Archive
665 posts





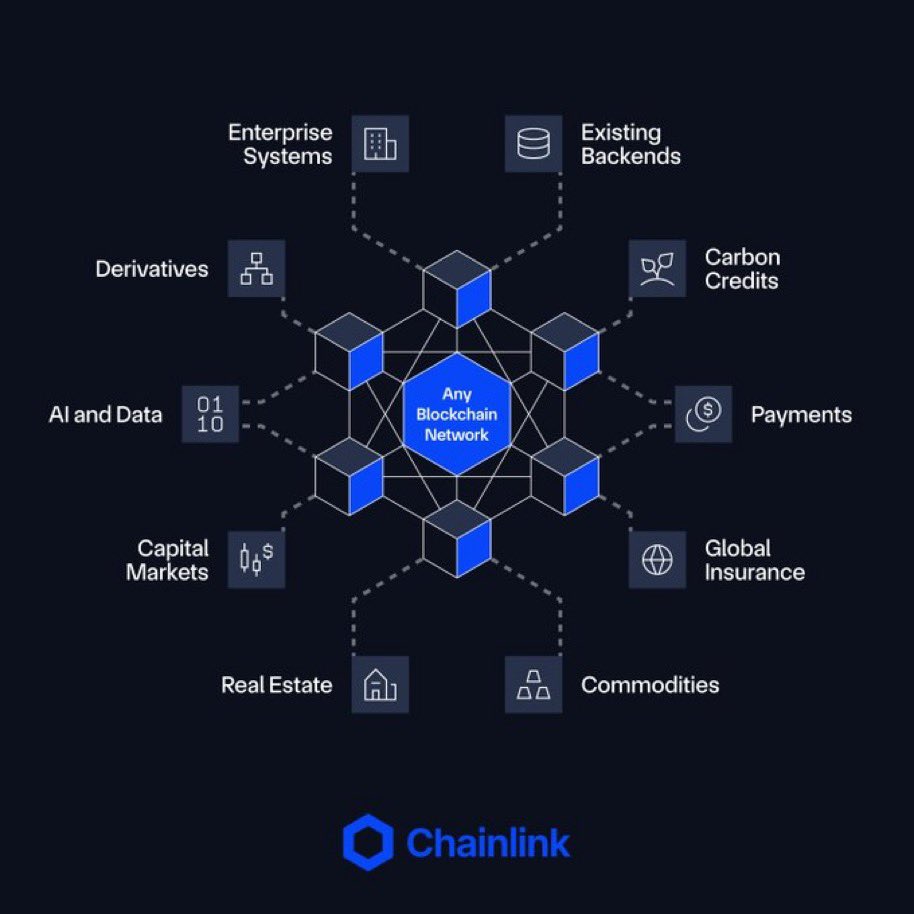
Kraken is deprecating its existing cross-chain provider and migrating to @Chainlink CCIP as its exclusive cross-chain infra to secure Kraken Wrapped Bitcoin (kBTC) & all future Kraken Wrapped Assets. Kraken chose Chainlink CCIP because it offers enterprise-grade infrastructure with strict security & risk management requirements, including: • ISO 27001 and SOC 2 Type 2 certifications • Secure by default architecture • 16 independent nodes • Native rate limits, and more. Together, Chainlink and Kraken can help accelerate the global adoption of crypto by unlocking utility and distribution for all Kraken Wrapped Assets across DeFi. For kBTC customers, no action is required. More details on the migration process to follow on official Kraken channels.


LayerZero has lost $4B in TVL after 5 major protocols migrated to Chainlink's CCIP You get hacked once and its over


Following a comprehensive security review of the cross-chain infrastructure underpinning LBTC and BTC.b: - CCIP will replace LayerZero as the cross-chain infrastructure across Solana, Etherlink, Berachain, Corn, and TAC - LayerZero on Morph and Swell will be fully deprecated


Following recent bridge exploits, Lido contributors are publishing the security principles behind wstETH’s multi-chain strategy, and why @chainlink CCIP was selected as the official cross-chain solution. The analysis covers how Chainlink CCIP delivers strong decentralization, native safeguards, and issuer control as default protocol-level guarantees, which insulates wstETH from a number of attack vectors behind the Kelp / LayerZero exploit. This decision was made last November by the Network Expansion Committee, with CCIP securing wstETH via 16 independent node operators, native rate limiting, and no vendor lock-in over token contracts. Read the full breakdown from Lido contributors: blog.lido.fi/cross-chain-se…



Without the Clarity Act, the digital asset industry will move offshore to any nation that has regulators willing to engage. Every day that we stall is a day we hand our competitors an advantage we won't get back. The Clarity Act is critical to securing our financial future.

