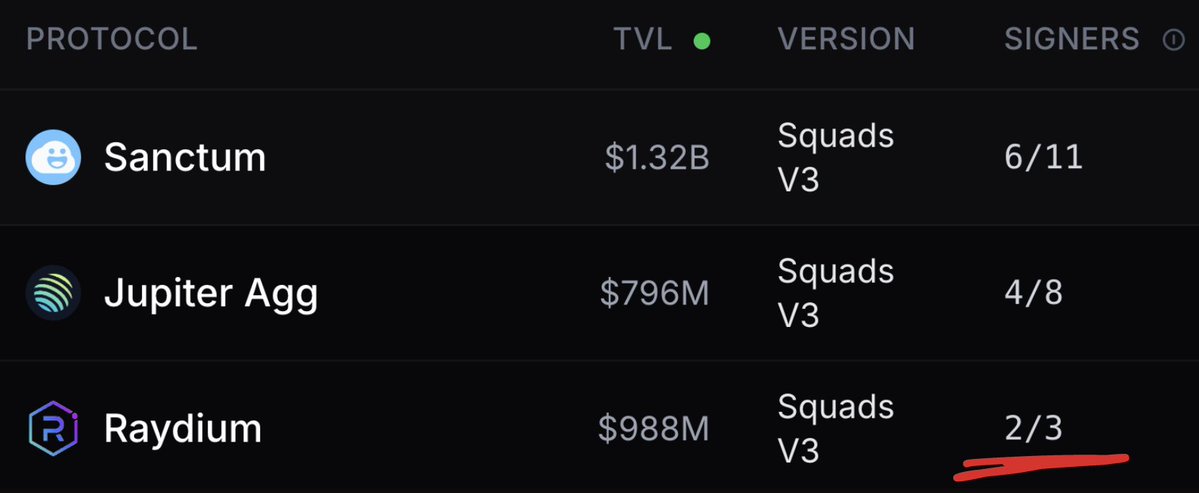
Spent some time digging further into why Drift were targeted and whether other Solana protocols are showing similar risk. Their 6 month social engineering story breaks down how the attack happened, but not why they were picked in the first place. I looked into their governance operational history and applied the same checks to 49 others Drift's pre exploit governance setup had never been updated since the multisig was created in April 2024. Across 918 transactions on the original multisig over its lifetime: - Zero config changes. No threshold updates, no member rotations, no timelock adjustments - Signing activity concentrated in a narrow UTC window, making the operating schedule predictable - An external configAuthority key that could change threshold, members, and timelock without any multisig vote at all. This was the only protocol in my scan with this configuration. Squads default is for the multisig to control itself, so any config changes go through member voting. Drift has run three separate multisigs across this timeline, original, exploited, and recovery, and the same external configAuthority was manually attached to every one of them. It's still live today - Zero timelock between approval and execution - Durable nonce accounts in use by signers - Threshold ratio below what Squads recommends - Same person could propose and execute Every one of these conditions is public on-chain As for the other 49 Solana protocols, here's what I've found Multi purpose governance keys The same key approving multisig governance actions is also being used as someone's personal wallet across multiple protocols. What I found on those keys: - Meme coin trading through pumpfun and similar platforms - Airdrop farming across ecosystem campaigns - NFT marketplace activity on Magic Eden and Tensor - General swap volume through DEX aggregators - Team members trading on their own protocol The worst one I found had a large number of swaps on the same key that approves multisig actions. Squads recommends keys used only for Squads transactions. By not following this, every dapp it touches, every blind signature, every approval prompt is another place where that signing power can be phished or drained Single proposer pipelines One signer creates most of the proposals and is also the top approver. This is happening at several protocols. Even with a multi signer threshold, one person is really setting the agenda and pushing things through Multisig bloat Some protocols list more members on their multisig than actually sign. The member count makes it look distributed, but the signing activity tells a different story. Some teams might say these are emergency only or board signers, which is a fair setup. The problem is those members are still being counted in the public threshold. A 5 of 9 looks like distributed control on paper, but if 4 of those members have never signed, the real signing set is smaller than what's advertised. For multisigs that are genuinely dormant, the real threshold drops to whoever still controls the active keys No role separation Squads V4 has three permission types. Proposer, Voter, Executor. Splitting them across members stops any single key from both creating a proposal and pushing it through to execution. More than half of the Squads V4 protocols I scanned give every member full permissions, which combines all three. Squads docs say to always approve and execute in separate steps, and to avoid the approve + execute feature. More than half of V4 protocols have set this up to make that combined action possible Below recommended threshold Squads recommends a threshold of 4 of 6 or higher. No V4 protocol I scanned meets both the suggested threshold and ratio. Smaller teams have a fair point, they might not have 4 to 6 trusted people to act as signers. That's a legitimate reason to fall short on that specific recommendation. What it doesn't excuse is the rest. A 3 person team can still: - Avoid giving every key all three permissions - Add a timelock - Use dedicated keys for governance The team size argument only covers the absolute member count. Most of the protocols that fall short on threshold also fall short on the practices that have nothing to do with team size No timelocks Most of the Squads V4 protocols I scanned have zero timelock between approval and execution. Squads recommends 10 to 15 minutes for program upgrades and longer for treasury. The Drift exploit happened with zero timelock. V3 multisigs can't add timelocks at all, that's a known limit of the older program. But there are many V4 protocols that haven't turned one on. This is 3 steps in the multisig settings Durable nonces still in use The Drift exploit used pre signed transactions held in durable nonce accounts. Signers were tricked into signing transactions they thought were routine, and those signatures stayed valid indefinitely because the nonce replaces the normal blockhash expiry. More than a week later, the attacker submitted them and took admin control Squads has a 2 minute rule telling signers to wait 2 minutes between signatures, so any captured blockhash expires before it can be replayed. That defends against signature capture attacks, which is a different attack type to Drift's. Durable nonces break that defence too. If a signer has an active nonce account, the blockhash expiry doesn't protect them either way Several other protocols have signers using durable nonces. When I measured the gap between their consecutive signatures, most are signing seconds apart. The Drift style risk isn't being addressed, and the 2 minute rule isn't being followed either Solana's own docs now have a deprecation warning on durable nonces, pointing to an active discussion about removing them entirely. The base layer is questioning whether this should exist at all Off hours config changes The Drift exploit executed in the early hours of the morning in the Singapore time zone. Other protocols show patterns of operating in concentrated time windows. Teams based in Asia or the Pacific will rightly point out that what's 2am UTC for someone else is their working day. The pattern I'm describing isn't about a specific timezone, it's about predictability and visibility. A multisig that consistently makes config changes when most of its users and watchers are asleep has a smaller detection window than one whose changes are spread across the day. The fix isn't to match someone else's schedule, it's to avoid bunching sensitive changes when no one's around to notice What I think this means Some of these are coincidences. Some are operational shortcuts. Some are deliberate choices that work for the team behind them. But when you put the pieces together, they tell a story. Drift had those pieces sitting in plain view long before the 6 month operation started. The insider access made it possible, but the governance setup made it easier than it needed to be Other protocols have versions of the same framework Drift had. The same conditions Squads explicitly warns against are present right now Looking at the on-chain data, it's clear some protocols are taking security more seriously than others. Granted, there are edge cases like program timelocks and other nuances hidden without disclosure. Others could learn a lot from how the stronger ones have their governance set up Why things need to change The Drift exploit didn't just impact Drift. It cascaded through 22 other protocols, something I covered in more depth in my recent DeFi article. Yield aggregators, vaults, and lending positions were all plugged into Drift behind the scenes. The same conditions that enabled that cascade are sitting on other protocols today. Billions in TVL are wired together across the ecosystem. At that scale, a governance failure at one protocol becomes everyone else's problem too A lot of the post exploit conversation mentioned Circle for their lack of urgency. I'm not excusing how they handled the situation, but you shouldn't rely on others to patch vulnerabilities you ignored. If the basic governance practices Squads has published were being followed, we probably wouldn't be debating Circle's response time to Drift in the first place. Everything here was discovered on-chain. The Squads best practices I referenced are published on their site. None of this is gated or insider information. It takes some work to surface, but the raw data is public. Anyone motivated enough can see this for themselves h/t Helius - goated RPC



