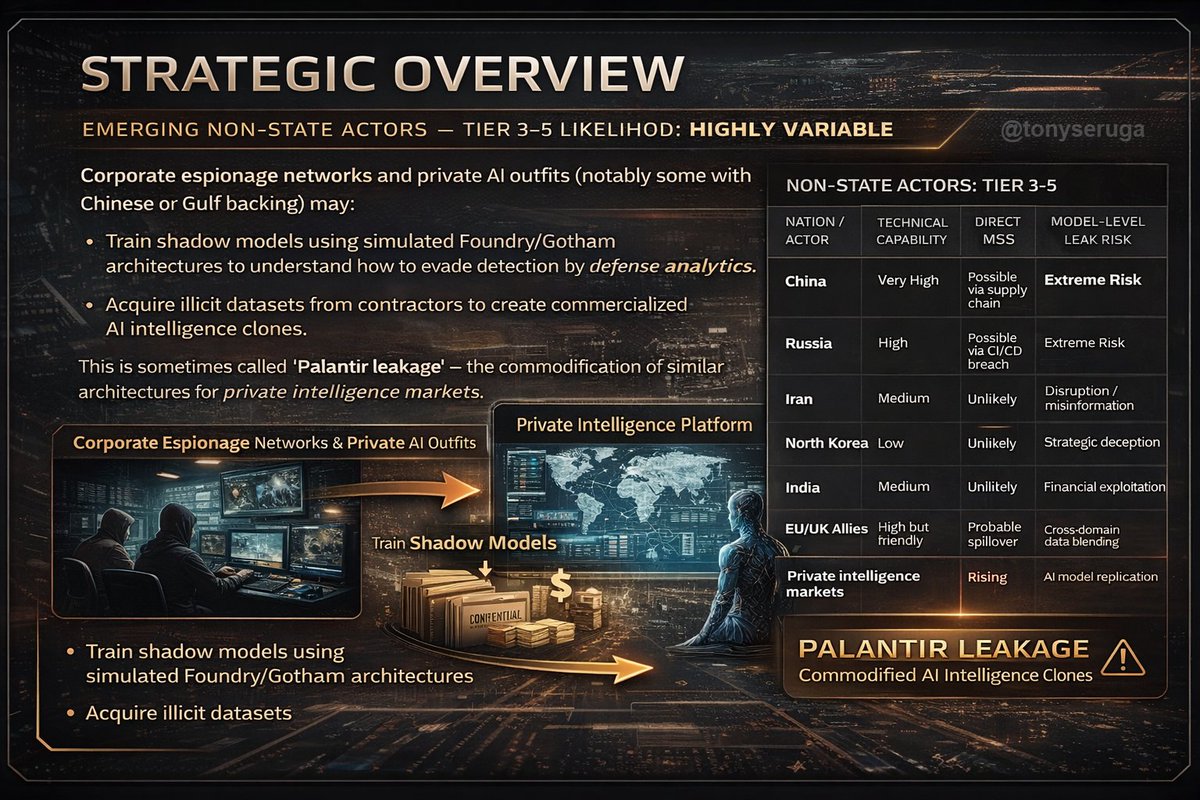
🚨 China Turns Iran War Data Into Future Battlefield Strategy, Intelligence Warns China May Have Backdoor Access to the Military’s Artificial Intelligence (AI) That Is Assisting in Identifying, Prioritizing, and Selecting Targets Palantir’s Maven Smart System epitomizes the fusion of national defense with private algorithmic governance. By centralizing command, data, and inference into a single private ecosystem, it grants unparalleled operational advantage — but also creates an unprecedented strategic vulnerability: the compromise of a single cognitive system could blind or misdirect an entire military command. Given Palantir’s reliance on both subcontractors and partner militaries: Contractor ecosystem sprawl: each subcontractor introduces another partially vetted node with remote access. CI/CD supply chain compromise: tampering in dependency packages (Python, JVM, or container base images) could plant implants before deployment. Insider inference exfiltration: employees can’t copy data, but can screenshot dashboards — visual inference leakage remains a persistent risk. To meaningfully secure MSS, the following reforms are critical — though politically inconvenient: 1. Zero-trust segmentation across ontology tiers. Every data type and AI model should be isolated from full graph visibility unless cryptographically justified. 2. Mandatory third‑party code audits of Apollo update pipelines. No system should have self‑updating privileges in a classified battlespace without external cryptographic verification. 3. Model provenance registries. Record all training lineage and validator credentials — immutable logs, blockchain‑style, to trace corrupted weights. 4. Explainable inference enforcement. Require model-generated evidentiary traces human analysts can interrogate — removing Palantir’s “black‑box” protection. 5. Kill‑switch air‑gap enforcement. Field nodes must have the ability to sever synchronization entirely during suspected compromise.