hexens
1.8K posts


hexens
@hexens
Security for those who cannot afford a mistake.







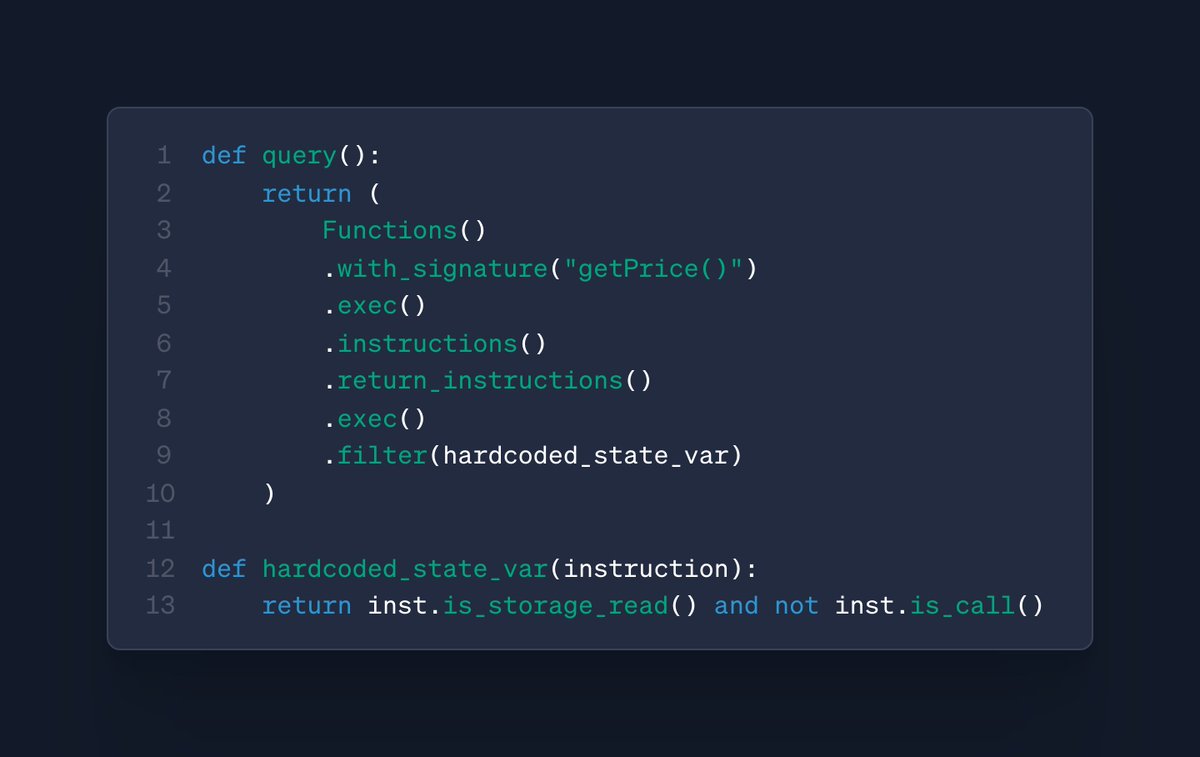
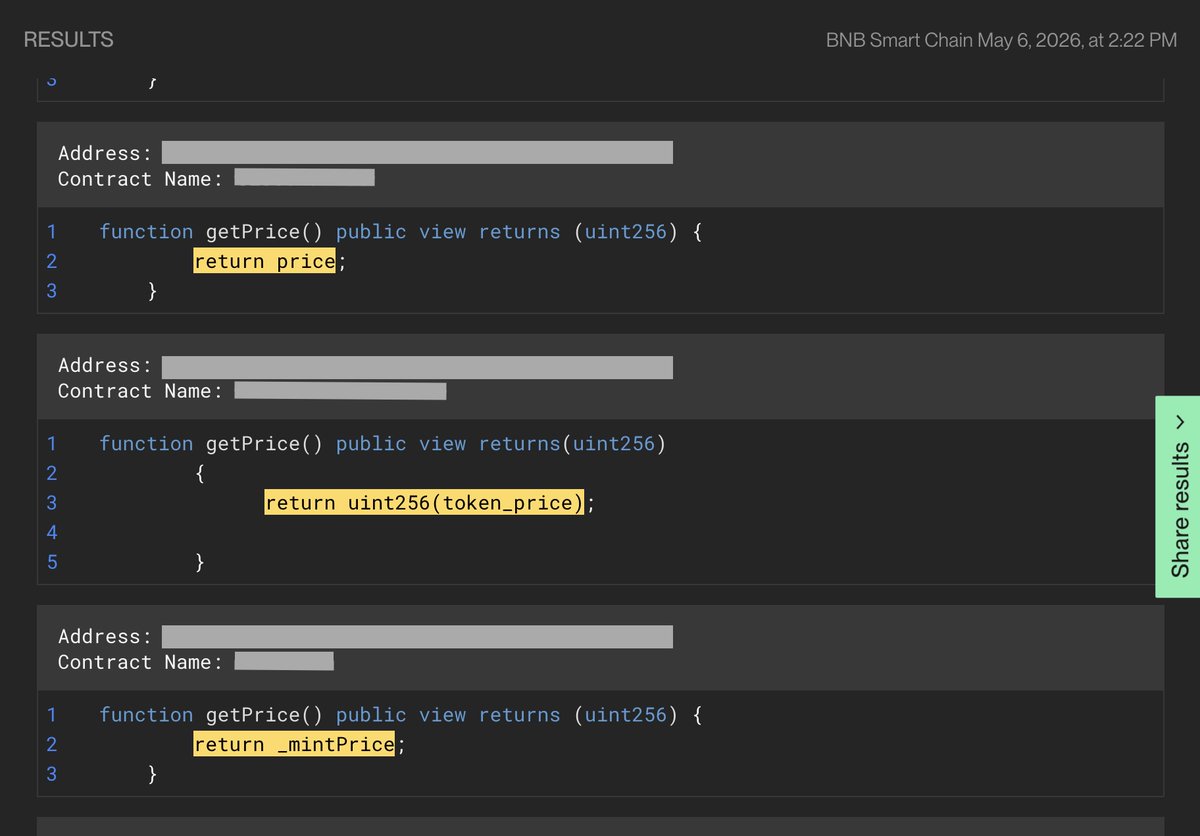

