Leon Trampert retweetledi
Leon Trampert
12 posts


Leon Trampert retweetledi

StackWarp: A new CPU vulnerability affecting AMD SEV-SNP (Zen 1-5). A malicious host can manipulate the stack pointer inside the confidential virtual machine, breaking integrity and confidentiality guarantees.
/cc @Rayiizzz
stackwarpattack.com
English
Leon Trampert retweetledi
Thrilled to present our (Lukas G., @LTrampert ,Youheng L, @jovanbulck ,@misc0110) newest paper ("SCASE: Automated Secret Recovery via Side-Channel-Assisted Symbolic Execution") at #USENIX Security this week!
1/n
English
Leon Trampert retweetledi
Heading to Black Hat Asia now! @LTrampert and I will give a briefing about deanonymizing users not only on the web but also in their email clients! #BHASIA
English
Leon Trampert retweetledi

Join Lorenz (@hetterichlorenz) and me tomorrow at our #BHUSA briefing "Arbitrary Data Manipulation and Leakage with CPU Zero-Day Bugs on RISC-V." We'll unveil a novel architectural CPU bug that breaks all security isolations on affected RISC-V hardware.
#arbitrary-data-manipulation-and-leakage-with-cpu-zero-day-bugs-on-risc-v-38293" target="_blank" rel="nofollow noopener">blackhat.com/us-24/briefing…
English
Leon Trampert retweetledi
#CacheWarp: a new software-based fault attack on AMD EPYC CPUs. It allows attackers to hijack control flow, break into encrypted VMs and perform privilege escalation inside the VM within minutes.
English
Leon Trampert retweetledi
Had the pleasure to present two papers at ESORICS today! The first analyzes the remaining attack surface of Meltdown 3a, the second (presented together with @fth0mas) shows that we can use Meltdown-US to leak the cache state of kernel structures on fully patched systems! 1/n

English
Leon Trampert retweetledi

I'm thrilled to present our (@____salmon____, @misc0110) work Hammulator, a parameterizable Rowhammer simulator, at #DRAMSec 2023 (June 17).
Our simulator supports both syscall and full-system emulation, enabling comprehensive analysis of #Rowhammer attacks and mitigations.
English
Leon Trampert retweetledi
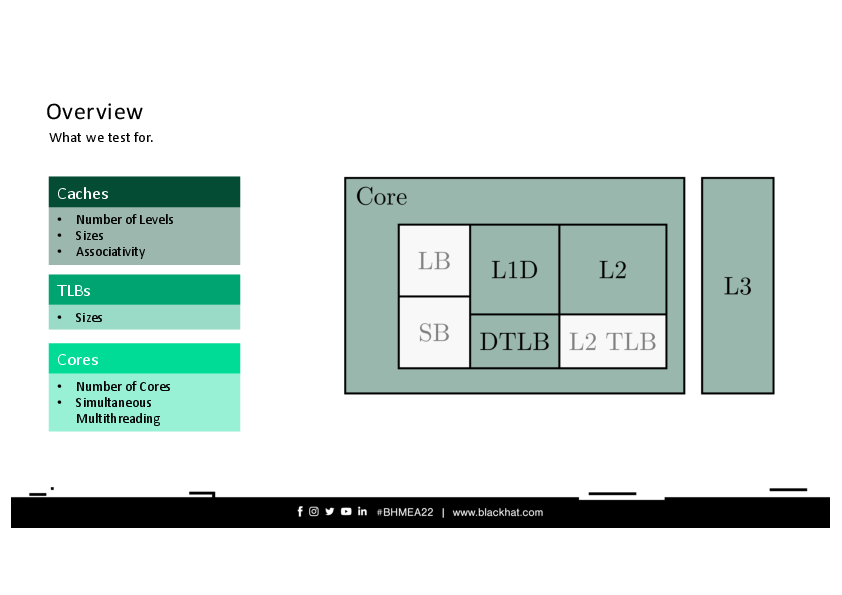
Thrilled to announce my first #Blackhat talk! We (@weber_daniel, @misc0110) will present how the power-optimization instructions umonitor/umwait can be abused to mount microarchitectural attacks. #BHMEA22

English
Leon Trampert retweetledi