Marc Smeets
23.8K posts


Marc Smeets
@MarcOverIP
Does a thing or two with red teaming @OutflankNL | part time race and drift car instructor




Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin


New release: kicking off Red Macros Factory integration into OST by @OutflankNL researcher @mariuszbit! ⚙️ Builder tool now ships with better script payload gen, obfuscation, guardrails, LNK tradecraft, and new conversion paths. More formats and payload shenanigans coming soon!





The userland demon is about to drop again.



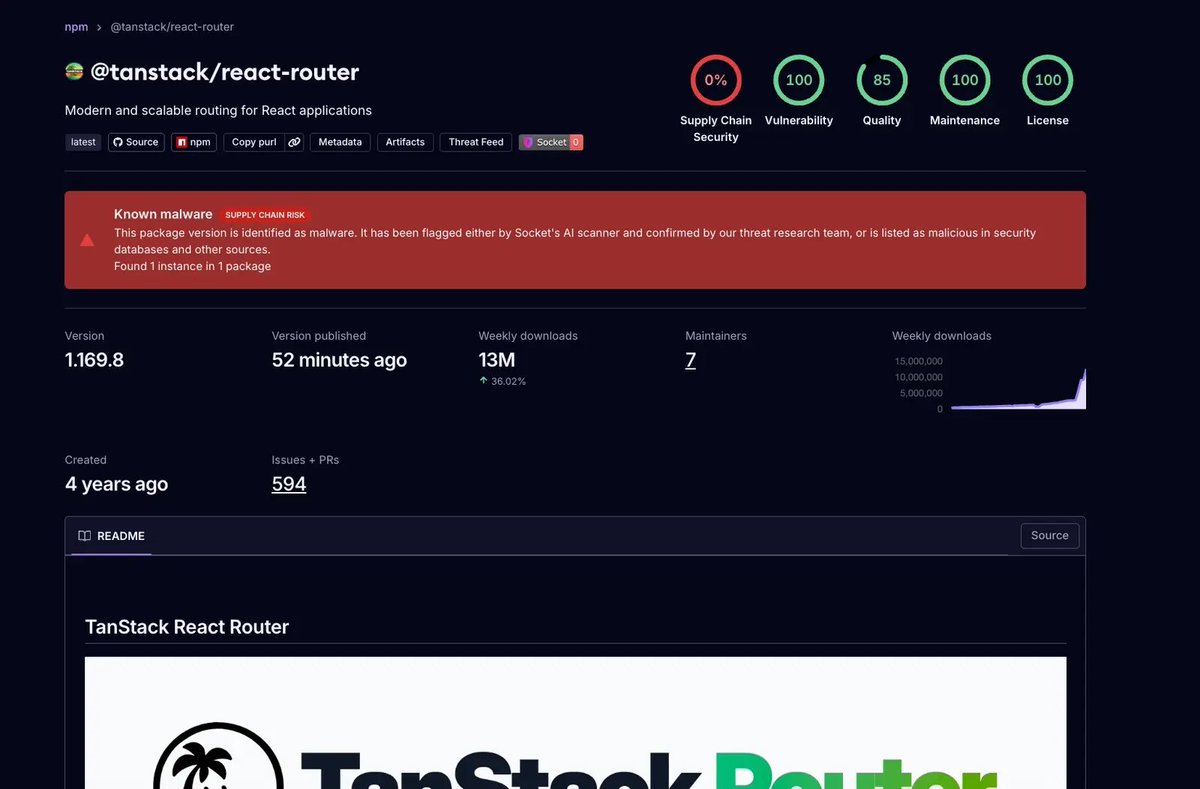
This attack leveraged GitHub Actions Cache Poisoning. Payload deployed here: github.com/TanStack/route… It looks like it detonated here: #step:26:2" target="_blank" rel="nofollow noopener">github.com/TanStack/route…

2026 version of the 1940s airplane-got-shot illustration. This is an Ukrainian interceptor drone btw.


Have you noticed that those deep-dive stories about complex Windows malware have pretty much vanished, especially in recent years? It feels like the era of "blockbuster" Windows malware has just gone silent, and this blog post tries to give some answers why. r136a1.dev/2026/05/07/whe…