Pat1776
237.4K posts

Pat1776
@Matka1776
EVIL ONLY THRIVES IN DARKNESS! Expose everything…bring it into the light! Stay united and hold the line…God wins!!!


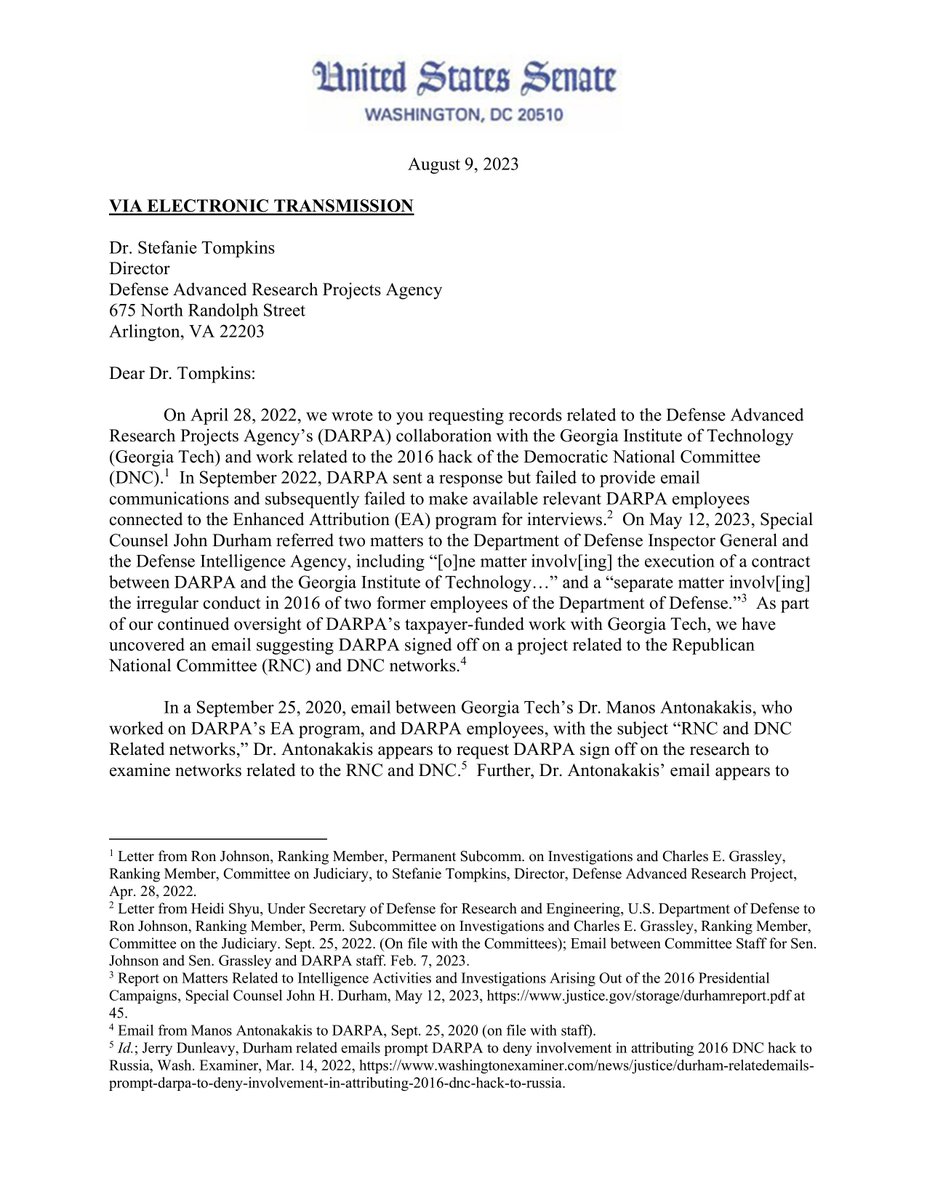
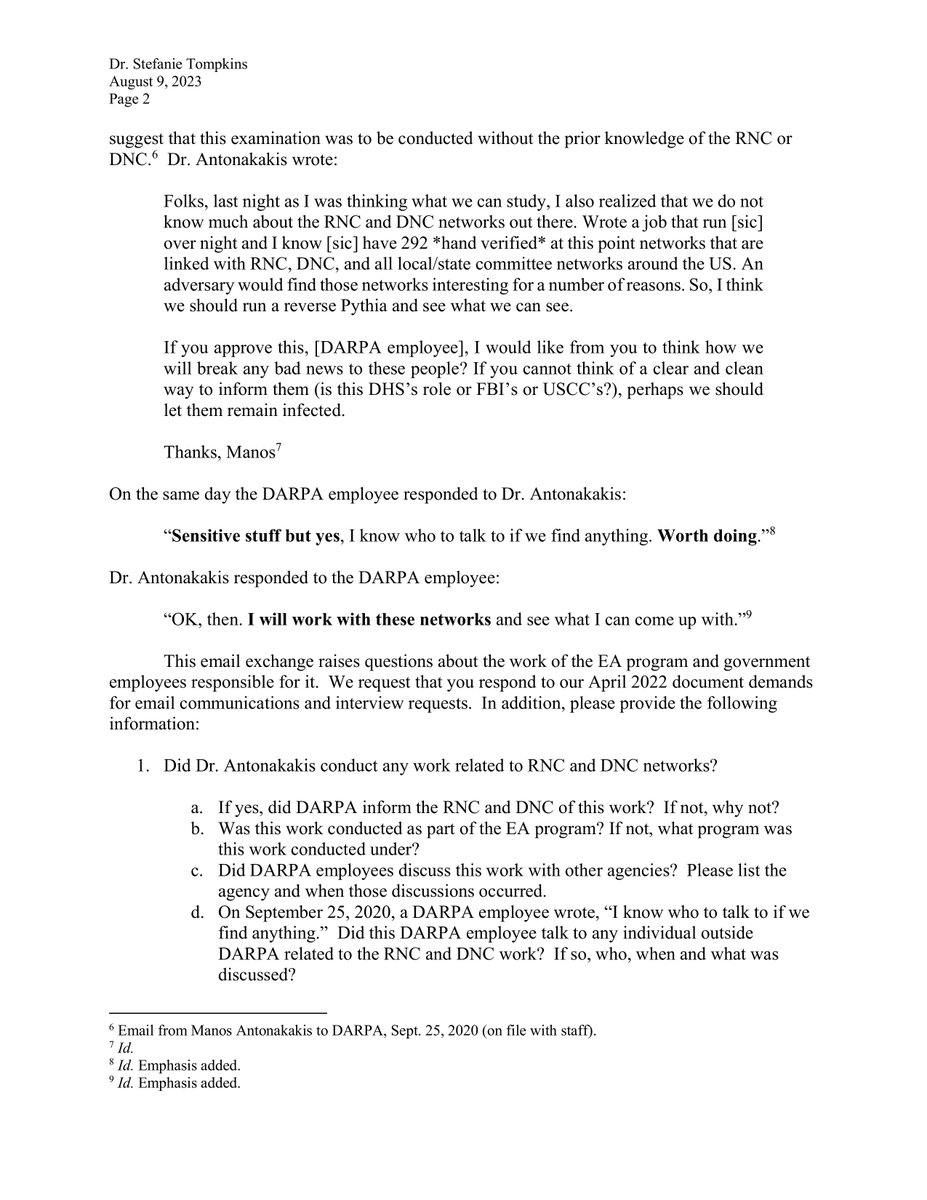
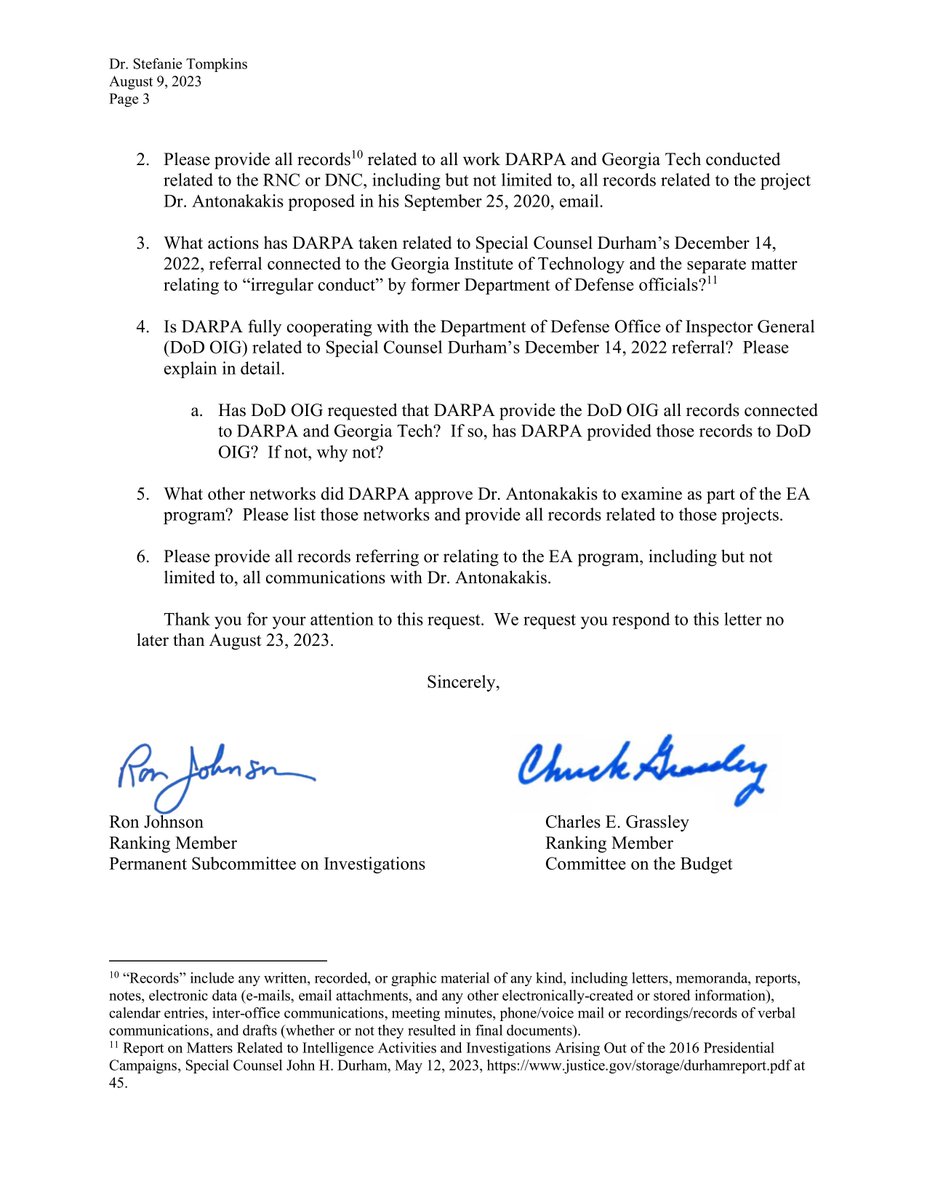



Does anyone know who chose @marceelias to be in charge of the elections in our country? Why is he endlessly filing lawsuits as if he represents We the People? The guy is the guru behind the Russia Hoax and Hillary’s fake dossier. He should have lost his law license years ago.

🚨 BREAKING: The House of Representatives has passed a bill mandating automatic deportation for illegal aliens who commit welfare fraud, in a 231–186 vote.




64. Among the US Senators who were briefed were Sen. Kevin Cramer (R-N.D.) & Ron Johnson (R-Wis.). Several NSC officials also got the documents. Neither Cramer nor Johnson nor Trump's NSC officials tried to authorize the investigation outlined in the docs.

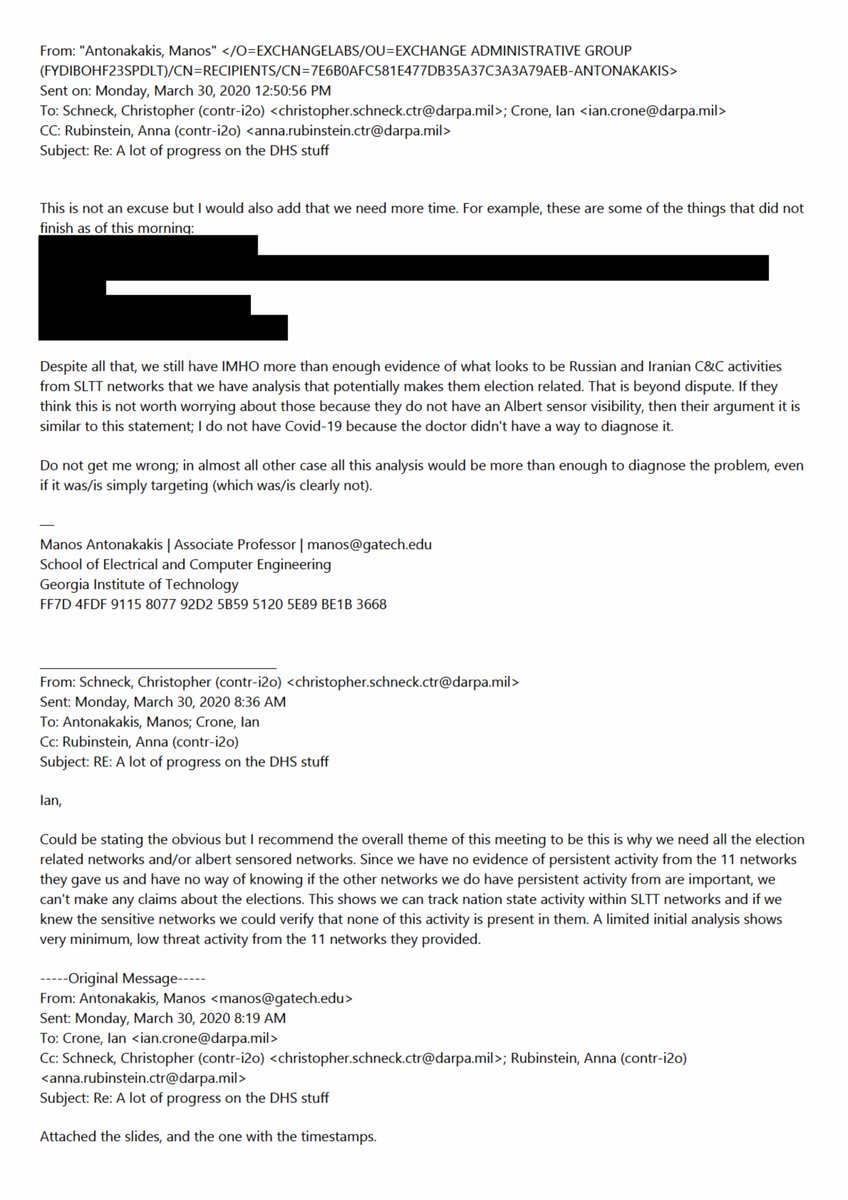
