Sabitlenmiş Tweet
Ruiyi Zhang
101 posts

Ruiyi Zhang
@Rayiizzz
Microarchitectural Security | PhD Candidate at CISPA | Ex Research Intern @Google | #StackWarp #CacheWarp
Katılım Ağustos 2019
226 Takip Edilen549 Takipçiler
@robertomasymas @weber_daniel @fth0mas @misc0110 I’m leaning toward it being an implementation bug. Regardless, it’s patched now, and CVMs are more secure.
English

@Rayiizzz @weber_daniel @fth0mas @misc0110 This seems so tightly controlled as to suggest it might be a government back door
English
@JustWantToQ1 That's correct. As I noted in the quote, while the bug exists on Zen 1-5, it only becomes a security vulnerability for confidential VMs.
English

@Rayiizzz I don't mean to take away from your work btw. Just trying not to scare people.
English
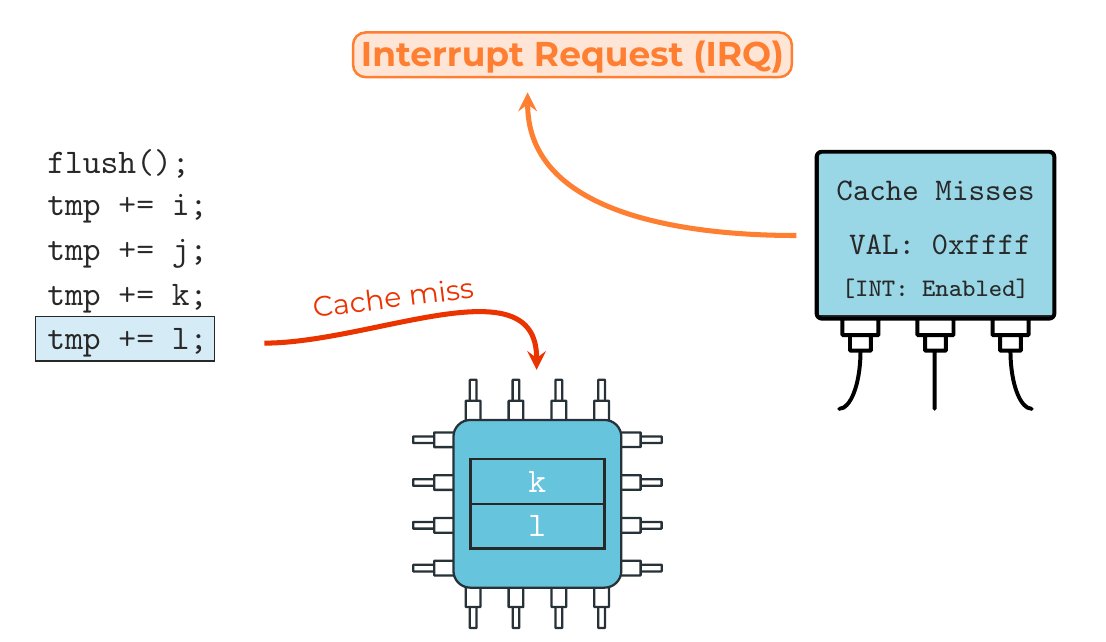
To clear up some confusion: the root cause lies in the stack engine, a CPU frontend optimization that manages the Stack Pointer (RSP) to reduce backend overhead.
We discovered that an undocumented MSR bit acts as a toggle for this optimization. (1/2)
Ruiyi Zhang@Rayiizzz
Today we reveal StackWarp: a new CPU vulnerability exploiting a synchronization bug in AMD’s stack engine across Zen 1–5 CPUs. It enables deterministic manipulation of Confidential VM's stack pointer, allowing RCE and privilege escalation via both control- and data-flow hijacking
English
Ruiyi Zhang retweetledi
New StackWarp Attack Threatens Confidential VMs on AMD Processors securityweek.com/new-stackwarp-…
English
@Rayiizzz Interesting work! We'd love to have you as a guest on the Off By One Security channel to walk us through this if you'd be interested!? Viewers love the low level vulnerability research topics.
@OffByOneSecurity" target="_blank" rel="nofollow noopener">youtube.com/@OffByOneSecur…
English
@Void_The_Null We disclosed this vulnerability to AMD in March 2025 and embargo is over as of today. AMD already released a microcode patch to mitigate it :)
English
For more details on the discovery process and our findings, we refer to our research paper, which is published at USENIX Security 2026.
paper: stackwarpattack.com
github: github.com/cispa/StackWarp
\cc Tristan Hornetz, @weber_daniel, @fth0mas, @misc0110
English
Ruiyi Zhang retweetledi

The program for uASC'26 is online uasc.cc/program.html We have some very interesting papers which are already available, so be sure to check them out. Better yet, join us in Leuven next month to listen to the authors! Registration is still open and free but seats are limited.
English
Ruiyi Zhang retweetledi

🔓 Heracles @acm_ccs'25: Breaking AMD’s Confidential Computing!
We show that the hypervisor can read and move hardware-encrypted memory on AMD SEV-SNP.
We build a chosen-plaintext oracle to leak kernel memory, auth keys, and cookies from "confidential" VMs
heracles-attack.github.io
English
Ruiyi Zhang retweetledi
Ruiyi Zhang retweetledi

long embargo, but there is a demo with good music at least: youtu.be/jrsOvaN7PaA

YouTube
Sandro@sparchatus
Disclosing Branch Predictor Race Conditions (BPRC), a new class of vulnerabilities where asynchronous branch predictor operations violate hardware-enforced privilege and context separation in virtually all recent Intel CPUs. @wiknerj @kavehrazavi : comsec.ethz.ch/bprc
English
Ruiyi Zhang retweetledi

✅ Write constant-time crypto code
☠️ Compiler introduces timing side-channels
Do Compilers Break Constant-time Guarantees?
fc25.ifca.ai/preproceedings…
TL;DR: Yes!🥲
👏👏👏Great work @misc0110 & team!

English
Ruiyi Zhang retweetledi

github.com/google/securit…
Our newest research project is finally public! We can load malicious microcode on Zen1-Zen4 CPUs!
English
Ruiyi Zhang retweetledi
Super excited to present our (L. Niemann, @____salmon____, @jan__reineke, @misc0110) newest paper at #ACSAC2024! We show how modern CPU hardware can be leveraged to stop side-channel attacks almost instantly (~200 CPU cycles)!
Code/Paper: github.com/cispa/IRQGuard
English
Ruiyi Zhang retweetledi

Excited to announce the release of the Rapid Data Analysis (RDA) framework! RDA streamlines side-channel analysis with plotting, processing, and analysis tools—usable directly from the terminal or in scripts. Check it out: github.com/0xhilbert/rda #SideChannel

English