Kraken is deprecating its existing cross-chain provider and migrating to @Chainlink CCIP as its exclusive cross-chain infra to secure Kraken Wrapped Bitcoin (kBTC) & all future Kraken Wrapped Assets. Kraken chose Chainlink CCIP because it offers enterprise-grade infrastructure with strict security & risk management requirements, including: • ISO 27001 and SOC 2 Type 2 certifications • Secure by default architecture • 16 independent nodes • Native rate limits, and more. Together, Chainlink and Kraken can help accelerate the global adoption of crypto by unlocking utility and distribution for all Kraken Wrapped Assets across DeFi. For kBTC customers, no action is required. More details on the migration process to follow on official Kraken channels.



Heslin Kim @HeslinKim, Co-Founder & CBO of @ZenithFdn, takes the Proof of Talk stage this June on the Canton Track. Zenith is building the EVM execution layer for Canton, letting Ethereum devs and institutions deploy on the same infra with privacy, compliance, and atomic settlement built in. They're a Super Validator on Canton with the maximum weight of 10. Alongside @jpmorgan, @HSBC, @Visa, and @The_DTCC. Heslin has spent 10+ years in digital assets and tokenized securities. At the Louvre he's talking cross-VM architecture, app composability, and bridging DeFi to institutional-grade onchain finance. June 2–3. Louvre Palace, Paris. The Davos of Web3. tickets.proofoftalk.io/passes




ERC677 = Stateful = TCP ERC20 = Stateless = UDP CCIP = Stateful = active Risk Management Every other blockchain bridge = Stateless = passive/no risk management CCIP is the new TCP/IP The Risk Management Network is the new <firewall vendor you think most secure> #DeFI #crypto

The Clarity Act is a joke. - Retail is getting absorbed into the predatory finance system which does NOT give equal access like crypto did - No real developer protections - Warren speaking out without reading - Don’t even ask about the emoji, you know






When devs want omnichain apps and real interoperability… They look at LayerZero 👀 Positive vibes. Fast innovation. Real builder energy. Meanwhile Chainlink maxis still fighting on Twitter 😭 $ZRO



All the hate around @LayerZero_Core is a desperate effort from the link marines to win a battle that has already been won by LayerZero, no 1 in the interop game. As I do agree that LZ has their fault in the whole situation, but the hate is being blown out of proportion.

This new post from @LayerZero_Core directly contradicts Bryan's claim yesterday that the LayerZero Labs multisig signer who was trading the "McPepes" memecoin on Uniswap was just "testing the PEPE OFT integration" Turns out that gaslighting doesn't work when people can check the chain and verify for themselves Naturally, they attempt to minimize the issue by making it seem like this was a one time incident, involving only one signing key, and that the memecoin trader was quickly rotated off the multisig In reality, the multisig signer attempted multiple memecoin trades over the span of a year and stayed on the multisig for nearly two years after the first memecoin trade, before finally being rotated off Furthermore, there were actually 3 signing addresses that were engaged in non-multisig related activity (memecoin trading, DEX swaps, bridging, LP provisioning) on a 2-of-5 Gnosis Safe multisig Billions of dollars in OFT value was exposed to the risk of being exploited by a multisig whose majority threshold of signers failed to practice even the most basic opsec and key isolation practices, FOR YEARS This was not a one-time error oopsie, this was a complete disregard for opsec -- Timeline of events of the LayerZero memecoin trader multisig signer: March 1, 2023 - 0xf1f5E swaps 0.198548 ETH for 1,727,120 McPepes (PEPES) December 21, 2023 - 0xf1f5E calls approve() for Uniswap on the McPepes ERC20 contract April 20, 2024 - 0xf1f5E attempts to sell McPepes on Uniswap but the transaction reverts January 27, 2025 - 0xf1f5E is finally rotated off LayerZero’s Gnosis Safe multisigs and signing threshold changed -- More context in following tweets