Sabitlenmiş Tweet
Michael Schwarz
690 posts

Michael Schwarz
@misc0110
InfoSec Faculty @ #CISPA. Side-channel attacks. Exploiting microarchitectures. #Meltdown #Spectre #ZombieLoad #SGX #JavaScript #Rowhammer
Katılım Mart 2014
458 Takip Edilen7.2K Takipçiler
Michael Schwarz retweetledi
Michael Schwarz retweetledi
New StackWarp Attack Threatens Confidential VMs on AMD Processors securityweek.com/new-stackwarp-…
English
Michael Schwarz retweetledi

StackWarp: A new CPU vulnerability affecting AMD SEV-SNP (Zen 1-5). A malicious host can manipulate the stack pointer inside the confidential virtual machine, breaking integrity and confidentiality guarantees.
/cc @Rayiizzz
stackwarpattack.com
English
Michael Schwarz retweetledi
Michael Schwarz retweetledi

New StackWarp Attack Threatens Confidential VMs on AMD Processors: Researchers have disclosed technical details on a new AMD processor attack that allows remote code execution inside confidential VMs.
The post New StackWarp Attack Threatens… securityweek.com/new-stackwarp-…
English
Michael Schwarz retweetledi

Registration is open for MICSEC Winter School 2025 (Dec 1–5)!
An incredible week in side-channel and microarchitectural security with talks and hands-on sessions from world-class experts.
Register now: micsec.wp.imt.fr
English
Michael Schwarz retweetledi
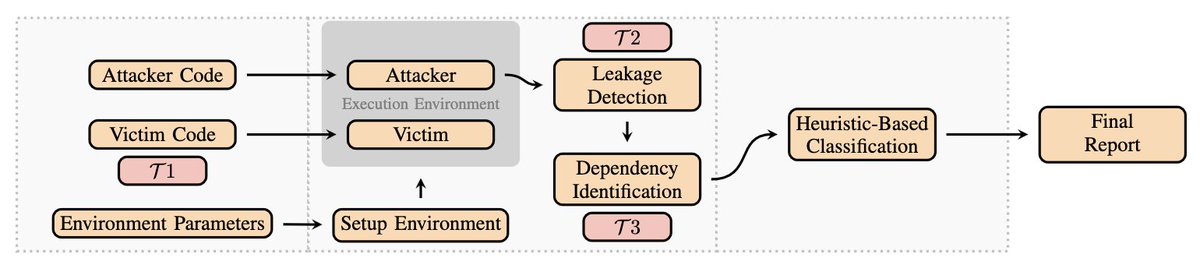
Thrilled to present our (Lukas G., @LTrampert ,Youheng L, @jovanbulck ,@misc0110) newest paper ("SCASE: Automated Secret Recovery via Side-Channel-Assisted Symbolic Execution") at #USENIX Security this week!
1/n
English
Michael Schwarz retweetledi
Michael Schwarz retweetledi

✅ Write constant-time crypto code
☠️ Compiler introduces timing side-channels
Do Compilers Break Constant-time Guarantees?
fc25.ifca.ai/preproceedings…
TL;DR: Yes!🥲
👏👏👏Great work @misc0110 & team!

English
Michael Schwarz retweetledi
@LTrampert and I just gave a talk at Black Hat Asia showing how CSS can be abused to deanonymize you when opening an email!
cc: @BlackHatEvents #BHASIA25

English
Michael Schwarz retweetledi
Heading to Black Hat Asia now! @LTrampert and I will give a briefing about deanonymizing users not only on the web but also in their email clients! #BHASIA
English
Michael Schwarz retweetledi

The second #DIMVA25 deadline is upcoming: February 12 AoE. If you're planning to submit a paper, register it already: dimva.org/dimva2025/
DIMVA has a great community and is quite visible: 3 out of my 10 top cited papers are DIMVA papers!
Hope to see many of you in Austria!
English

@_MatteoRizzo Wow, great work! The PoC also works like a charm on the Ryzen 9 7940HS I tested. Looking forward to reading more details about that.
English
Michael Schwarz retweetledi

github.com/google/securit…
Our newest research project is finally public! We can load malicious microcode on Zen1-Zen4 CPUs!
English
Michael Schwarz retweetledi

The uASC registration is open now:
uasc.cc
Also the uASC deadline is approaching: January 27 AoE.
We accept papers, posters, and talks. We have conference proceedings. We're interested in any insights broadly around microarchitecture security.
English
Michael Schwarz retweetledi

CFP for uASC 25 is still open. We have rolling reviews, and 1 submission is already accepted. If you have interesting results on microarchitecture security (incl. weak threat models or reproducing prior work), check out the CFP at uasc.cc
The CFP closes **Jan 28**
English
Michael Schwarz retweetledi
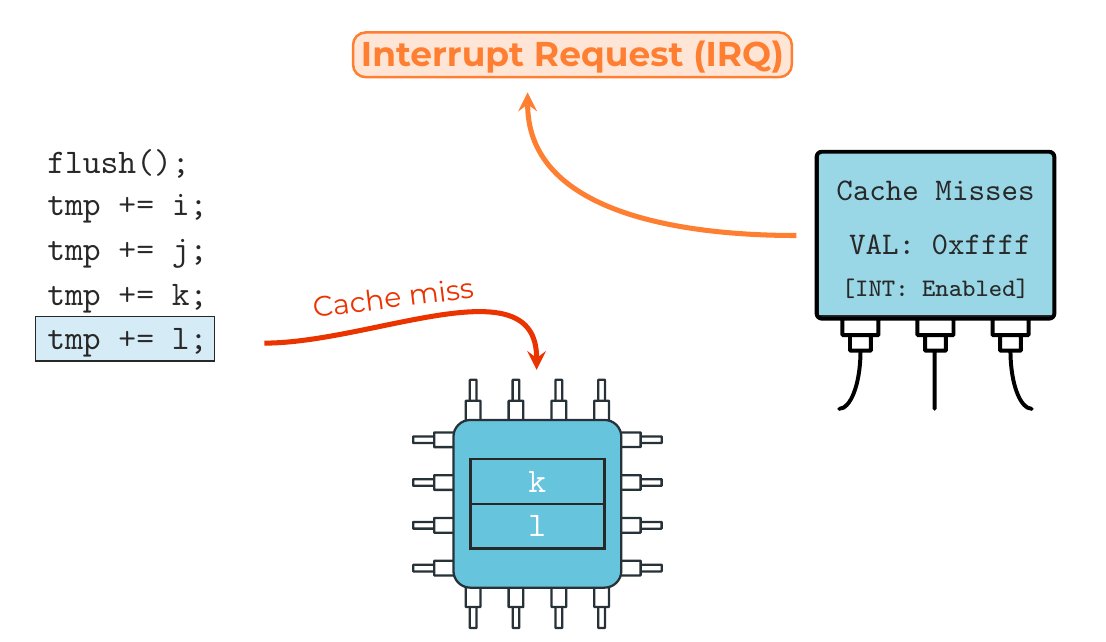
Super excited to present our (L. Niemann, @____salmon____, @jan__reineke, @misc0110) newest paper at #ACSAC2024! We show how modern CPU hardware can be leveraged to stop side-channel attacks almost instantly (~200 CPU cycles)!
Code/Paper: github.com/cispa/IRQGuard
English
Michael Schwarz retweetledi

Got some negative or unrealistic threat model results that still bring interesting insights? A side channel that requires root to leak something from the kernel? Reproducing prior work? Somewhat related to microarchitecture? Here's your venue: uasc.cc
English