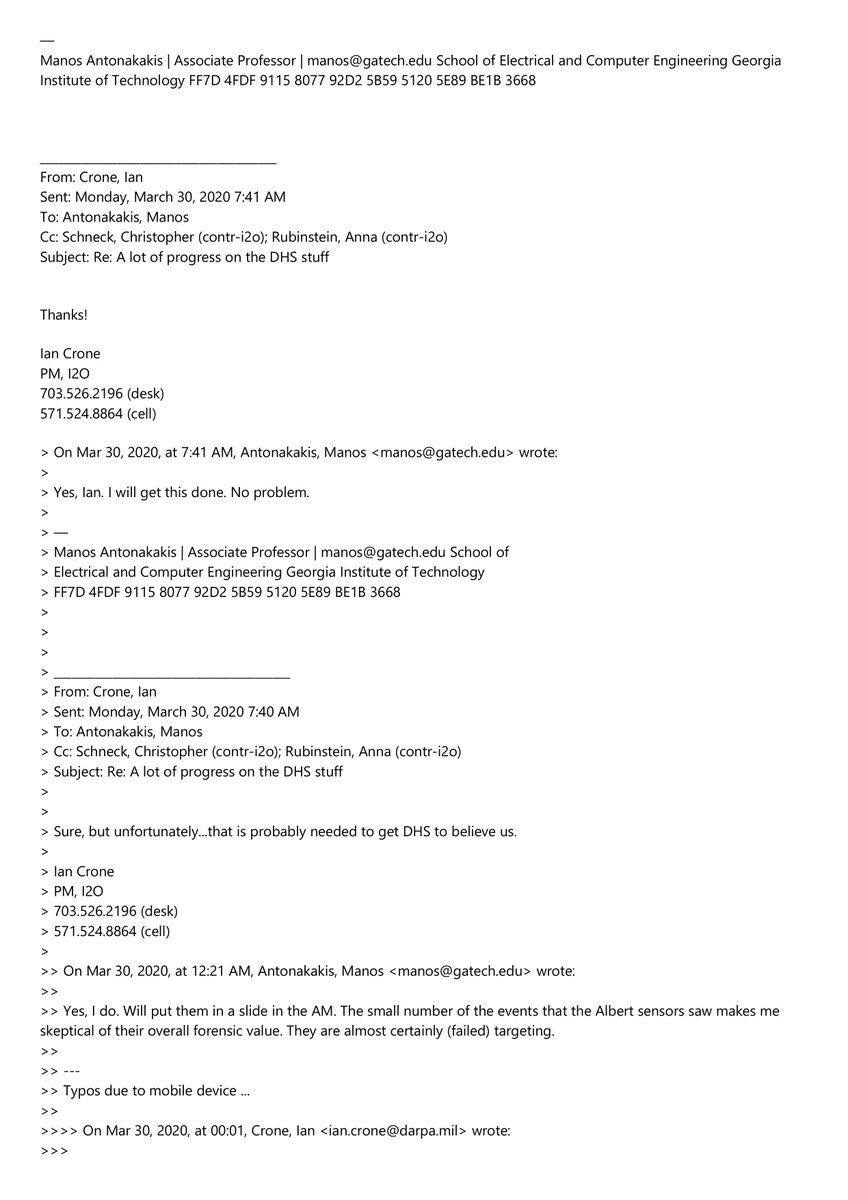













🔥🔥🔥Holy Cow! John Brennan is linked to global disinfo and anti conservative orgs! You see, the Intelligence Studies Project (ISP) that John Brennan and two other ex CIA belonged to was involved in the Global Disinformation Index (GDI) thru the Global Disinformation Lab (GDIL). It’s also affiliated with the illiberalism Studies Program. Plus, I have a massive surprise at the end! Remember the Texas National Security Network? It’s the entire University Of Texas state wide campus’s and its orgs. They all work together interchangeably. Part of this Network is the LBJ School of Public Affairs. LBJ is where ex CIA John Brennan, Paul Pope, and Stephen Slick run the Intelligence Studies Program. Both Global Disinformation Lab cofounders (Ryan Williams and Kiril Avramov) are from LBJ. Ryan Williams headed up the Global Disinformation Labs Project Evergreen. Where they used a Policy Research Project team from the LBJ School of Public