FFE4 retweetledi

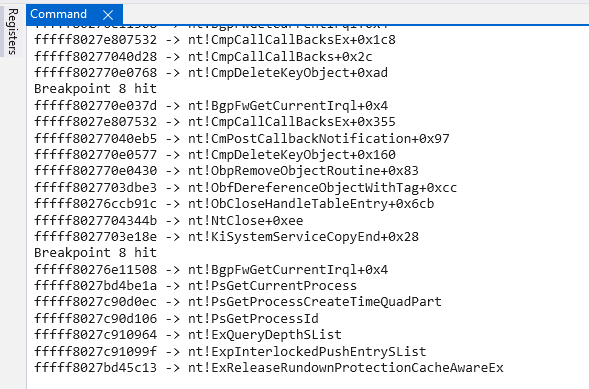
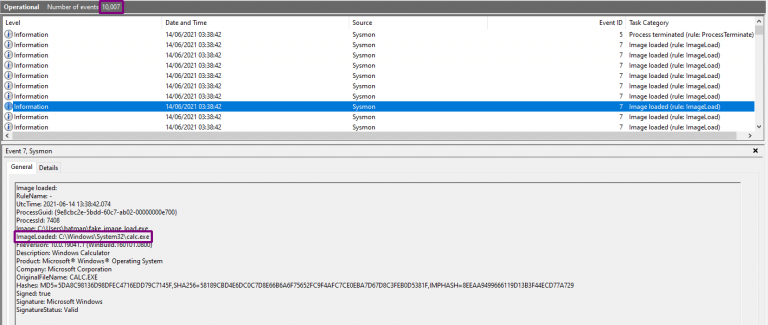
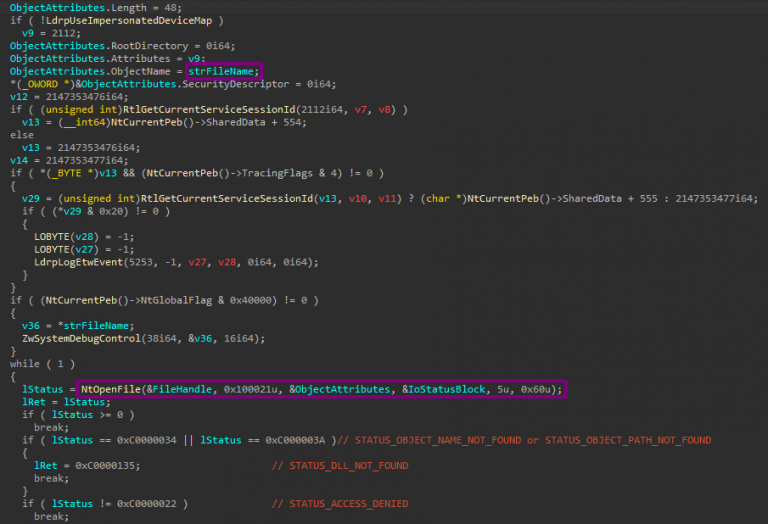
An analysis of CVE-2026-21236 - A heap based buffer overflow in the Microsoft Windows Kernel afd.sys - was just published by @ASN_Sinanju_06S a recent secondment with my team EDG!
Nice work for her first triage of a kernel memory corruption bug!
nccgroup.com/research/vulne…
English