We decided to test @xyz_remedy glider tool and found a critical vulnerability in a privacy protocol. Tldr: Broken Groth16 deployment leads to proof forgery, allowing to withdraw full TVL. Read more below 👇

Attacks like KelpDAO/LZ will keep happening until we close the RPC Security gap. That's why we're partnering with @cyfrin, @hackenclub, @Hashlock_ and @hexens to help teams harden the layers smart contract audits don't reach. Learn more and check your exposure to RPC attacks 👇

KalqiX Mainnet is now LIVE. This isn’t just a new DEX. It’s infrastructure for the next generation of DeFi. Launch your own CLOB DEX. Plug into shared liquidity. Scale seamlessly. ⚡ Sub-10 microsecond execution 🔐 ZK-powered verification 📊 On-chain orderbooks 🛡️ MEV protection by design The next generation of high-performance DeFi starts now. On KalqiX. kalqix.com

It's never been harder to build or raise in crypto. And the teams that need audits the most are the ones just starting out. Hexens Builder Support: real security engagement built around where early-stage protocols actually are. Who qualifies: — Under $1M raised — First security audit (no prior professional audit) — Live or near-launch product (not just an idea) Too many good protocols die before their first audit or ship without one and get exploited. That's why we built Builder Support. To catch the ones worth catching, before anyone else does. Apply: hexens.io/?request-a-quo…