Affairs to write a database of global policy responses to disinformation. Brennan, Pope, and Slicks Intelligence Studies Project is at LJB and often sponsored events for the Global Disinformation Lab. Just one big happy family. The Global Disinformation Lab proclaimed an outright partnership with the Global Disinformation Index. And also worked with each other on a Disinformation Risk Assessment. Here are the Global Disinformation Labs affiliates. -illiberalism Studies Program -Intelligence Studies Project -Strauss center -Clements center -Center for European Studies university Texas Austin -Center for Russian, Eastern European and Eurasian Studies (CREEES) * Intelligence Studies Project is ran By Strauss and Clements at LBJ. Biden’s State department worked with them too. Liz Allen the Under Secretary of State for Public Diplomacy and Public was their go to. “Really appreciate US Dept of States efforts in working to understand and countering mis- and disinformation. Looking forward to jointly collaborating on these efforts!” ♦️The Illiberalism Studies Program: “Addresses questions related to democratic backlash, the spread of authoritarianism, post-liberalism, the far right, populism and nationalism.” “Adherents of illiberalism argue that, in the face of a liberalism that has “gone too far,” it is time to reassert the rights of the collective, or of an alleged silent majority, by restoring national sovereignty in various spheres: politically, by rejecting supranational and multilateral institutions in favor of the nation-state and preferring a strong leader.” Plus I have a 110 page report where they compare republican Christians to Russians: “Marlene Laruelle explores the parallel between US Christian nationalism and the Russian case of a blending of the Russian Orthodox Church with the political language of the Putin regime. ♦️Now the Global Disinformation Lab works on more than disinfo. They work with the Army Cyber Institute of the U.S. Military Academy at West Point to the tune of $250,000. This also involves Threatcasting which I have previously discussed during my CTI League files exposé. I don’t trust this disinfo lab in this arena. They also run Project Tearline, where the military even gave it its own website. Tearline.mil ♦️ Now for even more big news! John Brennan was involved in a US Election LBJ Policy Research Project headed by Stephan Slick. This also involved Chris Krebs, Michael Daniel, Nick Rasmussen, & more. I have this below mentioned 243 page report and Brennan talks Russiagate outta the wazoo. I think a lot of X folks in the Spygate corner would be extremely interested in this. “Working in collaboration with Nicholas Rasmussen, an Intelligence Studies Project Senior Fellow who serves as the director of the Global Internet Forum to Counter Terrorism, Slick & his students will draft a final report to counterparts at Office of the DNI that includes recommendations to defend against future attempts to influence elections. Sources to follow!