If you're wondering when stablecoin issuers MUST freeze assets, this podcast is worth a listen. @austincampbell and I dive deep into the legal requirements of issuers like Circle, who recently froze USDC after a court order but failed to after the Drift exploit.


Today, Drift is announcing a collaboration with @tether and other partners totaling up to nearly $150 million to support our commitment to a relaunch with USDT at the center, and a path to user recovery. These funds encompass a $100M revenue-linked credit facility, an ecosystem grant, and loans to market makers, designed to fund a dedicated user recovery pool. Learn more 👇


Today, Drift is announcing a collaboration with @tether and other partners totaling up to nearly $150 million to support our commitment to a relaunch with USDT at the center, and a path to user recovery. These funds encompass a $100M revenue-linked credit facility, an ecosystem grant, and loans to market makers, designed to fund a dedicated user recovery pool. Learn more 👇

1/ Every day @DriftProtocol stays silent, the on-chain evidence speaks louder against them. We aren't here for PR bedtime stories. No more hiding. Time to answer questions 👇 @Solana #DriftProtocol #DeFi #Exploit















#DriftProtocol #Solana #Exploit To everyone who missed the tech details: For years, your funds on Drift weren't protected by a decentralized council. They sat behind a simple, single-signature wallet with unilateral power. A lone key. Zero actual consensus. Total negligence!



1/ The $500M+ TVL & Single Point of Failure Drift has long marketed its security as being rooted in a decentralized 2-of-5 Squads Multisig. However, they deliberately omitted a critical architectural fact - Drift utilized (and still does) a Controlled Multisig configuration.